NTRU(number theory reserach unit/Nth DegreeTruncated Polynomial Ring—N次截断多项式环问题)是设计在多项式环上的公钥密码系统,它基于多项式代数,安全性基于格中寻找最短向量困难问题(SVP)
文章目录
基本概念重申
SVP:在格L中寻找一个最短的非零向量v∈L,使它的欧几里得范数||v||最小。
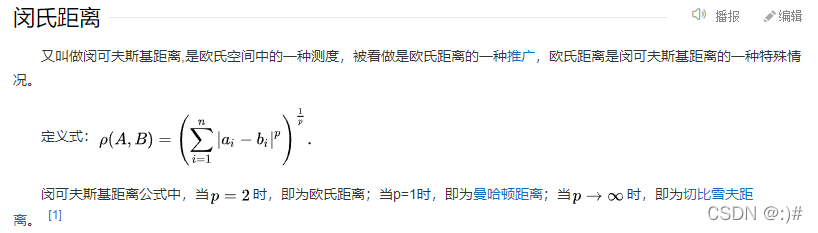
P范数(P norm):║x║p=(|x1|p+|x2|p+…+|xn|p){1/p}
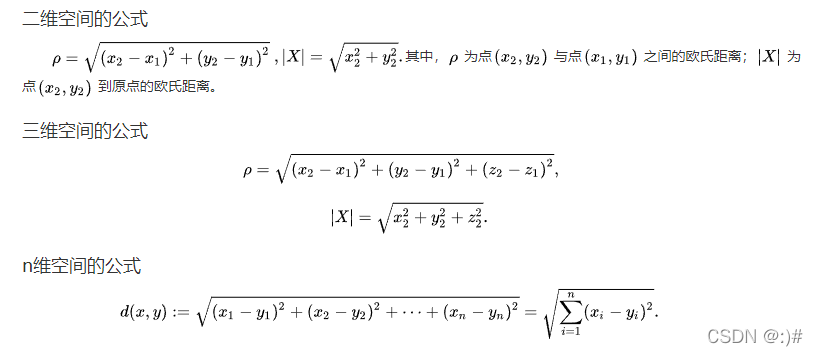
在数学中,欧几里得距离(Euclidean Metric,Euclidean Distance)或欧几里得度量是欧几里得空间中两点间“普通”(即直线)距离。使用这个距离,欧氏空间成为度量空间。相关联的范数称为欧几里得范数。较早的文献称之为毕达哥拉斯度量。
欧几里得范数(Euclidean norm)== 欧式长度(距离) == L2范数 == L2距离
Euclidean norm == Euclidean length == L2 norm == L2 distance == ι 2 \iota ^{2} ι2 norm
最大公约数:记为(a,b)
最小公倍数:记为[a,b]
若干个互质数的最小公倍数为它们的乘积的绝对值。
常见范数计算方法:
给定向量x=(x1,x2,...xn)
L1范数 = ||x||1 = 向量各个元素绝对值之和 = x与0之间的曼哈顿距离
L2范数 = ||x||2 = 向量各个元素的平方求和然后求平方根 = x与0之间的欧式距离
Lp范数 = ||x||p = 向量各个元素绝对值的p次方求和然后求1/p次方
L∞范数 = ||x||∞ = 向量各个元素求绝对值,最大那个元素的绝对值
一、NTRU
1.特点
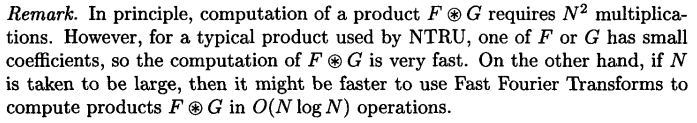
2.Scheme — Key Generation
- Random chooses 2 polynomials f , g ∈ L g f,g ∈ L^g f,g∈Lg
f f f must satify the additional requirement that it have inverses modulo q and modulo p.
Denote these inverses by F q a n d F p , F_q and F_p , FqandFp,that is
F q ∗ f = 1 m o d q F_q*f = 1 mod q Fq∗








 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章


















 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








