会被Sql注入攻击的写法:
public class JDBCTest {
public static void main(String [] args) throws Exception {
//加载jdbc驱动
Class.forName("com.mysql.cj.jdbc.Driver");
//建立连接 Connection 通过账户 密码 url协议
String name="root";
String pwd="root";
String url="jdbc:mysql://127.0.0.1:3306/xd_web?" +
"useUnicode=true&characterEncoding=utf-8&useSSL=false";
Connection connection= DriverManager.getConnection(url,name,pwd);
//创建执行的SQL语句Statement
Statement statement=connection.createStatement();
//处理执行的结果ResultSet 该方式会被Sql注入攻击
ResultSet resultSet=statement.executeQuery("select *from user ");
while (resultSet.next()){
System.out.println("用户名 name="+resultSet.getString("username")+"练习方式 WeChat="+resultSet.getString("wechat"));
}
//释放资源
resultSet.close();
statement.close();
connection.close();
}
}
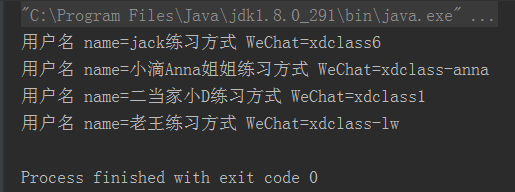
截图:
改进版————只是在statement处改变查询方法变为了 PreparedStatement
public class JDBCTest {
public static void main(String [] args) throws Exception {
jdbctest();
}
private static void jdbctest()throws Exception{
//加载jdbc驱动
Class.forName("com.mysql.cj.jdbc.Driver");
//建立连接 Connection 通过账户 密码 url协议
String name="root";
String pwd="root";
String url="jdbc:mysql://127.0.0.1:3306/xd_web?" +
"useUnicode=true&characterEncoding=utf-8&useSSL=false";
Connection connection= DriverManager.getConnection(url,name,pwd);
String sname="jack";
String spwd="666";
//创建执行的SQL语句Statement
PreparedStatement preparedStatement =connection.prepareStatement("select * from user where username=? and pwd=?");
preparedStatement.setString(1,sname);
preparedStatement.setString(2,spwd);
//处理执行的结果ResultSet
ResultSet resultSet=preparedStatement.executeQuery();
while (resultSet.next()){
System.out.println("用户名 name="+resultSet.getString("username")+"练习方式 WeChat="+resultSet.getString("wechat"));
}
//释放资源
resultSet.close();
preparedStatement.close();
connection.close();
}
}
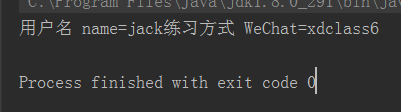
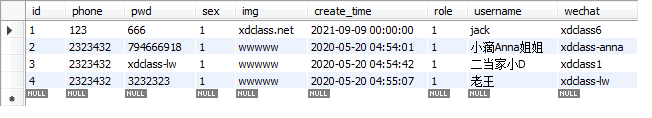
数据库:
























 703
703











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








