Kali ettercap DNS欺骗
实验环境
Kali IP:192.168.195.128
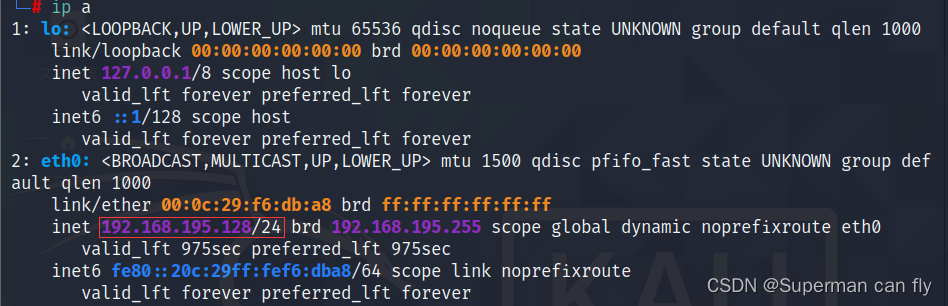
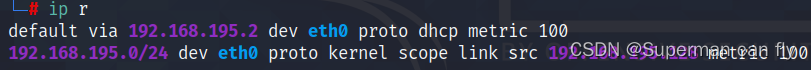
gateway 192.168.195.2
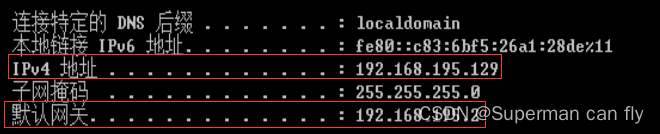
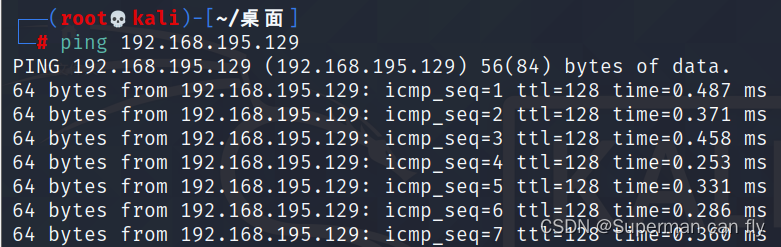
Winser2008R2 IP:192.168.195.129 gateway:192.168.195.2
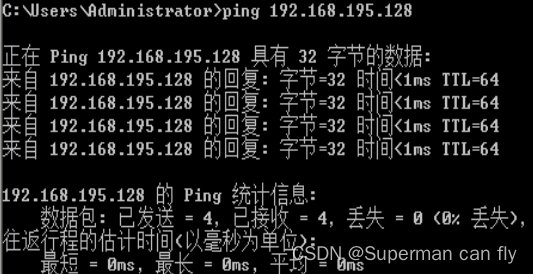
网络互通:Winser2008R2 ping kali
网络互通:kali ping Winser2008R2
实验步骤
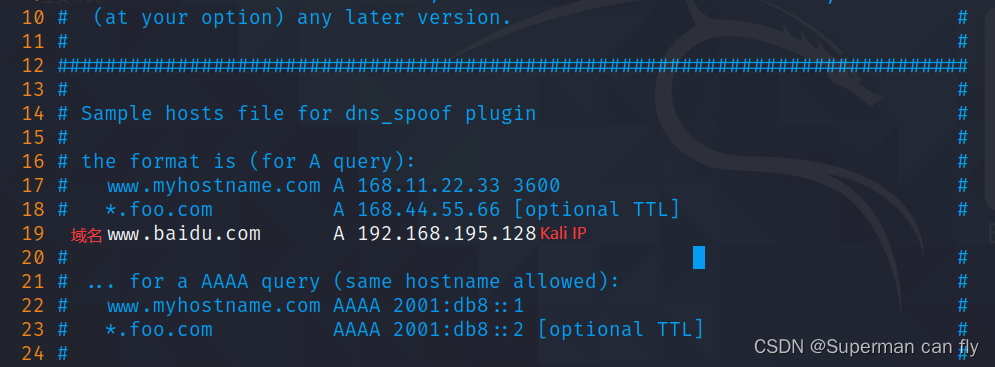
修改ettercap解析文件
vim /etc/ettercap/etter.dns
apache服务
启动apache服务 ┌──(root💀kali)-[/var/www/html] └─# systemctl start apache2 查看apache服务 ┌──(root💀kali)-[/var/www/html] └─# systemctl status apache2 ● apache2.service - The Apache HTTP Server Loaded: loaded (/lib/systemd/system/apache2.service; enabled; vendor p> Active: active (running) since Wed 2023-11-01 14:12:51 CST; 36min ago Docs: https://httpd.apache.org/docs/2.4/ Process: 1772 ExecStart=/usr/sbin/apachectl start (code=exited, status=> Main PID: 1783 (apache2) Tasks: 6 (limit: 4915) Memory: 15.1M CGroup: /system.slice/apache2.service ├─1783 /usr/sbin/apache2 -k start ├─1785 /usr/sbin/apache2 -k start ├─1786 /usr/sbin/apache2 -k start ├─1787 /usr/sbin/apache2 -k start ├─1788 /usr/sbin/apache2 -k start └─1789 /usr/sbin/apache2 -k start 11月 01 14:12:51 kali systemd[1]: Starting The Apache HTTP Server... 11月 01 14:12:51 kali apachectl[1782]: AH00558: apache2: Could not reliably> 11月 01 14:12:51 kali systemd[1]: Started The Apache HTTP Server.
ettercap
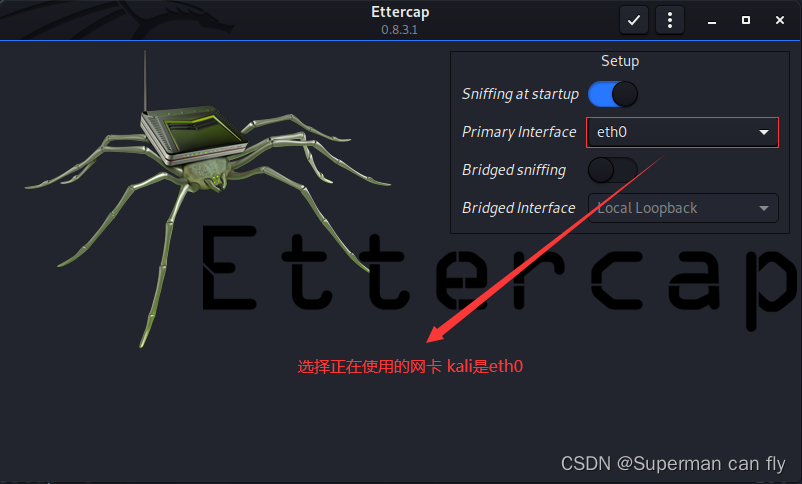
图形化启动ettercap ┌──(root💀kali)-[/var/www/html] └─# ettercap -G
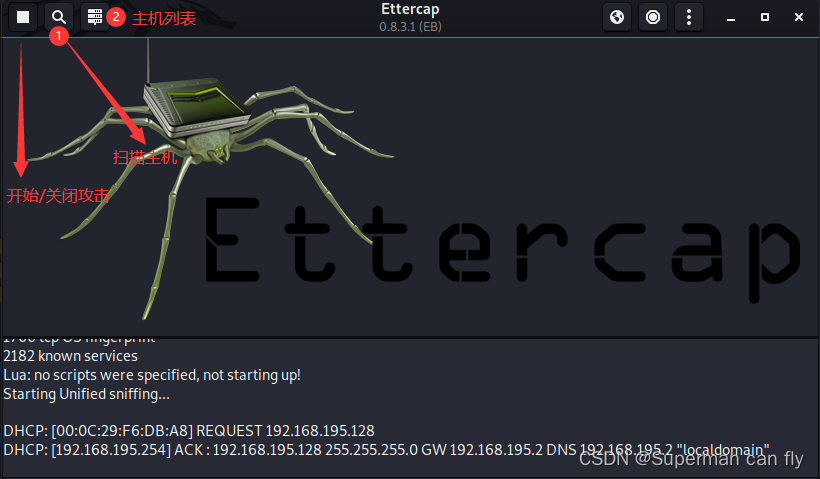

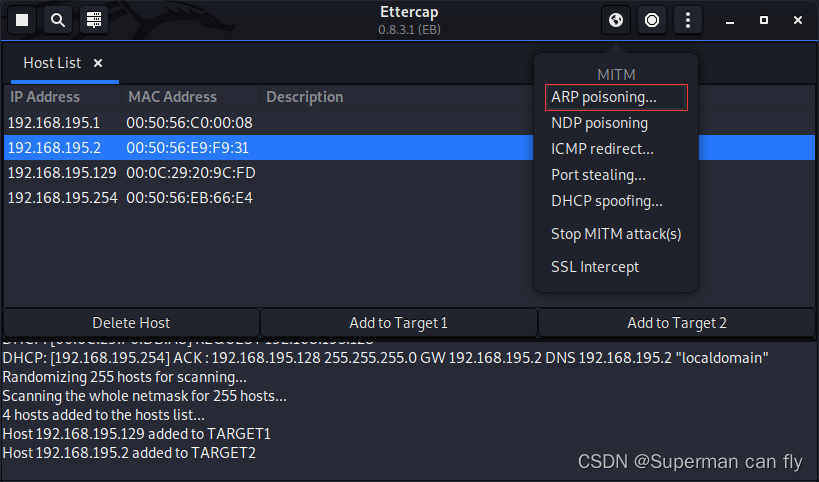
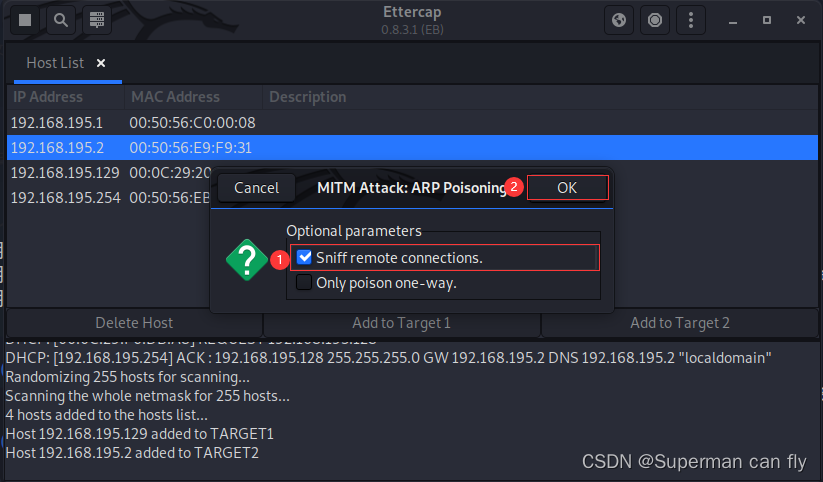
选择ARP攻击
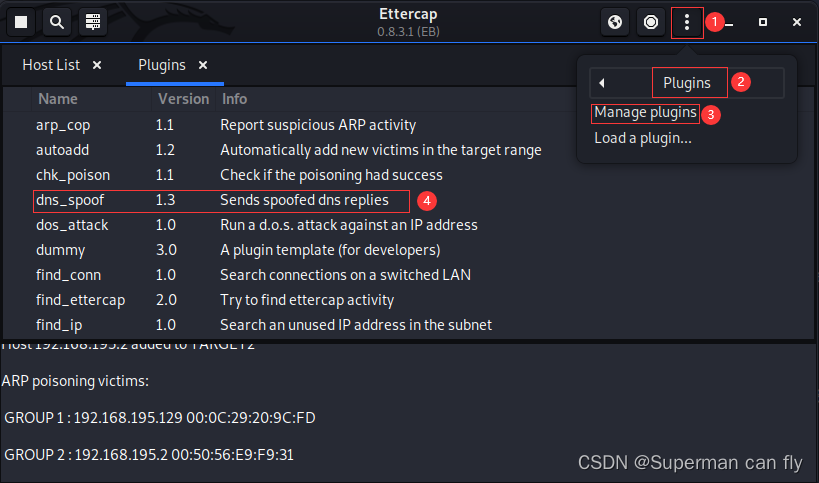
选择DNS欺骗攻击插件
验证
打开Winser2008R2,在IE中搜索http://www.baidu.com

发现百度的页面变为Apache的默认页面,DNS欺骗成功






















 402
402











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








