补充:
跨网络访问:
(1)服务自身相关权限的开启
(2)文件系统自身权限的开启
vsftpd虚拟用户:
虚拟用户(给特定服务使用的用户账号)。
1.所有虚拟用户会统一映射为一个指定的系统帐号:访问共享位置,即为此系统帐号的家目录
2.各虚拟用户可被赋予不同的访问权限,通过匿名用户的权限控制参数进行指定
3.虚拟用户帐号的存储方式:(文件、关系型数据库中的表中)
(1)文件:
文件:创建文本文件,奇数行为用户名,偶数行为密码,再被编码为hash 格式Berkeley DB database文件
例如:db_load -T -t hash -f virusers.txt virusers.db
(2)关系型数据库中的表中:(实时查询数据库完成用户认证)
vsftpd 支持mysql库:pam要依赖于pam-mysql
/lib64/security/pam_mysql.so
/usr/share/doc/pam_mysql-0.7/README
1、实现基于MYSQL验证的vsftpd虚拟用户访问
实验如图
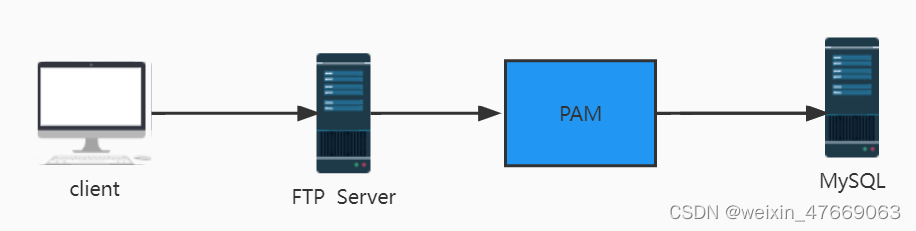
FTP server:CentOS7
mysql server: mysql(不要使用8.0)或者mariadb
(1)MySQL server 安装mysql数据库,并配置好支持vsftbd服务
[20:21:24 root@CS8-VM8-10 ~][#yum install -y mariadb-server
[20:52:42 root@CS8-VM8-10 ~][#systemctl enable --now mariadb.service
#建立存储虚拟用户数据库和表
[20:53:41 root@CS8-VM8-10 ~][#mysql
...
MariaDB [(none)]> create database vsftpd;
Query OK, 1 row affected (0.001 sec)
MariaDB [(none)]> use vsftpd;
Database changed
MariaDB [vsftpd]> create table users (
-> id int auto_increment not null primary key,
-> name char(50) binary not null,
-> password char(48) binary not null );
Query OK, 0 rows affected (0.004 sec)
#添加虚拟用户,为了安全应该使用PASSWORD函数加密其密码后存储
MariaDB [vsftpd]> insert into users(name,password) values('alice',password('123456'))
-> ;
Query OK, 1 row affected (0.001 sec)
MariaDB [vsftpd]> insert into users(name,password) values('bob',password('123456'));
Query OK, 1 row affected (0.001 sec)
MariaDB [vsftpd]> select * from users;
+----+-------+-------------------------------------------+
| id | name | password |
+----+-------+-------------------------------------------+
| 1 | alice | *6BB4837EB74329105EE4568DDA7DC67ED2CA2AD9 |
| 2 | bob | *6BB4837EB74329105EE4568DDA7DC67ED2CA2AD9 |
+----+-------+-------------------------------------------+
2 rows in set (0.001 sec)
#创建连接的数据库用户
MariaDB [vsftpd]> grant select on vsftpd.* to vsftpd@'10.0.8.%' identified by '123456';
Query OK, 0 rows affected (0.000 sec)
MariaDB [vsftpd]> flush privileges;
Query OK, 0 rows affected (0.001 sec)
MariaDB [vsftpd]>
(2)在FTP服务器上安装vsftp和pam_mysql包
由于CS7\8:无对应的rpm包,所以需要手动编译安装。
CS6由epel源提供:yum install -y pam_mysql
pam-mysql源码编译安装:
2 2022-07-13 21:09:14 yum install -y vsftpd
3 2022-07-13 21:09:29 yum -y install vsftpd gcc gcc-c++ make mariadb-devel pam-devel
#包的下载地址:
http://prdownloads.sourceforge.net/pam-mysql/pam_mysql-0.7RC1.tar.gz
https://github.com/NigelCunningham/pam-MySQL/archive/v0.8.1.tar.gz
4 2022-07-13 21:10:32 rz -E #这里本人已提前下载好
5 2022-07-13 21:10:40 ll
6 2022-07-13 21:10:48 tar xf pam_mysql-0.7RC1.tar.gz
7 2022-07-13 21:10:53 cd pam_mysql-0.7RC1/
8 2022-07-13 21:11:50 ./configure --with-pam-mods-dir=/lib64/security
9 2022-07-13 21:12:07 make install
[21:12:08 root@CS7-VM8-10 pam_mysql-0.7RC1]#ll /lib64/security/pam_mysql*
-rwxr-xr-x. 1 root root 882 Jul 13 21:12 /lib64/security/pam_mysql.la
-rwxr-xr-x. 1 root root 141712 Jul 13 21:12 /lib64/security/pam_mysql.so
(3)在FTP服务器上建立pam认证所需的文件
[21:21:24 root@CS7-VM8-10 ~]#vim /etc/pam.d/vsftpd.mysql
#添加以下两行(与mysql server相对应)
auth required pam_mysql.so user=vsftpd passwd=123456 host=10.0.8.8 db=vsftpd table=users usercolumn=name passwdcolumn=password crypt=2
account required pam_mysql.so user=vsftpd passwd=123456 host=10.0.8.8 db=vsftpd table=users usercolumn=name passwdcolumn=password crypt=2
(4)建立相应用户和修改vsftpd配置文件
[21:25:56 root@CS7-VM8-10 ~]#useradd -s /sbin/nologin -d /data/ftproot -r viruser
[21:27:07 root@CS7-VM8-10 ~]#mkdir -pv /data/ftproot/upload
