拜读wp:
- 2024 H&NCTF WriteUP-CSDN博客
- https://www.52pojie.cn/thread-1924143-1-1.html
涉及到的知识点:
RC4流密码
hashcat工具的使用
解释性语言代码混淆
题目原代码:
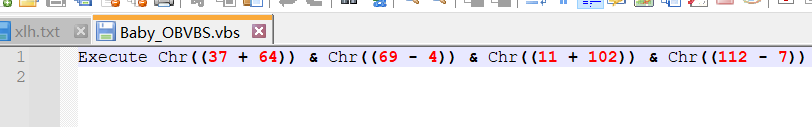
被混淆了直接将Execute改成输出语句就可以得到被混淆的源码了~
解混淆代码:代码太长就不贴完整的了自己补全
Dim expression
expression = Chr((37 + 64))......0)) & Chr((47 - 7)) & Chr((51 * 2.03921568627451)) & Chr((163 - 74)) & Chr((159 - 83)) & Chr((106 + 11)) & Chr((77 - 36))
Dim outputFilePath
outputFilePath = "decode.txt"
Dim fso, outputFile
Set fso = CreateObject("Scripting.FileSystemObject")
Set outputFile = fso.CreateTextFile(outputFilePath, True)
outputFile.WriteLine(expression)
outputFile.Close
成功解出混淆发现还有一个base64混淆: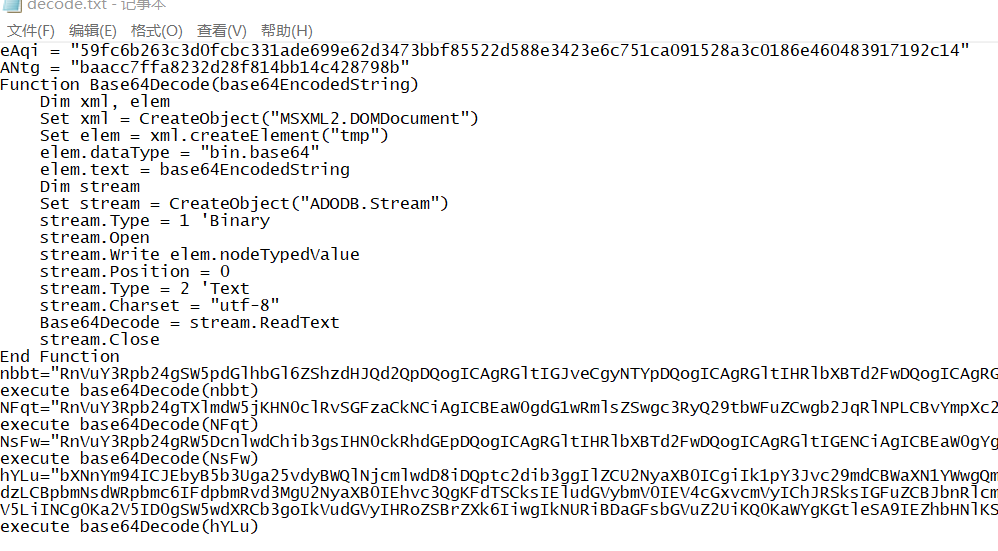
继续使用vbs解密混淆:通用的逻辑直接将代码输出出来就好!
Function Base64Decode(base64EncodedString)
Dim xml, elem
Set xml = CreateObject("MSXML2.DOMDocument")
Set elem = xml.createElement("tmp")
elem.dataType = "bin.base64"
elem.text = base64EncodedString
Dim stream
Set stream = CreateObject("ADODB.Stream")
stream.Type = 1 'Binary
stream.Open
stream.Write elem.nodeTypedValue
stream.Position = 0
stream.Type = 2 'Text
stream.Charset = "utf-8"
Base64Decode = stream.ReadText
stream.Close
End Function
nbbt="RnVuY3R.....24="
NFqt="RnVuY3Rpb24gT...dGlvbg=="
NsFw="RnVuY3Rpb24gRW5Dcn...5jdGlvbg=="
hYLu="bXNnYm94ICJEbyB5b3Uga25vdyBWQlNjcmlwdD8iDQptc2dib3ggIlZCU2NyaXB0ICgiIk1pY3Jvc29mdCBWaXN1YWwgQmFzaWMgU2NyaXB0aW5nIEV..."
