(current platform is Ubuntu-8.04-i386-desktop with wireshark 1.0.0 )
=== note ===
if would be convinient if you have root password. Or else if you want to capture packet you can modify settings -for more details, see http://www.wireshark.org/lists/wireshark-dev/200809/msg00168.html
=== Build wireshark ===
* extract source files under /wireshark, and execute "sudo ./autogen.sh && sudo./configure && sudo make install" in command line, under this directory
* install libgtk2.0-dev and libpcap-dev, otherwise you may get confusing error message. Then install other packages reported in error messages.
* type "make" and wait until make finished
* type "sudo ./wireshark" to start, then specify Capture->Option->Interface. Then click Capture->Interface->Start. Now you can see packets captured.
=== Setup Testing environment ===
* Create following java file to generate simple UDP traffic
* To verify that you can capture program generated traffic, open wireshark, capture the traffic of above java program. ("udp && !dns && bootp" can be used as filter).
* As a preparation for generating traffic needed for dissector (refer to http://www.wireshark.org/docs/wsdg_html_chunked/ChDissectAdd.html ), change above above code to below:
=== write plugin ===
* create directory foo under /wireshark/plugins/ * create packet-foo.c with the following code:
* copy rest of files from agentx to foo directory, and replace all "agentx" with "foo" inside them.
* referring to the places of agentx, you will also need to change the files found by the following command:
- cd wireshark && grep agentx -l * * /* */ */* >& tmp.txt && cat tmp.txt | grep -v doc/ | grep -v agentx/ | grep -v wireshark-gtk
* execute following command to rebuild wireshark with plugin
- ./autogen.sh && ./configure --prefix=${HOME}/build/root && make install
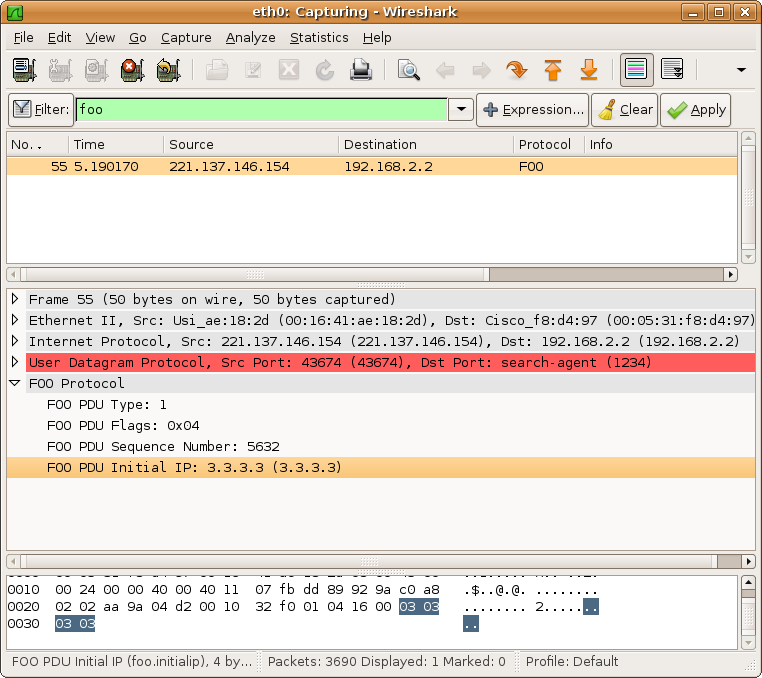
* now run wireshark and execute the java program to send traffic, you will find that, packet has been recognized as FOO protocol
* modify packet-foo.c into following content(for code explanation see http://www.wireshark.org/docs/wsdg_html_chunked/ChDissectAdd.html ).
* at this moment, re-build wireshark and run it, you can see the follow screen:
























 943
943

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








