Attackers' goal
a. Confidentiality 保密性:控制程序
b. Integrity 完整性:插入新代码
c. Avaliablity 可用性:意外终止程序
Command Injection
a. Commands to perform specific tasks 输入控制系统执行外来命令
b. With system() or popen() is dangerous(system: open a shell; popen: open a process
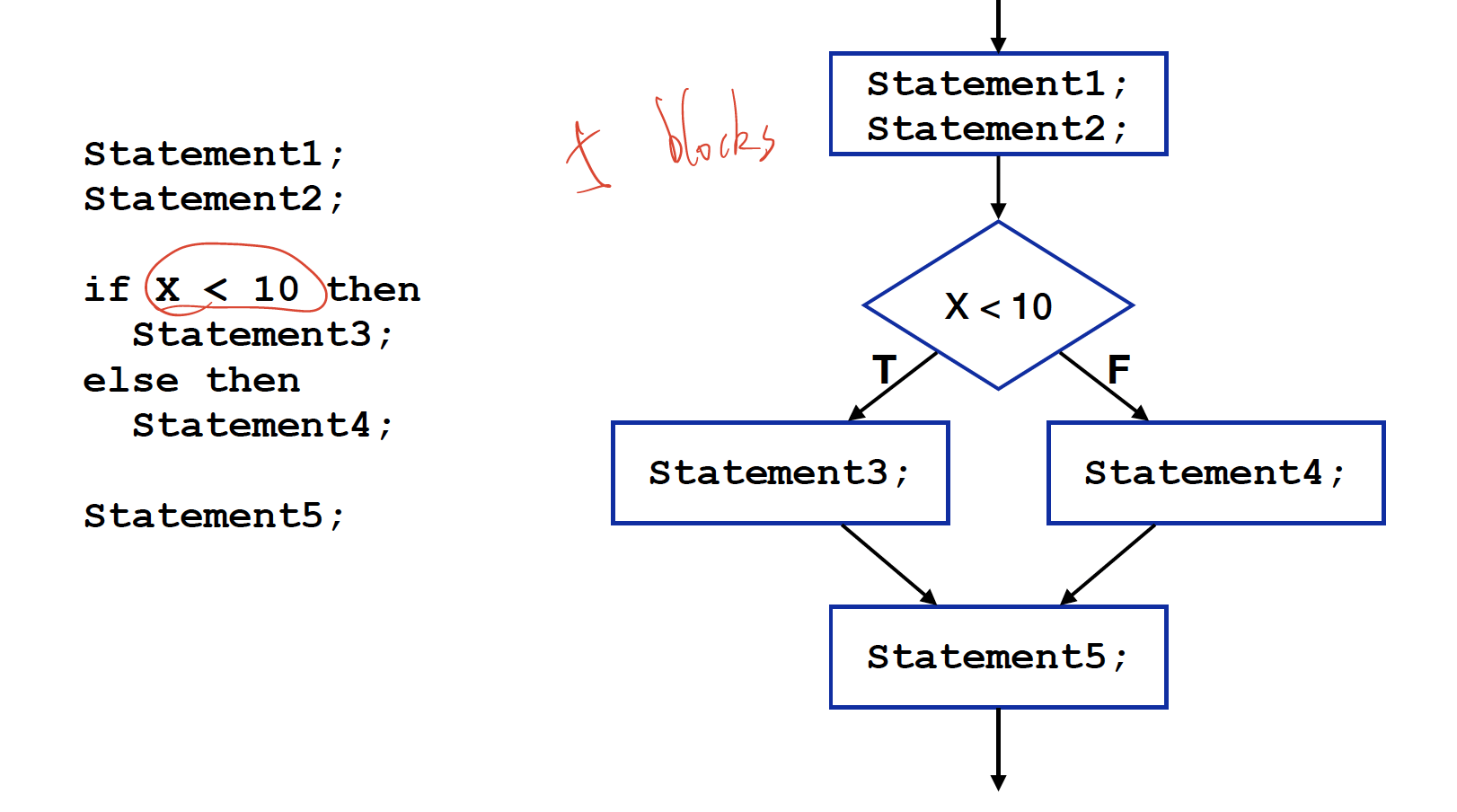
c. Use Control Flow Graph(CFG) to avoid this attack: 画出这个程序运行的所有paths
eg.
