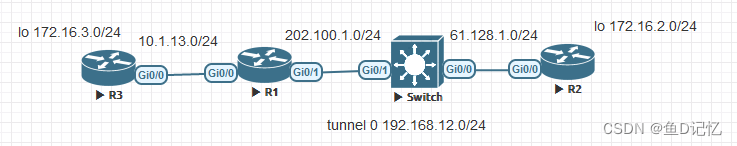
底层
R1
int g0/0
ip add 10.1.13.1 255.255.255.0
int g0/1
ip add 202.100.1.1 255.255.255.0
ip route 0.0.0.0 0.0.0.0 202.100.1.100
ip route 172.16.3.0 255.255.255.0 10.1.13.3R3
int g0/0
ip add 10.1.13.3 255.255.255.0
int lo 0
ip add 172.16.3.3 255.255.255.0
ip route 0.0.0.0 0.0.0.0 10.1.13.1R2
int lo 0
ip add 172.16.2.1 255.255.255.0
int g0/0
ip add 61.128.1.2 255.255.255.0
ip route 0.0.0.0 0.0.0.0 61.128.1.100Switch
int g0/1
no sw
ip add 202.100.1.100 255.255.255.0
int g0/0
no sw
ip add 61.128.1.100 255.255.255.0建立R1,R2的tunnel
R1
int t0
ip add 192.168.12.1
tun sou 202.100.1.1
tun des 61.128.1.2
ip route 172.16.2.0 255.255.255.0 t0R2
int t0
ip add 192.168.12.2 255.255.255.0
tun sou 61.128.1.2
tun des 202.100.1.1
ip route 172.16.3.0 255.255.255.0 t0此时测试两端lo0互ping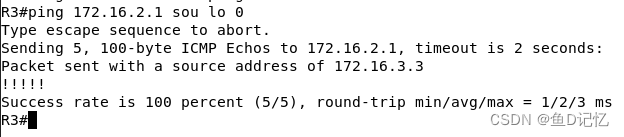
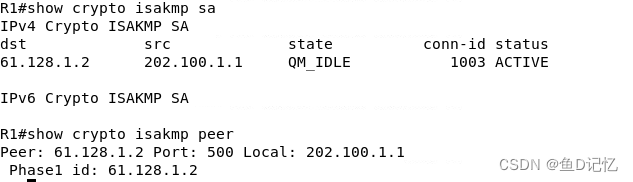
制定一阶段策略
R1
crypto isakmp policy 10
encr 3des
auth pre-share
group 2
hash sha
crypto isakmp key cisco123 add 61.128.1.2
R2
crypto isakmp policy 10
encr 3des
auth pre-share
group 2
hash sha
crypto isakmp key cisco123 add 202.100.1.1
定义二阶段策略
R1
crypto ipsec tran TS esp-3des esp-sha-hmac
mode transport
access-list 100 per gre host 202.100.1.1 host 61.128.1.2
逻辑的t0,物理的g0/1,g0/0R2
crypto ipsec tran TS esp-3des esp-sha-hmac
mode transport
access-list 100 per gre host 61.128.1.2 host 202.100.1.1
逻辑的t0,物理的g0/1,g0/0打包,接口引用
R1
crypto map Gos 10 ipsec-isakmp
set peer 61.128.1.2
set trans TS
mat add 100
int g0/1
crypto map GoSR2
crypto map Gos 10 ipsec-isakmp
set peer 202.100.1.1
set trans TS
mat add 100
int g0/0
crypto map GoS建立ipsec profile,将IPSec SA关联到tunnel接口上
R1
crypto ipsec profile PRF
set tran TS
int t0
tunnel protection ipsec profile PRFR2可不敲





















 2140
2140











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