Dim outputFilePath
outputFilePath = "decode1.txt"
Dim fso, outputFile
Set fso = CreateObject("Scripting.FileSystemObject")
Set outputFile = fso.CreateTextFile(outputFilePath, True)
outputFile.WriteLine(base64Decode(nbbt)& vbCr & vbLf & base64Decode(NFqt)& vbCr & vbLf & base64Decode(NsFw)& vbCr & vbLf & base64Decode(hYLu))
outputFile.Close
最后的解密结果是这个:
Function Base64Decode(base64EncodedString)
Dim xml, elem
Set xml = CreateObject("MSXML2.DOMDocument")
Set elem = xml.createElement("tmp")
elem.dataType = "bin.base64"
elem.text = base64EncodedString
Dim stream
Set stream = CreateObject("ADODB.Stream")
stream.Type = 1 'Binary
stream.Open
stream.Write elem.nodeTypedValue
stream.Position = 0
stream.Type = 2 'Text
stream.Charset = "utf-8"
Base64Decode = stream.ReadText
stream.Close
End Function
Function Initialize(strPwd)
Dim box(256)
Dim tempSwap
Dim a
Dim b
For i = 0 To 255
box(i) = i
Next
a = 0
b = 0
For i = 0 To 255
a = (a + box(i) + Asc(Mid(strPwd, (i Mod Len(strPwd)) + 1, 1))) Mod 256
tempSwap = box(i)
box(i) = box(a)
box(a) = tempSwap
Next
Initialize = box
End Function
Function Myfunc(strToHash)
Dim tmpFile, strCommand, objFSO, objWshShell, out
Set objFSO = CreateObject("Scripting.FileSystemObject")
Set objWshShell = CreateObject("WScript.Shell")
tmpFile = objFSO.GetSpecialFolder(2).Path & "\" & objFSO.GetTempName
objFSO.CreateTextFile(tmpFile).Write(strToHash)
strCommand = "certutil -hashfile " & tmpFile & " MD5"
out = objWshShell.Exec(strCommand).StdOut.ReadAll
msgbox out
objFSO.DeleteFile tmpFile
Myfunc = Replace(Split(Trim(out), vbCrLf)(1), " ", "")
End Function
Function EnCrypt(box, strData)
Dim tempSwap
Dim a
Dim b
Dim x
Dim y
Dim encryptedData
encryptedData = ""
For x = 1 To Len(strData)
a = (a + 1) Mod 256
b = (b + box(a)) Mod 256
tempSwap = box(a)
box(a) = box(b)
box(b) = tempSwap
y = Asc(Mid(strData, x, 1)) Xor box((box(a) + box(b)) Mod 256)
encryptedData = encryptedData & LCase(Right("0" & Hex(y), 2))
Next
EnCrypt = encryptedData
End Function
eAqi = "59fc6b263c3d0fcbc331ade699e62d3473bbf85522d588e3423e6c751ca091528a3c0186e460483917192c14"
ANtg = "baacc7ffa8232d28f814bb14c428798b"
key = InputBox("Enter the key:", "CTF Challenge")
if (key = False) then wscript.quit
if (len(key)<>6) then
wscript.echo "wrong key length!"
wscript.quit
end if
If (Myfunc(key) = ANtg) Then
wscript.echo "You get the key!Move to next challenge."
Else
wscript.echo "Wrong key!Try again!"
wscript.quit
End If
userInput = InputBox("Enter the flag:", "CTF Challenge")
if (userInput = False) then wscript.quit
if (len(userInput)<>44) then
wscript.echo "wrong!"
wscript.quit
end if
box = Initialize(key)
encryptedInput = EnCrypt(box, userInput)
If (encryptedInput = eAqi) Then
MsgBox "Congratulations! You have learned VBS!"
Else
MsgBox "Wrong flag. Try again."
End If
wscript.echo "bye!"
发现主要逻辑:
- 首先输入key作为rc4的密钥,但是只知道key的hash值和key的长度为6
- 输入的flag是44个字节结果与eAqi进行比较判断flag的正确性
由于key的长度是确定的可以直接使用kali自带的hash解密工具来爆破出key的值!
使用方法:https://blog.csdn.net/smli_ng/article/details/106111493
baacc7ffa8232d28f814bb14c428798b:H&NKEY
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 0 (MD5)
Hash.Target......: baacc7ffa8232d28f814bb14c428798b
Time.Started.....: Thu May 16 00:49:03 2024 (2 mins, 11 secs)
Time.Estimated...: Thu May 16 00:51:14 2024 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Mask.......: ?a?a?a?a?a?a [6]
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 128.9 MH/s (1.78ms) @ Accel:512 Loops:128 Thr:1 Vec:8
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 15483021312/735091890625 (2.11%)
Rejected.........: 0/15483021312 (0.00%)
Restore.Point....: 1714176/81450625 (2.10%)
Restore.Sub.#1...: Salt:0 Amplifier:6016-6144 Iteration:0-128
Candidate.Engine.: Device Generator
Candidates.#1....: 6W{t ! -> QjDLEY
Hardware.Mon.#1..: Util: 92%
Started: Thu May 16 00:48:31 2024
Stopped: Thu May 16 00:51:16 2024
解出key的值那么接下来就算上py脚本解密出flag了!
from Crypto.Cipher import ARC4
def rc4_decrypt(key, encrypt_data):
"""
RC4 decryption using the Crypto.Cipher library
"""
cipher = ARC4.new(key)
decrypted_data = cipher.decrypt(encrypt_data)
return decrypted_data
# Example usage
key = b'H&NKEY'
encrypt_data = bytes.fromhex("59fc6b263c3d0fcbc331ade699e62d3473bbf85522d588e3423e6c751ca091528a3c0186e460483917192c14")
decrypted_data = rc4_decrypt(key, encrypt_data)
print(decrypted_data.decode())
























 1826
1826

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








