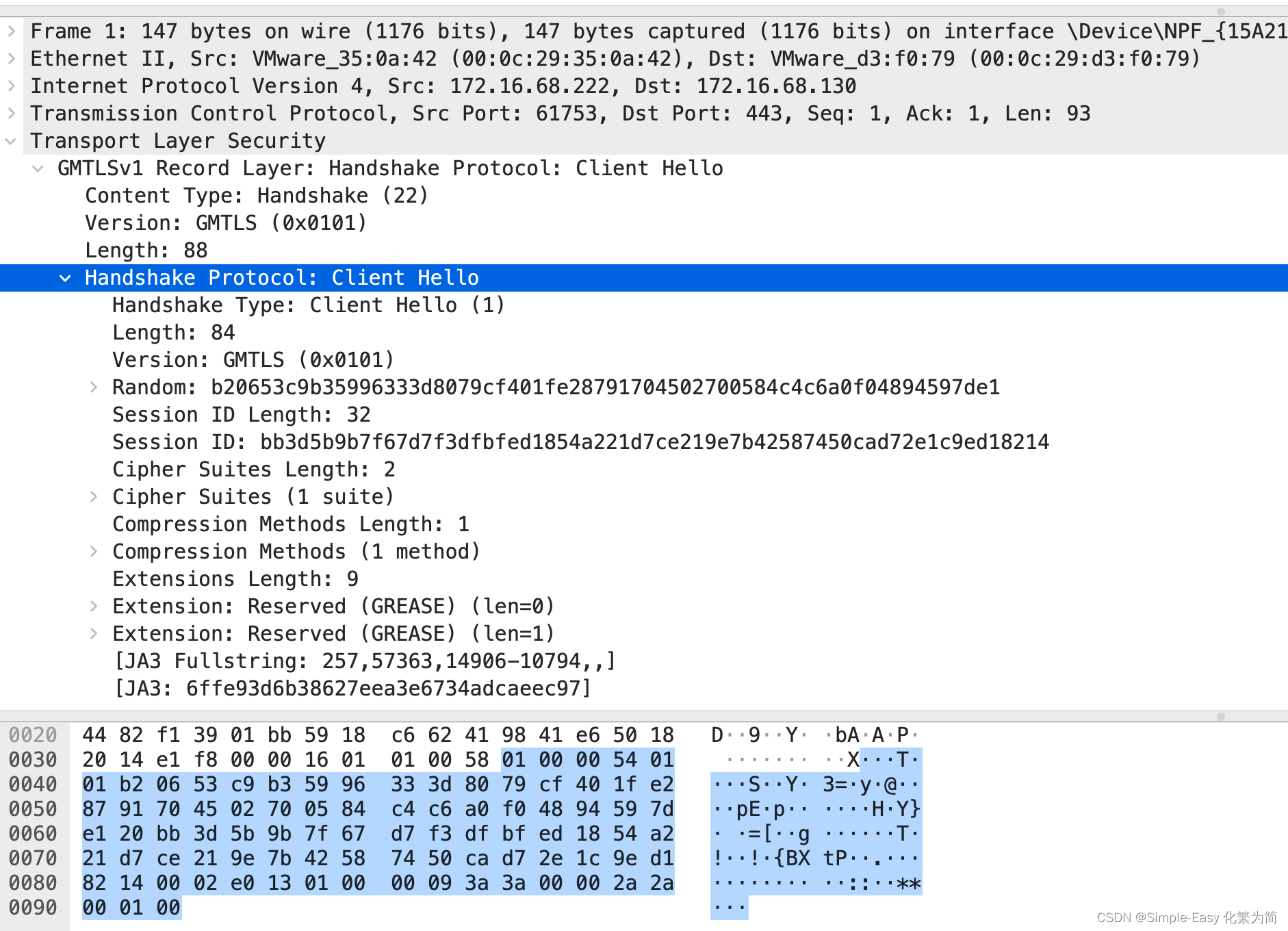
本文给的例子是ECC-SM3-SM4-CBC;
GBT-38636-2020(传输层密码协议TLCP) 定义了pre-master key 和 master key;
Pre- master Key 48字节长度,version 2字节,随机数46字节,由客户端产生。采用SM2加密后的密文放在client key exchange 里发送;
pre-master key:
0101 版本号
E582AAC5064CF164DCAC7A14BFEC7BF30AF646558DC7DC63CBC77265EDE6E7721D2161FA098EF3EC41FECBFEF107 46字节随机数
Master key 计算公式:
下面是标准的master key的计算方法;
如果客户端和服务端在hello消息都携带了extended_master_secret扩展项的话,将会采用扩展方法进行master key的计算,这个方法在RFC7627里定义。不在本国密规范定义;
master_secret = PRF(pre_master_secret, "extended master secret", session_hash)[0..47];
A0 = seed = 6d617374657220736563726574B20653C9B35996333D8079CF401FE28791704502700584C4C6A0F04894597DE1D76E6BC156B1BA2A5CEA6C251B6C2038E00CBD8194132BC33452E22E0F324F2D