[21:27:16 root@CS7-VM8-10 ~]#chown viruser:viruser /data/ftproot/upload
[21:27:58 root@CS7-VM8-10 ~]#vim /etc/vsftpd/vsftpd.conf
#添加以下内容
guest_enable=YES
guest_username=vuser
pam_service_name=vsftpd.mysql
[21:29:45 root@CS7-VM8-10 ~]#systemctl restart vsftpd.service
(5)a和b都能够登录,但是a和b账号不能上传
(6)针对不同的用户设置不同的访问权限
[21:30:02 root@CS7-VM8-10 ~]#vim /etc/vsftpd/vsftpd.conf
user_config_dir=/etc/vsftpd/conf.d/
[21:43:39 root@CS7-VM8-10 ~]#mkdir /etc/vsftpd/conf.d
[21:44:03 root@CS7-VM8-10 ~]#vim /etc/vsftpd/conf.d/alice
anon_upload_enable=YES
anon_mkdir_write_enable=YES
anon_other_write_enable=YES
local_root=/data/ftproot/alice
[21:46:02 root@CS7-VM8-10 ~]#mkdir /etc/vsftpd/conf.d/alice
[21:46:40 root@CS7-VM8-10 conf.d]#systemctl restart vsftpd.service
[21:49:20 root@CS7-VM8-10 conf.d]#mkdir /data/ftproot/alice
[21:49:26 root@CS7-VM8-10 conf.d]#cd /data/ftproot/alice
[21:49:30 root@CS7-VM8-10 alice]#ll
total 0
[21:49:31 root@CS7-VM8-10 alice]#cd ..
[21:49:33 root@CS7-VM8-10 ftproot]#pwd
/data/ftproot
[21:49:36 root@CS7-VM8-10 ftproot]#cd alice/
[21:49:43 root@CS7-VM8-10 alice]#touch alice.txt
[21:49:53 root@CS7-VM8-10 alice]#systemctl restart vsftpd.service
(7)验证:
[21:48:44 root@CS8-VM8-10 ~][#ftp 10.0.8.7
Connected to 10.0.8.7 (10.0.8.7).
220 (vsFTPd 3.0.2)
Name (10.0.8.7:root): alice
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> pwd
257 "/"
ftp> ls
227 Entering Passive Mode (10,0,8,7,49,206).
150 Here comes the directory listing.
-rw-r--r-- 1 0 0 0 Jul 13 13:49 alice.txt #验证成功
226 Directory send OK.
ftp>
2、配置samba共享,实现/www目录共享
注:
samba服务专用账户,必须是操作系统的账户
服务器端:CS8(10.0.8.8)
窗口一:
#安装samba服务器端软件
2 2022-07-20 09:20:08 yum install -y samba
#启动该服务
4 2022-07-20 09:21:49 systemctl enable --now smb
#查看新开的端口:tcp445、139
5 2022-07-20 09:21:54 ss -ntlu
#查看已经拥有的samba账号
6 2022-07-20 09:26:37 pdbedit -L
#创建相应的账号和密码
7 2022-07-20 09:27:26 useradd smb1
8 2022-07-20 09:27:42 smbpasswd -a smb1
9 2022-07-20 09:28:01 pdbedit -L
#对应的用户数据库文件
10 2022-07-20 09:28:40 ll /var/lib/samba/private/passdb.tdb
11 2022-07-20 09:29:01 file /var/lib/samba/private/passdb.tdb
12 2022-07-20 09:33:20 rpm -qc samba
13 2022-07-20 09:33:36 rpm -qc samba-common
14 2022-07-20 09:33:46 ls /etc/samba/
#配置文件
15 2022-07-20 09:34:13 vim /etc/samba/smb.conf
#添加以下内容
[share] #共享文件的名称
path=/www #文件的真是路径
read only = no #写权限的开启(或者writeable=yes)
窗口二:
[09:45:11 root@CS8-VM8-10 /][#history
1 2022-07-20 09:35:04 mkdir /www
5 2022-07-20 09:35:29 cd /www/
6 2022-07-20 09:35:30 ll
7 2022-07-20 09:35:43 touch test1.txt
8 2022-07-20 09:35:46 touch test2.txt
9 2022-07-20 09:35:51 ll
10 2022-07-20 09:44:18 cd ..
11 2022-07-20 09:44:19 ll
12 2022-07-20 09:44:24 ll | grep www
13 2022-07-20 09:44:49 chmod 777 /www
15 2022-07-20 09:45:11 ll /www -d
客户端:CS7(10.0.8.7)
2022-07-20 09:20:47 yum install -y samba-client
2022-07-20 09:24:54 smbclient -L 10.0.8.8
Enter SAMBA\root's password:
Anonymous login successful
Sharename Type Comment
--------- ---- -------
print$ Disk Printer Drivers
IPC$ IPC IPC Service (Samba 4.14.5)
Reconnecting with SMB1 for workgroup listing.
smbXcli_negprot_smb1_done: No compatible protocol selected by server.
protocol negotiation failed: NT_STATUS_INVALID_NETWORK_RESPONSE
Unable to connect with SMB1 -- no workgroup available
2022-07-20 09:30:34 smbclient -L 10.0.8.8 -U smb1%123456
Sharename Type Comment
--------- ---- -------
print$ Disk Printer Drivers
share Disk
IPC$ IPC IPC Service (Samba 4.14.5)
smb1 Disk Home Directories
Reconnecting with SMB1 for workgroup listing.
