文件属性
根据文件运行结果应该是调用了win32函数,有点像mfc,查壳后发现是32位无壳,VC++编译
算法分析
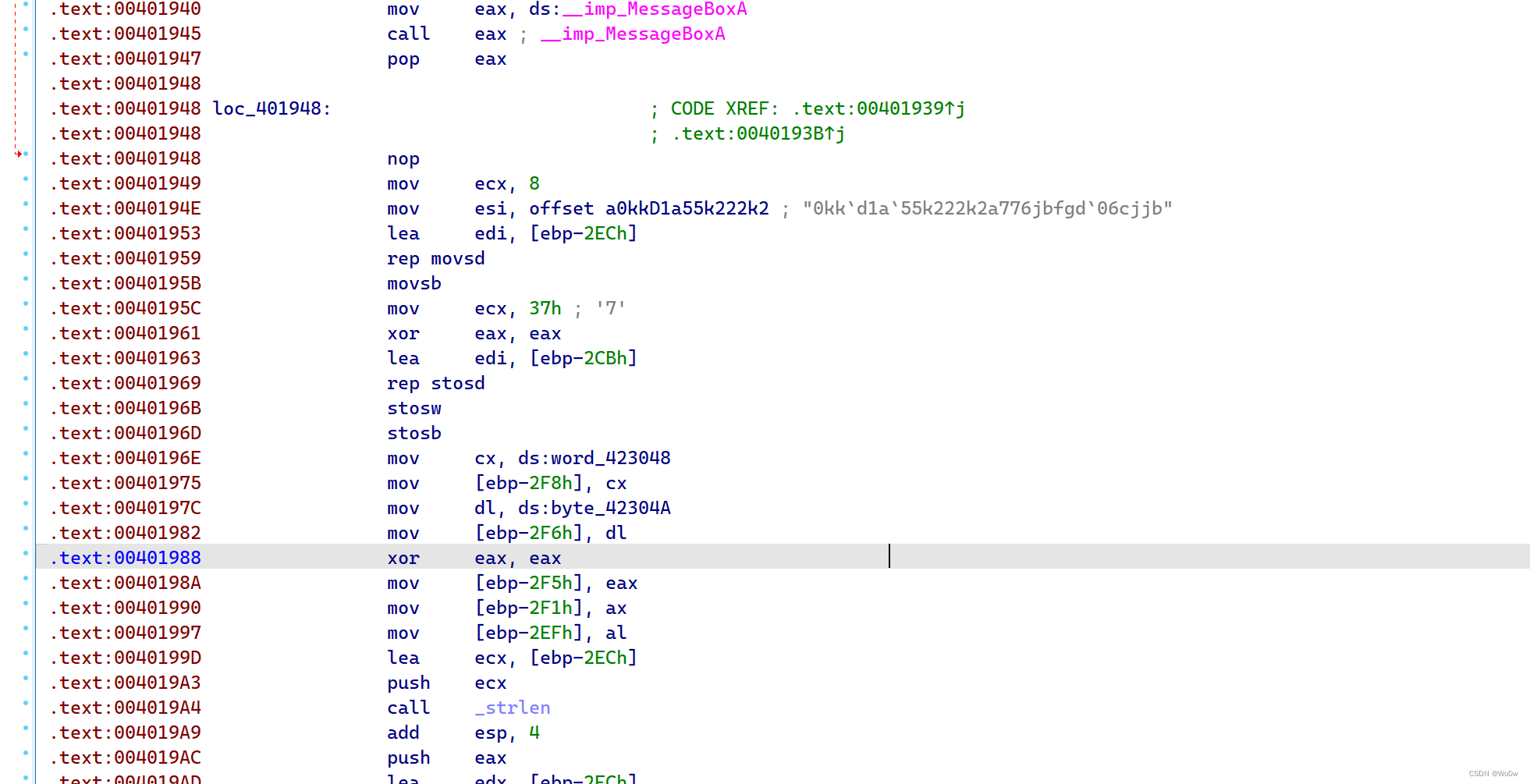
根据字符串定位代码后发现无法直接转代码,有脏东西😕
下面有个判断有问题,会无条件跳转执行不了接下来的代码,但ida默认是都会执行
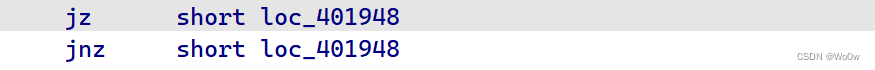
将下面的jmp nop掉因为原程序中不会执行,在这里干扰了ida的判断,然后转函数就成功了
定位到加密区域
Hash
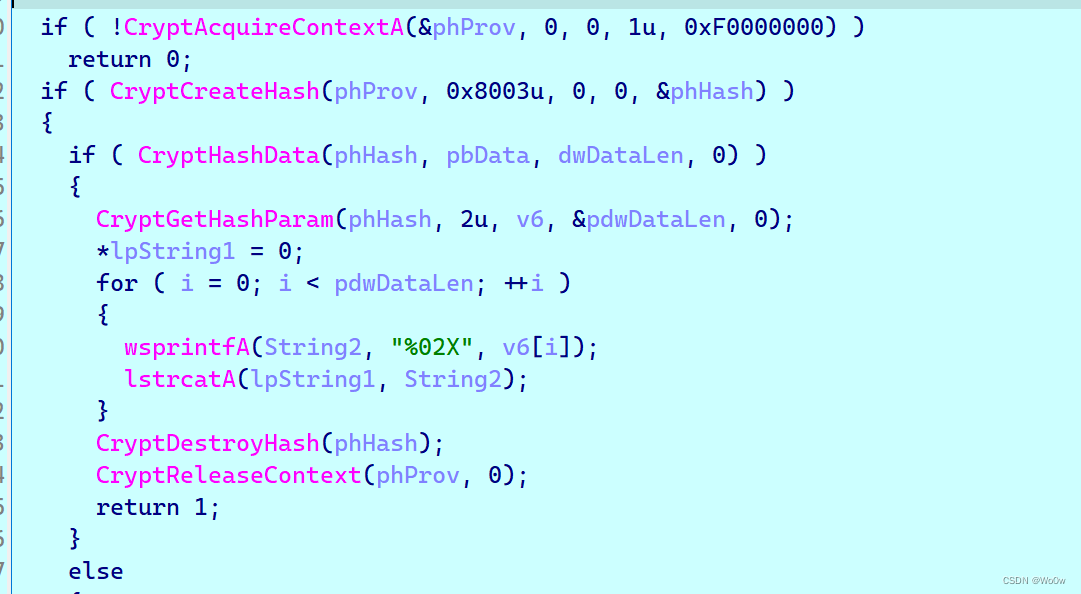
对输入值进行hash
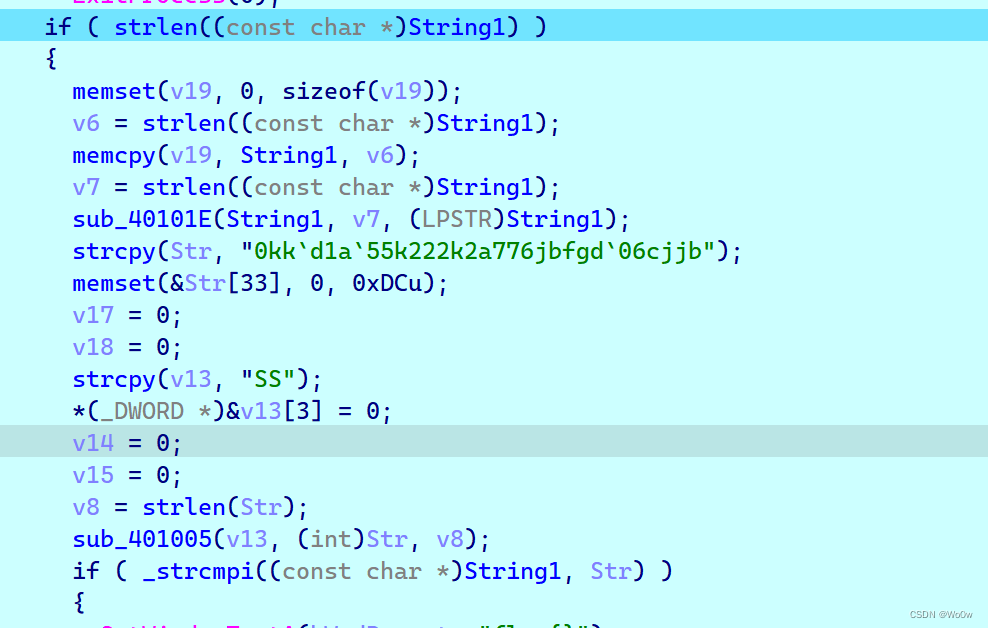
SS异或
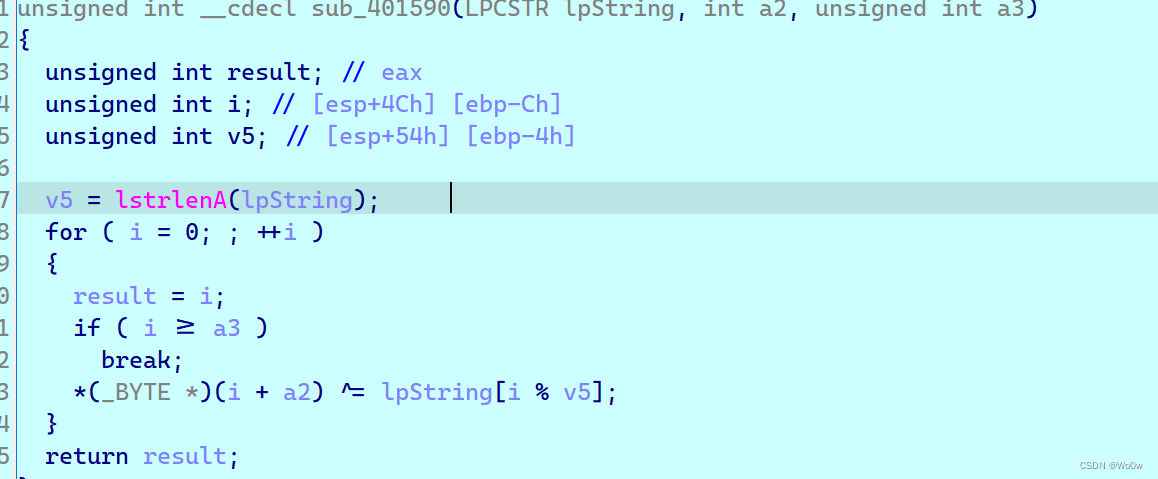
将SS作为密钥与str异或
str:“0kkd1a55k222k2a776jbfgd`06cjjb”
第二次调用异或函数
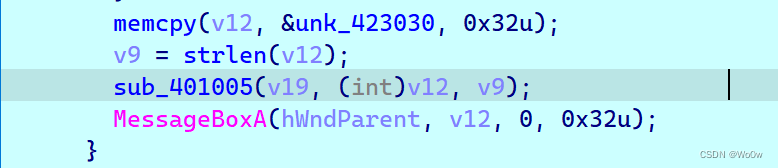
unk_423030动调值为:
