一、安装相关依赖工具
yum install -y git wget epel-release
yum install -y gcc-c++ flex bison yajl yajl-devel curl-devel curl GeoIP-devel doxygen zlib-devel pcre-devel lmdb-devel libxml2-devel ssdeep-devel lua-devel libtool autoconf automake
二、安装Modsecurity
cd /usr/local
git clone https://github.com/SpiderLabs/ModSecurity
cd ModSecurity
git checkout -b v3/master origin/v3/master # 这里会报个错,没问题
git submodule init
git submodule update
sh build.sh
./configure
make
make install
三、安装nginx与ModSecurity-nginx
cd /usr/local
git clone https://github.com/SpiderLabs/ModSecurity-nginx
wget http://nginx.org/download/nginx-1.16.1.tar.gz
tar -xvzf nginx-1.16.1.tar.gz
cd /usr/local/nginx-1.16.1
./configure --add-module=/usr/local/ModSecurity-nginx
make
make install
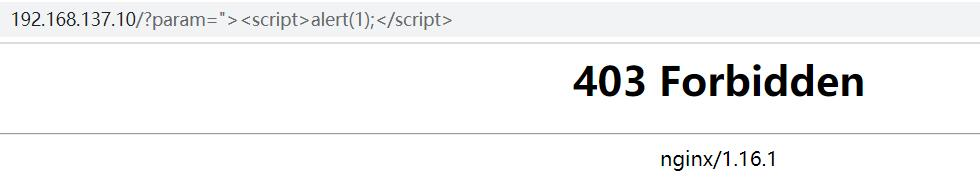
四、测试效果
启动nginx
/usr/local/nginx/sbin/nginx
模拟攻击,测试未启动ModSecurity时的访问效果,访问URL为:http://服务器IP/?param=%22%3E%3Cscript%3Ealert(1);%3C/script%3E

五、最后配置:
创建用于存在配置文件的文件夹
mkdir /usr/local/nginx/conf/modsecurity
cp -r /usr/local/ModSecurity/modsecurity.conf-recommended /usr/local/nginx/conf/modsecurity/
mv /usr/local/nginx/conf/modsecurity/modsecurity.conf-recommended /usr/local/nginx/conf/modsecurity/modsecurity.conf
cp -r /usr/local/ModSecurity/unicode.mapping /usr/local/nginx/conf/modsecurity/
将/usr/local/Modsecurity/modsecurity.conf-recommended复制到/usr/local/nginx/conf/modsecurity,并重命名为modsecurity.conf;
将/usr/local/Modsecurity/unicode.mapping复制到/usr/local/nginx/conf/modsecurity;
wget http://www.modsecurity.cn/download/corerule/owasp-modsecurity-crs-3.3-dev.zip
unzip owasp-modsecurity-crs-3.3-dev.zip
cp -r owasp-modsecurity-crs-3.3-dev/crs-setup.conf.example /usr/local/nginx/conf/modsecurity/crs-setup.conf
cp -r owasp-modsecurity-crs-3.3-dev/rules/ /usr/local/nginx/conf/modsecurity/
cd /usr/local/nginx/conf/modsecurity/rules/
mv REQUEST-900-EXCLUSION-RULES-BEFORE-CRS.conf.example REQUEST-900-EXCLUSION-RULES-BEFORE-CRS.conf
mv RESPONSE-999-EXCLUSION-RULES-AFTER-CRS.conf.example RESPONSE-999-EXCLUSION-RULES-AFTER-CRS.conf
下载规则文件压缩包,解压后复制crs-setup.conf.example到/usr/local/nginx/conf/modsecurity/下并重命名为crs-setup.conf;
复制rules文件夹到/usr/local/nginx/conf/modsecurity/下,同时修改REQUEST-900-EXCLUSION-RULES-BEFORE-CRS.conf.example与RESPONSE-999-EXCLUSION-RULES-AFTER-CRS.conf.example两个文件的文件名,将".example"删除,可将自己写的规则放置于此两个文件中;
编辑nginx.conf
在http或server节点中添加以下内容(在http节点添加表示全局配置,在server节点添加表示为指定网站配置):
vim /usr/local/nginx/conf/nginx.conf
modsecurity on;
modsecurity_rules_file /usr/local/nginx/conf/modsecurity/modsecurity.conf;
编辑modsecurity.conf
SecRuleEngine DetectionOnly改为SecRuleEngine On
同时添加以下内容:
Include /usr/local/nginx/conf/modsecurity/crs-setup.conf
Include /usr/local/nginx/conf/modsecurity/rules/*.conf
六、重新加载Nginx测试效果
/usr/local/nginx/sbin/nginx -s reload
七、其他补充
如果要确保ModSecurity v3.0.3在记录审计日志时保存请求体,SecAuditLogParts需要添加配置C,而不是IJ,否则审计日志将无法记录请求体
另外贴一下 ModSecurity 地址
中文官网:http://www.modsecurity.cn/
规则集地址:https://github.com/coreruleset/coreruleset
github:https://github.com/SpiderLabs/ModSecurity
小知识:
如何隐藏nginx版本号?
只需要在http{}里面加入 server_tokens off; 即可






















 2410
2410











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