smbXcli_negprot_smb1_done: No compatible protocol selected by server.
protocol negotiation failed: NT_STATUS_INVALID_NETWORK_RESPONSE
Unable to connect with SMB1 -- no workgroup available
2022-07-20 09:43:06 smbclient //10.0.8.8/share -U smb1%123456 #share是要分享的目录。(与smbclient -L 10.0.8.8 -U smb1%123456命令提示信息相一致)
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Wed Jul 20 09:35:46 2022
.. D 0 Wed Jul 20 09:35:04 2022
#服务器端/www中的文件test1.txt 和test2.txt
test1.txt N 0 Wed Jul 20 09:35:43 2022
test2.txt N 0 Wed Jul 20 09:35:46 2022
104806400 blocks of size 1024. 98818268 blocks available
smb: \> !ls
anaconda-ks.cfg Documents Music Templates
a.sh Downloads Pictures Videos
Desktop initial-setup-ks.cfg Public
smb: \> put a
anaconda-ks.cfg a.sh
smb: \> put anaconda-ks.cfg #上传文件anaconda-ks.cfg
putting file anaconda-ks.cfg as \anaconda-ks.cfg (618.1 kb/s) (average 618.2 kb/s)
至此,实验成功。
3、使用rsync+inotify实现/www目录实时同步
数据服务器:CS8(10.0.8.8)
窗口一:(窗口一、二单机使用)
1 2022-07-20 20:15:37 yum install -y epel-release
2 2022-07-20 20:16:02 yum install -y inotify-tools
3 2022-07-20 20:16:24 mkdir /data/www
4 2022-07-20 20:18:21 rpm -ql inotify-tools #两个主要文件如下
/usr/bin/inotifywait (在被监控的文件或目录上等待特定文件系统事件(open ,close,delete等)发生,常用于实时同步的目录监控)
/usr/bin/inotifywatch (收集被监控的文件系统使用的统计数据,指文件系统事件发生的次数统计)
...
5 2022-07-20 20:19:46 inotifywait /data/www (inotifywait 用法略)
Setting up watches.
Watches established.
/data/www/ CREATE a.txt
6 2022-07-20 20:21:43 inotifywait -mrq /data/www --timefmt "%F %H:%M:%S" --format "%T %w%f event: %;e" -e create,delete,moved_to,close_write,attrib #持续前台监控特定事件(文件的属性发生变化)
[20:19:37 root@CS8-VM8-10 ~][#touch /data/www/a.txt
[20:19:58 root@CS8-VM8-10 ~][#mkdir /data/www/dir2
[20:20:28 root@CS8-VM8-10 ~][#rm -rf /data/www/a.txt
[20:22:00 root@CS8-VM8-10 ~][#touch /data/www/a1.txt
[20:22:40 root@CS8-VM8-10 ~][#cat /data/www/a1.txt
窗口二:(窗口一、二单机使用)
[20:19:58 root@CS8-VM8-10 ~][#inotifywait /data/www
Setting up watches.
Watches established.
/data/www/ CREATE,ISDIR dir2
--format "%T %w%f event: ~][#inotifywait -mrq /data/www --timefmt "%F %H:%M:%S"
> %;e" -e create,delete,moved_to,close_write,attrib
2022-07-20 20:22:00 /data/www/a.txt event:
DELETE
2022-07-20 20:22:40 /data/www/a1.txt event:
CREATE
2022-07-20 20:22:40 /data/www/a1.txt event:
ATTRIB
2022-07-20 20:22:40 /data/www/a1.txt event:
CLOSE_WRITE;CLOSE
^C
窗口三:(配合备份服务器使用)
1 2022-07-20 16:04:30 rsync rsync://10.0.8.18 ( 两者相等rsync 10.0.8.18::)
3 2022-07-20 16:10:23 rsync /etc/shadow root@10.0.8.18::backup
4 2022-07-20 16:11:28 rsync /etc/networks root@10.0.8.18::backup
5 2022-07-20 16:15:43 ss -ntul
