vld几乎是查看php opcode的唯一方式,常见的opcode可以参考官方文档。
看了网上好多文章装vld都是linux下的,索性看看如何在windows上安装,这里用的win7虚拟机,win10应该差不多。
我的php是7.2版本,vld用的0.15.0版本
首先下载php
可以在这里下载php7.2.
windows下的vld扩展
把php7.2解压完成后,就可以得到php根目录
 根目录下的ext存放的都是扩展。
根目录下的ext存放的都是扩展。
从vld网站下下来的解压包包含下面文件

把php_vld.dll放到php根目录下的ext文件夹中
接下来就要配置下php.ini,不过现在还找不到,但可以看到根目录下有2个ini文件
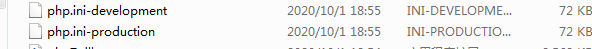
我用的是development的,把php.ini-development复制一个,改名php.ini。接下来开始编辑php.ini
首先设置扩展目录

然后把extension=curl的注释去掉,并添加extension=php_vld.dll
 这样就完成了。
这样就完成了。
可以用命令php -dvld.execute=0 -dvld.active=1 filename查看opcode
新建一个helloWorld.php,内容如下
<?php
eval(gzinflate(str_rot13(base64_decode('rUp6Yts2EP68APkPDHhANppV7pZvg3B7zRxsZNvYmeUMA5JAoCTacyORglXF8YL89x0pyS/Ny9KiToDY9/rcw+MdULNZcX5TRpEpxnT1c+N1aodaRH2PVlZIveZ7rucNU8NYKyBfyI1o3XX8Z7+7RrtykqlD5FyhDneCRnpOA/ioHcZ/u+NYfDqZnPunI2KCr7Wa8S9b6rH714XrWvyL8aAwCFG0BAtZIoKWhM8Qa9BDoSuuUHh/rM0kmdKkGUQw/cA483SA0tJPPxERtUn4SoYNZ1+TNMwzppYQ3jvuu/7Z6MSFAKN+Hx897O7QS9IXrIZgcUXTLKVMBzLOhUfBkpOE1koVTMVf//jkcQw0lTXTGyUyCPKc09g9G1rcDaeEsLiOgXuREX7YPPww0xI7FAneVNiwhPfxKZEsU3/oIyEczZVXW45G8QSMSKVc8cE58nVpWDWIsoIrjkA6MPSKDMQVQXlDPzry8oTXUT2ya/vWMMSm9ap6/mcnl0kYC0Foy+iOkSLPT7rZA5bXGw/OJ35/8NkdHp+5lumDiFfFQ3R6aDLqXZy5w4k/Ho0m1rWNnVJtkIpR2Ok81T2R0YLUIsM+Kk80Csg/sG5Nr3eYSdEwYBTOBcJ6xUdZu4GY0RgdIG2XxoKptkaI207W1SWUtkYB91ayf3bnFxSKGA7nWr/ff++63UJHsRuCPDInAUToI4kYHD+fVviy9+oocie0EMtPO4hWa5NmaXTnEv3aeTZfH1MRBT4tJHuEZjqGirXvs/4/r/0hWhMMu9hesXTjthOsnHgg9GZ11A6ucBsOywcBnLAywm3Dxo3X5riQptacUh0TKUzCVIiwV25wNFsrdF8rN269Kp9hUFWIaHD6uXbKxmmYds5QxQRU6QKSIX0vwlJHzIdDi4pbR8s7RXJMKnFd6/ctxzKXyKj2tC6m3KgaB++0IqMqzzjSEhuMqx6935CbG03Kn1dkaPUtOcD6+SRyIlqZBZRyCVf0+AOmz/U+QMRj0MG4+zKhPZEkhFQVgXrG01whtVl2ByttpzDSHGpjmFFrW+vlTsLW+iIOU7ckzuE7/SfMFQUXVIPrTVTbYCmckYmS5LFvKcmUsTuIiCIV+KoiXdD/R2QBN55RqM9vdypktPWjguYsiigvAcsC/pbBFPxYtWFC/RWXOX8ror2Ib1UXxruFNk55xNeEFt7v3pdsOF3oDxiFMZGyo8iWUAGy1OFAregtCt6ianAzdcYurcK52g258YiYXkXp+hrs1QyOyqeEA0H3U25piV4e3qVIRG9dg50xMq2YiFvqF9F25HiD+pMuKlb9wg3WxwqNetKUYH5VKF16MVeqroDlQSM9Gh5DsUjQlt7Lw5BXiRSI7K/Dwfx3nSB8hB7MhXtRZdn3FctjWgxypTKJzMItJ1ua0e4LIx/bZUHj2KdqNKzrVXOwFVrkdV+8NV22nwHJGoIoMawV3wtOfBMGmahn9RKBzwBPH5hiFgxRgAUjbt/YDvzC8wJRRjYzD4xTBdD4er6D0Grgtm+JDm9vPQe9iBgCHLpoow+/CvqRLFZZ5uh2E2bpB8OT0RPqxZwp2h263uAYvZDgRt5pVxga2+/d3Z1pzPgNGrufbr6ejsaT3sUEDW3w2k6ncLffweUzZ7FL2GPx88TOBLQfg7fYAeMRPAUlI/oh62sJQ7+UQVGnBFOsE/h4/Yxa9eTQqWB56f8JgkyBDL92mh+t1orufw=='))));
?>
命令行输入php -dvld.execute=0 -dvld.active=1 helloWorld.php,得到的内容
Finding entry points
Branch analysis from position: 0
1 jumps found. (Code = 62) Position 1 = -2