0x57, 0x5E, 0x52, 0x54, 0x49, 0x5F, 0x01, 0x6D, 0x69, 0x46,
0x02, 0x6E, 0x5F, 0x02, 0x6C, 0x57, 0x5B, 0x54, 0x4C, 0x00
wp
#include"stdio.h"
#include"string.h"
unsigned int __cdecl sub_401590(char* lpString, char *a2, unsigned int a3);
int main(){
char data[]="0kk`d1a`55k222k2a776jbfgd`06cjjb";
char key ='S';
for(int i=0;i<strlen(data);i++)
data[i] ^=key;
printf("%s",data);
//c8837b23ff8aaa8a2dde915473ce0991,在线解hash:
//123321
char table[] ={ 0x57, 0x5E, 0x52, 0x54, 0x49, 0x5F, 0x01, 0x6D, 0x69, 0x46,
0x02, 0x6E, 0x5F, 0x02, 0x6C, 0x57, 0x5B, 0x54, 0x4C, 0x00};
char flag[20] ="123321";
sub_401590(flag,table,20);
printf(flag);
return 0;
}
unsigned int __cdecl sub_401590(char* lpString, char *a2, unsigned int a3)
{
unsigned int result; // eax
unsigned int i; // [esp+4Ch] [ebp-Ch]
unsigned int v5; // [esp+54h] [ebp-4h]
v5 = strlen(lpString);
for ( i = 0; ; ++i )
{
result = i;
if ( i >= a3 )
break;
*(char *)(i + a2) ^= lpString[i % v5];
}
printf(a2);
return result;
}
flag{n0_Zu0_n0_die}





















 8330
8330











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