A1 = 45 AC 10 55 74 46 2C 6A 68 41 6C 93 22 94 F2 8F 88 C7 1C 76 EC 22 E9 09 29 D3 D1 ED 3A B3 41 2A
A2 = FE 2A 0D B1 BD 8B F7 12 D4 54 B4 5E 6E 54 29 59 10 52 1B 20 0C E8 33 30 E0 68 61 20 78 50 1E 20
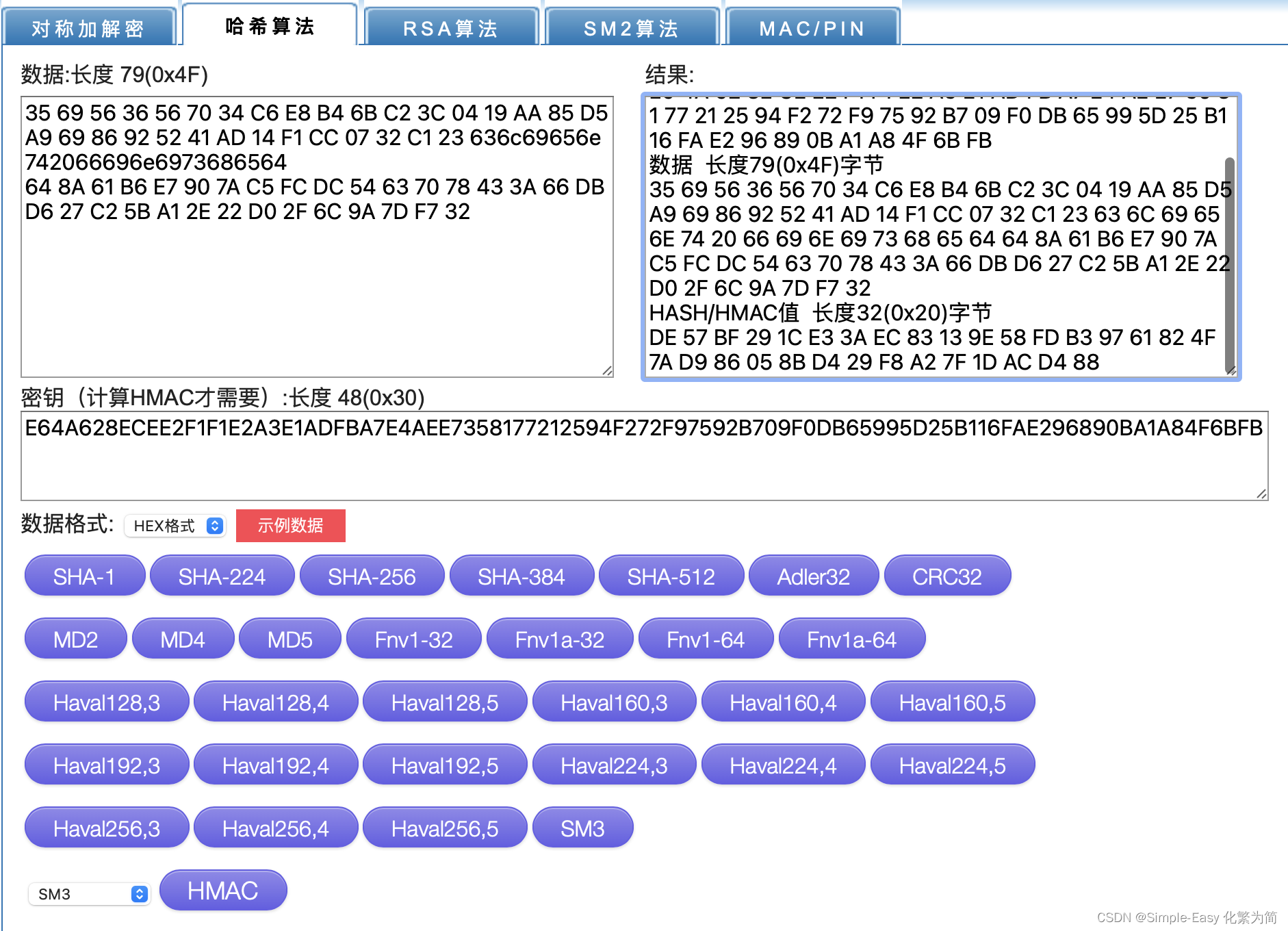
HMAC(A1+Seed) = E6 4A 62 8E CE E2 F1 F1 E2 A3 E1 AD FB A7 E4 AE E7 35 81 77 21 25 94 F2 72 F9 75 92 B7 09 F0 DB
HMAC(A2+Seed) = 65 99 5D 25 B1 16 FA E2 96 89 0B A1 A8 4F 6B FB 79 80 81 0D 0F 47 4F 42 56 7B 83 8F 00 E8 4E 73
取HMAC(A1+Seed) + HMAC(A2+Seed) 的前48字节,产生
master key = E6 4A 62 8E CE E2 F1 F1 E2 A3 E1 AD FB A7 E4 AE E7 35 81 77 21 25 94 F2 72 F9 75 92 B7 09 F0 DB 65 99 5D 25 B1 16 FA E2 96 89 0B A1 A8 4F 6B FB 79 80 81 0D 0F 47 4F 42 56 7B 83 8F 00 E8 4E 73
