Bugku Web32
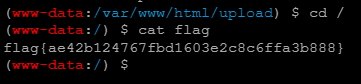
这个题有些许的坑(如果独自做题的话需要猜源码中过滤了什么),这里直接贴源码,可以发现白名单里有php4,并且还要求multipart/form-data不能是multipart/form-data,所以上传的时候需要将multipart/form-data改成Multipart/form-data来绕过检测,直接burp修改数据包,然后用蚁剑连接,便可以找到flag
<html>
<body>
<?php
$flag = "flag{test}"
?>
<form action="index.php" method="post" enctype="multipart/form-data">
My name is margin,give me a image file not a php<br>
<br>
<input type="file" name="file" id="file" />
<input type="submit" name="submit" value="Submit" />
</form>
<?php
function global_filter(){
$type = $_SERVER["CONTENT_TYPE"];
if (strpos($type,"multipart/form-data") !== False){
$file_ext = substr($_FILES["file"]["name"], strrpos($_FILES["file"]["name"], '.')+1);
$file_ext = strtolower($file_ext);
if (stripos($file_ext,"php") !== False){
die("Invalid File<br />");
}
}
}
?>
<?php
global_filter();
if ((stripos($_FILES["file"]["type"],'image')!== False) && ($_FILES["file"]["size"] < 10*1024*1024)){
if ($_FILES["file"]["error"] == 0){
$file_ext = substr($_FILES["file"]["name"], strrpos($_FILES["file"]["name"], '.')+1);
$file_ext = strtolower($file_ext);
$allowexts = array('jpg','gif','jpeg','bmp','php4');
if(!in_array($file_ext,$allowexts)){
die("give me a image file not a php");
}
$_FILES["file"]["name"]="bugku".date('dHis')."_".rand(1000,9999).".".$file_ext;
if (file_exists("upload/" . $_FILES["file"]["name"])){
echo $_FILES["file"]["name"] . " already exists. <br />";
}
else{
if (!file_exists('./upload/')){
mkdir ("./upload/");
system("chmod 777 /var/www/html/upload");
}
move_uploaded_file($_FILES["file"]["tmp_name"],"upload/" . $_FILES["file"]["name"]);
echo "Upload Success<br>";
$filepath = "upload/" . $_FILES["file"]["name"];
echo "Stored in: " ."<a href='" . $filepath . "' target='_blank'>" . $filepath . "<br />";
}
}
}
else{
if($_FILES["file"]["size"] > 0){
echo "You was catched! :) <br />";
}
}
?>
</body>
</html>
























 233
233











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