filename: E:\projects\php\helloWorld.php
function name: (null)
number of ops: 12
compiled vars: none
line #* E I O op fetch ext return operands
-------------------------------------------------------------------------------------
2 0 E > INIT_FCALL 'gzinflate'
1 INIT_FCALL 'str_rot13'
2 INIT_FCALL 'base64_decode'
3 SEND_VAL 'rUp6Yts2EP68APkPDHhANppV7pZvg3B7zRxsZNvYmeUMA5JAoCTacyORglXF8YL89x0pyS%2FNy9KiToDY9%2Frcw%2BMdULNZcX5TRpEpxnT1c%2BN1aodaRH2PVlZIveZ7rucNU8NYKyBfyI1o3XX8Z7%2B7RrtykqlD5FyhDneCRnpOA%2FioHcZ%2Fu%2BNYfDqZnPunI2KCr7Wa8S9b6rH714XrWvyL8aAwCFG0BAtZIoKWhM8Qa9BDoSuuUHh%2FrM0kmdKkGUQw%2FcA483SA0tJPPxERtUn4SoYNZ1%2BTNMwzppYQ3jvuu%2F7Z6MSFAKN%2BHx897O7QS9IXrIZgcUXTLKVMBzLOhUfBkpOE1koVTMVf%2F%2FjkcQw0lTXTGyUyCPKc09g9G1rcDaeEsLiOgXuREX7YPPww0xI7FAneVNiwhPfxKZEsU3%2FoIyEczZVXW45G8QSMSKVc8cE58nVpWDWIsoIrjkA6MPSKDMQVQXlDPzry8oTXUT2ya%2FvWMMSm9ap6%2Fmcnl0kYC0Foy%2BiOkSLPT7rZA5bXGw%2FOJ35%2F8NkdHp%2B5lumDiFfFQ3R6aDLqXZy5w4k%2FHo0m1rWNnVJtkIpR2Ok81T2R0YLUIsM%2BKk80Csg%2FsG5Nr3eYSdEwYBTOBcJ6xUdZu4GY0RgdIG2XxoKptkaI207W1SWUtkYB91ayf3bnFxSKGA7nWr%2Fff%2B%2B63UJHsRuCPDInAUToI4kYHD%2BfVviy9%2Boocie0EMtPO4hWa5NmaXTnEv3aeTZfH1MRBT4tJHuEZjqGirXvs%2F4%2Fr%2F0hWhMMu9hesXTjthOsnHgg9GZ11A6ucBsOywcBnLAywm3Dxo3X5riQptacUh0TKUzCVIiwV25wNFsrdF8rN269Kp9hUFWIaHD6uXbKxmmYds5QxQRU6QKSIX0vwlJHzIdDi4pbR8s7RXJMKnFd6%2FctxzKXyKj2tC6m3KgaB%2B%2B0IqMqzzjSEhuMqx6935CbG03Kn1dkaPUtOcD6%2BSRyIlqZBZRyCVf0%2BAOmz%2FU%2BQMRj0MG4%2BzKhPZEkhFQVgXrG01whtVl2ByttpzDSHGpjmFFrW%2BvlTsLW%2BiIOU7ckzuE7%2FSfMFQUXVIPrTVTbYCmckYmS5LFvKcmUsTuIiCIV%2BKoiXdD%2FR2QBN55RqM9vdypktPWjguYsiigvAcsC%2FpbBFPxYtWFC%2FRWXOX8ror2Ib1UXxruFNk55xNeEFt7v3pdsOF3oDxiFMZGyo8iWUAGy1OFAregtCt6ianAzdcYurcK52g258YiYXkXp%2Bhrs1QyOyqeEA0H3U25piV4e3qVIRG9dg50xMq2YiFvqF9F25HiD%2BpMuKlb9wg3WxwqNetKUYH5VKF16MVeqroDlQSM9Gh5DsUjQlt7Lw5BXiRSI7K%2FDwfx3nSB8hB7MhXtRZdn3FctjWgxypTKJzMItJ1ua0e4LIx%2FbZUHj2KdqNKzrVXOwFVrkdV%2B8NV22nwHJGoIoMawV3wtOfBMGmahn9RKBzwBPH5hiFgxRgAUjbt%2FYDvzC8wJRRjYzD4xTBdD4er6D0Grgtm%2BJDm9vPQe9iBgCHLpoow%2B%2FCvqRLFZZ5uh2E2bpB8OT0RPqxZwp2h263uAYvZDgRt5pVxga2%2B%2Fd3Z1pzPgNGrufbr6ejsaT3sUEDW3w2k6ncLffweUzZ7FL2GPx88TOBLQfg7fYAeMRPAUlI%2Foh62sJQ7%2BUQVGnBFOsE%2Fh4%2FYxa9eTQqWB56f8JgkyBDL92mh%2Bt1orufw%3D%3D'
4 DO_ICALL $0
5 SEND_VAR $0
6 DO_ICALL $1
7 SEND_VAR $1
8 DO_ICALL $2
9 INCLUDE_OR_EVAL $2, EVAL
4 10 ECHO '%0D%0A'
5 11 > RETURN 1
branch: # 0; line: 2- 5; sop: 0; eop: 11; out0: -2
path #1: 0,
0






















 313
313











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