工作密钥:最终用于加密和生成校验码的密码是通过对master key再推导出来的。

本规范还定义了PRF函数:
Master key :E64A628ECEE2F1F1E2A3E1ADFBA7E4AEE7358177212594F272F97592B709F0DB65995D25B116FAE296890BA1A84F6BFB
A0=seed = 6b657920657870616e73696f6eD76E6BC156B1BA2A5CEA6C251B6C2038E00CBD8194132BC33452E22E0F324F2DB20653C9B35996333D8079CF401FE28791704502700584C4C6A0F04894597DE1
A1 = 0B 52 D1 CF 1A BF 3B 6F C6 5C 80 8B E1 7C 22 93 B5 CE A4 18 C2 DC 14 8B 1C 3B 02 6C 09 98 19 51
A2 = 22 7C 0A D1 C5 0E F6 4A 33 35 24 0F 07 D5 8D 7B 4F 03 F9 54 AA 80 A0 38 EA 07 0C 2A EC 0A 11 25
A3 = 0D E2 4D AC 1A A1 8F 45 9E 90 67 33 D5 A1 83 53 FD C0 BA 28 F6 70 3C 1A 49 DA 94 1C AA 61 0F 94
client_write_MAC_secret(32字节):
HMAC(A1+Seed) = B1 8D 1B 2B 67 7E A3 AB 5C 08 1B 6B F2 81 05 9E C3 25 E9 ED 2A FA 64 A9 C9 BE 87 F0 92 5F A6 0E
server_write_MAC_secret(32字节)
HMAC(A2+Seed) = E4 50 F3 DC 28 68 B9 63 DA B2 01 03 C4 05 93 45 F8 F8 A9 E7 B0 11 8F EE 48 A9 33 BC 88 36 64 EB
HMAC(A3+Seed) =
client_write_key (16字节)
E5 F8 54 2F 7B 23 01 C6 A3 BF 39 DA D8 15 E9 C8
server_write_key (16字节)
0F 31 84 20 AD 79 5B BE 66 DA 75 03 95 C8 1C 48
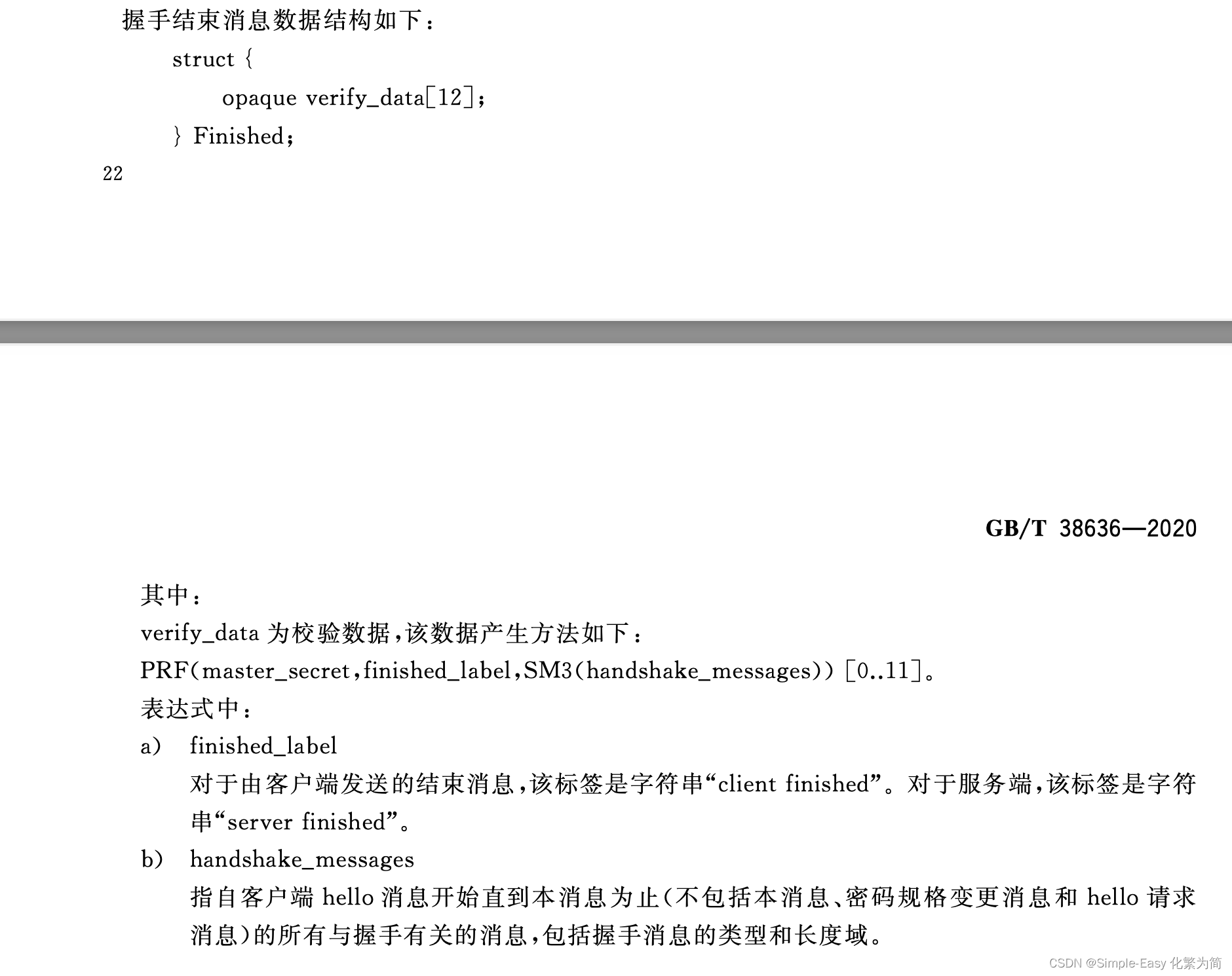
Finshed 消息(即 encrpted handshake message):
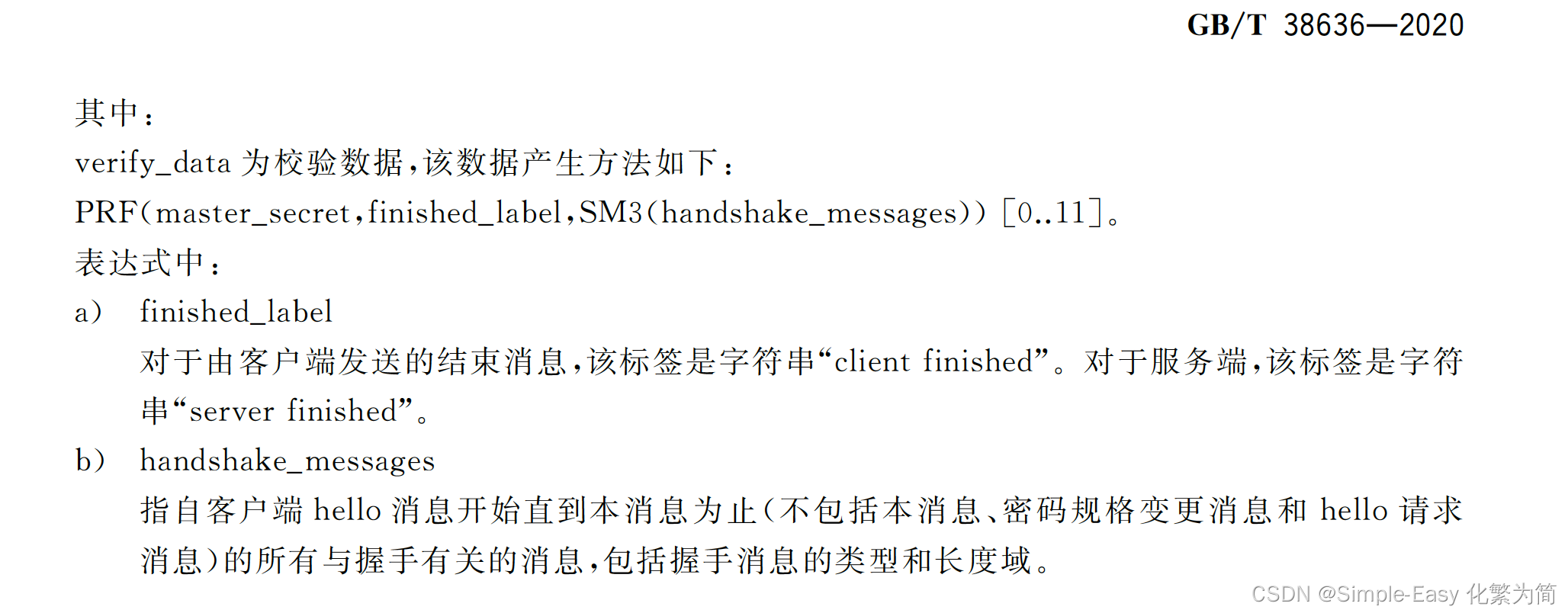
Finished 消息加密后长度80字节(16字节IV+ciphered(16字节finished消息明文+32字节MAC+16字节的padding)),在wireshark里面显示为Encrypted handshake message,解密后可以显示为Finished消息
IV(16字节)
52f5403d3ea71482c81986ae42433c2e
Ciphered text(64字节)
2e89c8572989dada0e6840ce6b248c91
a703b727082505a40fadffb0c4972f73e64c585187df39ad084b26d2319aed0c
cbcd5cd877bd3a863956aa2824e85f14

SM4 CBC depher后:
client Finshed(16字节)
14 00 00 0C DE 57 BF 29 1C E3 3A EC 83 13 9E 58其中14 类型
00 00 0C长度
DE 57 BF 29 1C E3 3A EC 83 13 9E 58 对以往handshake消息的hash值,从client hello消息开始,到change cipher spec消息结束(不包括change cipher spec,finished消息,hellorequest(注意不是client hello和server hello))
消息包括消息类型和长度以及内容,如下图蓝色所示。
通过下面式子计算后,取前12个字节
PRF(master_secret, finished_label, SM3 (handshake_messages)) [0.11].