6 2022-07-20 16:17:44 setfacl -m u:nobody:rwx /data/backup/
[21:01:31 root@CS8-VM8-10 backup][#
[21:00:37 root@CS8-VM8-10 ~][#inotifywait -mrq /data/backup --timefmt "%F %H:%M:%S" --format "%T %w%f event: %;e" -close_write,attrib
2022-07-20 21:01:22 /data/backup/.shadow.dJfKLV event: CREATE
2022-07-20 21:01:22 /data/backup/.shadow.dJfKLV event: ATTRIB
2022-07-20 21:01:22 /data/backup/.shadow.dJfKLV event: CLOSE_WRITE;CLOSE
2022-07-20 21:01:22 /data/backup/.shadow.dJfKLV event: ATTR
备份服务器:CS8(10.0.8.18)
3 2022-07-20 15:57:44 rsync
4 2022-07-20 15:58:02 rpm -ql rsync
5 2022-07-20 15:58:16 rpm -qf rsync
6 2022-07-20 15:58:31 rpm -qf `which rsync`
7 2022-07-20 15:58:51 rsync --daemon
8 2022-07-20 15:59:02 touch /etc/rsyncd.conf
9 2022-07-20 15:59:04 rsync --daemon
10 2022-07-20 15:59:10 ss -ntlu 873端口
11 2022-07-20 16:00:26 vim /etc/rsyncd.conf (与下文内容一样)
killall rsync
#手动开启守护进程,为了减少麻烦,直接安装rsync-daemon,此时手动开启之后修改了配置文件,服务无法启动。
---------------------------------------------------------------------------------------------------
---------------------------------------------------------------------------------------------------
12 2022-07-20 16:00:12 mkdir /data/backup
13 2022-07-20 16:02:15 yum install -y rsync-daemon
14 2022-07-20 16:02:37 rpm -ql rsync-daemo
17 2022-07-20 16:03:02 systemctl enable --now rsyncd
15 2022-07-20 16:03:11 ss -ntlu (873端口开启)
20 2022-07-20 16:07:57 vim /etc/rsyncd.conf
[backup]
path = /data/backup/
read only = no
21 2022-07-20 16:08:26 systemctl restart rsyncd
22 2022-07-20 16:07:57 setfacl -m u:nobody:rwx /data/backup/
[20:58:45 root@CS8-VM8-10 backup][#ll
total 4
-rw-r--r-- 1 nobody nobody 58 Jul 20 20:58 networks
[20:58:45 root@CS8-VM8-10 backup][#ll
total 8
-rw-r--r-- 1 nobody nobody 58 Jul 20 20:58 networks
---------- 1 nobody nobody 1362 Jul 20 21:01 shadow
自此,实验成功
4、LVS调度算法总结
ipvs scheduler:根据其调度时是否考虑各RS当前的负载状态。
静态方法(仅算法本身进行调度):
1.RR:roundrobin,轮询(较常用)
2.WRR:Weighted RR,加权轮询(较常用)----可设置相关比重
3.SH:Sourse Hashing ,实现session sticky,源ip地址hash。
将来自同一个ip地址的请求始终发往第一次选中的RS中,实现会话绑定。
4.DH:Destination Hashing,目标地址哈希,第一次轮询调度至RS,后续将发往同一个目标地址的请求始终发至第一次选中的RS中。(例:Web缓存)
5.FO(Weighted Fail Over)调度算法,在此FO算法中,遍历虚拟服务所关联的真实服务器链表,找到还未过载(未设IP_VS_DEST_F_OVERLOAD标志)的且权重最高的真实服务器,进行调度。
该算法是内核版本4.15版本后新增加的调度算法。
动态方法(根据每RS当前的负载状态及调度算法进行调度Overhead=value 较小的RS将被调度):
1.LC:Least Connections 适用于长连接应用。[ Overhead=activeconns*256+inactiveconns ]
2.WLC:Weighted LC,默认调度算法,较常用。 [ Overhead=(activeconns*256+inactiveconns)/weight)]
3.SED:Shortest Expection Delay,初始连接高权重优先,只检查活动连接,而不考虑非活动连接。[ Overhead=(activeconns+1)*256/weight ]
4.NQ:Never Queue,第一次均匀分配,后续SED
