流量控制之traffic-filter
-
背景
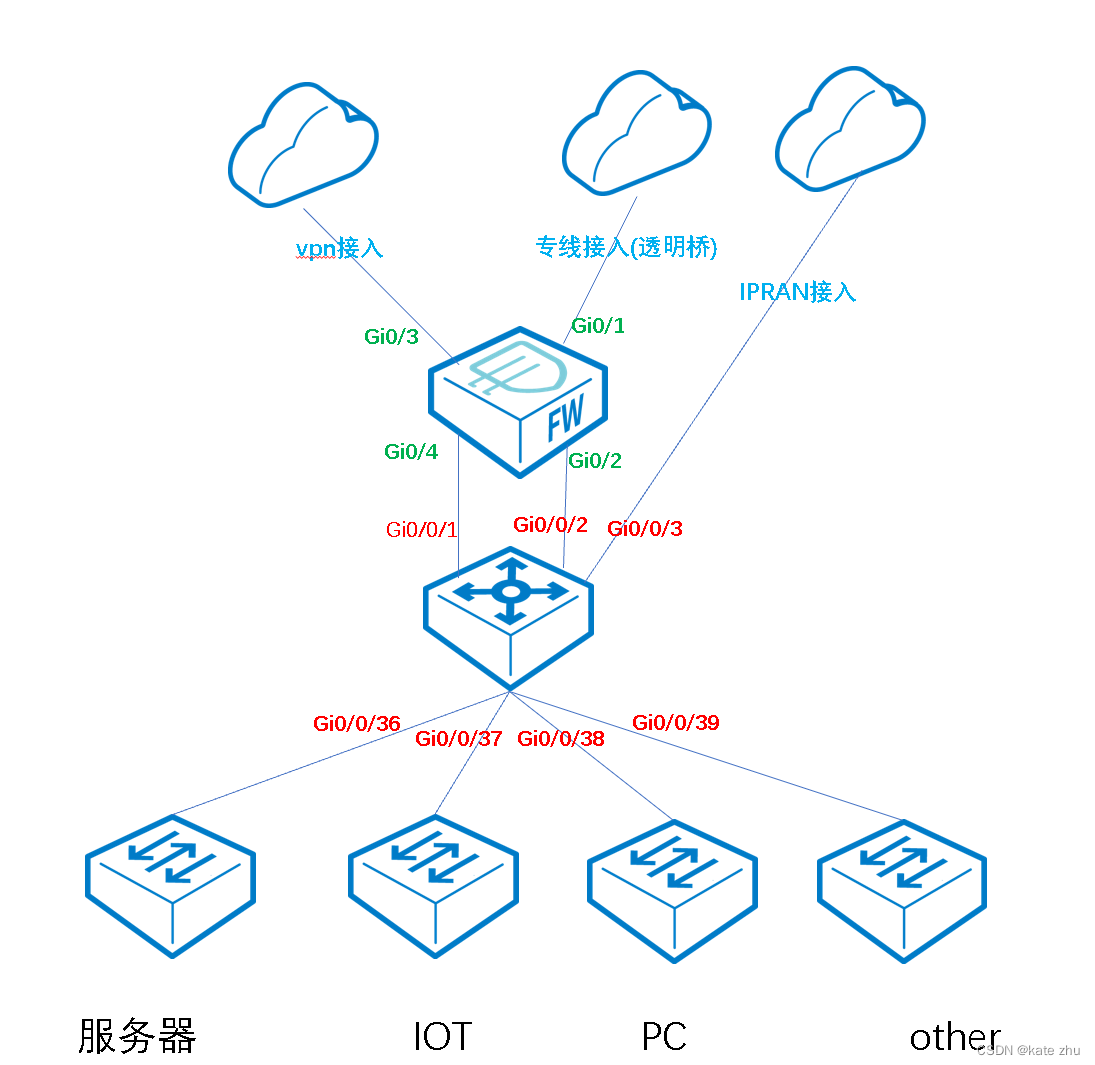
出口防火墙作为企业出口网关,具备入侵防护,病毒防护,访问控制,互联网接入,VPN接入,专线接入等综合性网关;
企业内网核心交换机下挂在出口FW,业务交换机下挂在核心交换机下面;
-
需求
服务器,IOT等区域内网间通信做流量控制。例如:服务器可以被访问,但不能主动访问别人等;分析:业务网关都在核心交换机上面起了vlanif,此时不能通过在防火墙上面做流控,因为网关间通信在核心交换机上面完成,流量不会到防火墙上面去,出口流量才会。
-
配置思路
针对需要做流控策略的地址段使用ACL进行抓取,再到对应的接口进行调用即可。
子网数量:
vlan 250,230,100,252,242;
10.10.0.0/24
10.0.0.0/24
172.18.0.0/16
ACL
acl name vlan250-deny 3991
rule 5 deny ip source 172.22.250.0 0.0.0.255 destination 172.22.242.0 0.0.0.255
rule 10 deny ip source 172.22.250.0 0.0.0.255 destination 172.22.230.0 0.0.0.255
rule 15 deny ip source 172.22.250.0 0.0.0.255 destination 172.22.100.0 0.0.0.255
acl name vlan242-deny 3992
rule 5 deny ip source 172.22.242.0 0.0.0.255 destination 172.22.250.0 0.0.0.255
rule 10 deny ip source 172.22.242.0 0.0.0.255 destination 172.22.252.0 0.0.0.255
rule 15 deny ip source 172.22.242.0 0.0.0.255 destination 172.22.100.0 0.0.0.255
rule 20 deny ip source 172.22.242.0 0.0.0.255 destination 10.10.0.0 0.0.0.255
rule 25 deny ip source 172.22.242.0 0.0.0.255 destination 10.0.0.0 0.0.0.255
rule 30 deny ip source 172.22.242.0 0.0.0.255 destination 172.18.0.0 0.0.255.255
acl name vlan252-deny 3993
rule 5 deny ip source 172.22.252.0 0.0.0.255 destination 172.22.242.0 0.0.0.255