MAC code(32字节)
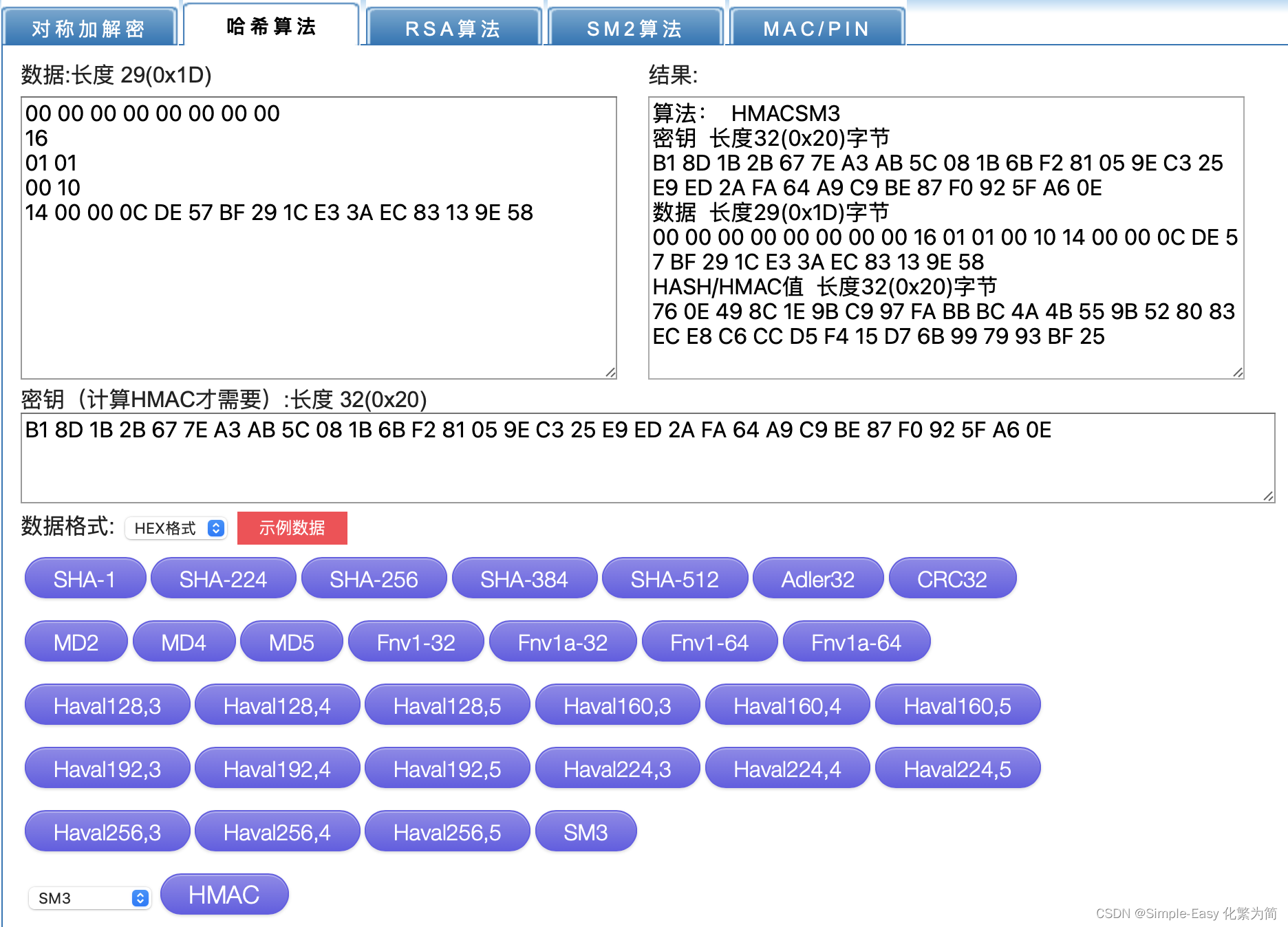
76 0E 49 8C 1E 9B C9 97 FA BB BC 4A 4B 55 9B 52 80 83 EC E8 C6 CC D5 F4 15 D7 6B 99 79 93 BF 25
HMAC_hash(MAC_write_secret,seq_num+TLSCompresed.type+TLSCompresed.version+
TLSCompresedl.ength+TLSCompresed.fragment)
MAC_write_secret = B1 8D 1B 2B 67 7E A3 AB 5C 08 1B 6B F2 81 05 9E C3 25 E9 ED 2A FA 64 A9 C9 BE 87 F0 92 5F A6 0Eseq_num+TLSCompresed.type+TLSCompresed.version+
TLSCompresedl.ength+TLSCompresed.fragmen
00 00 00 00 00 00 00 00 seq 8字节
16 1字节type
01 01 2字节version
00 10 2字节长度值
14 00 00 0C DE 57 BF 29 1C E3 3A EC 83 13 9E 58 (16字节的finished消息)HMAC_hash的hash算法是SM3
pading len + Pading content(共16字节padding)
0F 0F 0F 0F 0F 0F 0F 0F 0F 0F 0F 0F 0F 0F 0F 0F





















 1996
1996











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








