免杀-绕过内存扫描 复现
参考文章:https://xz.aliyun.com/t/9399
起因是在群里看到大佬们在聊这个,就上网搜了一份教程,我本地没有卡巴斯基,所以随便复现一下,做个记录,当个笔记。
内存扫描是耗时耗力不管是卡巴还是其他杀软,一般来说都是扫描进程中一些高危的区域比如带有可执行属性的内存区域,既然他扫描带有X(可执行)属性的内存区域那么只要我们去除X属性,那自然就不会被扫也就不会被发现,但问题是去除X属性后Beacon也就跑不起来,但是不用怕我们知道Windows进程触发异常时我们可以对它处理,而此时我们可以在一瞬间恢复内存X属性让它跑起来然后等它再次进入sleep时去除X属性隐藏起来
复现
下载一份detours库,然后用vs编译成x64版本
https://github.com/microsoft/Detours.git
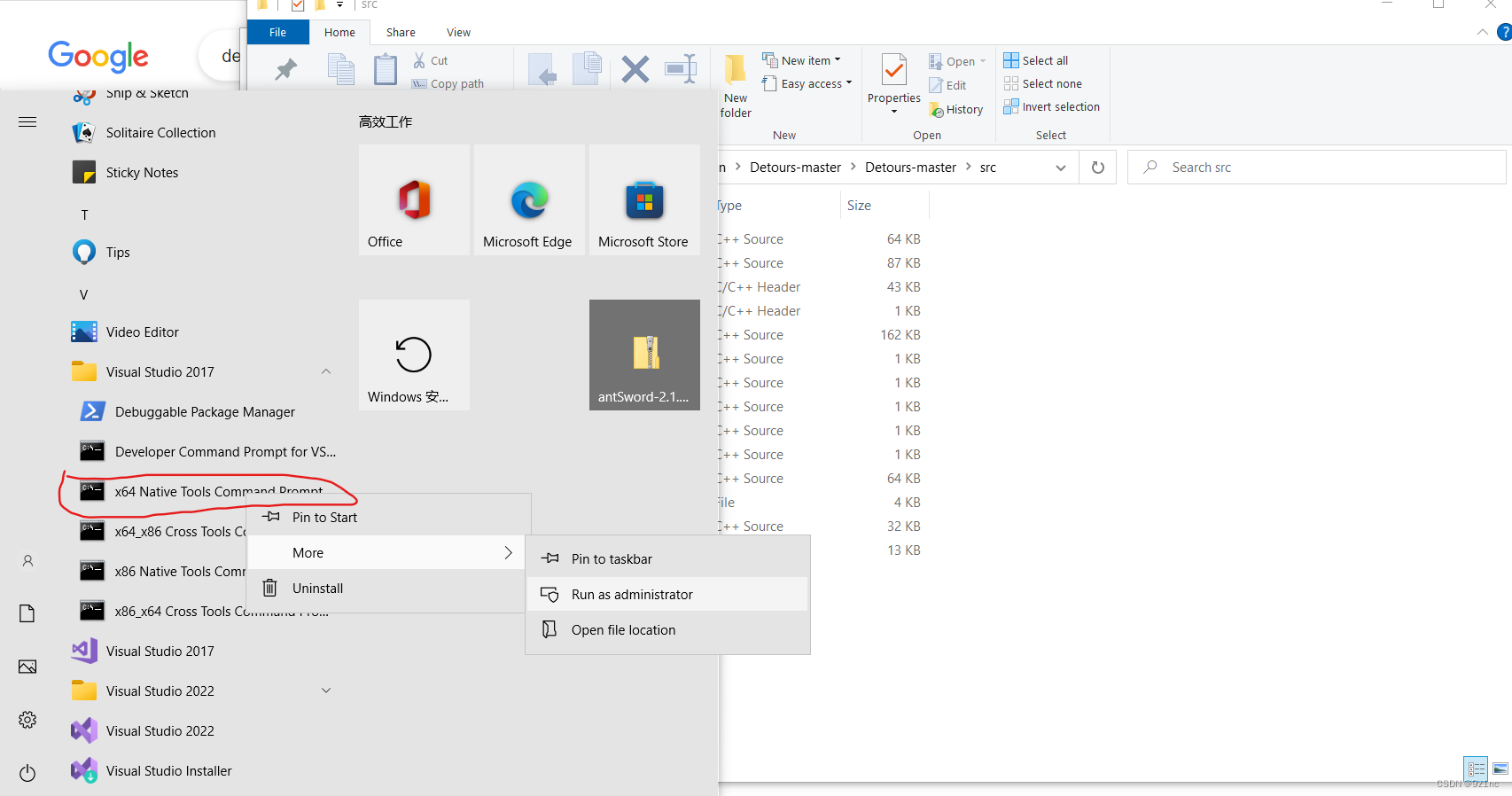
找到vs,使用x64编译以这个库
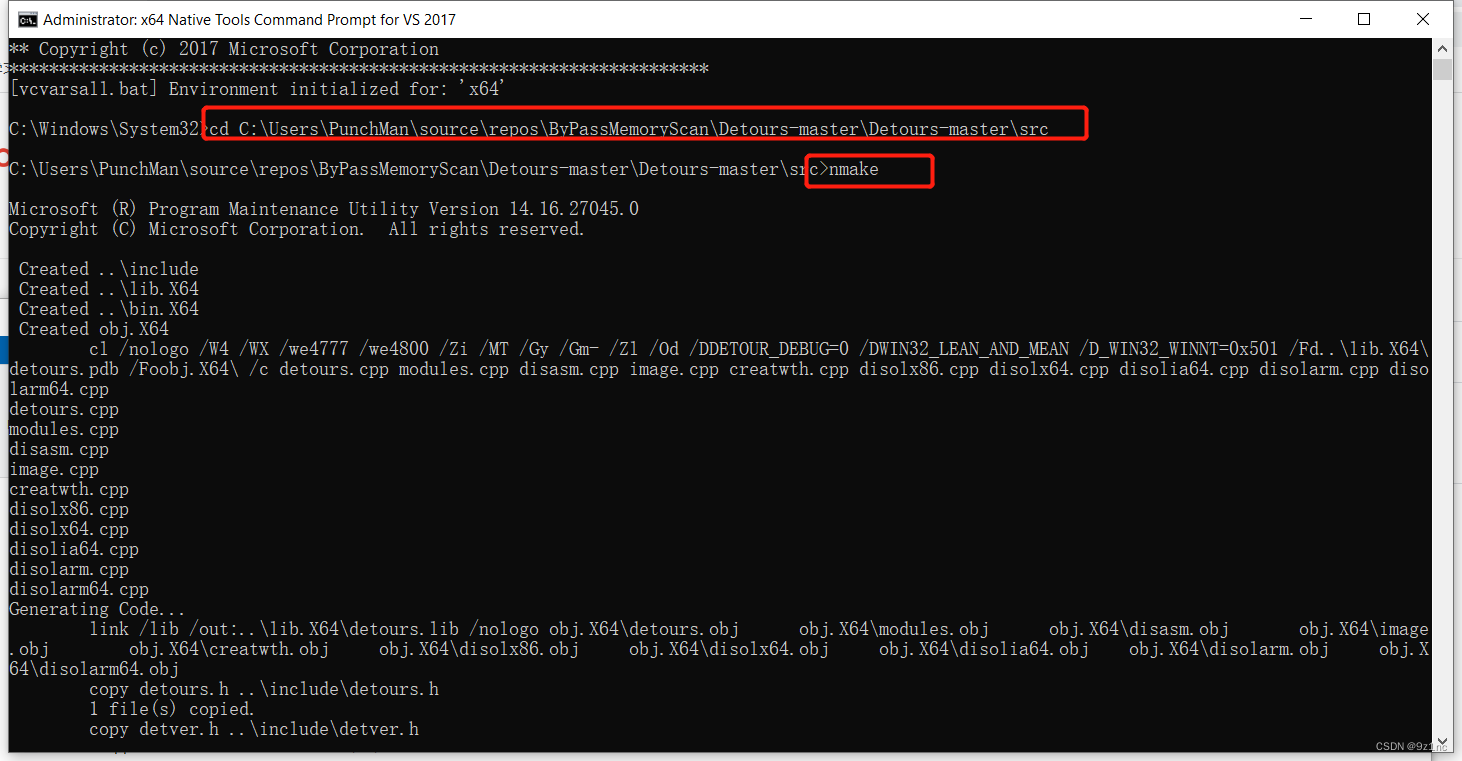
进入到src目录使用namke编译x64版本
将编译出来的如下三个文件 放到创建好的c++项目中








 本文介绍了如何利用Detours库在Windows环境下实现免杀Beacon的技术,通过修改内存页权限,在异常处理时瞬间恢复可执行属性,从而避开杀毒软件的内存扫描。详细步骤包括下载Detours库,编译x64版本,注入代码并设置异常处理程序,以及在执行过程中动态调整内存页权限。
本文介绍了如何利用Detours库在Windows环境下实现免杀Beacon的技术,通过修改内存页权限,在异常处理时瞬间恢复可执行属性,从而避开杀毒软件的内存扫描。详细步骤包括下载Detours库,编译x64版本,注入代码并设置异常处理程序,以及在执行过程中动态调整内存页权限。
 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章

















 1347
1347

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