rule 10 deny ip source 172.22.252.0 0.0.0.255 destination 172.22.230.0 0.0.0.255
acl name vlan230-deny 3994
rule 5 deny ip source 172.22.230.0 0.0.0.255 destination 172.22.250.0 0.0.0.255
rule 10 deny ip source 172.22.230.0 0.0.0.255 destination 172.22.252.0 0.0.0.255
rule 15 deny ip source 172.22.230.0 0.0.0.255 destination 172.22.100.0 0.0.0.255
VLAN接口调用
traffic-filter vlan 250 inbound acl name vlan250-deny
traffic-filter vlan 242 inbound acl name vlan242-deny
traffic-filter vlan 252 inbound acl name vlan252-deny
traffic-filter vlan 230 inbound acl name vlan230-deny
配置完成后,
vlan 250无法访问vlan 242,230,100;
vlan 242无法访问vlan 250,252,100,10.10.0.0/24,10.0.0.0/24,172.18.0.0/16;
vlan 252无法访问vlan 242,230;
vlan 230无法访问vlan 250,252,100;











 文章描述了一种在企业网络环境中,通过在核心交换机上的VLAN接口应用ACL规则来实现特定子网间流量控制的方法。配置了多个ACL,如vlan250-deny,vlan242-deny等,禁止了某些VLAN间的特定通信,例如vlan250无法访问vlan242、230、100等。同时,这些ACL也限制了内网某些子网对其他特定网络段的访问,如vlan242对10.10.0.0/24、10.0.0.0/24等的访问。
文章描述了一种在企业网络环境中,通过在核心交换机上的VLAN接口应用ACL规则来实现特定子网间流量控制的方法。配置了多个ACL,如vlan250-deny,vlan242-deny等,禁止了某些VLAN间的特定通信,例如vlan250无法访问vlan242、230、100等。同时,这些ACL也限制了内网某些子网对其他特定网络段的访问,如vlan242对10.10.0.0/24、10.0.0.0/24等的访问。

















 2334
2334

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