Stack Overflow
a. Stack:
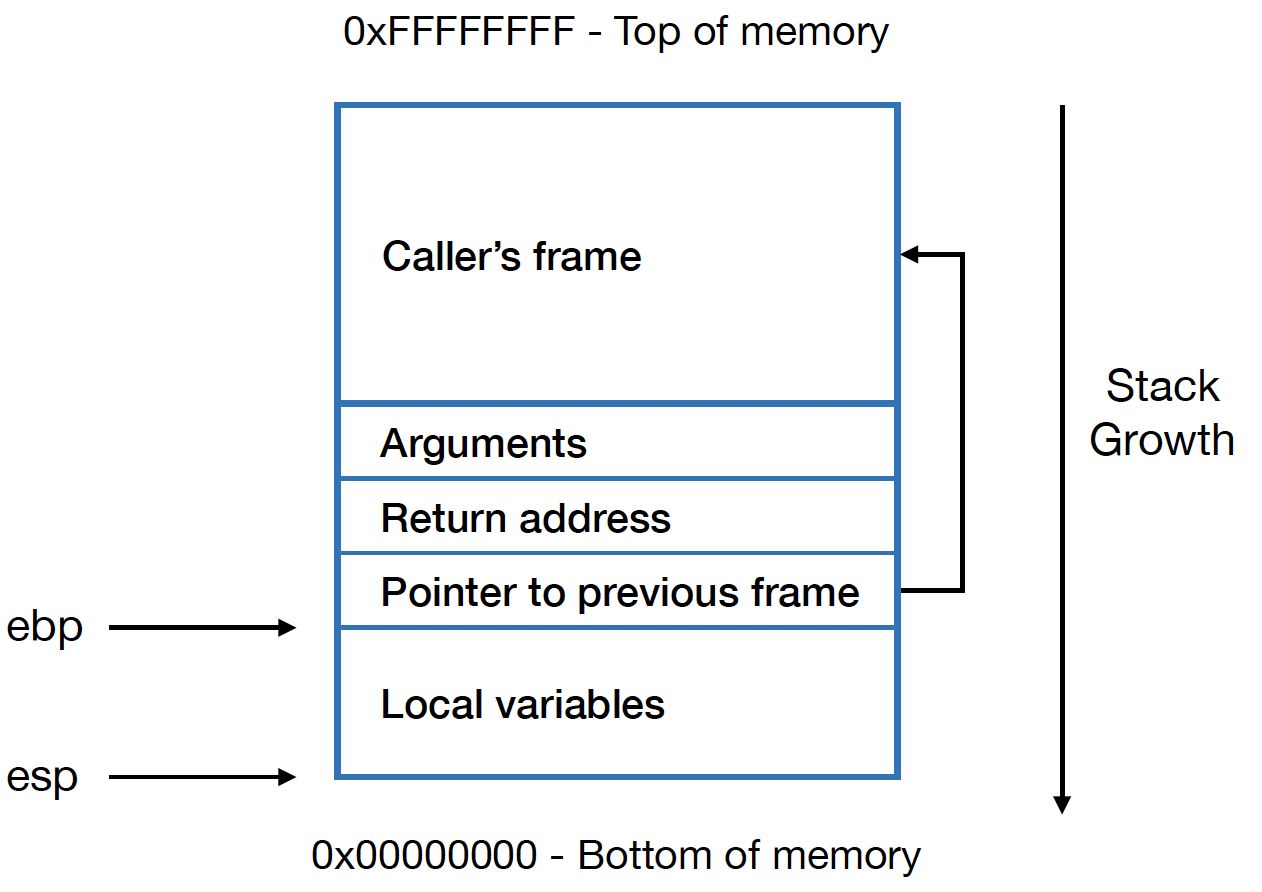
ebp: Address of current frame 此时function的开头
esp: Top of stack 栈顶
b. Reason: Data is copied/written without checking boundaries (未检查边界)
c. Result: Sensitive data, return address, user-defined code be the overflow data
e. Vulnerable Functions: get(); strcpy()/strcat(); sprintf()/vsprintf(); scanf()/sscanf()/fscanf()
f. Cause:
Copying overflows: buffer的复制超出界限
Array indexing overflows:同上
Integer overflows:整数超出,变成unexpected的整数
大的signed整数会变成大的signed整数
大的unsigned整数变成小的unsigned整数
使用assertions and similar checks 来避免overflow
Loop overflows
Format String Vulnerabilities 格式化字符串攻击:
void function(int score) {
printf("Score: %d");
}
会打印stack中上4个的地址






















 1万+
1万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