5.LBLC:Locality-Based LC动态的DH算法。例如:实现web cache
6.LBLCR:LBLC with Replication 带复制功能的LBLC,解决LBLC负载不均衡问题,从负载重的复制到负载轻的RS,,实现Web Cache等
7.OVF(Overflow-connection)调度算法,基于真实服务器的活动连接数量和权重值实现。将新连接调度到权重值最高的真实服务器,直到其活动连接数量超过权重值,
之后调度到下一个权重值最高的真实服务器,在此OVF算法中,遍历虚拟服务相关联的真实服务器链表,找到权重值最高的可用真实服务器。
该算法是内核版本4.15版本后新增加的调度算法。
一个可用的真实服务器需要同时满足以下条件:
(1)未过载(未设置IP_VS_DEST_F_OVERLOAD标志)
(2)真实服务器当前的活动连接数量小于其权重值
(3)其权重值不为零
5、LVS的跨网络DR实现(与“7.lvs-dr单网段的实现”步骤差不多,这里只写主要步骤)
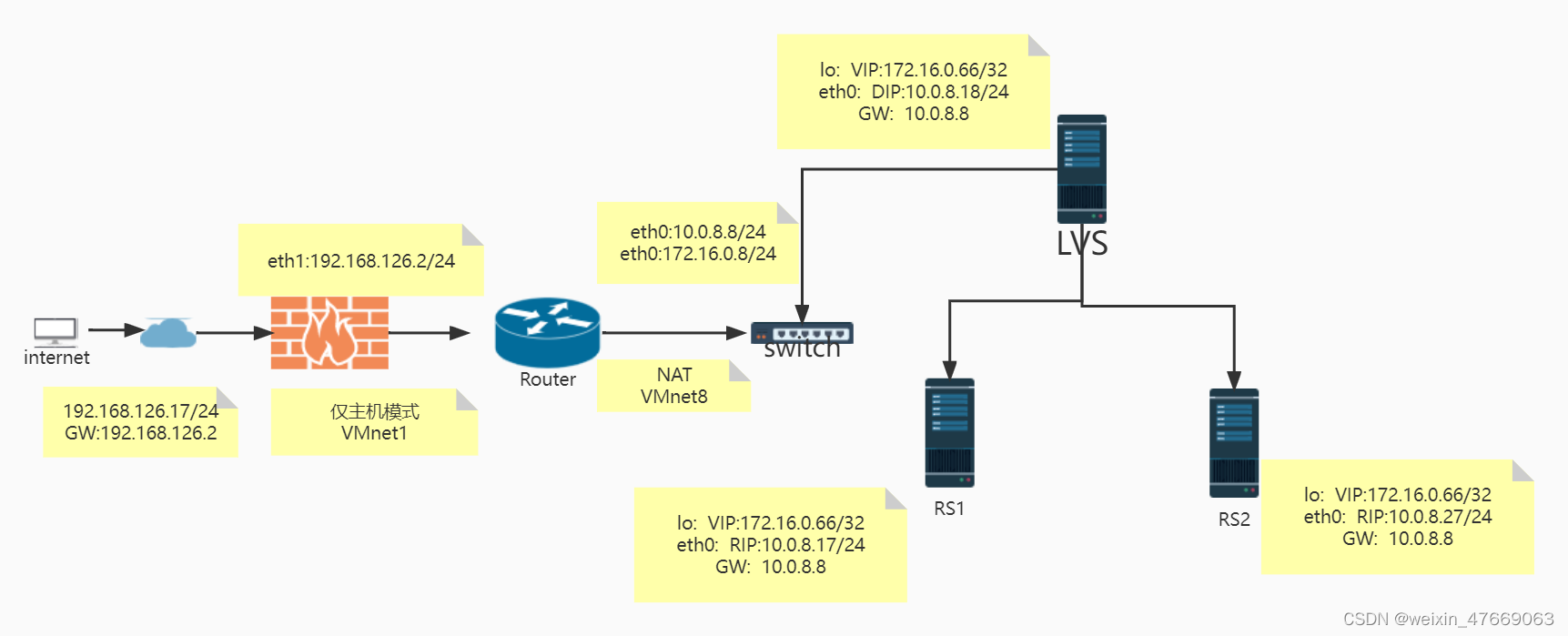
(1)internet (略–与本章第七题(1)一样)
(2)route:(eth0:10.0.8.8/24 172.16.0.8/24 eth1:192.168.126.2/24)
首先增加一张新的网卡
2 2022-07-23 21:49:33 ip addr add 172.16.0.8/24 dev eth0
3 2022-07-23 21:50:02 ip addr add 192.168.126.2/24 dev eth1
打开ip_forward(此项一定要打开,否则实验会失败)
8 2022-07-23 22:17:14 echo 'net.ipv4.ip_forward=1' >> /etc/sysctl.conf
9 2022-07-23 22:17:19 sysctl -p
net.ipv4.ip_forward = 1
(3)lvs:(运行脚本)
[22:41:27 root@lvs ~][#cat lvs_dr_vs.sh
#!/bin/bash
vip='172.16.0.66'
iface='lo:1'
mask='255.255.255.255'
port='80'
rs1='10.0.8.17'
rs2='10.0.8.27'
scheduler='wrr'
type='-g'
rpm -q ipvsadm &> /dev/null || yum -y install ipvsadm &> /dev/null
case $1 in
start)
ifconfig $iface $vip netmask $mask #broadcast $vip up
iptables -F
ipvsadm -A -t ${vip}:${port} -s $scheduler
ipvsadm -a -t ${vip}:${port} -r ${rs1} $type -w 1
ipvsadm -a -t ${vip}:${port} -r ${rs2} $type -w 1
echo "The VS Server is Ready!"
;;
stop)
ipvsadm -C
ifconfig $iface down
echo "The VS Server is Canceled!"
;;
*)
echo "Usage: $(basename $0) start|stop"
exit 1
;;
esac
#脚本运行结果
[22:10:58 root@lvs ~][#bash lvs_dr_vs.sh start
The VS Server is Ready!
(4)rs1(rs1与rs2配置基本相似。脚本一致)
[22:08:19 root@rs1 ~]#cat lvs_dr_rs1.sh
#!/bin/bash
vip=172.16.0.66
mask='255.255.255.255'
dev=lo:1
rpm -q httpd &> /dev/null || yum -y install httpd &>/dev/null
service httpd start &> /dev/null && echo "The httpd Server is Ready!"
echo "`hostname -I`" > /var/www/html/index.html
case $1 in
start)
echo 1 > /proc/sys/net/ipv4/conf/all/arp_ignore
echo 1 > /proc/sys/net/ipv4/conf/lo/arp_ignore
echo 2 > /proc/sys/net/ipv4/conf/all/arp_announce
echo 2 > /proc/sys/net/ipv4/conf/lo/arp_announce
ifconfig $dev $vip netmask $mask #broadcast $vip up
echo "The RS Server is Ready!"
;;
stop)
ifconfig $dev down
echo 0 > /proc/sys/net/ipv4/conf/all/arp_ignore
echo 0 > /proc/sys/net/ipv4/conf/lo/arp_ignore
echo 0 > /proc/sys/net/ipv4/conf/all/arp_announce
echo 0 > /proc/sys/net/ipv4/conf/lo/arp_announce
echo "The RS Server is Canceled!"
;;
*)
echo "Usage: $(basename $0) start|stop"
exit 1
;;
esac
#脚本运行结果
[22:11:26 root@rs1 ~]#bash lvs_dr_rs1.sh start
The httpd Server is Ready!
The RS Server is Ready!
