About
碍于流量比较多所以编写一个脚本来提取数据包中的冰蝎流量进行解密
思路
工具编写思路
配合系统tshark将冰蝎的POST流量进行导出,
对shell文件进行url解码和base解码,得到aes的key密钥
赛题下载
链接:https://pan.baidu.com/s/1xSNiDSb5zlAAxSQnWDqOyA?pwd=q1hw
提取码:q1hw
实践
tshark -r behinder.pcap -Y "http.request.method==POST" -T fields -e http.file_data -E quote=d > output.txt
导出冰蝎传输数据,使用tshark配合,对POST传输进行过滤 ,再导出file_data的数据
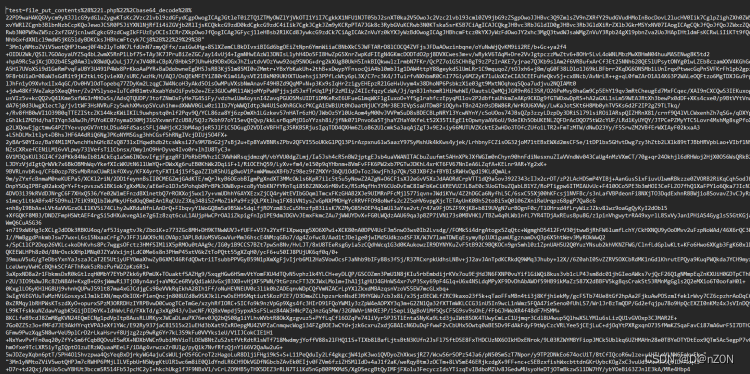
得到最原始的传输数据,需要进行多次解码
使用正则的方式进行筛选加密数据
def kkey():
file = open('output.txt', 'r', encoding='utf-8')
F = file.read()
try:
for i in range(0,1):
x = r'"(.*?)"'
flag = re.findall(x, F)[i]
nt = urllib.parse.unquote(flag)
l = r'e\("(.*?)"\)'
flag2 = re.findall(l,nt)[0]
b64 = base64.b64decode(flag2)
m = r'key="(.*?)";'
global flag3
flag3 = re.findall(m,str(b64))[0]
except IndexError:
print("exit")
进行多次正则筛选出key的值
def ddencode():
AES_key = flag3.encode('utf-8')
file = open('output.txt','r',encoding='utf-8')
F = file.read()
try:
for i in range(1,300000000000000):
x = r'"(.*?)"'
flag = re.findall(x,F)[i]
encrypted_bytes = base64.b64decode(flag)
aes = AES.new(AES_key, AES.MODE_CBC)
decrypted_bytes = aes.decrypt(encrypted_bytes)
decrypted_text = decrypted_bytes.rstrip(b'\0').decode('latin-1')
l = r"e\('(.*?)'\)"
flag2 = re.findall(l, decrypted_text)[0]
b64 = base64.b64decode(flag2)
out = open('flag.txt','a')
out.write('\n'+str(b64)+'\n')
except IndexError:
print("exit")
再使用key对数据进行解密,值得关注的是数据转换的格式很有趣,转为utf-8则乱码
def bcmd():
file = open('flag.txt', 'r', encoding='utf-8')
F = file.read()
try:
for i in range(0,10000000000):
lm = r'cmd="(.*?)";'
op = re.findall(lm,F)[i]
ab = base64.b64decode(op)
print(ab)
out = open('cmdflag.txt', 'a')
out.write('\n' + str(ab) + '\n')
except IndexError:
print("exit")
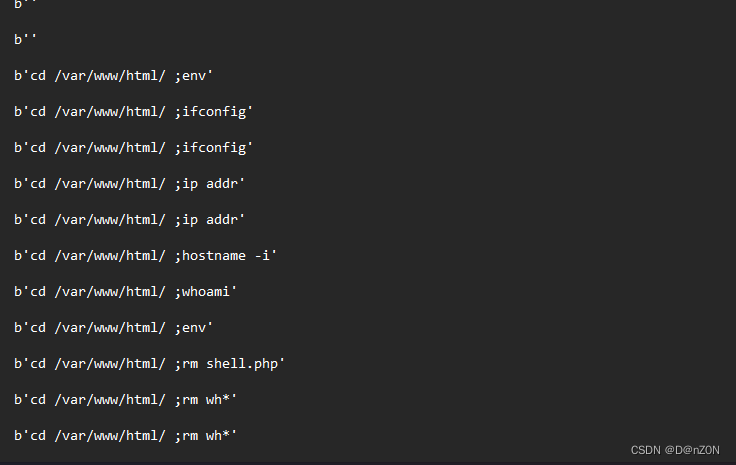
得到原始的数据,可以看到一些命令的执行,
贴一份完整代码
攻击端数据恢复
# -*- coding: utf-8 -*-
import re
import urllib
import base64
from Crypto.Cipher import AES
def ddencode():
AES_key = flag3.encode('utf-8')
file = open('output.txt','r',encoding='utf-8')
F = file.read()
try:
for i in range(1,300000000000000):
x = r'"(.*?)"'
flag = re.findall(x,F)[i]
encrypted_bytes = base64.b64decode(flag)
aes = AES.new(AES_key, AES.MODE_CBC)
decrypted_bytes = aes.decrypt(encrypted_bytes)
decrypted_text = decrypted_bytes.rstrip(b'\0').decode('latin-1')
l = r"e\('(.*?)'\)"
flag2 = re.findall(l, decrypted_text)[0]
b64 = base64.b64decode(flag2)
out = open('flag.txt','a')
out.write('\n'+str(b64)+'\n')
except IndexError:
print("exit")
def kkey():
file = open('output.txt', 'r', encoding='utf-8')
F = file.read()
try:
for i in range(0,1):
x = r'"(.*?)"'
flag = re.findall(x, F)[i]
nt = urllib.parse.unquote(flag)
l = r'e\("(.*?)"\)'
flag2 = re.findall(l,nt)[0]
b64 = base64.b64decode(flag2)
m = r'key="(.*?)";'
global flag3
flag3 = re.findall(m,str(b64))[0]
except IndexError:
print("exit")
def bcmd():
file = open('flag.txt', 'r', encoding='utf-8')
F = file.read()
try:
for i in range(0,10000000000):
lm = r'cmd="(.*?)";'
op = re.findall(lm,F)[i]
ab = base64.b64decode(op)
print(ab)
out = open('cmdflag.txt', 'a')
out.write('\n' + str(ab) + '\n')
except IndexError:
print("exit")
if __name__ == '__main__':
kkey()
print("key is "+flag3)
ddencode()
bcmd()
现阶段困难点
由于无法过滤出原始的数据流导致无法最终服务器回显的数据
本来是想写成自动化的,有时间的话后期应该会完善
结语
写的代码比较烂如果有不懂的请私信我,博主正在努力中…









 本文介绍了如何通过编写Python脚本,利用tshark工具捕获和分析冰蝎流量,通过URL解码、Base64解码获取AES密钥,进而对传输数据进行多次解码,最终恢复出一些命令执行的内容。
本文介绍了如何通过编写Python脚本,利用tshark工具捕获和分析冰蝎流量,通过URL解码、Base64解码获取AES密钥,进而对传输数据进行多次解码,最终恢复出一些命令执行的内容。















 446
446











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










