前言:一般解密RSA需要写脚本,但是由于p,q数值太大,本人的编译器无法运行,后来发现网上一个好用的小工具
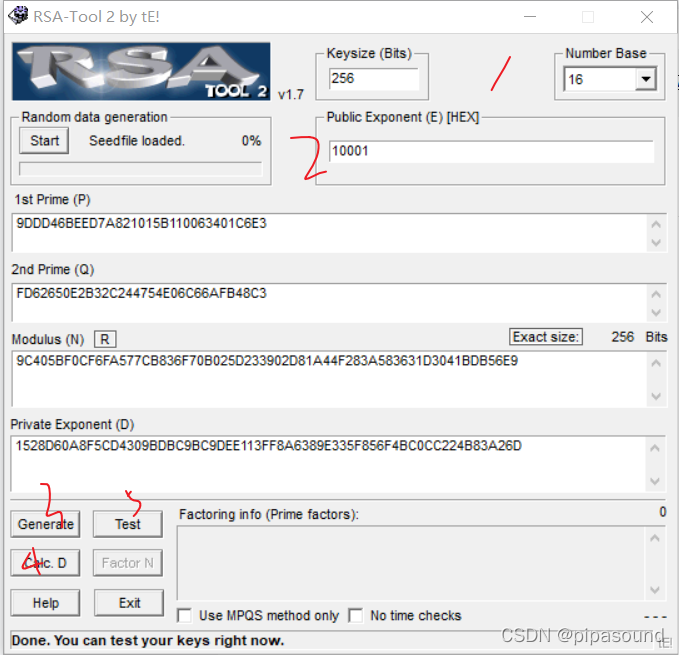
- 1,看给的条件情况,若全是数字就是十进制,有字母试试十六进制
- 2,此工具的e需转成十六进制
- 若条件给了N,点击3可转成素数p,q
- 因为n=p*q,所以有了p和q就能转成N,点击Cale.D自动生成N,D
- 最后点击test进行测试
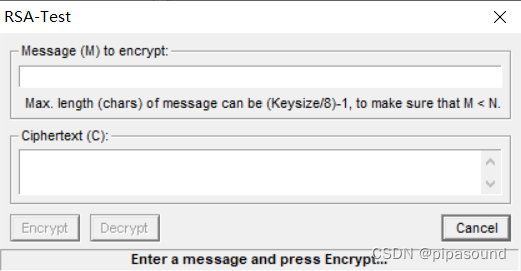
- 刚开始在M里面输入值,只会有Encrypt(加密)可以点击,随便输个明文后点击EN,此时才能使用Decrypt(解密).
- 注意密文的进制,若是十六进制应转成十进制








 本文介绍了如何使用在线RSA解密工具,包括判断输入数值的进制、转换素数及生成解密参数,并提供了详细的操作步骤,如从给定条件转换N、D,以及进行加密和解密操作。该工具特别适用于处理大数值时编译器无法运行的情况。
本文介绍了如何使用在线RSA解密工具,包括判断输入数值的进制、转换素数及生成解密参数,并提供了详细的操作步骤,如从给定条件转换N、D,以及进行加密和解密操作。该工具特别适用于处理大数值时编译器无法运行的情况。
















 303
303

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