(5)rs2(略)
(6)最后测试:在client(internet)上测试
[22:17:22 root@client ~]#curl 172.16.0.66
10.0.8.27
[22:17:23 root@client ~]#curl 172.16.0.66
10.0.8.17
[22:17:25 root@client ~]#curl 172.16.0.66
10.0.8.27
[22:17:25 root@client ~]#curl 172.16.0.66
10.0.8.17
[22:17:26 root@client ~]#curl 172.16.0.66
10.0.8.27
[22:17:26 root@client ~]#curl 172.16.0.66
10.0.8.17
[22:17:27 root@client ~]#curl 172.16.0.66
10.0.8.27
[22:17:27 root@client ~]#curl 172.16.0.66
10.0.8.17
至此,实验成功
6、实现基于文件验证的vsftpd虚拟用户
(1)创建用户数据库文件
#参照补充当中所需安装的相关包
1 2022-07-13 10:26:16 rpm -qf `which db_load`
2 2022-07-13 10:26:42 yum install -y libdb-utils
3 2022-07-13 10:26:59 cd /etc/vsftpd/
4 2022-07-13 10:27:01 ll
5 2022-07-13 10:28:15 vim virusers.txt
xiaoming #用户名(且是奇数行)
123456 #密码(且是偶数行)
xiaohong
000000
6 2022-07-13 10:30:16 db_load -T -t hash -f virusers.txt virusers.db
7 2022-07-13 10:30:25 ll virusers.txt
8 2022-07-13 10:30:28 ll virusers.db
#为了保证安全,设置权限
9 2022-07-13 10:31:03 chmod 600 virusers.txt
10 2022-07-13 10:31:06 chmod 600 virusers.db
(2)创建用户和访问ftp目录
[10:43:50 root@CS8-VM8-10 vsftpd][#useradd -d /data/ftproot -s /sbin/nologin -r virusers
[10:53:15 root@CS8-VM8-10 vsftpd][#mkdir -pv /data/ftproot/upload
mkdir: created directory '/data/ftproot'
mkdir: created directory '/data/ftproot/upload'
[10:53:35 root@CS8-VM8-10 vsftpd][#chown virusers:virusers /data/ftproot/upload/
[10:54:38 root@CS8-VM8-10 vsftpd][#
(3)创建pam配置文件
16 2022-07-13 10:56:33 cd /etc/pam.d/
17 2022-07-13 10:56:34 ll
18 2022-07-13 10:59:38 vim vsftpd.db
#增加以下行:
auth required pam_userdb.so db=/etc/vsftpd/virusers
account required pam_userdb.so db=/etc/vsftpd/virusers
(4)指定pam配置文件
20 2022-07-13 11:03:37 vim /etc/vsftpd/vsftpd.conf
#增加以下行:
guest_enable=YES
guest_username=virusers
pam_service_name=vsftpd.db
(5)虚拟用户建立独立的配置文件(这里只写xiaoming)
#指定各个用户配置文件的存放位置
[15:27:31 root@CS8-VM8-10 ~][#vim /etc/vsftpd/vsftpd.conf
#增加该行:(小明和小红的权限不一致时,小明可以上传文件,小红不行)
user_config_dir=/etc/vsftpd/conf.d/
#创建各个用户配置文件的存放位置
[15:29:31 root@CS8-VM8-10 ~][#mkdir /etc/vsftpd/conf.d
[15:30:12 root@CS8-VM8-10 ~][#cd /etc/vsftpd/conf.d/
[15:30:29 root@CS8-VM8-10 conf.d][#ll
total 0
#创建各用户自已的配置文件,允许xiaoming用户可读写,其它用户只读
[15:30:32 root@CS8-VM8-10 conf.d][#vim /etc/vsftpd/conf.d/xiaoming
#增加以下行:(为xiaoming用户单独设置配置文件时可省略,写入至xiaoming单独用户中)
anon_upload_enable=YES
anon_mkdir_write_enable=YES
anon_other_write_enable=YES
#为xiaoming用户单独设置相关配置文件
[16:12:05 root@CS8-VM8-10 conf.d][#pwd /etc/vsftpd/conf.d
[16:13:26 root@CS8-VM8-10 conf.d][#vim xiaoming
#增加一下几行:
local_root=/data/ftproot_xiaoming/ #登录目录改变至指定的目录
anon_upload_enable=YES
anon_mkdir_write_enable=YES
anon_other_write_enable=YES
#创建xiaoming用户建立对应的数据目录( 与local_root=/data/ftproot_xiaoming/目录相一致 ;小明、小红创建各自相对的独立文件:)
[16:01:26 root@CS8-VM8-10 ~][#getent passwd virusers
virusers:x:974:974::/data/ftproot:/sbin/nologin
[16:01:38 root@CS8-VM8-10 ~][#mkdir /data/ftproot_xiaoming
[16:02:03 root@CS8-VM8-10 ~][#mkdir /data/ftproot_xiaohong
[16:02:08 root@CS8-VM8-10 ~][#touch /data/ftproot_xiaoming/xiaoming.txt
[16:02:33 root@CS8-VM8-10 ~][#touch /data/ftproot_xiaohong/xiaohong.txt
[16:02:42 root@CS8-VM8-10 ~][#cd /data/ftproot
#目录结构为:
[17:38:25 root@CS8-VM8-10 vsftpd][#tree /data/ftproot*
/data/ftproot
├── b.txt
└── upload
├── a.txt
├── hosts
└── issue
/data/ftproot_xiaohong
└── xiaohong.txt
/data/ftproot_xiaoming
└── xiaoming.txt
3 directories, 4 files
[17:42:04 root@CS8-VM8-10 vsftpd][#
(6)验证小明登录时看到自己对应的文件、权限等相相关设置
[17:38:29 root@CS7-VM8-10 ~]#ftp 10.0.8.8
Connected to 10.0.8.8 (10.0.8.8).
220 (vsFTPd 3.0.3)
Name (10.0.8.8:root): xiaoming
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> pwd
257 "/" is the current directory
ftp> ls
227 Entering Passive Mode (10,0,8,8,47,135).
150 Here comes the directory listing.
-rw-r--r-- 1 0 0 0 Jul 13 08:02 xiaoming.txt (#验证成功)
226 Directory send OK.
ftp>
(7)后期在添加一个用户
cd /etc/vsftpd/
ll
vim virusers.txt (#为后期维护方便,该文件不要删除)
#增加该行
xiaoqiang
654321
db_load -T -t hash -f virusers.txt virusers.db
自此,小强亦可登陆。
由于没有设置相关配置文件,默认用主配置文件中的相关定义。(即默认目录/data/ftproot为家目录)
#做完映射,此时操作系统的账号(virusers)不能登录ftp服务器(useradd -d /data/ftproot -s /sbin/nologin -r virusers)
7.lvs-dr单网段的实现
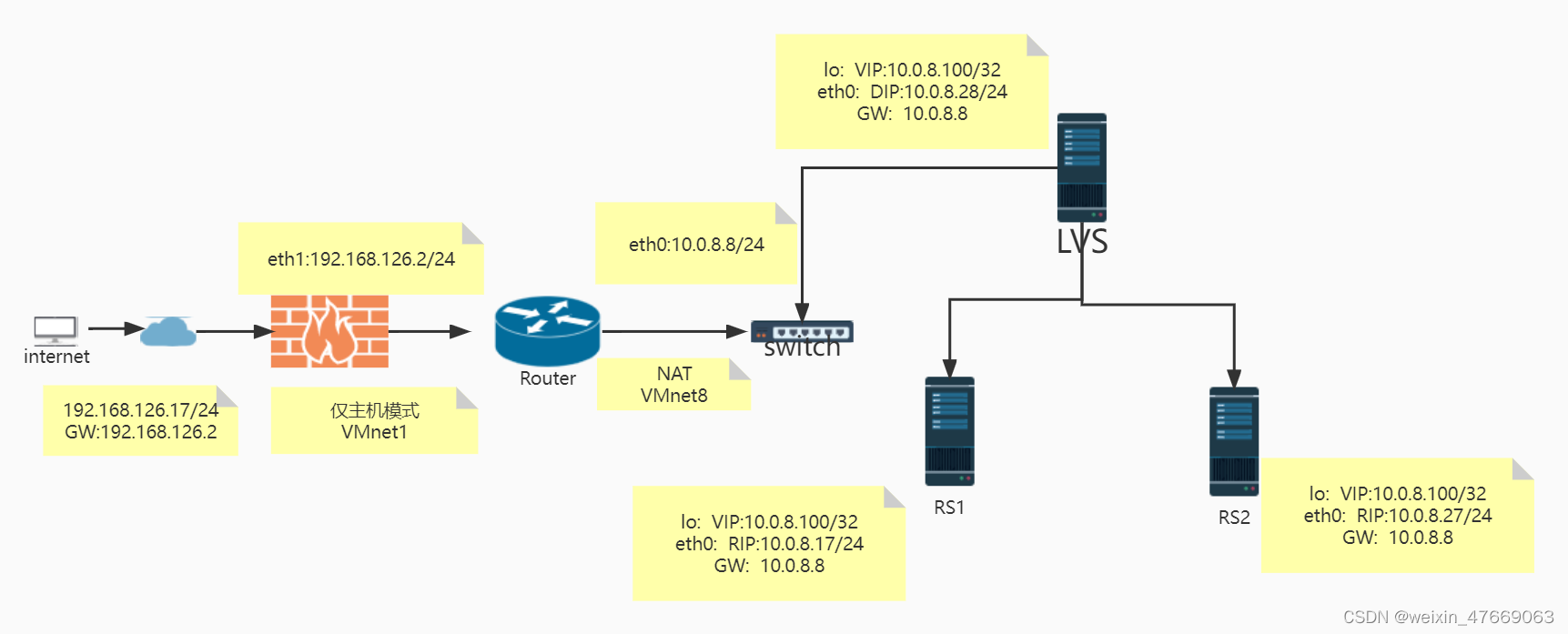
五台主机:地址等详细信息如上图:
五台主机搭建的顺序按照先易后难进行,并且逐段进行测试。(搭建顺序如下:1.client;2.router;3.RS1;4.RS2;5.LVS)
(1)internet主机:(仅主机模式)
(7CS7:192.168.126.17/24 GW:192.168.126.2)
4 2022-07-22 21:30:31 hostnamectl set-hostname client
5 2022-07-22 21:30:33 exit
6 2022-07-23 09:43:34 ip a
7 2022-07-23 09:44:05 cd /etc/sysconfig/network/
8 2022-07-23 09:44:11 cd /etc/sysconfig/network-scripts/
11 2022-07-23 09:44:50 vim ifcfg-eth0
#内容如下:
1 DEVICE=eth0
2 NAME=eth0
3 BOOTPROTO=static
4 IPADDR=192.168.126.17
5 PREFIX=24
6 GATEWAY=192.168.126.2
(2)Router:(eth0:10.0.8.8 eth1:192.168.126.2)
首先增加一个网卡,配置为仅主机模式。
1 2022-07-22 21:31:22 hostnamectl set-hostname router
#打开ip_forward功能
[21:33:50 root@router ~][#echo 'net.ipv4.ip_forward=1' >> /etc/sysctl.conf
[21:34:36 root@router ~][#sysctl -p
net.ipv4.ip_forward = 1
5 2022-07-23 09:46:42 cd /etc/sysconfig/network-scripts/
6 2022-07-23 09:46:44 ll
7 2022-07-23 09:47:08 cp -a ifcfg-eth0 ./ifcfg-eth1
8 2022-07-23 09:47:10 ll
10 2022-07-23 09:47:28 vim ifcfg-eth0
#内容如下:
DEVICE=eth0
NAME=eth0
BOOTTPROTO=static
IPADDR=10.0.8.8
PREFIX=24
ONBOOT=yes
11 2022-07-23 09:48:21 vim ifcfg-eth1
#内容如下:
DEVICE=eth1
NAME=eth1
BOOTTPROTO=static
IPADDR=192.168.126.2
PREFIX=24
ONBOOT=yes
#让新增加的网卡生效
16 2022-07-23 09:50:33 nmcli connection reload
17 2022-07-23 09:50:36 nmcli connection reload up
#能ping通,说明router与client相通
19 2022-07-23 09:50:50 ping 192.168.126.17
PING 192.168.126.17 (192.168.126.17) 56(84) bytes of data.
64 bytes from 192.168.126.17: icmp_seq=1 ttl=64 time=0.790 ms
...
(3)LVS:
2 2022-07-22 21:31:48 hostnamectl set-hostname lvs
3 2022-07-22 21:31:51 exit
4 2022-07-23 09:36:33 ip a
5 2022-07-23 09:51:23 cd /etc/sysconfig/network-scripts/
6 2022-07-23 09:51:30 vim ifcfg-eth0
#内容如下:
DEVICE=eth0
NAME=eth0
BOOTTPROTO=static
IPADDR=10.0.8.28
PREFIX=24
GATEWAY=10.0.8.8
ONBOOT=yes
#增加访问的VIP地址,将其绑定在回环网卡上
7 2022-07-23 09:55:26 ifconfig lo:1 10.0.8.100/32
8 2022-07-23 09:55:28 ip a
#重新加载网卡,使其生效
10 2022-07-23 09:56:46 nmcli connection reload
11 2022-07-23 09:56:48 nmcli connection reload up
#查看路由是否生效(生效)
13 2022-07-23 09:58:40 route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
0.0.0.0 10.0.8.8 0.0.0.0 UG 100 0 0 eth0
10.0.8.0 0.0.0.0 255.255.255.0 U 100 0 0 eth0
#检测与route中eth0接口的地址是否ping通
15 2022-07-23 09:59:10 ping 10.0.8.8
PING 10.0.8.8 (10.0.8.8) 56(84) bytes of data.
64 bytes from 10.0.8.8: icmp_seq=1 ttl=64 time=0.822 ms
#检测与route中eth1接口的地址是否ping通
19 2022-07-23 10:10:17 ping 192.168.126.17
PING 192.168.126.17 (192.168.126.17) 56(84) bytes of data.
64 bytes from 192.168.126.17: icmp_seq=1 ttl=128 time=0.588 ms
。。。
20 2022-07-23 10:10:35 cat /etc/sysconfig/network-scripts/ifcfg-eth0
21 2022-07-23 10:17:17 ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
***inet 10.0.8.100/0 scope global lo:1***
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc mq state UP group default qlen 1000
link/ether 00:0c:29:b2:ca:b4 brd ff:ff:ff:ff:ff:ff
inet 10.0.8.28/24 brd 10.0.8.255 scope global noprefixroute eth0
valid_lft forever preferred_lft forever
inet6 fe80::20c:29ff:feb2:cab4/64 scope link
valid_lft forever preferred_lft forever
#安装LVS的相关软件(程序包ipvsadm)
22 2022-07-23 10:19:18 yum install -y ipvsadm
23 2022-07-23 10:19:49 dnf -y install ipvsadm
#查看对应的规则(此时没有进行配置)
24 2022-07-23 10:20:39 ipvsadm -Ln
IP Virtual Server version 1.2.1 (size=4096)
Prot LocalAddress:Port Scheduler Flags
-> RemoteAddress:Port Forward Weight ActiveConn InActConn
25 2022-07-23 10:22:31 ipvsadm -A -t 10.0.8.100:80 -s rr
26 2022-07-23 10:22:59 ipvsadm -a -t 10.0.8.100:80 -r 10.0.8.17 -g
27 2022-07-23 10:23:05 ipvsadm -a -t 10.0.8.100:80 -r 10.0.8.27 -g
#配置完之后
28 2022-07-23 10:23:08 ipvsadm -Ln
IP Virtual Server version 1.2.1 (size=4096)
Prot LocalAddress:Port Scheduler Flags
-> RemoteAddress:Port Forward Weight ActiveConn InActConn
TCP 10.0.8.100:80 rr
-> 10.0.8.17:80 Route 1 0 0
-> 10.0.8.27:80 Route 1 0 0
(4)RS1:(略)
(5)RS2:(RS1与RS2的配置类似)
1 2022-07-22 21:32:20 hostnamectl set-hostname rs2
2 2022-07-22 21:32:22 exit
3 2022-07-23 10:04:28 cd /etc/sysconfig/network-scripts/
4 2022-07-23 10:04:32 vim ifcfg-eth0
#内容如下:
DEVICE=eth0
NAME=eth0
BOOTPROTO=static
IPADDR=10.0.8.27
PREFIX=24
GATEWAY=10.0.8.8
8 2022-07-23 10:06:34 systemctl start httpd
9 2022-07-23 10:06:40 systemctl status httpd
10 2022-07-23 10:07:04 hostname -I > /var/www/html/index.html
12 2022-07-23 10:08:14 curl 10.0.8.27
10.0.8.27
13 2022-07-23 10:16:49 ip a
14 2022-07-23 10:17:05 ifconfig lo:1 10.0.8.100/32
15 2022-07-23 10:17:07 ip a
16 2022-07-23 10:17:52 echo 1 > /proc/sys/net/ipv4/conf/all/arp_ignore
17 2022-07-23 10:17:56 echo 1 > /proc/sys/net/ipv4/conf/lo/arp_ignore
18 2022-07-23 10:18:37 echo 2 > /proc/sys/net/ipv4/conf/all/arp_announce
19 2022-07-23 10:18:44 echo 2 > /proc/sys/net/ipv4/conf/lo/arp_announce
20 2022-07-23 10:19:31 ping 192.168.126.17
21 2022-07-23 16:23:09 history
PING 192.168.126.17 (192.168.126.17) 56(84) bytes of data.
64 bytes from 192.168.126.17: icmp_seq=1 ttl=63 time=0.376 ms
。。。
最后测试:在client上测试
[10:23:22 root@client network-scripts]#curl 10.0.8.100
10.0.8.27
[10:23:33 root@client network-scripts]#curl 10.0.8.100
10.0.8.17
[10:23:35 root@client network-scripts]#curl 10.0.8.100
10.0.8.27
[10:23:37 root@client network-scripts]#curl 10.0.8.100
10.0.8.17
[10:23:38 root@client network-scripts]#curl 10.0.8.100
10.0.8.27
[10:23:39 root@client network-scripts]#curl 10.0.8.100
10.0.8.17

























 1万+
1万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








